US8850050B1 - Providing a managed browser - Google Patents
Providing a managed browserDownload PDFInfo
- Publication number
- US8850050B1 US8850050B1US14/043,343US201314043343AUS8850050B1US 8850050 B1US8850050 B1US 8850050B1US 201314043343 AUS201314043343 AUS 201314043343AUS 8850050 B1US8850050 B1US 8850050B1
- Authority
- US
- United States
- Prior art keywords
- computing device
- managed
- policies
- managed browser
- browser
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Active
Links
Images
Classifications
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/20—Network architectures or network communication protocols for network security for managing network security; network security policies in general
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/30—Authentication, i.e. establishing the identity or authorisation of security principals
- G06F21/31—User authentication
- G06F21/41—User authentication where a single sign-on provides access to a plurality of computers
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/50—Monitoring users, programs or devices to maintain the integrity of platforms, e.g. of processors, firmware or operating systems
- G06F21/52—Monitoring users, programs or devices to maintain the integrity of platforms, e.g. of processors, firmware or operating systems during program execution, e.g. stack integrity ; Preventing unwanted data erasure; Buffer overflow
- G06F21/53—Monitoring users, programs or devices to maintain the integrity of platforms, e.g. of processors, firmware or operating systems during program execution, e.g. stack integrity ; Preventing unwanted data erasure; Buffer overflow by executing in a restricted environment, e.g. sandbox or secure virtual machine
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/60—Protecting data
- G06F21/62—Protecting access to data via a platform, e.g. using keys or access control rules
- G06F21/6218—Protecting access to data via a platform, e.g. using keys or access control rules to a system of files or objects, e.g. local or distributed file system or database
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F9/00—Arrangements for program control, e.g. control units
- G06F9/06—Arrangements for program control, e.g. control units using stored programs, i.e. using an internal store of processing equipment to receive or retain programs
- G06F9/46—Multiprogramming arrangements
- G06F9/50—Allocation of resources, e.g. of the central processing unit [CPU]
- G06F9/5005—Allocation of resources, e.g. of the central processing unit [CPU] to service a request
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L12/00—Data switching networks
- H04L12/28—Data switching networks characterised by path configuration, e.g. LAN [Local Area Networks] or WAN [Wide Area Networks]
- H04L12/46—Interconnection of networks
- H04L12/4633—Interconnection of networks using encapsulation techniques, e.g. tunneling
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L41/00—Arrangements for maintenance, administration or management of data switching networks, e.g. of packet switching networks
- H04L41/08—Configuration management of networks or network elements
- H04L41/0803—Configuration setting
- H04L41/0813—Configuration setting characterised by the conditions triggering a change of settings
- H04L41/0816—Configuration setting characterised by the conditions triggering a change of settings the condition being an adaptation, e.g. in response to network events
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L41/00—Arrangements for maintenance, administration or management of data switching networks, e.g. of packet switching networks
- H04L41/50—Network service management, e.g. ensuring proper service fulfilment according to agreements
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L47/00—Traffic control in data switching networks
- H04L47/70—Admission control; Resource allocation
- H04L47/76—Admission control; Resource allocation using dynamic resource allocation, e.g. in-call renegotiation requested by the user or requested by the network in response to changing network conditions
- H04L47/762—Admission control; Resource allocation using dynamic resource allocation, e.g. in-call renegotiation requested by the user or requested by the network in response to changing network conditions triggered by the network
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/08—Network architectures or network communication protocols for network security for authentication of entities
- H04L63/0815—Network architectures or network communication protocols for network security for authentication of entities providing single-sign-on or federations
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/10—Network architectures or network communication protocols for network security for controlling access to devices or network resources
- H04L63/101—Access control lists [ACL]
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/10—Network architectures or network communication protocols for network security for controlling access to devices or network resources
- H04L63/102—Entity profiles
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L65/00—Network arrangements, protocols or services for supporting real-time applications in data packet communication
- H04L65/40—Support for services or applications
- H04L65/403—Arrangements for multi-party communication, e.g. for conferences
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L67/00—Network arrangements or protocols for supporting network services or applications
- H04L67/01—Protocols
- H04L67/02—Protocols based on web technology, e.g. hypertext transfer protocol [HTTP]
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L67/00—Network arrangements or protocols for supporting network services or applications
- H04L67/01—Protocols
- H04L67/10—Protocols in which an application is distributed across nodes in the network
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F2221/00—Indexing scheme relating to security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F2221/21—Indexing scheme relating to G06F21/00 and subgroups addressing additional information or applications relating to security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F2221/2143—Clearing memory, e.g. to prevent the data from being stolen
Definitions
- aspects of the disclosurerelate to computer hardware and software.
- one or more aspects of the disclosuregenerally relate to computer hardware and software for providing a managed browser.
- Various aspects of the disclosureprovide more efficient, effective, functional, and convenient ways of controlling how mobile devices can be used, what resources mobile devices can access, and how the applications and other software running on these devices can interact with other resources.
- a managed browsercan be deployed, implemented, and/or used in a number of different ways to provide one or more of these and/or other advantages.
- a computing devicemay load a managed browser. Subsequently, the computing device may receive a request to access one or more enterprise resources via the managed browser. Then, the computing device may create at least one application tunnel from the managed browser to the one or more enterprise resources. The computing device then may obtain enterprise data from the one or more enterprise resources via the at least one application tunnel.
- a computing devicemay load a managed browser. Subsequently, the computing device may establish a connection to at least one other computing device to initiate a device cloud. Then, the computing device may extend a session of the managed browser across the device cloud.
- a computing devicemay load a managed browser. Subsequently, the computing device may obtain device state information. Then, the computing device may determine, based on the device state information, whether to selectively disable one or more operational modes of the managed browser. In response to determining to selectively disable at least one operational mode of the managed browser, the computing device may cause the at least one operational mode to be disabled.
- a computing devicemay load a managed browser. Subsequently, the computing device may receive one or more policies. Then, the computing device may apply the one or more policies to the managed browser.
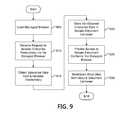
- a computing devicemay load a managed browser. Subsequently, the computing device may receive a request to access one or more enterprise resources via the managed browser. Then, the computing device may obtain enterprise data from the one or more enterprise resources based on the request. The computing device then may store the obtained enterprise data in a secure document container.
- a computing devicemay load a managed browser. Subsequently, the computing device may receive a single sign-on (SSO) credential that is associated with at least one user account. Then, the computing device may obtain enterprise data from one or more enterprise resources based on the SSO credential. The computing device then may provide access to the obtained enterprise data via the managed browser.
- SSOsingle sign-on
- a computing devicemay load a managed browser. Subsequently, the computing device may receive a request to access an application store via the managed browser. Then, the computing device may obtain enterprise data from the application store based on the request.
- a computing devicemay load a managed browser. Subsequently, the computing device may receive a request to access one or more enterprise resources via the managed browser. Then, the computing device may obtain enterprise data from the one or more enterprise resources based on the request. The computing device then may control the obtained enterprise data based on one or more policies.
- FIG. 1depicts an illustrative computer system architecture that may be used in accordance with one or more illustrative aspects described herein.
- FIG. 2depicts an illustrative remote-access system architecture that may be used in accordance with one or more illustrative aspects described herein.
- FIG. 3depicts an illustrative enterprise mobility management system that may be used in accordance with one or more illustrative aspects described herein.
- FIG. 4depicts another illustrative enterprise mobility management system that may be used in accordance with one or more illustrative aspects described herein.
- FIG. 5depicts a flowchart that illustrates a method of creating an application tunnel from a managed browser to one or more enterprise resources in accordance with one or more illustrative aspects discussed herein.
- FIG. 6depicts a flowchart that illustrates a method of extending a managed browser session across a device cloud in accordance with one or more illustrative aspects discussed herein.
- FIG. 7depicts a flowchart that illustrates a method of selectively disabling an operational mode of a managed browser in accordance with one or more illustrative aspects discussed herein.
- FIG. 8depicts a flowchart that illustrates a method of applying one or more mobile device management policies to a managed browser in accordance with one or more illustrative aspects discussed herein.
- FIG. 9depicts a flowchart that illustrates a method of providing access to a secure document container via a managed browser in accordance with one or more illustrative aspects discussed herein.
- FIG. 10depicts a flowchart that illustrates a method of obtaining enterprise data based on a single sign-on credential and providing access to the data via a managed browser in accordance with one or more illustrative aspects discussed herein.
- FIG. 11depicts a flowchart that illustrates a method of providing access to an application store via a managed browser in accordance with one or more illustrative aspects discussed herein.
- FIG. 12depicts a flowchart that illustrates a method of obtaining and controlling enterprise data with a managed browser in accordance with one or more illustrative aspects discussed herein.
- FIG. 13depicts a flowchart that illustrates a method of administering one or more policies for a managed browser in accordance with one or more illustrative aspects discussed herein.
- FIG. 14depicts a flowchart that illustrates another method of providing access to an application store via a managed browser in accordance with one or more illustrative aspects discussed herein.
- FIG. 15depicts a flowchart that illustrates a method of providing a managed execution environment within a managed browser in accordance with one or more illustrative aspects discussed herein.
- FIGS. 1-4Before discussing these concepts in greater detail, however, several examples of computing architecture and enterprise mobility management architecture that may be used in implementing and/or otherwise providing various aspects of the disclosure will first be discussed with respect to FIGS. 1-4 .
- FIG. 1illustrates one example of a system architecture and data processing device that may be used to implement one or more illustrative aspects described herein in a standalone and/or networked environment.
- Various network nodes 103 , 105 , 107 , and 109may be interconnected via a wide area network (WAN) 101 , such as the Internet.
- WANwide area network
- Other networksmay also or alternatively be used, including private intranets, corporate networks, local area networks (LANs), metropolitan area networks (MAN), wireless networks, personal networks (PAN), and the like.
- Network 101is for illustration purposes and may be replaced with fewer or additional computer networks.
- a LANmay have one or more of any known LAN topology and may use one or more of a variety of different protocols, such as Ethernet.
- Devices 103 , 105 , 107 , 109 and other devicesmay be connected to one or more of the networks via twisted pair wires, coaxial cable, fiber optics, radio waves or other communication media.
- networkrefers not only to systems in which remote storage devices are coupled together via one or more communication paths, but also to stand-alone devices that may be coupled, from time to time, to such systems that have storage capability. Consequently, the term “network” includes not only a “physical network” but also a “content network,” which is comprised of the data—attributable to a single entity—which resides across all physical networks.
- the componentsmay include data server 103 , web server 105 , and client computers 107 , 109 .
- Data server 103provides overall access, control and administration of databases and control software for performing one or more illustrative aspects describe herein.
- Data server 103may be connected to web server 105 through which users interact with and obtain data as requested.
- data server 103may act as a web server itself and be directly connected to the Internet.
- Data server 103may be connected to web server 105 through the network 101 (e.g., the Internet), via direct or indirect connection, or via some other network.
- Usersmay interact with the data server 103 using remote computers 107 , 109 , e.g., using a web browser to connect to the data server 103 via one or more externally exposed web sites hosted by web server 105 .
- Client computers 107 , 109may be used in concert with data server 103 to access data stored therein, or may be used for other purposes.
- a usermay access web server 105 using an Internet browser, as is known in the art, or by executing a software application that communicates with web server 105 and/or data server 103 over a computer network (such as the Internet).
- FIG. 1illustrates just one example of a network architecture that may be used, and those of skill in the art will appreciate that the specific network architecture and data processing devices used may vary, and are secondary to the functionality that they provide, as further described herein. For example, services provided by web server 105 and data server 103 may be combined on a single server.
- Each component 103 , 105 , 107 , 109may be any type of known computer, server, or data processing device.
- Data server 103e.g., may include a processor 111 controlling overall operation of the rate server 103 .
- Data server 103may further include RAM 113 , ROM 115 , network interface 117 , input/output interfaces 119 (e.g., keyboard, mouse, display, printer, etc.), and memory 121 .
- I/O 119may include a variety of interface units and drives for reading, writing, displaying, and/or printing data or files.
- Memory 121may further store operating system software 123 for controlling overall operation of the data processing device 103 , control logic 125 for instructing data server 103 to perform aspects described herein, and other application software 127 providing secondary, support, and/or other functionality which may or may not be used in conjunction with aspects described herein.
- the control logicmay also be referred to herein as the data server software 125 .
- Functionality of the data server softwaremay refer to operations or decisions made automatically based on rules coded into the control logic, made manually by a user providing input into the system, and/or a combination of automatic processing based on user input (e.g., queries, data updates, etc.).
- Memory 121may also store data used in performance of one or more aspects described herein, including a first database 129 and a second database 131 .
- the first databasemay include the second database (e.g., as a separate table, report, etc.). That is, the information can be stored in a single database, or separated into different logical, virtual, or physical databases, depending on system design.
- Devices 105 , 107 , 109may have similar or different architecture as described with respect to device 103 .
- data processing device 103may be spread across multiple data processing devices, for example, to distribute processing load across multiple computers, to segregate transactions based on geographic location, user access level, quality of service (QoS), etc.
- QoSquality of service
- One or more aspectsmay be embodied in computer-usable or readable data and/or computer-executable instructions, such as in one or more program modules, executed by one or more computers or other devices as described herein.
- program modulesinclude routines, programs, objects, components, data structures, etc. that perform particular tasks or implement particular abstract data types when executed by a processor in a computer or other device.
- the modulesmay be written in a source code programming language that is subsequently compiled for execution, or may be written in a scripting language such as (but not limited to) Javascript or ActionScript.
- the computer executable instructionsmay be stored on a computer readable medium such as a nonvolatile storage device.
- Any suitable computer readable storage mediamay be utilized, including hard disks, CD-ROMs, optical storage devices, magnetic storage devices, and/or any combination thereof.
- various transmission (non-storage) media representing data or events as described hereinmay be transferred between a source and a destination in the form of electromagnetic waves traveling through signal-conducting media such as metal wires, optical fibers, and/or wireless transmission media (e.g., air and/or space).
- signal-conducting mediasuch as metal wires, optical fibers, and/or wireless transmission media (e.g., air and/or space).
- signal-conducting mediasuch as metal wires, optical fibers, and/or wireless transmission media (e.g., air and/or space).
- Various aspects described hereinmay be embodied as a method, a data processing system, or a computer program product. Therefore, various functionalities may be embodied in whole or in part in software, firmware and/or hardware or hardware equivalents such as integrated circuits, field programmable gate arrays (F
- FIG. 2depicts an example system architecture including a generic computing device 201 in an illustrative computing environment 200 that may be used according to one or more illustrative aspects described herein.
- Generic computing device 201may be used as a server 206 a in a single-server or multi-server desktop virtualization system (e.g., a remote access or cloud system) configured to provide virtual machines for client access devices.
- the generic computing device 201may have a processor 203 for controlling overall operation of the server and its associated components, including random access memory (RAM) 205 , read-only memory (ROM) 207 , input/output (I/O) module 209 , and memory 215 .
- RAMrandom access memory
- ROMread-only memory
- I/Oinput/output
- I/O module 209may include a mouse, keypad, touch screen, scanner, optical reader, and/or stylus (or other input device(s)) through which a user of generic computing device 201 may provide input, and may also include one or more of a speaker for providing audio output and a video display device for providing textual, audiovisual, and/or graphical output.
- Softwaremay be stored within memory 215 and/or other storage to provide instructions to processor 203 for configuring generic computing device 201 into a special purpose computing device in order to perform various functions as described herein.
- memory 215may store software used by the computing device 201 , such as an operating system 217 , application programs 219 , and an associated database 221 .
- Computing device 201may operate in a networked environment supporting connections to one or more remote computers, such as terminals 240 (also referred to as client devices).
- the terminals 240may be personal computers, mobile devices, laptop computers, tablets, or servers that include many or all of the elements described above with respect to the generic computing device 103 or 201 .
- the network connections depicted in FIG. 2include a local area network (LAN) 225 and a wide area network (WAN) 229 , but may also include other networks.
- LANlocal area network
- WANwide area network
- computing device 201may be connected to the LAN 225 through a network interface or adapter 223 .
- computing device 201When used in a WAN networking environment, computing device 201 may include a modem 227 or other wide area network interface for establishing communications over the WAN 229 , such as computer network 230 (e.g., the Internet). It will be appreciated that the network connections shown are illustrative and other means of establishing a communications link between the computers may be used.
- Computing device 201 and/or terminals 240may also be mobile terminals (e.g., mobile phones, smartphones, PDAs, notebooks, etc.) including various other components, such as a battery, speaker, and antennas (not shown).
- aspects described hereinmay also be operational with numerous other general purpose or special purpose computing system environments or configurations.
- Examples of other computing systems, environments, and/or configurations that may be suitable for use with aspects described hereininclude, but are not limited to, personal computers, server computers, hand-held or laptop devices, multiprocessor systems, microprocessor-based systems, set top boxes, programmable consumer electronics, network PCs, minicomputers, mainframe computers, distributed computing environments that include any of the above systems or devices, and the like.
- one or more client devices 240may be in communication with one or more servers 206 a - 206 n (generally referred to herein as “server(s) 206 ”).
- the computing environment 200may include a network appliance installed between the server(s) 206 and client machine(s) 240 .
- the network appliancemay manage client/server connections, and in some cases can load balance client connections amongst a plurality of backend servers 206 .
- the client machine(s) 240may in some embodiments be referred to as a single client machine 240 or a single group of client machines 240
- server(s) 206may be referred to as a single server 206 or a single group of servers 206 .
- a single client machine 240communicates with more than one server 206
- a single server 206communicates with more than one client machine 240
- a single client machine 240communicates with a single server 206 .
- a client machine 240can, in some embodiments, be referenced by any one of the following non-exhaustive terms: client machine(s); client(s); client computer(s); client device(s); client computing device(s); local machine; remote machine; client node(s); endpoint(s); or endpoint node(s).
- the server 206in some embodiments, may be referenced by any one of the following non-exhaustive terms: server(s), local machine; remote machine; server farm(s), or host computing device(s).
- the client machine 240may be a virtual machine.
- the virtual machinemay be any virtual machine, while in some embodiments the virtual machine may be any virtual machine managed by a Type 1 or Type 2 hypervisor, for example, a hypervisor developed by Citrix Systems, IBM, VMware, or any other hypervisor.
- the virtual machinemay be managed by a hypervisor, while in aspects the virtual machine may be managed by a hypervisor executing on a server 206 or a hypervisor executing on a client 240 .
- Some embodimentsinclude a client device 240 that displays application output generated by an application remotely executing on a server 206 or other remotely located machine.
- the client device 240may execute a virtual machine client agent program or application to display the output in an application window, a browser, or other output window.
- the applicationis a desktop, while in other examples the application is an application that generates or presents a desktop.
- a desktopmay include a graphical shell providing a user interface for an instance of an operating system in which local and/or remote applications can be integrated.
- Applicationsas used herein, are programs that execute after an instance of an operating system (and, optionally, also the desktop) has been loaded.
- the server 206uses a remote presentation protocol or other program to send data to a thin-client or remote-display application executing on the client to present display output generated by an application executing on the server 206 .
- the thin-client or remote-display protocolcan be any one of the following non-exhaustive list of protocols: the Independent Computing Architecture (ICA) protocol developed by Citrix Systems, Inc. of Ft. Lauderdale, Fla.; or the Remote Desktop Protocol (RDP) manufactured by the Microsoft Corporation of Redmond, Wash.
- ICAIndependent Computing Architecture
- RDPRemote Desktop Protocol
- a remote computing environmentmay include more than one server 206 a - 206 n such that the servers 206 a - 206 n are logically grouped together into a server farm 206 , for example, in a cloud computing environment.
- the server farm 206may include servers 206 that are geographically dispersed while and logically grouped together, or servers 206 that are located proximate to each other while logically grouped together.
- Geographically dispersed servers 206 a - 206 n within a server farm 206can, in some embodiments, communicate using a WAN (wide), MAN (metropolitan), or LAN (local), where different geographic regions can be characterized as: different continents; different regions of a continent; different countries; different states; different cities; different campuses; different rooms; or any combination of the preceding geographical locations.
- the server farm 206may be administered as a single entity, while in other embodiments the server farm 206 can include multiple server farms.
- a server farmmay include servers 206 that execute a substantially similar type of operating system platform (e.g., WINDOWS, UNIX, LINUX, iOS, ANDROID, SYMBIAN, etc.)
- server farm 206may include a first group of one or more servers that execute a first type of operating system platform, and a second group of one or more servers that execute a second type of operating system platform.
- Server 206may be configured as any type of server, as needed, e.g., a file server, an application server, a web server, a proxy server, an appliance, a network appliance, a gateway, an application gateway, a gateway server, a virtualization server, a deployment server, a SSL VPN server, a firewall, a web server, an application server or as a master application server, a server executing an active directory, or a server executing an application acceleration program that provides firewall functionality, application functionality, or load balancing functionality.
- Other server typesmay also be used.
- Some embodimentsinclude a first server 206 a that receives requests from a client machine 240 , forwards the request to a second server 206 b , and responds to the request generated by the client machine 240 with a response from the second server 206 b .
- First server 206 amay acquire an enumeration of applications available to the client machine 240 and well as address information associated with an application server 206 hosting an application identified within the enumeration of applications.
- First server 206 acan then present a response to the client's request using a web interface, and communicate directly with the client 240 to provide the client 240 with access to an identified application.
- One or more clients 240 and/or one or more servers 206may transmit data over network 230 , e.g., network 101 .
- FIG. 2shows a high-level architecture of an illustrative desktop virtualization system.
- the desktop virtualization systemmay be single-server or multi-server system, or cloud system, including at least one virtualization server 206 configured to provide virtual desktops and/or virtual applications to one or more client access devices 240 .
- a desktoprefers to a graphical environment or space in which one or more applications may be hosted and/or executed.
- a desktopmay include a graphical shell providing a user interface for an instance of an operating system in which local and/or remote applications can be integrated.
- Applicationsmay include programs that execute after an instance of an operating system (and, optionally, also the desktop) has been loaded.
- Each instance of the operating systemmay be physical (e.g., one operating system per device) or virtual (e.g., many instances of an OS running on a single device).
- Each applicationmay be executed on a local device, or executed on a remotely located device (e.g., remoted).
- FIG. 3represents an enterprise mobility technical architecture 300 for use in an enterprise environment, a BYOD environment, or other mobile environments.
- the architectureenables a user of a mobile device 302 (e.g., as client 107 , 211 , or otherwise) to both access enterprise or personal resources from a mobile device 302 and use the mobile device 302 for personal use.
- the usermay access such enterprise resources 304 or enterprise services 308 using a mobile device 302 that is purchased by the user or a mobile device 302 that is provided by the enterprise to the user.
- the usermay utilize the mobile device 302 for business use only or for business and personal use.
- the mobile devicemay run an iOS operating system, Android operating system, and/or the like.
- the enterprisemay choose to implement policies to manage the mobile device 304 .
- the policiesmay be implanted through a firewall or gateway in such a way that the mobile device may be identified, secured or security verified, and provided selective or full access to the enterprise resources.
- the policiesmay be mobile device management policies, mobile application management policies, mobile data management policies, or some combination of mobile device, application, and data management policies.
- a mobile device 304 that is managed through the application of mobile device management policiesmay be referred to as an enrolled device.
- the operating system of the mobile devicemay be separated into a managed partition 310 and an unmanaged partition 312 .
- the managed partition 310may have policies applied to it to secure the applications running on and data stored in the managed partition.
- the applications running on the managed partitionmay be secure applications.
- the secure applicationsmay be email applications, web browsing applications, software-as-a-service (SaaS) access applications, Windows Application access applications, and the like.
- the secure applicationsmay be secure native applications 314 , secure remote applications 322 executed by a secure application launcher 318 , virtualization applications 326 executed by a secure application launcher 318 , and the like.
- the secure native applications 314may be wrapped by a secure application wrapper 320 .
- the secure application wrapper 320may include integrated policies that are executed on the mobile device 302 when the secure native application is executed on the device.
- the secure application wrapper 320may include meta-data that points the secure native application 314 running on the mobile device 302 to the resources hosted at the enterprise that the secure native application 314 may require to complete the task requested upon execution of the secure native application 314 .
- the secure remote applications 322 executed by a secure application launcher 318may be executed within the secure application launcher application 318 .
- the virtualization applications 326 executed by a secure application launcher 318may utilize resources on the mobile device 302 , at the enterprise resources 304 , and the like.
- the resources used on the mobile device 302 by the virtualization applications 326 executed by a secure application launcher 318may include user interaction resources, processing resources, and the like.
- the user interaction resourcesmay be used to collect and transmit keyboard input, mouse input, camera input, tactile input, audio input, visual input, gesture input, and the like.
- the processing resourcesmay be used to present a user interface, process data received from the enterprise resources 304 , and the like.
- the resources used at the enterprise resources 304 by the virtualization applications 326 executed by a secure application launcher 318may include user interface generation resources, processing resources, and the like.
- the user interface generation resourcesmay be used to assemble a user interface, modify a user interface, refresh a user interface, and the like.
- the processing resourcesmay be used to create information, read information, update information, delete information, and the like.
- the virtualization applicationmay record user interactions associated with a GUI and communicate them to a server application where the server application will use the user interaction data as an input to the application operating on the server.
- an enterprisemay elect to maintain the application on the server side as well as data, files, etc. associated with the application.
- an enterprisemay elect to “mobilize” some applications in accordance with the principles herein by securing them for deployment on the mobile device, this arrangement may also be elected for certain applications. For example, while some applications may be secured for use on the mobile device, others may not be prepared or appropriate for deployment on the mobile device so the enterprise may elect to provide the mobile user access to the unprepared applications through virtualization techniques.
- the enterprisemay have large complex applications with large and complex data sets (e.g. material resource planning applications) where it would be very difficult, or otherwise undesirable, to customize the application for the mobile device so the enterprise may elect to provide access to the application through virtualization techniques.
- the enterprisemay have an application that maintains highly secured data (e.g. human resources data, customer data, engineering data) that may be deemed by the enterprise as too sensitive for even the secured mobile environment so the enterprise may elect to use virtualization techniques to permit mobile access to such applications and data.
- An enterprisemay elect to provide both fully secured and fully functional applications on the mobile device as well as a virtualization application to allow access to applications that are deemed more properly operated on the server side.
- the virtualization applicationmay store some data, files, etc. on the mobile phone in one of the secure storage locations.
- An enterprisefor example, may elect to allow certain information to be stored on the phone while not permitting other information.
- the mobile devicemay have a virtualization application that is designed to present GUI's and then record user interactions with the GUI.
- the applicationmay communicate the user interactions to the server side to be used by the server side application as user interactions with the application.
- the application on the server sidemay transmit back to the mobile device a new GUI.
- the new GUImay be a static page, a dynamic page, an animation, or the like.
- the applications running on the managed partitionmay be stabilized applications.
- the stabilized applicationsmay be managed by a device manager 324 .
- the device manager 324may monitor the stabilized applications and utilize techniques for detecting and remedying problems that would result in a destabilized application if such techniques were not utilized to detect and remedy the problems.
- the secure applicationsmay access data stored in a secure data container 328 in the managed partition 310 of the mobile device.
- the data secured in the secure data containermay be accessed by the secure wrapped applications 314 , applications executed by a secure application launcher 318 , virtualization applications 326 executed by a secure application launcher 318 , and the like.
- the data stored in the secure data container 328may include files, databases, and the like.
- the data stored in the secure data container 328may include data restricted to a specific secure application 330 , shared among secure applications 332 , and the like. Data restricted to a secure application may include secure general data 334 and highly secure data 338 .
- Secure general datamay use a strong form of encryption such as AES 128-bit encryption or the like, while highly secure data 338 may use a very strong form of encryption such as AES 254-bit encryption.
- Data stored in the secure data container 328may be deleted from the device upon receipt of a command from the device manager 324 .
- the secure applicationsmay have a dual-mode option 340 .
- the dual mode option 340may present the user with an option to operate the secured application in an unsecured mode.
- the secure applicationsmay access data stored in an unsecured data container 342 on the unmanaged partition 312 of the mobile device 302 .
- the data stored in an unsecured data containermay be personal data 344 .
- the data stored in an unsecured data container 342may also be accessed by unsecured applications 348 that are running on the unmanaged partition 312 of the mobile device 302 .
- the data stored in an unsecured data container 342may remain on the mobile device 302 when the data stored in the secure data container 328 is deleted from the mobile device 302 .
- An enterprisemay want to delete from the mobile device selected or all data, files, and/or applications owned, licensed or controlled by the enterprise (enterprise data) while leaving or otherwise preserving personal data, files, and/or applications owned, licensed or controlled by the user (personal data). This operation may be referred to as a selective wipe. With the enterprise and personal data arranged in accordance to the aspects described herein, an enterprise may perform a selective wipe.
- the mobile devicemay connect to enterprise resources 304 and enterprise services 308 at an enterprise, to the public Internet 348 , and the like.
- the mobile devicemay connect to enterprise resources 304 and enterprise services 308 through virtual private network connections.
- the virtual private network connectionsmay be specific to particular applications 350 , particular devices, particular secured areas on the mobile device, and the like (e.g., 352 ).
- each of the wrapped applications in the secured area of the phonemay access enterprise resources through an application specific VPN such that access to the VPN would be granted based on attributes associated with the application, possibly in conjunction with user or device attribute information.
- the virtual private network connectionsmay carry Microsoft Exchange traffic, Microsoft Active Directory traffic, HTTP traffic, HTTPS traffic, application management traffic, and the like.
- the virtual private network connectionsmay support and enable single-sign-on authentication processes 354 .
- the single-sign-on processesmay allow a user to provide a single set of authentication credentials, which are then verified by an authentication service 358 .
- the authentication service 358may then grant to the user access to multiple enterprise resources 304 , without requiring the user to provide authentication credentials to each individual enterprise resource 304 .
- the virtual private network connectionsmay be established and managed by an access gateway 360 .
- the access gateway 360may include performance enhancement features that manage, accelerate, and improve the delivery of enterprise resources 304 to the mobile device 302 .
- the access gatewaymay also re-route traffic from the mobile device 302 to the public Internet 348 , enabling the mobile device 302 to access publicly available and unsecured applications that run on the public Internet 348 .
- the mobile devicemay connect to the access gateway via a transport network 362 .
- the transport network 362may be a wired network, wireless network, cloud network, local area network, metropolitan area network, wide area network, public network, private network, and the like.
- the enterprise resources 304may include email servers, file sharing servers, SaaS applications, Web application servers, Windows application servers, and the like.
- Email serversmay include Exchange servers, Lotus Notes servers, and the like.
- File sharing serversmay include SHAREFILE servers, other file sharing services, and the like.
- SaaS applicationsmay include Salesforce, and the like.
- Windows application serversmay include any application server that is built to provide applications that are intended to run on a local Windows operating system, and the like.
- the enterprise resources 304may be premise-based resources, cloud based resources, and the like.
- the enterprise resources 304may be accessed by the mobile device 302 directly or through the access gateway 360 .
- the enterprise resources 304may be accessed by the mobile device 302 via a transport network 362 .
- the transport network 362may be a wired network, wireless network, cloud network, local area network, metropolitan area network, wide area network, public network, private network, and the like.
- the enterprise services 308may include authentication services 358 , threat detection services 364 , device manager services 324 , file sharing services 368 , policy manager services 370 , social integration services 372 , application controller services 374 , and the like.
- Authentication services 358may include user authentication services, device authentication services, application authentication services, data authentication services and the like.
- Authentication services 358may use certificates.
- the certificatesmay be stored on the mobile device 302 , by the enterprise resources 304 , and the like.
- the certificates stored on the mobile device 302may be stored in an encrypted location on the mobile device, the certificate may be temporarily stored on the mobile device 302 for use at the time of authentication, and the like.
- Threat detection services 364may include intrusion detection services, unauthorized access attempt detection services, and the like.
- Unauthorized access attempt detection servicesmay include unauthorized attempts to access devices, applications, data, and the like.
- Device management services 324may include configuration, provisioning, security, support, monitoring, reporting, and decommissioning services.
- File sharing services 368may include file management services, file storage services, file collaboration services, and the like.
- Policy manager services 370may include device policy manager services, application policy manager services, data policy manager services, and the like.
- Social integration services 372may include contact integration services, collaboration services, integration with social networks such as Facebook, Twitter, and LinkedIn, and the like.
- Application controller services 374may include management services, provisioning services, deployment services, assignment services, revocation services, wrapping services, and the like.
- the enterprise mobility technical architecture 300may include an application store 378 .
- the application store 378may include unwrapped applications 380 , pre-wrapped applications 382 , and the like. Applications may be populated in the application store 378 from the application controller 374 .
- the application store 378may be accessed by the mobile device 302 through the access gateway 360 , through the public Internet 348 , or the like.
- the application storemay be provided with an intuitive and easy to use user interface.
- the application store 378may provide access to a software development kit 384 .
- the software development kit 384may provide a user the capability to secure applications selected by the user by wrapping the application as described previously in this description. An application that has been wrapped using the software development kit 384 may then be made available to the mobile device 302 by populating it in the application store 378 using the application controller 374 .
- the enterprise mobility technical architecture 300may include a management and analytics capability.
- the management and analytics capabilitymay provide information related to how resources are used, how often resources are used, and the like.
- Resourcesmay include devices, applications, data, and the like. How resources are used may include which devices download which applications, which applications access which data, and the like. How often resources are used may include how often an application has been downloaded, how many times a specific set of data has been accessed by an application, and the like.
- FIG. 4is another illustrative enterprise mobility management system 400 . Some of the components of the mobility management system 300 described above with reference to FIG. 3 have been omitted for the sake of simplicity.
- the architecture of the system 400 depicted in FIG. 4is similar in many respects to the architecture of the system 300 described above with reference to FIG. 3 and may include additional features not mentioned above.
- the left hand siderepresents an enrolled mobile device 402 (e.g., client 107 , 212 , 302 , etc.) with a client agent 404 , which interacts with gateway server 406 (which includes access gateway and application controller functionality) to access various enterprise resources 408 and services 409 such as Exchange, Sharepoint, PKI Resources, Kerberos Resources, and Certificate Issuance Service, as shown on the right hand side above.
- gateway server 406which includes access gateway and application controller functionality
- enterprise resources 408 and services 409such as Exchange, Sharepoint, PKI Resources, Kerberos Resources, and Certificate Issuance Service
- the mobile device 402may also interact with an enterprise application store (e.g., StoreFront) for the selection and downloading of applications.
- Client agent 404may, for example, be a software application executing on a client device that facilitates communications with remote resources and/or virtualized resources.
- Gateway server 406may, for example, be a server or other resource that provides access to enterprise resources and/or cloud resources.
- the client agent 404acts as the UI (user interface) intermediary for Windows apps/desktops hosted in an Enterprise data center, which are accessed using the HDX/ICA display remoting protocol, or any other remoting protocol.
- the client agent 404also supports the installation and management of native applications on the mobile device 402 , such as native iOS or Android applications.
- native applications 410email, browser, wrapped application
- a managed applicationis one that is capable of being controlled based on and operated in accordance with independently defined and communicated policy files.
- the secure IPC links 412 between the native applications 410 and client agent 404represent a management channel, which allows client agent to supply policies to be enforced by the application management framework 414 “wrapping” each application.
- the IPC channel 412also allows client agent 404 to supply credential and authentication information that enables connectivity and SSO to enterprise resources 408 .
- the IPC channel 412allows the application management framework 414 to invoke user interface functions implemented by client agent 404 , such as online and offline authentication.
- Communications between the client agent 404 and gateway server 406are essentially an extension of the management channel from the application management framework 414 wrapping each native managed application 410 .
- the application management framework 414requests policy information from client agent 404 , which in turn requests it from gateway server 406 .
- the application management framework 414requests authentication, and client agent 404 logs into the gateway services part of gateway server 406 (also known as NetScaler Access Gateway).
- Client agent 404may also call supporting services on gateway server 406 , which may produce input material to derive encryption keys for the local data vaults 416 , or provide client certificates which may enable direct authentication to PKI protected resources, as more fully explained below.
- the application management framework 414“wraps” each managed application 410 . This may be incorporated via an explicit build step, or via a post-build processing step.
- the application management framework 414may “pair” with client agent 614 on first launch of an application 410 to initialize the secure IPC channel and obtain the policy for that application.
- the application management framework 414may enforce relevant portions of the policy that apply locally, such as the client agent login dependencies and some of the containment policies that restrict how local OS services may be used, or how they may interact with the application 410 .
- the application management framework 414may use services provided by client agent 404 over the secure IPC channel 412 to facilitate authentication and internal network access.
- Key management for the private and shared data vaults 416(containers) may be also managed by appropriate interactions between the managed applications 410 and client agent 404 .
- Vaults 416may be available only after online authentication, or may be made available after offline authentication if allowed by policy. First use of vaults 416 may require online authentication, and offline access may be limited to at most the policy refresh period before online authentication is again required.
- Network access to internal resourcesmay occur directly from individual managed applications 410 through access gateway 406 .
- the application management framework 414is responsible for orchestrating the network access on behalf of each application 410 .
- Client agent 404may facilitate these network connections by providing suitable time limited secondary credentials obtained following online authentication. Multiple modes of network connection may be used, such as reverse web proxy connections and end-to-end VPN-style tunnels 418 .
- the mail and browser managed applications 410have special status and may make use of facilities that might not be generally available to arbitrary wrapped applications.
- the mail applicationmay use a special background network access mechanism that allows it to access Exchange over an extended period of time without requiring a full AD logon.
- the browser applicationmay use multiple private data vaults to segregate different kinds of data.
- gateway server 406(including its gateway services) in some cases will not need to validate AD passwords. It can be left to the discretion of an enterprise whether an AD password is used as an authentication factor for some users in some situations. Different authentication methods may be used if a user is online or offline (i.e., connected or not connected to a network).
- Step up authenticationis a feature wherein gateway server 406 may identify managed native applications 410 that are allowed to have access to highly classified data requiring strong authentication, and ensure that access to these applications is only permitted after performing appropriate authentication, even if this means a re-authentication is required by the user after a prior weaker level of login.
- the vaults 416may be encrypted so that all on-device data including files, databases, and configurations are protected.
- the keysmay be stored on the server (gateway server 406 ), and for off-line vaults, a local copy of the keys may be protected by a user password.
- a minimum of AES 256 encryption algorithmbe utilized.
- a logging featuremay be included, wherein all security events happening inside an application 410 are logged and reported to the backend. Data wiping may be supported, such as if the application 410 detects tampering, associated encryption keys may be written over with random data, leaving no hint on the file system that user data was destroyed.
- Screenshot protectionis another feature, where an application may prevent any data from being stored in screenshots. For example, the key window's hidden property may be set to YES. This may cause whatever content is currently displayed on the screen to be hidden, resulting in a blank screenshot where any content would normally reside.
- Local data transfermay be prevented, such as by preventing any data from being locally transferred outside the application container, e.g., by copying it or sending it to an external application.
- a keyboard cache featuremay operate to disable the autocorrect functionality for sensitive text fields.
- SSL certificate validationmay be operable so the application specifically validates the server SSL certificate instead of it being stored in the keychain.
- An encryption key generation featuremay be used such that the key used to encrypt data on the device is generated using a passphrase supplied by the user (if offline access is required). It may be XORed with another key randomly generated and stored on the server side if offline access is not required.
- Key derivation functionsmay operate such that keys generated from the user password use KDFs (key derivation functions, notably PBKDF2) rather than creating a cryptographic hash of it. The latter makes a key susceptible to brute force or dictionary attacks.
- one or more initialization vectorsmay be used in encryption methods.
- An initialization vectorwill cause multiple copies of the same encrypted data to yield different cipher text output, preventing both replay and cryptanalytic attacks. This will also prevent an attacker from decrypting any data even with a stolen encryption key if the specific initialization vector used to encrypt the data is not known.
- authentication then decryptionmay be used, wherein application data is decrypted only after the user has authenticated within the application.
- Another featuremay relate to sensitive data in memory, which may be kept in memory (and not in disk) only when it's needed. For example, login credentials may be wiped from memory after login, and encryption keys and other data inside objective-C instance variables are not stored, as they may be easily referenced. Instead, memory may be manually allocated for these.
- An inactivity timeoutmay be implemented, wherein after a policy-defined period of inactivity, a user session is terminated.
- Data leakage from application management framework 414may be prevented in other ways. For example, when an application 410 is put in the background, the memory may be cleared after a predetermined (configurable) time period. When backgrounded, a snapshot may be taken of the last displayed screen of the application to fasten the foregrounding process. The screenshot may contain confidential data and hence should be cleared.
- OTPone time password
- ADactive directory
- Another security featurerelates to the use of an OTP (one time password) 420 without the use of an AD (active directory) 422 password for access to one or more applications.
- OTPone time password
- some usersdo not know (or are not permitted to know) their AD password, so these users may authenticate using an OTP 420 such as by using a hardware OTP system like SecurID (OTPs may be provided by different vendors also, such as Entrust or Gemalto).
- OTPsSecurID
- a textis sent to the user with an OTP 420 . In some cases, this may be implemented only for online use, with a prompt being a single field.
- An offline passwordmay be implemented for offline authentication for those applications 410 for which offline use is permitted via enterprise policy.
- an enterprisemay want the enterprise application store to be accessed in this manner.
- the client agent 404may require the user to set a custom offline password and the AD password is not used.
- Gateway server 406may provide policies to control and enforce password standards with respect to the minimum length, character class composition, and age of passwords, such as described by the standard Windows Server password complexity requirements, although these requirements may be modified.
- Another featurerelates to the enablement of a client side certificate for certain applications 410 as secondary credentials (for the purpose of accessing PKI protected web resources via the application management framework micro VPN feature).
- an applicationsuch as a corporate email application may utilize such a certificate.
- certificate-based authentication using ActiveSync protocolmay be supported, wherein a certificate from the client agent 404 may be retrieved by gateway server 406 and used in a keychain.
- Each managed applicationmay have one associated client certificate, identified by a label that is defined in gateway server 406 .
- Gateway server 406may interact with an enterprise special purpose web service to support the issuance of client certificates to allow relevant managed applications to authenticate to internal PKI protected resources.
- the client agent 404 and application management framework 414may be enhanced to support obtaining and using client certificates for authentication to internal PKI protected network resources. More than one certificate may be supported, such as to match various levels of security and/or separation requirements.
- the certificatesmay be used by the mail and browser managed applications, and ultimately by arbitrary wrapped applications (provided those applications use web service style communication patterns where it is reasonable for application management framework to mediate HTTPS requests).
- Application management framework client certificate support on iOSmay rely on importing a PKCS 12 BLOB (Binary Large Object) into the iOS keychain in each managed application for each period of use.
- Application management framework client certificate supportmay use a HTTPS implementation with private in-memory key storage. The client certificate will never be present in the iOS keychain and will not be persisted except potentially in “online-only” data value that is strongly protected.
- Mutual SSLmay also be implemented to provide additional security by requiring that a mobile device 402 is authenticated to the enterprise, and vice versa.
- Virtual smart cards for authentication to gateway server 406may also be implemented.
- the full support featurerelates to an ability to do full Kerberos login to AD 422 , using an AD password or trusted client certificate, and obtain Kerberos service tickets to respond to HTTP negotiate authentication challenges.
- the limited support featurerelates to constrained delegation in AFEE, where AFEE supports invoking Kerberos protocol transition so it can obtain and use Kerberos service tickets (subject to constrained delegation) in response to HTTP negotiate authentication challenges. This mechanism works in reverse web proxy (a.k.a. CVPN) mode, and when HTTP (but not HTTPS) connections are proxied in VPN and MicroVPN mode.
- Another featurerelates to application container locking and wiping, which may automatically occur upon jail-break or rooting detections, and occur as a pushed command from administration console, and may include a remote wipe functionality even when an application 410 is not running.
- a multi-site architecture or configuration of the enterprise application store and application controllermay be supported that allows users to be service from one of several different locations in case of failure.
- managed applications 410may be allowed to access a certificate and private key via an API (example OpenSSL).
- Trusted managed applications 410 of an enterprisemay be allowed to perform specific Public Key operations with an application's client certificate and private key.
- Various use casesmay be identified and treated accordingly, such as when an application behaves like a browser and no certificate access is required, when an application reads a certificate for “who am I,” when an application uses the certificate to build a secure session token, and when an application uses private keys for digital signing of important data (e.g. transaction log) or for temporary data encryption.
- FIG. 5depicts a flowchart that illustrates a method of creating an application tunnel from a managed browser to one or more enterprise resources in accordance with one or more illustrative aspects discussed herein.
- the method illustrated in FIG. 5 and/or one or more steps thereofmay be performed by a computing device (e.g., generic computing device 201 ).
- the method illustrated in FIG. 5 and/or one or more steps thereofmay be embodied in computer-executable instructions that are stored in a computer-readable medium, such as a non-transitory computer-readable memory.
- a computing devicee.g., a mobile computing device, such as a laptop computer, tablet computer, smart phone, or other type of mobile device
- a managed browsere.g., by opening and/or otherwise initiating execution of a managed browser
- the managed browsermay be a web browser that is configured to provide one or more enterprise security features (e.g., mobile device management features, mobile application management features, policy acquisition and enforcement features, etc.). Additionally or alternatively, the managed browser may extend various enterprise security features for use with mobile device applications that may be configured to run within the browser.
- an enterprisemay require some or all of its employees and/or other users to install and use the managed browser on their respective mobile devices in a bring-your-own-device (BYOD) scheme to reduce enterprise security risks.
- the managed browsercan, for instance, be used to enable mobile device users to access a corporate intranet and/or other enterprise resources without connecting to a virtual private network (VPN).
- the managed browsermay implement and/or provide application tunneling functionalities, such as those discussed in greater detail below, to enable such access to a corporate intranet and/or other enterprise resources.
- the managed browsermay additionally or alternatively be configured to provide secure browsing and caching of data obtained from at least one enterprise resource.
- the managed browsermay be further configured to securely cache the obtained data (e.g., in one or more local caches, which may be encrypted using one or more encryption protocols).
- the managed browsermay be further configured to provide secure browsing of the obtained data (e.g., by controlling and providing access to the obtained data based on validation of one or more authentication credentials, based on compliance with and/or enforcement of one or more mobile device management and/or mobile application management policies, etc.).
- the managed browsermay be configured to provide at least one managed mode in which one or more policies are applied to the managed browser.
- the one or more policiesmay, for instance, be configured to limit one or more functions of the managed browser.
- the one or more policiesmay selectively restrict the types of information that can be accessed using the managed browser, the resources (e.g., enterprise resources, network resources, etc.) that can be accessed using the managed browser, the users that can access information using the managed browser, the times at which the managed browser can be used to access specific types of information, the locations at which the managed browser can be used to access specific types of information, and/or other may impose other restrictions.
- At least one policy of the one or more policiesmay limit and/or otherwise restrict application tunneling functionalities of the managed browser, as discussed below.
- the managed browsermay be configured to provide at least one unmanaged mode in which the one or more policies (which, e.g., may be applied to the browser in the managed mode) might not be applied to the managed browser, such that the managed browser may operate without the restrictions that might be imposed by the one or more policies.
- a request to access one or more enterprise resources via the managed browsermay be received.
- the computing devicemay receive a request to access one or more enterprise resources via the managed browser.
- a requestmay, for instance, be based on and/or correspond to user input received by the computing device via the managed browser (e.g., based on a user selecting a link and/or otherwise requesting access to a network resource using the managed browser).
- At least one application tunnelmay be created from the managed browser to the one or more enterprise resources.
- the computing devicemay create and/or otherwise establish one or more VPN-style tunnels to enterprise servers and/or other enterprise resources that may, for instance, enable the managed browser to securely access and obtain enterprise data from the enterprise servers and/or other enterprise resources.
- application tunnelingmay include techniques in which one network protocol (e.g., the delivery protocol) encapsulates a different network protocol. By using application tunneling, a secure path may be provided through an untrusted network.
- creating the at least one application tunnelmay include creating a first application tunnel from the managed browser to a first enterprise resource, and creating a second application tunnel from the managed browser to a second enterprise resource, where the second enterprise resource is different from the first enterprise resource.
- the computing devicemay create a different individual application tunnel for each enterprise resource that may be accessed by the managed browser.
- the first enterprise resourcemay have a first security level and the second enterprise resource may have a second security level different from the first security level.
- the second enterprise resourcemay have a higher security level than the first enterprise resource, and additional authentication credentials and/or more secure access protocols and/or encryption methods may be needed to access the second enterprise resource (e.g., as compared to accessing the first enterprise resource).
- the at least one application tunnelmay be created (e.g., in step 515 ) based on one or more policies that may be applied to the managed browser. For example, in creating the at least one application tunnel, the managed browser and/or the computing device on which the managed browser is running may create the at least one application tunnel in accordance with one or more policies that may be applied to the managed browser and/or may selectively limit and/or otherwise restrict the managed browser's ability to create and/or use application tunnels.
- At least one policy of the one or more policiesmay selectively restrict the types of information that can be accessed using an application tunnel, the resources that can be accessed using an application tunnel, the users that can access information using an application tunnel, the times at which the managed browser can create an application tunnel, the locations at which the managed browser can create an application tunnel, and/or other may impose other restrictions.
- enterprise data from the one or more enterprise resourcesmay be obtained via the at least one application tunnel.
- the computing devicemay obtain enterprise data from the one or more enterprise resources via the application tunnel(s) created in step 515 .
- the computing devicealso may provide access to the obtained enterprise data via the managed browser (e.g., by causing some or all of the obtained enterprise data to be displayed in the managed browser).
- one or more policiesmay be applied to the managed browser.
- the one or more policiesmay be configured to limit at least one function of the managed browser.
- the one or more policiesmay define certain circumstances in which certain function(s) of the managed browser are to be selectively disabled, and the computing device may detect and/or otherwise identify these circumstances (e.g., based on device state information, as discussed below) and subsequently disable the function(s) in accordance with the one or more policies.
- Some examples of the functions of the managed browser that may be limited by a policy in some instancesinclude cut-and-paste functions, instant messaging functions, and video chat functions. While these functions are listed here as examples of the functions that may be limited in some instances, other functions may be similarly limited in other instances.
- one or more policiesmay be applied to the managed browser, and at least one policy of the one or more policies may be configured to limit usage of the obtained enterprise data.
- the one or more policiesmay define certain circumstances in which the enterprise data (e.g., the enterprise data obtained via the application tunnel(s) by the computing device and/or the managed browser in step 520 ) can only be used in certain ways, and the computing device may detect and/or otherwise identify these circumstances (e.g., based on device state information, as discussed below) and subsequently restrict and/or otherwise control the way(s) in which the data can be used in accordance with the one or more policies.
- At least one policy of the one or more policiesmay be configured to limit the circumstances in which the obtained enterprise data can be copied and pasted (e.g., from the managed browser into another application).
- at least one policy of the one or more policiesmay be configured to limit the circumstances in which the obtained enterprise data can be saved or printed (e.g., by the managed browser and/or by the computing device).
- At least one policy of the one or more policiesmay depend on device state information.
- the limit(s) on the function(s) of the managed browsere.g., as imposed by the one or more policies
- the limit(s) on the way(s) in which enterprise data may be used by the managed browsere.g., as additionally or alternatively imposed by the one or more policies
- Such state informationmay, for instance, be collected and/or monitored by a mobile resource management (MRM) agent that is configured to run on the computing device (e.g., as a background application, service, or process) and which may, for instance, incorporate one or more aspects of client agent 404 (discussed above).
- MRM agentmay, for instance, provide and/or be configured to provide mobile device management (MDM) functionalities, mobile application management (MAM) functionalities, and/or other functionalities.
- MDMmobile device management
- MAMmobile application management
- the MRM agentmay be configured to collect and/or monitor device-level state information, such as state information that is indicative of the operating systems and/or applications that are stored on and/or running on the device, state information that is indicative of the network connections that are available to and/or being used by the device, and/or state information that is indicative of the current location of where the device is located and/or being used (e.g., in terms of geographic coordinates; in terms of semantic labels, such as “home” or “work;” etc.).
- device-level state informationsuch as state information that is indicative of the operating systems and/or applications that are stored on and/or running on the device, state information that is indicative of the network connections that are available to and/or being used by the device, and/or state information that is indicative of the current location of where the device is located and/or being used (e.g., in terms of geographic coordinates; in terms of semantic labels, such as “home” or “work;” etc.).
- state informationWhile these types of state information are listed here as examples of the types of state information that may be collected and/or monitored (e.g., by the MRM agent, by one or more other applications or services or processes on the computing device, etc.) in some instances, additional and/or alternative types of state information may be similarly collected and/or monitored in other instances. In addition, any and/or all of this state information may be used (e.g., by the computing device and/or by the managed browser) in applying and/or enforcing policies on the managed browser, such as the policies discussed above.
- FIG. 6depicts a flowchart that illustrates a method of extending a managed browser session across a device cloud in accordance with one or more illustrative aspects discussed herein.
- the method illustrated in FIG. 6 and/or one or more steps thereofmay be performed by a computing device (e.g., generic computing device 201 ).
- the method illustrated in FIG. 6 and/or one or more steps thereofmay be embodied in computer-executable instructions that are stored in a computer-readable medium, such as a non-transitory computer-readable memory.
- a computing devicee.g., a mobile computing device, such as a laptop computer, tablet computer, smart phone, or other type of mobile device
- a computing devicemay load a managed browser, similar to how such a managed browser may be loaded in step 505 (discussed above).
- the managed browsermay, for instance, be configured to provide at least one managed mode in which one or more policies are applied to the managed browser, and the one or more policies may be configured to limit one or more functions of the managed browser, as discussed above.
- the managed browsermay, in some embodiments, be configured to provide secure browsing and caching of data obtained from at least one enterprise resource.
- a connection to at least one other computing devicemay be established to initiate a device cloud.
- the computing devicemay establish a network connection to one or more other computing devices to initiate a device cloud.
- a device cloudmay, for instance, enable two or more computing devices to be used in combination with each other to perform a single function or task.
- the devicesmay be used by the same user and/or both may be located near each other (e.g., within a predetermined distance of each other) and/or near the user (e.g., within a predetermined distance of the user).
- a device cloudmay be used to provide a function that is not supported by one of the user's devices, but is supported by another one of the user's devices. For example, a user of a laptop computer may wish to conduct a video conference with another person, but the laptop computer might not include a camera. If the user also has a smart phone (or other computing device) that includes a camera, however, a device cloud may be used to dynamically link the functionalities provided by the two devices so that they may be used in providing the video conference.
- a device cloudmay be established such that the user's smart phone may be used as a video input device for the video conference (which may, e.g., be facilitated by a video conferencing plug-in, applet, web application, etc. that may be running within the managed browser), while the user's laptop computer can be used to perform other functions that may be involved in conducting the video conference (e.g., establishing the connection to the other person's device(s), providing text-based chat functionalities, etc.). While this example illustrates some ways in which a device cloud may be used to extend the functionalities of one or more devices in some embodiments, such a device cloud may be used in other ways to extend additional and/or alternative functionalities of various devices in other embodiments.
- a session of the managed browsermay be extended across the device cloud.
- the computing devicemay extend a session of the managed browser (e.g., a current session of the managed browser with which a user of the computing device is interacting) across the device cloud (e.g., the device cloud created in step 610 ).
- extending the session of the managed browser across the device cloudmay include causing at least one other managed browser to be loaded on the at least one other computing device, and sharing session data with the at least one other managed browser.
- the computing devicemay initially cause instance(s) of the managed browser to be loaded on the other device(s) participating in the device cloud.
- the computing devicemay share session data with the instance(s) of the managed browser that are running on the other device(s) participating in the device cloud.
- the computing devicemay, for instance, send some or all of the information that is currently being used and/or displayed by the managed browser on the computing device, which may include enterprise data and/or non-enterprise data.
- the computing devicemay receive information that may be subsequently displayed and/or otherwise used by the managed browser on the computing device.
- one or more policiesmay be applied to the managed browser, and the one or more policies may be configured to limit at least one function of the managed browser.
- the computing device and/or software running on the computing devicemay apply one or more policies to the managed browser that are configured to limit function(s) of the managed browser, as discussed above.
- one or more policiesmay be applied to the managed browser, and the one or more policies may be configured to limit the device cloud.
- the computing device and/or software running on the computing devicemay, in some instances, apply one or more policies to the managed browser that are configured limit various aspects of the device cloud (e.g., the device cloud created in step 610 ).
- at least one policy of the one or more policiesmay be configured to allocate at least one role to the at least one other computing device.
- the computing device and/or the software running on the computing devicemay define, apply, and/or enforce at least one policy that is configured to allocate particular role(s) in the device cloud to the other computing device(s) that are participating in the device cloud.
- the mobile device management policiesmay allocate a video capturing role to the smart phone involved in the device cloud, and the mobile device management policies may allocate a connection maintenance role to the laptop computer involved in the device cloud.
- the connection to the at least one other computing devicemay be established based on at least one policy of the one or more policies that may be applied to the managed browser.
- the managed browser and/or the computing device on which the managed browser is runningmay connect to and/or exchange data with the at least one other computing device in accordance with one or more policies that may be applied to the managed browser.
- the one or more policiesmay define certain circumstances in which the managed browser's ability to initiate the device cloud may be selectively enabled, selectively disabled, and/or otherwise restricted.
- At least one policy of the one or more policiesmay selectively restrict the types of information that can be exchanged with the other computing device(s), the users that can access information exchanged with the other computing device(s), the times at which the managed browser can exchange information with the other computing device(s), the locations at which the managed browser can exchange information with the other computing device(s), and/or other may impose other restrictions. Any and/or all of these restrictions may limit the circumstances in which the computing device can establish a connection to the at least one other computing device and/or may otherwise limit the circumstances in which the device cloud can be initiated.
- establishing the connection to the at least one other computing devicemay include evaluating state information associated with the at least one other computing device, and determining, based on the evaluated state information, to allow the at least one other computing device to participate in the device cloud. For example, in establishing the connection to the at least one other computing device (e.g., in step 610 ), the computing device may obtain and/or evaluate state information associated with the at least one other computing device.
- state informationmay, for instance, describe various aspects of the current device state of the at least one other computing device, such as the applications that may be installed and/or running on the at least one other computing device, the networks to which the at least one other computing device is connected to, the location of the at least one other computing device, and/or other considerations.
- the computing devicemay determine, based on evaluating this state information, whether to allow the at least one other computing device to participate in the device cloud. Such a determination may, for instance, be based on one or more policies. For example, one or more policies may dictate that the computing device may allow the at least one other computing device to participate in the device cloud if the state information associated with the at least one other computing device indicates that the device is or is not located in a certain location, does or does not have certain applications installed and/or running on the device, is or is not connected to one or more specific networks, and/or the like.
- FIG. 7depicts a flowchart that illustrates a method of selectively disabling an operational mode of a managed browser in accordance with one or more illustrative aspects discussed herein.
- the method illustrated in FIG. 7 and/or one or more steps thereofmay be performed by a computing device (e.g., generic computing device 201 ).
- the method illustrated in FIG. 7 and/or one or more steps thereofmay be embodied in computer-executable instructions that are stored in a computer-readable medium, such as a non-transitory computer-readable memory.
- a managed browsermay be loaded.
- a computing devicee.g., a mobile computing device, such as a laptop computer, tablet computer, smart phone, or other type of mobile device
- the managed browsermay, for instance, be configured to provide at least one managed mode in which one or more policies are applied to the managed browser, and the one or more policies may be configured to limit one or more functions of the managed browser, as discussed above.
- the managed browsermay, in some embodiments, be configured to provide secure browsing and caching of data obtained from at least one enterprise resource.
- the managed browsermay be a dual-mode application that has a managed mode and an unmanaged mode.
- the managed mode of the managed browsermay be configured to provide access to enterprise data
- the unmanaged mode of the managed browsermay be configured to limit access to enterprise data.
- the managed browsermay apply specific content filters, restrict specific downloads, and/or block specific plug-ins, whereas in the unmanaged mode, the managed browser might not apply such filters, restrict such downloads, and/or block such plug-ins.
- the computing device and/or other software running on the computing devicemay selectively disable the managed mode of the managed browser, as discussed below, such that the managed browser might only be able to run and/or continue running in the unmanaged mode (e.g., until the managed mode of the managed browser is re-enabled by the computing device and/or by the other appropriate software running on the computing device).
- an MRM agentmay selectively disable the managed mode of the managed browser, as discussed below, such that the managed browser might only be able to run and/or continue running in the unmanaged mode (e.g., until the managed mode of the managed browser is re-enabled by the computing device and/or by the other appropriate software running on the computing device).
- step 710device state information may be obtained.
- the computing devicemay obtain state information that is indicative of the current state of the computing device.
- state informationmay be obtained by an MRM agent running on the computing device, such as the MRM agent discussed in the examples above.
- the device state informationmay include information identifying one or more applications that are present on the computing device. For example, in obtaining device state information (e.g., in step 710 ), the computing device and/or the MRM agent running on the computing device may inspect one or more storage devices (which may, e.g., be connected to and/or otherwise accessible to the computing device) and/or installation logs (which may, e.g., be maintained by the computing device) to determine what application(s) are stored on the computing device, installed on the computing device, previously run on the computing device, and/or currently running on the computing device.
- storage deviceswhich may, e.g., be connected to and/or otherwise accessible to the computing device
- installation logswhich may, e.g., be maintained by the computing device
- the device state informationmay include information identifying one or more network connections that are used by the computing device.
- the computing device and/or the MRM agent running on the computing devicemay inspect one or more network interfaces and/or other network devices (which may, e.g., be connected to and/or otherwise usable by the computing device) and/or one or more connection logs (which may, e.g., be maintained by the computing device) to determine what network(s) are accessible to and/or in range of the computing device, what network(s) that computing device has previously connected to, and/or what network(s) the computing device is currently connected to.
- the device state informationmay include information identifying a current location of the computing device.
- the computing device and/or the MRM agent running on the computing devicemay determine and/or cause one or more other components (e.g., a GPS receiver, other positioning components, etc.) and/or devices to determine a current position of the computing device.
- the location informationmay include geographic coordinates that are indicative of the current position of the computing device.
- the location informationmay include semantic labels that are indicative of the current position of the computing device relative to one or more user-specific landmarks (e.g., “home” or “work”). Any and/or all of this location may, for instance, be used by the computing device and/or by the MRM agent running on the computing device in applying and/or enforcing one or more location-based mobile device management policies.
- step 715it may be determined, based on the device state information, whether to selectively disable one or more operational modes of the managed browser. For example, in step 715 , the computing device may determine, based on the device state information obtained in step 710 , whether to selectively disable one or more operational modes of the managed browser. As discussed above, the managed browser may, in some instances, be a dual-mode application that has a managed mode and an unmanaged mode. Thus, in some instances, the computing device may, in step 715 , determine whether to selectively disable the managed mode of the managed browser based on the device state information obtained in step 710 .
- the computing devicemay determine whether to selectively disable the managed mode of the managed browser based on information identifying one or more applications that are present on the computing device, information identifying one or more network connections that are used by the computing device, and/or information identifying a current location of the computing device.
- the computing devicemay additionally or alternatively evaluate one or more policies in combination with the device state information in determining whether to selectively disable a mode of the managed browser (e.g., the managed mode of the managed browser).
- step 715If it is determined, in step 715 , not to disable one or more operational modes of the managed browser, then the method may end. Additionally or alternatively, the method may continue in a loop, such that steps 710 and 715 may be periodically repeated (e.g., to obtain updated device state information and/or reevaluate the updated device state information to determine whether to selectively disable one or more operational modes of the managed browser).
- the at least one operational mode of the managed browsermay be disabled.
- the computing devicemay disable the at least one operational mode of the managed browser (e.g., the mode(s) determined to be disabled in step 715 ) and/or cause the at least one operational mode of the managed browser to be disabled.
- the managed modemay, for example, be disabled by the computing device (and/or be caused to be disabled by the computing device) in step 720 .
- causing the at least one managed mode to be disabledmay include causing the managed browser to enter a second mode different from the at least one managed mode. For example, in disabling the managed mode of the managed mode of the managed browser and/or otherwise causing the managed mode of the managed browser to be disabled (e.g., in step 720 ), the computing device may cause the managed browser to enter a second mode that is different from the managed mode that the managed browser was previously operating in. In some instances, the second mode may be another managed mode that is simply different from the managed mode that the managed browser was previously operating in (e.g., because different policies are applied to the managed browser).
- the second modemay, in some instances, be a managed mode in which a second set of one or more policies is applied to the managed browser, where the second set of one or more policies includes at least one policy different from the one or more policies that are applied to the managed browser in the at least one managed mode.
- the second mode(which, e.g., the managed browser may enter after the at least one managed mode is disabled) may be an unmanaged mode in which the managed browser is no longer managed by at least one device manager.
- the computing devicemay cause the managed browser to enter an unmanaged mode, such as the unmanaged mode discussed above, in which the managed browser might not be managed by at least one device manager.
- a device managermay, for instance, be a mobile resource management agent that is running on the device and is configured to apply and/or enforce one or more policies on the managed browser and/or other applications, services, and/or functions of the device.
- access to one or more resourcesmay be blocked in the unmanaged mode.
- the managed browser and/or the computing devicemay block access to specific resources, such as specific enterprise resources. Such block may, for instance, prevent a user of the managed browser from accessing enterprise resources and/or other specific resources while the managed browser is operating in an unmanaged mode in which policy enforcement, monitoring, and/or other security features might not be applied and/or available to ensure the security of enterprise information that might otherwise be accessed using the managed browser.
- the managed browser and/or the computing devicealso may, in the unmanaged mode, block access to specific information that may be cached locally on the device. For example, during the unmanaged mode, such blocking may prevent the managed browser from accessing locally-cached data that was originally obtained from enterprise resources, such as locally-cached enterprise application store information and/or other locally-cached enterprise information.
- the managed browsermay be configured to transition from the unmanaged mode back to the at least one managed mode based on updated device state information. For example, after entering the unmanaged mode, the managed browser and/or the computing device may be configured to monitor and periodically reevaluate current device state information to determine whether the managed browser can reenter the managed mode (e.g., in which one or more policies may be applied to the managed browser, the managed browser may be managed by the device manager, etc.). If, for instance, the managed browser and/or the computing device determines that specific circumstances are satisfied, for instance, based on the state information, the computing device may cause the managed browser to switch back to the managed mode.
- the managed browser and/or the computing devicemay be configured to monitor and periodically reevaluate current device state information to determine whether the managed browser can reenter the managed mode (e.g., in which one or more policies may be applied to the managed browser, the managed browser may be managed by the device manager, etc.). If, for instance, the managed browser and/or the computing device determines that specific circumstances
- the computing device and/or the managed browsermay, for instance, evaluate the current device state information in view of one or more policies, which may include the one or more policies that were evaluated in determining to switch the managed browser to the unmanaged mode in the first place.
- FIG. 8depicts a flowchart that illustrates a method of applying one or more mobile device management policies to a managed browser in accordance with one or more illustrative aspects discussed herein.
- the method illustrated in FIG. 8 and/or one or more steps thereofmay be performed by a computing device (e.g., generic computing device 201 ).
- the method illustrated in FIG. 8 and/or one or more steps thereofmay be embodied in computer-executable instructions that are stored in a computer-readable medium, such as a non-transitory computer-readable memory.
- a computing devicee.g., a mobile computing device, such as a laptop computer, tablet computer, smart phone, or other type of mobile device
- a computing devicemay load a managed browser, similar to how such a managed browser may be loaded in step 505 (discussed above).
- the managed browsermay, for instance, be configured to provide at least one managed mode in which one or more policies are applied to the managed browser, and the one or more policies may be configured to limit one or more functions of the managed browser, as discussed above.
- the managed browsermay, in some embodiments, be configured to provide secure browsing and caching of data obtained from at least one enterprise resource.
- one or more policiesmay be received.
- the computing devicemay receive one or more policies.
- the one or more policiesmay, for instance, be mobile device management policies that define permitted, prohibited, and/or restricted functions based on different sets of circumstances that may be evaluated using device state information (e.g., device state information that is obtained and/or monitored by the computing device and/or by an MRM agent running on the computing device).
- device state informatione.g., device state information that is obtained and/or monitored by the computing device and/or by an MRM agent running on the computing device.
- the policiesmay be used in enforcing device-state-based behavior limitations on various functions, including various functions of the managed browser.
- the one or more policiesmay be received from a policy server.
- the computing devicemay, in step 810 , connect to and/or receive a number of policies from a policy server.
- the policy servermay, for instance, be part of an enterprise network infrastructure, and may be connected to and/or included in one or more enterprise resources that may be accessed by the managed browser in accordance with the policies that are received (e.g., by the computing device in step 810 ).
- the one or more policiesmay be applied to the managed browser.
- the computing devicemay application the one or more policies (e.g., as received in step 810 ) to the managed browser, such that certain functions of the managed browser may be selectively enabled and/or disabled (e.g., based on device state information being obtained and/or monitored by the computing device and/or by an MRM agent running on the computing device).
- the one or more policiesmay be applied to the managed browser based on identity information associated with a user of the computing device. For example, in applying the one or more policies to the managed browser (e.g., in step 815 ), the computing device may request and/or obtain identity information associated with a current user of the computing device. Such identity information may, for instance, be obtained via one or more authentication prompts that are configured to prompt the user to provide his or her login information and/or other authentication credentials.
- policiesBy applying policies to the managed browser based on identity information, the specific functions that are selectively enabled, disabled, and/or restricted (e.g., by the one or more policies being applied to the managed browser) for the current user of the managed browser and/or the computing device may be more particularly tailored to the current user in view of their identity.
- the one or more policiesmay be applied to the managed browser based on role information associated with a user of the computing device.
- the computing devicemay request and/or obtain identity information and/or role information associated with a current user of the computing device.
- the role informationmay, for instance, specify the role(s) of the current user within the enterprise (e.g., sales, engineering, legal, accounting, executive, etc.).
- the computing devicemay, for example, determine role information for the current user of the computing device based on identity information for the current user of the computing device (e.g., by using the identity information to access and/or look up role information for the user in one or more databases, directories, and/or enterprise resources).
- identity informationfor the current user of the computing device
- the specific functions that are selectively enabled, disabled, and/or restrictede.g., by the one or more policies being applied to the managed browser
- the computing devicemay be more particularly tailored to the needs of and/or access level of the current user in view their role(s) within the enterprise.
- the computing devicemay determine whether the current user of the computing device is a doctor or a nurse (e.g., by obtaining and/or analyzing identity information for the current user of the computing device). If the computing device determines that the current user of the computing device is a doctor, the computing device may apply a first set of policies to the managed browser, and if the computing device determines that the current user of the computing device is a nurse, the computing device may apply a second set of policies to the managed browser that is different from the first set of policies.
- the second set of policiesmay, for instance, selectively enable, disable, and/or restrict additional and/or alternative functions of the managed browser than the first set of policies, based on the differences between the nurse's role in the healthcare enterprise and the doctor's role in the healthcare enterprise. For example, as a result of the policies that are applied to the managed browser, the doctor may, for instance, be able to use the managed browser on the computing device to access specific resources that the nurse might not be able to access.
- the computing devicemay determine whether the current user of the computing device is an attorney or other professional within a group of professionals that has been screened from specific cases and/or other matters being handling by the law firm. If the computing device determines that the current user of the computing device is within the group of professionals that has been screened, then the computing device map apply a first set of policies to the managed browser, and if the computing device determines that the current user of the computing device is not within the group of professionals that has been screened, then the computing device may apply a second set of policies to the managed browser that is different from the first set of policies.
- the second set of policiesmay, for instance, selectively enable, disable, and/or restrict additional and/or alternative functions of the managed browser than the first set of policies, based on the differences between certain professionals' roles in the legal enterprise. For example, as a result of the policies that are applied to the managed browser, certain lawyers may be able to use the managed browser on the computing device to access specific resources that other lawyers within the law firm might not be able to access.
- applying the one or more policies to the managed browsermay include controlling access to one or more enterprise resources that are accessible via the managed browser.
- the computing devicemay control access to the enterprise resource(s) that can be accessed using the managed browser.
- at least one policy of the one or more policiesmay, for instance, selectively enable, disable, and/or limit access to particular enterprise resource(s), such as particular databases, servers, and/or other enterprise resources (which may, e.g., be connected to and/or part of an enterprise infrastructure).
- such a policymay, for instance, depend on device state information (which may, e.g., include information identifying one or more applications that are present on the computing device, information identifying one or more network connections that are used by the computing device, and/or information identifying a current location of the computing device), such that access to particular enterprise resource(s) may be controlled based on the current state of the computing device.
- device state informationwhich may, e.g., include information identifying one or more applications that are present on the computing device, information identifying one or more network connections that are used by the computing device, and/or information identifying a current location of the computing device
- applying the one or more policies to the managed browsermay include controlling use of information obtained from one or more enterprise resources via the managed browser.
- the computing devicemay control how information obtained from the enterprise resource(s), such as information obtained from the enterprise resource(s) using the managed browser, can be used (e.g., by the managed browser and/or by other applications, services, and/or processes on the computing device).
- At least one policy of the one or more policiesmay, for instance, selectively allow, prohibit, and/or otherwise restrict the ability to save information obtained from the enterprise resource(s), the ability to print information obtained from the enterprise resource(s), the ability to cut, copy, and/or paste information obtained from the enterprise resource(s), the ability to edit information obtained from the enterprise resource(s), and/or other abilities to interact with and/or use the information obtained from the enterprise resource(s).
- such a policymay, for instance, depend on device state information (which may, e.g., include information identifying one or more applications that are present on the computing device, information identifying one or more network connections that are used by the computing device, and/or information identifying a current location of the computing device), such that usage of particular information obtained from the enterprise resource(s) may be controlled based on the current state of the computing device.
- device state informationwhich may, e.g., include information identifying one or more applications that are present on the computing device, information identifying one or more network connections that are used by the computing device, and/or information identifying a current location of the computing device
- FIG. 9depicts a flowchart that illustrates a method of providing access to a secure document container via a managed browser in accordance with one or more illustrative aspects discussed herein.
- the method illustrated in FIG. 9 and/or one or more steps thereofmay be performed by a computing device (e.g., generic computing device 201 ).
- the method illustrated in FIG. 9 and/or one or more steps thereofmay be embodied in computer-executable instructions that are stored in a computer-readable medium, such as a non-transitory computer-readable memory.
- a managed browsermay be loaded.
- a computing devicee.g., a mobile computing device, such as a laptop computer, tablet computer, smart phone, or other type of mobile device
- the managed browsermay, for instance, be configured to provide at least one managed mode in which one or more policies are applied to the managed browser, and the one or more policies may be configured to limit one or more functions of the managed browser, as discussed above.
- the managed browsermay, in some embodiments, be configured to provide secure browsing and caching of data obtained from at least one enterprise resource.
- a request to access one or more enterprise resources via the managed browsermay be received.
- the computing devicemay receive a request to access one or more enterprise resources via the managed browser.
- a requestmay, for instance, be based on and/or correspond to user input received by the computing device via the managed browser (e.g., based on a user selecting a link and/or otherwise requesting access to a network resource using the managed browser).
- step 915enterprise data from the one or more enterprise resources may be obtained based on the request.
- the computing devicemay connect to, request, and subsequently receive and/or otherwise obtain information from the one or more enterprise resources based on the request received in step 910 .
- the obtained enterprise datamay be stored in a secure document container.
- the computing devicemay store the enterprise data obtained in step 915 in a secure document container.
- the secure document containermay be a data repository on the computing device that is configured to securely store enterprise data received by the computing device from one or more enterprise resources.
- one or more mobile device management policiesmay define certain circumstances in which access to the secure document container is to be restricted, modified, and/or otherwise controlled, and the computing device and/or an MRM agent running on the computing device may detect these circumstances based on device state information and subsequently restrict, modify, and/or otherwise control access to the secure document container in accordance with the policies.
- other aspects of the secure document containere.g., other than access to the secure document container
- access to the secure document containermay be provided via the managed browser.
- the computing devicemay provide access to the secure document container via the managed browser.
- the computing devicemay, for instance, cause the managed browser to display and/or otherwise present one or more user interfaces that are configured to allow the enterprise data and/or other information stored in the secure document container to be viewed, edited, and/or otherwise accessed.
- the computing devicemay cause the managed browser to display and/or otherwise present one or more user interfaces that allow a user of the computing device to browse the information stored in the secure document container, view particular files and/or other information stored in the secure document container, edit the information stored in the secure document container, delete the information stored in the secure document container, and/or otherwise interact with and/or access the information that is stored in the secure document container.
- datamay be selectively wiped from the secure document container.
- the computing devicemay selectively wipe and/or otherwise delete information from the secure document container.
- the computing devicemay selectively wipe data from the secure document container based on device state information, one or more policies, and/or other factors and/or circumstances that may be evaluated and/or detected by the computing device and/or by an MRM agent running on the computing device.
- the computing devicemay wipe some data from the secure document container, such as the enterprise data obtained in step 915 , while leaving other data, such as other data, including other enterprise data, which may be stored in the secure document container.
- the computing devicemay wipe data from the secure document container that was received and/or stored during a certain time period (e.g., within the last four hours) while leaving other data (e.g., data that was received and/or stored during a different time period).
- the computing devicemay wipe data from the secure document container that was received and/or stored in connection with the managed browser and/or a particular session of the managed browser, while leaving other data (e.g., data that is associated with other applications and/or other session(s) of the managed browser).
- selectively wiping data from the secure document containermay include deleting the enterprise data obtained from the one or more enterprise resources based on the request.
- the computing devicemay delete the enterprise data obtained from the enterprise resource(s) in step 915 .
- the computing devicemay, for instance, delete the enterprise data obtained during the particular browsing session(s) in which the enterprise data was obtained, as well as any other information that may have been obtained during these browsing session(s), while leaving and/or otherwise preserving other data that may be stored in the secure document container (which, e.g., may have been obtained during other browsing session(s), may be associated with other application(s), etc.).
- datamay be selectively wiped from the secure document container when the managed browser is closed.
- the computing devicemay, in some instances, selectively wipe data from the secure document container in response to and/or otherwise based on the managed browser being closed (e.g., when a user of the computing device closes the managed browser, when a user of the computing devices closes a tab of the managed browser and/or otherwise closes a particular session of the managed browser, when the managed browser is closed or caused to be closed by another application, service, or process on the computing device, such as an MRM agent running on the computing device, etc.).
- datamay be selectively wiped from the secure document container based on one or more policies.
- the computing devicemay, in some instances, selectively wipe data from the secure document container based on one or more mobile device management policies.
- one or more mobile device management policiesmay define certain circumstances in which certain type(s) of data are to be selectively wiped from the secure document container, and the computing device and/or an MRM agent running on the computing device may detect these circumstances based on device state information and subsequently wipe data from the secure document container in accordance with the policies.
- the computing device and/or an MRM agent running on the computing devicemay selectively wipe enterprise data from the secure document container that was obtained from one or more enterprise resources using the managed browser (e.g., in step 915 ) and subsequently stored in the secure document container (e.g., in step 920 ).
- datamay be selectively wiped from the secure document container based on the one or more policies that are applied to the managed browser when the managed browser is operating in the managed mode.
- the computing devicemay, in some instances, selectively wipe data from the secure document container based on the one or more policies that are applied to the managed browser in the managed mode, and at least one such policy may define specific circumstances in which specific data (which may, e.g., have been obtained using the managed browser) should be selectively deleted from the secure document container.
- these specific circumstancesmay be detected by the computing device and/or by an MRM agent running on the computing device based on device state information, as in the examples discussed above.
- FIG. 10depicts a flowchart that illustrates a method of obtaining enterprise data based on a single sign-on credential and providing access to the data via a managed browser in accordance with one or more illustrative aspects discussed herein.
- the method illustrated in FIG. 10 and/or one or more steps thereofmay be performed by a computing device (e.g., generic computing device 201 ).
- the method illustrated in FIG. 10 and/or one or more steps thereofmay be embodied in computer-executable instructions that are stored in a computer-readable medium, such as a non-transitory computer-readable memory.
- a computing devicee.g., a mobile computing device, such as a laptop computer, tablet computer, smart phone, or other type of mobile device
- a computing devicemay load a managed browser, similar to how such a managed browser may be loaded in step 505 (discussed above).
- the managed browsermay, for instance, be configured to provide at least one managed mode in which one or more policies are applied to the managed browser, and the one or more policies may be configured to limit one or more functions of the managed browser, as discussed above.
- the managed browsermay, in some embodiments, be configured to provide secure browsing and caching of data obtained from at least one enterprise resource.
- a single sign-on (SSO) credential that is associated with at least one user accountmay be received.
- the computing devicemay receive a single sign-on credential, and the single sign-on credential may be linked to and/or otherwise associated with a particular user of the computing device and/or a particular user account (which may, e.g., be utilized in accessing and/or using the computing device and/or other resources, such as enterprise resources and/or other network resources).
- the single sign-on credentialmay be an authentication credential that is configured to be used in accessing at least two different enterprise resources (e.g., various enterprise websites, databases, servers, other resources, etc.).
- the single sign-on credentialmay be received when the user is logging into a user account on the computing device, logging into an application on the computing device, logging into a website being accessed via the computing device, interacting with an authentication prompt presented on the computing device, and/or in other ways.
- the single sign-on credentialmay be received via the managed browser, for example, in connection with a request or attempt to access one or more enterprise resources and/or other resources or information using the managed browser.
- enterprise data from one or more enterprise resourcesmay be obtained based on the SSO credential.
- the computing devicemay connect to, request, and subsequently receive and/or otherwise obtain information from one or more enterprise resources using the SSO credential received in step 1010 .
- the SSO credentialmay, for instance, be used in authenticating with the enterprise resources, requesting rights-controlled information from the enterprise resources, and/or otherwise receiving the enterprise data from the enterprise resources.
- the computing devicemay initiate a connection to a specific enterprise resource, which may challenge the managed browser to provide authentication information.
- the managed browsermay provide the SSO credential (e.g., as received in step 1010 ) to the enterprise resource in order to authenticate with the enterprise resource and/or obtain information from the enterprise resource.
- access to the obtained enterprise datamay be provided via the managed browser.
- the computing devicemay provide access to the enterprise data obtained in step 1015 via the managed browser.
- the computing devicemay, for instance, cause the managed browser to display and/or otherwise present one or more user interfaces that are configured to allow the enterprise data to be viewed, edited, and/or otherwise accessed.
- the computing devicemay cause the managed browser to display and/or otherwise present one or more user interfaces that allow a user of the computing device to browse the obtained enterprise data, view the obtained enterprise data, edit the obtained enterprise data, delete the obtained enterprise data, and/or otherwise interact with and/or access the obtained enterprise data.
- the computing device and/or the managed browser running on the computing devicemay, depending on one or more policies and/or device state information, respond to one or more authentication challenges (which may, e.g., be presented by one or more enterprise resources) using the SSO credential without user involvement. For instance, such an authentication challenge may be automatically addressed by the managed browser and/or the computing device using the SSO credential based on one or more policies and/or device state information.
- the specific authentication challenges and/or types of authentication challenges that may be automatically addressed in this mannermay change depending on the one or more policies and/or the current context of the device (which may, e.g., be indicated by device state information, as in the examples discussed above).
- obtaining the enterprise data from the one or more enterprise resources based on the SSO credentialmay include: receiving an authentication challenge from at least one enterprise resource of the one or more enterprise resources; determining, based on at least one policy of the one or more policies, whether to provide the SSO credential to the at least one enterprise resource in response to the authentication challenge; and based on determining to provide the SSO credential to the at least one enterprise resource in response to the authentication challenge, providing the SSO credential to the at least one enterprise resource.
- the computing device and/or the managed browser running on the computing devicemay receive an authentication challenge from an enterprise resource (which the managed browser may, e.g., be attempting to access).
- an authentication challengemay, for instance, typically require a user to provide one or more authentication credentials in order to access the corresponding resource.
- the computing device and/or the managed browser running on the computing devicemay determine, based on one or more policies, whether to provide the SSO credential to the enterprise resource to respond to the authentication challenge. For instance, the computing device and/or the managed browser may such a determination on one or more policies that define specific circumstances in which the managed browser can automatically respond to such an authentication challenge using the SSO credential. In addition, the computing device and/or the managed browser may evaluate these circumstances based on device state information, similar to how such device state information may be evaluated in the examples discussed above.
- the computing device and/or the managed browsermay provide the SSO credential to the enterprise resource. For instance, the computing device and/or the managed browser may send the SSO credential (which may, e.g., have been received in step 1010 ) to the enterprise resource in order to automatically respond to the authentication challenge, which in turn may enable the computing device and/or the managed browser to access information from and/or stored by the enterprise resource. In addition, the computing device and/or the managed browser may send the SSO credential in this way without user involvement.
- the computing device and/or the managed browsermay send the SSO credential without prompting the user to provide any authentication credentials and/or without even notifying the user that the SSO credential is being provided to the enterprise resource.
- the computing device and/or the managed browsermay prompt the user to provide one or more authentication credentials (which may then, e.g., be used by the computing device and/or the managed browser in responding to the authentication challenge).
- the computing device and/or the managed browser running on the computing devicemay generate an authentication prompt that is configured to receive at least one authentication credential from a user of the computing device.
- providing access to the obtained enterprise data via the managed browsermay include enforcing one or more policies based on the SSO credential.
- the computing devicemay obtain one or more policies based on the SSO credential (e.g., by downloading, receiving, and/or otherwise obtaining one or more policies from a policy server and/or other enterprise resources based on the SSO credential), select applicable policies based on the SSO credential (e.g., by selectively activating, deactivating, and/or enforcing policies that are applicable to and/or appropriate for the current user of the computing device, in view of the identity information that may be associated with the SSO credential), and/or impose one or more behavior limitations on the managed browser in accordance with the policies (e.g., by enforcing behavior limitations on the managed browser that may be applicable to and/or appropriate for the identity and/or role of the user in view of the SSO credential).
- the one or more policiesmay be configured to limit one or more functions of the managed browser.
- the one or more policiesmay define certain circumstances in which certain function(s) of the managed browser are to be selectively disabled for certain users, and the computing device may detect and/or otherwise identify these circumstances (e.g., based on device state information) and subsequently disable the function(s) in accordance with the one or more policies and based on the SSO credential received in step 1010 .
- some examples of the functions of the managed browser that may be limited by a policyinclude cut-and-paste functions, instant messaging functions, and video chat functions.
- these functionsare listed here as examples of the functions that may be limited in some instances, other functions may be similarly limited in other instances.
- the one or more policiesmay be configured to limit access to the obtained enterprise data.
- the one or more policiesmay define certain circumstances in which the enterprise data (e.g., the enterprise data obtained in step 1015 ) can only be accessed and/or used in certain ways, and the computing device may detect and/or otherwise identify these circumstances (e.g., based on device state information) and subsequently restrict and/or otherwise control the way(s) in which the data can be accessed and/or used in accordance with the one or more policies and based on the SSO credential received in step 1010 .
- At least one policy of the one or more policiesmay be configured to limit the circumstances in which the obtained enterprise data can be copied and pasted (e.g., from the managed browser into another application).
- at least one policy of the one or more policiesmay be configured to limit the circumstances in which the obtained enterprise data can be saved or printed (e.g., by the managed browser and/or by the computing device).
- enforcement of at least one policy of the one or more policiesmay depend on device state information.
- the limit(s) on the function(s) of the managed browsere.g., as imposed by the one or more policies
- the limit(s) on the way(s) in which enterprise data may be accessed and/or used by the managed browsere.g., as additionally or alternatively imposed by the one or more policies
- Such state informationmay, for instance, be collected and/or monitored by an MRM agent, as in the examples discussed above, that is configured to run on the computing device (e.g., as a background application, service, or process).
- the MRM agentmay be configured to collect and/or monitor device-level state information, such as state information that is indicative of the operating systems and/or applications that are stored on and/or running on the device, state information that is indicative of the network connections that are available to and/or being used by the device, and/or state information that is indicative of the current location of where the device is located and/or being used.
- any and/or all of this state informationmay be used (e.g., by the computing device and/or by the managed browser) in applying and/or enforcing policies on the managed browser, such as the policies discussed above, in combination with the SSO credential (which may, e.g., be received in step 1010 , as discussed above).
- FIG. 11depicts a flowchart that illustrates a method of providing access to an application store via a managed browser in accordance with one or more illustrative aspects discussed herein.
- the method illustrated in FIG. 11 and/or one or more steps thereofmay be performed by a computing device (e.g., generic computing device 201 ).
- the method illustrated in FIG. 11 and/or one or more steps thereofmay be embodied in computer-executable instructions that are stored in a computer-readable medium, such as a non-transitory computer-readable memory.
- a managed browsermay be loaded.
- a computing devicee.g., a mobile computing device, such as a laptop computer, tablet computer, smart phone, or other type of mobile device
- the managed browsermay, for instance, be configured to provide at least one managed mode in which one or more policies are applied to the managed browser, and the one or more policies may be configured to limit one or more functions of the managed browser, as discussed above.
- the managed browsermay, in some embodiments, be configured to provide secure browsing and caching of data obtained from at least one enterprise resource.
- a request to access an application store via the managed browsermay be received.
- the computing devicemay receive a request to access an application store via the managed browser.
- a requestmay, for instance, be based on and/or correspond to user input received by the computing device via the managed browser (e.g., based on a user selecting a link and/or otherwise requesting access to an application store using the managed browser).
- the managed browsermay include an icon or toolbar that may be configured to cause the application store to be displayed within the managed browser upon selection of the icon or toolbar.
- a specific policy that is applied to the managed browsermay dynamically direct the browser to the correct application store based on one or more factors, such as the context (e.g., the state of the browser and/or various other programs that may be running on the device), user account information, and/or user role information.
- the application store(which, e.g., is requested to be accessed in step 1110 ) may be an enterprise application store that is configured to provide enterprise applications to one or more mobile computing devices.
- the enterprise application storealso may be configured to provide one or more mobile device management policies and/or policy updates to various devices.
- the application storemay be configured to provide one or more applications that can be downloaded by one or more mobile computing devices and/or other user devices and that can subsequently be run natively on such user devices.
- the application storealso may provide information that can be used to access one or more web applications and/or one or more virtualized applications.
- the application storemay provide a pointer and/or location information that can be used by the managed browser to locate and/or connect to a server that is running and/or otherwise configured to provide such a web application or virtualized application.
- the pointer and/or location informationmay also be passed by the managed browser to a different application on the computing device to execute the web application or the virtualized application.
- step 1115enterprise data from the application store may be obtained based on the request.
- the computing devicemay connect to, request, and subsequently receive and/or otherwise obtain information from the application store based on the request received in step 1110 .
- step 1120at least part of the obtained enterprise data may be presented via the managed browser.
- the computing devicemay present, via the managed browser, at least part of the enterprise data obtained from the application store in step 1115 .
- the computing devicemay, for instance, cause the managed browser to display and/or otherwise present one or more user interfaces that are configured to allow the enterprise data obtained from the application store to be viewed, interacted with, and/or otherwise accessed.
- the computing devicemay cause the managed browser to display and/or otherwise present one or more user interfaces that allow a user to view applications and/or other content available in the application store, select and/or download such applications and/or other content, and/or otherwise interact with application store data.
- presenting at least part of the obtained enterprise datamay include causing an application download interface to be provided via the managed browser.
- the computing devicemay display and/or cause the managed browser to display and/or otherwise present an application download interface.
- the application download interfacemay, for instance, include information about one or more applications that may be available for download via the application store and/or may include one or more links and/or other controls that are selectable to download the available application(s).
- presenting at least part of the obtained enterprise datamay include providing access to at least one application from the application store, where the at least one application is only accessible via the managed browser.
- the computing devicemay provide access to an application in the application store that is only available (e.g., for access, download, etc.) when the application store is accessed with the managed browser (e.g., and not with a conventional and/or non-managed browser).
- certain types of information associated with a specific application(which may, e.g., be available in the application store and/or may have been obtained from the application store) might only be provided to a user device when the user device is accessing the application store via the managed browser.
- access to enterprise templates, specific data sets, co-worker reviews, information about specific projects for which the application has been used, lists of other users and/or employees that have downloaded the application, and/or other types of information associated with a specific applicationmight only be provided via the managed browser.
- This informationmay, for instance, be considered enterprise specific, and thus access to the information may be restricted through use of the managed browser.
- presenting at least part of the obtained enterprise datamay include causing a virtualized session of at least one application to be provided via the managed browser.
- the computing devicemay cause a virtualized session of an application to be provided via the managed browser.
- the computing devicemay cause the managed browser to display and/or otherwise provide one or more virtualized user interfaces of the application, which may be obtained from and/or remotely executed by the application store and/or one or more enterprise resources.
- the managed browsermay be further configured to monitor device state information and enforce one or more policies based on the device state information.
- the managed browsermay be further configured to monitor device state information and enforce one or more policies (e.g., on the managed browser itself and/or on one or more other applications that may be running on the device).
- the managed browsermay be configured to operate as and/or provide functionalities similar to the MRM agent discussed above, such that the managed browser may operate on the computing device not only as a browser that can securely access enterprise resources, but also as a mobile resource management agent that can monitor device state information and enforce policies on various applications and/or other functions of the device based on the state information.
- FIG. 12depicts a flowchart that illustrates a method of obtaining and controlling enterprise data with a managed browser in accordance with one or more illustrative aspects discussed herein.
- the method illustrated in FIG. 12 and/or one or more steps thereofmay be performed by a computing device (e.g., generic computing device 201 ).
- the method illustrated in FIG. 12 and/or one or more steps thereofmay be embodied in computer-executable instructions that are stored in a computer-readable medium, such as a non-transitory computer-readable memory.
- a computing devicee.g., a mobile computing device, such as a laptop computer, tablet computer, smart phone, or other type of mobile device
- a computing devicemay load a managed browser, similar to how such a managed browser may be loaded in step 505 (discussed above).
- the managed browsermay, for instance, be configured to provide at least one managed mode in which one or more policies are applied to the managed browser, and the one or more policies may be configured to limit one or more functions of the managed browser, as discussed above.
- the managed browsermay, in some embodiments, be configured to provide secure browsing and caching of data obtained from at least one enterprise resource.
- a request to access one or more enterprise resources via the managed browsermay be received.
- the computing devicemay receive a request to access one or more enterprise resources via the managed browser.
- a requestmay, for instance, be based on and/or correspond to user input received by the computing device via the managed browser (e.g., based on a user selecting a link and/or otherwise requesting access to a network resource using the managed browser).
- step 1215enterprise data from the one or more enterprise resources may be obtained based on the request.
- the computing devicemay connect to, request, and subsequently receive and/or otherwise obtain information from the one or more enterprise resources based on the request received in step 1210 .
- the obtained enterprise datamay be controlled based on one or more policies.
- the computing devicemay control the enterprise data obtained in step 1215 using one or more mobile device management policies.
- the one or more mobile device management policiesmay, for instance, define certain circumstances in which certain functions (e.g., certain functions of the managed browser, certain functions involving the obtained enterprise data, etc.) may be allowed, prohibited, and/or otherwise restricted. Additionally or alternatively, the computing device may be configured to evaluate these circumstances based on device state information and subsequently control the enterprise data in accordance with the one or more policies.
- the obtained enterprise datamay be controlled using the same set of policies (e.g., a first set of policies) that may be applied to the managed browser in the managed mode.
- the obtained enterprise datamay be controlling using a different set of policies (e.g., a second set of policies different from the first set of policies) than may be applied to the managed browser in the managed mode.
- the policies that are used in controlling the enterprise datamay be specific to and/or grouped for one or more particular industries, such as healthcare, finance, law, engineering, and so on.
- industriessuch as healthcare, finance, law, engineering, and so on.
- a cohesive group of industry-specific policiescan be applied to the managed browser to create an industry-specific browser.
- a cohesive group of healthcare-related policiesmay be applied to the managed browser to create a “healthcare browser” in which, for instance, the policies may operate to block certain functionality to meet regulatory and/or privacy concerns.
- the policies that are used in controlling the enterprise datamay include one or more policies that allow and/or cause logging functions and/or other monitoring functions to be selectively applied and/or executed. Such logging functions and/or other monitoring functions may be applied to the managed browser and/or to one or more other applications and/or services running on the computing device.
- one or more policiesmay monitor and/or selectively filter network traffic during certain times, in certain locations, and/or based on the current context of the device. Additionally or alternatively, one or more policies may monitor and/or selectively filter network traffic based on user role information, performance information (which may, e.g., include device performance and/or network performance), and/or one or more other factors.
- controlling the obtained enterprise datamay include controlling the managed browser with a mobile resource management (MRM) agent, such as a mobile resource management (MRM) agent, that is configured to apply at least one policy to at least one other application on the computing device.
- MRMmobile resource management
- an MRM agentthat may be running on the computing device may be further configured to apply various mobile device management policies to other applications that are stored on and/or running on the computing device.
- Such an MRM agentmay, for instance, incorporate one or more aspects of client agent 404 (discussed above).
- At least one policy of the one or more policiesmay be configured to selectively disable one or more functions of the managed browser based on device state information.
- Some examples of the functions of the managed browser that may be selectively disabled by such a policy in some instancesinclude cut-and-paste functions, instant messaging functions, and video chat functions. While these functions are listed here as examples of the functions that may be selectively disabled in some instances, other functions may be similarly disabled in other instances.
- the device state information that may be used in evaluating the one or more policiesmay include information identifying one or more applications that are present on the computing device, information identifying one or more network connections that are used by the computing device, and/or information identifying a current location of the computing device, as in the examples discussed above.
- controlling the obtained enterprise data based on one or more policiesmay include controlling access to the obtained enterprise data.
- controlling access to the obtained enterprise datamay, in some instances, include controlling use of the obtained enterprise data.
- the one or more policiesmay define certain circumstances in which the enterprise data (e.g., the enterprise data obtained using the managed browser in step 1215 ) can only be accessed and/or used in certain ways, and the computing device may detect and/or otherwise identify these circumstances (e.g., based on device state information) and subsequently restrict and/or otherwise control the way(s) in which the data can be accessed and/or used in accordance with the one or more policies.
- At least one policy of the one or more policiesmay be configured to limit the circumstances in which the obtained enterprise data can be copied and pasted (e.g., from the managed browser into another application).
- at least one policy of the one or more policiesmay be configured to limit the circumstances in which the obtained enterprise data can be saved or printed (e.g., by the managed browser and/or by the computing device).
- the managed browsermay be configured to receive one or more policy updates for the MRM agent from a policy management server.
- the managed browsermay, in some instances, receive one or more policy updates (which may, e.g., include new and/or updated policies to be applied to the managed browser, other applications, and/or other aspects of the computing device).
- policy updatesmay, for instance, be received from a policy management server, and after receiving such a policy update, the managed browser may provide the policy update and its associated information to the MRM agent (which may, e.g., then receive and apply the new and/or updated policies as appropriate).
- controlling the obtained enterprise datamay include selectively blocking access to the obtained enterprise data when the managed browser is operating in an unmanaged mode. For example, after obtaining enterprise data from one or more enterprise resources (e.g., in step 1215 ), the managed browser and/or the computing device on which the managed browser is running may selectively block access to the obtained enterprise data when the managed browser is operating in an unmanaged mode (in which, e.g., one or more policies might not be applied to the browser, as discussed in the examples above).
- the managed browser and/or the computing device on which the managed browser is runningmay be configured such that a user of the computing device might only be able to access the obtained enterprise data with the managed browser while the managed browser is running in the managed mode, and may be prevented from accessing the obtained enterprise data via the managed browser while the managed browser is not running in the managed mode (e.g., when the managed browser is running in the unmanaged mode).
- FIG. 13depicts a flowchart that illustrates a method of administering one or more policies for a managed browser in accordance with one or more illustrative aspects discussed herein.
- the method illustrated in FIG. 13 and/or one or more steps thereofmay be performed by a computing device (e.g., generic computing device 201 ).
- the method illustrated in FIG. 13 and/or one or more steps thereofmay be embodied in computer-executable instructions that are stored in a computer-readable medium, such as a non-transitory computer-readable memory.
- the methodmay begin at step 1305 in which at least one policy to be applied to a managed browser on one or more user computing devices may be received.
- a policymay be received by a server computing device (which may, e.g., incorporate one or more aspects of generic computing device 201 and/or may be configured to provide policy management functionalities for an enterprise organization and/or its various users).
- the policymay be received by the server computing device from an administrative user and/or from a computing device being operated by such a user, who may be defining one or more new and/or updated policies to be applied to the managed browser(s) on various user computing devices.
- the managed browsermay, for instance, be configured to provide at least one managed mode in which one or more policies are applied to the managed browser, and the one or more policies may be configured to limit one or more functions of the managed browser. Additionally, the managed browser may, in some embodiments, be configured to provide secure browsing and caching of data obtained from at least one enterprise resource.
- At least one policy updatemay be provided to at least one user computing device of the one or more user computing devices based on the at least one policy.
- the server computing devicemay provide a policy update to a user computing device based on the policy received in step 1305 .
- the server computing devicemay, for instance, connect to, push, and/or otherwise send information to the user computing device about the new and/or updated policy, which may have been received by the server computing device in step 1305 .
- the at least one policy updatemay be configured to cause the at least one user computing device to apply the at least one received policy to a managed browser on the at least one user computing device.
- the policy update(which may, e.g., be provided by the server computing device to a user computing device in step 1310 ) may be configured to cause the user computing device to apply the policy (which may, e.g., be received by the server computing device in step 1305 ) to a managed browser on the user computing device.
- a managed browsermay, for example, be running, stored, and/or otherwise present on the user computing device that receives the policy update from the server computing device (e.g., in step 1310 ).
- the policy(which may, e.g., be received in step 1305 by the server computing device, and subsequently provided to and received by the user computing device via the policy update in step 1310 ) may define one or more specific rules that may be enforced on the managed browser and/or on the user computing device running the managed browser. Such rules may, for instance, be enforced in specific circumstances that may be defined in terms of and/or evaluated based on device state information (which may, e.g., include information about what other applications are running, installed on, and/or otherwise present on the user computing device; where the user computing device is located; what networks the user computing device is connected to; etc.)
- device state informationwhich may, e.g., include information about what other applications are running, installed on, and/or otherwise present on the user computing device; where the user computing device is located; what networks the user computing device is connected to; etc.
- the at least one received policymay include one or more content filtering rules.
- the policy received by the server computing device in step 1305may include one or more content filtering rules.
- a content filtering rulemay, for instance, control a managed browser's ability to access specific network resources, which may include specific enterprise resources.
- a content filtering rulemay selectively block and/or selectively allow access to specific types of content by the managed browser based on device state information (which may, e.g., include information about what other applications are running, installed on, and/or otherwise present on the user computing device; where the user computing device is located; what networks the user computing device is connected to; etc., as discussed above) and/or other specific criteria.
- the at least one received policymay include one or more caching rules.
- the policy received by the server computing device in step 1305may include one or more content caching rules.
- Such a content caching rulemay, for instance, control a managed browser's ability to cache specific types of content, which may include specific types of content received from one or more enterprise resources, specific types of content received from other network resources (e.g., web content, cookies, etc.), and/or other types of information.
- a content caching rulemay selectively block and/or selectively allow caching of specific types of content by the managed browser based on device state information (which may, e.g., include information about what other applications are running, installed on, and/or otherwise present on the user computing device; where the user computing device is located; what networks the user computing device is connected to; etc., as discussed above) and/or other specific criteria.
- device state informationwhich may, e.g., include information about what other applications are running, installed on, and/or otherwise present on the user computing device; where the user computing device is located; what networks the user computing device is connected to; etc., as discussed above
- the at least one received policymay include one or more plugin rules.
- the policy received by the server computing device in step 1305may include one or more plug-in management rules.
- Such a plug-in management rulemay, for instance, control a managed browser's ability to access, execute, and/or otherwise use specific plug-ins (which may, e.g., include various types of applications, extensions, applets, scripts, and/or other types of plug-ins).
- a plug-in management rulemay selectively prevent and/or selectively enable access, execution, and/or use of one or more specific plug-ins by the managed browser based on device state information (which may, e.g., include information about what other applications are running, installed on, and/or otherwise present on the user computing device; where the user computing device is located; what networks the user computing device is connected to; etc., as discussed above) and/or other specific criteria.
- device state informationwhich may, e.g., include information about what other applications are running, installed on, and/or otherwise present on the user computing device; where the user computing device is located; what networks the user computing device is connected to; etc., as discussed above
- the at least one received policymay include one or more credential management rules.
- the policy received by the server computing device in step 1305may include one or more credential management rules.
- Such a credential management rulemay, for instance, control a managed browser's ability to use specific credentials, which may include one or more single sign-on (SSO) credentials, for instance, in accessing one or more resources.
- SSOsingle sign-on
- a credential management rulemay selectively prevent and/or enable access to and/or use of one or more specific credentials by the managed browser based on device state information (which may, e.g., include information about what other applications are running, installed on, and/or otherwise present on the user computing device; where the user computing device is located; what networks the user computing device is connected to; etc., as discussed above) and/or other specific criteria.
- device state informationwhich may, e.g., include information about what other applications are running, installed on, and/or otherwise present on the user computing device; where the user computing device is located; what networks the user computing device is connected to; etc., as discussed above
- the at least one received policymay be configured to be enforced by the at least one user computing device based on device state information.
- the policy received by the server computing device in step 1305may be configured to be enforced by a user computing device based on device state information associated with the user computing device.
- Such a policymay, for instance, cause one or more specific functions to be executed and/or prevent one or more other specific functions from being executed based on state information associated with the user computing device.
- state informationmay, for example, include information about what other applications (e.g., besides the managed browser) may be running, installed on, and/or otherwise present on the user computing device, information about where the user computing device is located, information about what networks the user computing device is connected to, and/or other information.
- applicationse.g., besides the managed browser
- the at least one received policymay include one or more rules that are configured to cause the managed browser to switch to an unmanaged mode based on one or more criteria.
- the policy received by the server computing device in step 1305may include one or more rules that are configured to cause a managed browser on a user computing device to switch from a managed mode to an unmanaged mode based on one or more criteria.
- the one or more criteriamay, for example, be based on and/or include device state information associated with the user computing device.
- state informationmay, for example, include information about what other applications (e.g., besides the managed browser) may be running, installed on, and/or otherwise present on the user computing device, information about where the user computing device is located, information about what networks the user computing device is connected to, and/or other information.
- applicationse.g., besides the managed browser
- FIG. 14depicts a flowchart that illustrates another method of providing access to an application store via a managed browser in accordance with one or more illustrative aspects discussed herein.
- the method illustrated in FIG. 14 and/or one or more steps thereofmay be performed by a computing device (e.g., generic computing device 201 ).
- the method illustrated in FIG. 14 and/or one or more steps thereofmay be embodied in computer-executable instructions that are stored in a computer-readable medium, such as a non-transitory computer-readable memory.
- the methodmay begin at step 1405 in which a request from a managed browser on a user computing device may be received, at an application store, to access a first portion of the application store.
- a computing devicethat may provide an application store and/or be configured an application store, such as a server computing device that is configured to provide an enterprise application store, may receive a request from a managed browser on a user computing device to access a specific portion of the application store, such as a portion of the application store associated with specific applications and/or specific types of applications.
- step 1410it may be determined, by the application store, whether the managed browser is operating in a managed mode in which one or more policies are applied to the managed browser, where the one or more policies being configured to limit at least one function of the managed browser.
- the computing devicemay determine whether the managed browser running on the user computing device is running in a managed mode.
- the managed browser on the user computing devicemay provide and/or have a managed mode, similar to the managed mode(s) of the managed browser discussed in the examples above, for example, in which one or more policies are applied to the managed browser.
- the application storemay determine whether the managed browser is operating in the managed mode by interrogating and/or otherwise exchanging information (which may, e.g., include device state information associated with the user computing device) with the managed browser to determine its current operating mode.
- the application storemay allow the managed browser to access the first portion of the application store.
- the computing devicemay provide the managed browser with access to the first portion of the application store (which may, e.g., include providing information associated with the first portion of the application, such as information associated with specific applications and/or specific types of applications, to the managed browser).
- the managed browser on the user computing devicecan access specific portions of the application store, such as the first portion of the application store in this example, while it is running in a managed mode, and as illustrated below, the managed browser might not be able to access specific portions of the application store when it is not running in a managed mode (e.g., when the browser is running in an unmanaged mode).
- the application storemay prevent the managed browser from accessing the first portion of the application store.
- the computing devicemay prevent and/or block the managed browser (and/or the user computing device on which the managed browser is running) from accessing and/or otherwise obtaining information from the first portion of the application store.
- the application storemay provide the managed browser with access to a second portion of the application store different from the first portion of the application store. For example, after determining that the managed browser is not operating in the managed mode (e.g., in step 1410 ), the application store may, in step 1425 , provide the managed browser with access to a different portion of the application store (e.g., than the portion that may have been originally requested by the managed browser and/or by the user of the managed browser).
- the application storemay send a command to the managed browser, and the command may be configured to cause the managed browser to enter a managed mode.
- the application storemay, in step 1430 , send such a command to the managed browser.
- the computing device providing the application storemay, for instance, send and/or exchange data with the user computing device on which the managed browser is running.
- the application storemight send such a command, the managed browser on the user computing device might not enter the managed mode if, for instance, one or more policies and/or current device state information for the user computing device prevent the managed browser from entering the managed mode.
- the application storemay reevaluate whether the managed browser is operating in the managed mode after sending the command to the managed browser. For example, in step 1435 , the application store may again interrogate and/or otherwise exchange information with the user computing device and/or the managed browser running on the user computing device, which may include obtaining and/or analyzing device state information from the user computing device.
- the application storemay allow the managed browser to access the first portion of the application store. For example, in step 1440 , the computing device may provide the managed browser with access to the first portion of the application store, similar to how the application store may provide such access in step 1415 .
- the application storemay generate and/or send a notification to the managed browser, and such a notification may indicate that access to the first portion of the application store cannot be provided while the managed browser is not running in the managed mode.
- the application storemay send such a notification to the managed browser in hopes that the user of the managed browser may manually switch the managed browser into the managed mode and/or take other actions, which may alter the device state information and/or compliance with one or more policies, to allow the managed browser to enter the managed mode.
- Such actionsmay, for instance, include closing and/or deleting specific applications that may be on the user computing device besides the managed browser, moving the user computing device to another location different from the location at which the device is currently located, and/or connecting the user computing device to one or more other networks than the current network(s) to which the device may be currently connected.
- FIG. 15depicts a flowchart that illustrates a method of providing a managed execution environment within a managed browser in accordance with one or more illustrative aspects discussed herein.
- the method illustrated in FIG. 14 and/or one or more steps thereofmay be performed by a computing device (e.g., generic computing device 201 ).
- the method illustrated in FIG. 14 and/or one or more steps thereofmay be embodied in computer-executable instructions that are stored in a computer-readable medium, such as a non-transitory computer-readable memory.
- a computing devicee.g., a mobile computing device, such as a laptop computer, tablet computer, smart phone, or other type of mobile device
- a computing devicemay load a managed browser, similar to how such a managed browser may be loaded in step 505 (discussed above).
- the managed browsermay, for instance, be configured to provide at least one managed mode in which one or more policies are applied to the managed browser, and the one or more policies may be configured to limit one or more functions of the managed browser, as discussed above.
- the managed browsermay, in some embodiments, be configured to provide secure browsing and caching of data obtained from at least one enterprise resource.
- a managed execution environmentmay be provided within the managed browser.
- the managed execution environmentmay be configured to facilitate execution of one or more web applications, and the managed execution environment may be further configured to apply at least one policy of the one or more policies to the one or more web applications.
- the computing devicemay provide a managed execution environment within the managed browser.
- the managed execution environmentmay, for instance, operate as a shell in which one or more web applications may be executed.
- the web applications that may be executed in the managed execution environmentmay, for instance, be written in and/or otherwise utilize various different programming languages (which may, e.g., be interpreted when executed by the computing device at runtime within the managed execution environment).
- one or more policiesmay be applied to web applications that are executed within the managed execution environment, and the one or more policies may be defined and/or imposed by the computing device, an MRM agent running on the computing device, the managed browser, and/or the managed execution environment itself.
- the policies that are applied to web applications within the managed execution environmentmay be similar to the policies discussed in the examples above and may, for instance, be enforced based on and/or otherwise depend on device state information (which may, e.g., include device state information for the computing device providing the managed execution environment).
- the managed execution environmentmay be configured to facilitate execution of at least one HTML5 (HyperText Markup Language 5) application.
- HTML5HyperText Markup Language 5
- at least one web application of the one or more web applications that can be executed within the managed execution environmentmay be an HTML5 application that is, for instance, coded in HTML5 markup language.
- At least one policy of the one or more policiesmay be received from a policy management server.
- the one or more policies that may be applied to a web application in the managed execution environmentmay be received from a policy management server.
- a policy management servermay, for instance, communicate directly with the managed execution environment on the computing device and/or with the managed browser and/or an MRM agent running on the computing device to provide new and/or updated policies to be applied to various web applications that may be executed in the managed execution environment within the managed browser.
- At least one policy(which may, e.g., be applied to the one or more web applications in the managed execution environment) may be configured to prevent the one or more web applications from accessing at least one local storage resource. For example, based on one or more policies that may be applied by the managed execution environment and/or based on device state information (which may, e.g., affect how specific policies are enforced, as in the examples discussed above), the managed execution environment and/or the computing device that is providing the managed execution environment within the managed browser may prevent one or more web applications in the managed execution environment from storing data in one or more local resources on the computing device.
- the managed execution environment and/or the computing device that is providing the managed execution environment within the managed browsermay prevent one or more web applications in the managed execution environment from accessing locally stored data (which may, e.g., be stored in one or more local resources on the computing device).
- At least one policy(which may, e.g., be applied to the one or more web applications in the managed execution environment) may be configured to selectively enable the one or more web applications to access at least one local storage. For example, based on one or more policies that may be applied by the managed execution environment and/or based on device state information (which may, e.g., affect how specific policies are enforced, as in the examples discussed above), the managed execution environment and/or the computing device that is providing the managed execution environment within the managed browser may allow one or more specific web applications in the managed execution environment to access data in one or more local resources on the computing device.
- the managed execution environment and/or the computing device that is providing the managed execution environment within the managed browsermay allow one or more specific web applications in the managed execution environment to store and/or modify data in one or more local resources on the computing device.
- a policymay additionally or alternatively require the one or more web applications to utilize one or more encryption functions (e.g., to encrypt data being accessed from and/or stored in the local resources) in instances in which the one or more web applications are interacting with local storage resources.
- the managed execution environmentmay be configured to expose a policy management agent on the computing device to the one or more web applications.
- the managed execution environment and/or the computing device providing the managed execution environment within the managed browsermay, in some instances, expose a policy management agent (which may, e.g., be an MRM agent, as discussed in the examples above) that is running on the computing device to the one or more web applications that may be executed in the managed execution environment.
- a policy management agentwhich may, e.g., be an MRM agent, as discussed in the examples above
- the managed execution environmentmay be able to extend policy management functionalities, secure key management functionalities, and/or other functionalities to the managed execution environment and/or the web applications in the managed execution environment.
- the managed execution environmentmay be configured to expose one or more functions to the one or more web applications via an application programming interface.
- the managed execution environment and/or the computing device providing the managed execution environment within the managed browsermay, in some instances, expose one or more functions to the one or more web applications via one or more interfaces that may allow such a web application provide higher-level functionalities than might be provided by other web applications.
- the exposed functionsmay allow a web application in the managed execution environment to utilize encryption functionalities, secure tunneling functionalities, secure data storage functionalities, policy management functionalities, and/or other functionalities that may, for instance, be provided by other applications and/or services running on the computing device, such as an MRM agent running on the computing device.
- the managed execution environmentmay be configured to provide an authentication service for the one or more web applications.
- the managed execution environment and/or the computing device providing the managed execution environment within the managed browsermay, in some instances, provide an authentication service for one or more web applications in the managed execution environment.
- the managed execution environment and/or the computing device providing the managed execution environmentmay, for instance, handle multi-factor authentication processes for a web application, which may include obtaining credentials, maintaining keys, and/or providing credentials and/or keys to facilitate various handshakes in specific circumstances.
- the managed execution environment and/or the computing device providing the managed execution environmentmay enable execution of one or more specific functions within a particular web application and/or enable execution of a web application itself.
- the managed execution environmentmay be configured to apply a default set of policies to the one or more web applications.
- the managed execution environment and/or the computing device providing the managed execution environmentmay, in some instances, a default set of policies or a “policy bundle” to one or more specific web applications in the managed execution environment.
- the default set of policiesmay, for instance, be received from and/or periodically updated by a policy management server.
- the default set of policiesmay be applied to a particular web application in the managed execution environment unless a different and/or customized set of policies is defined for the web application.
- the managed execution environmentmay be configured to dynamically update a set of policies applied to the one or more web applications.
- the managed execution environment and/or the computing device providing the managed execution environmentmay, in some instances, dynamically update and/or otherwise modify on-the-fly the policies that are applied to a specific web application in the managed execution environment based on device state information and/or user information (which may, e.g., include user role information) to change, in real-time, the behavior of the managed execution environment based on current usage context of the device.
- the managed execution environment and/or the computing device providing the managed execution environmentmay selectively enable and/or selectively disable one or more policies that may be applied to one or more web applications in the managed execution environment.
- the managed execution environment and/or the computing device providing the managed execution environmentmay selectively enable and/or selectively disable one or more policies that may be applied to one or more web applications in the managed execution environment.
- the managed execution environmentmay dynamically adapt to changing conditions that may require different levels of controls to be imposed upon the web applications that are present in and/or being executed in the managed execution environment.
- various aspects of the disclosurerelate to providing a managed browser on a mobile computing device.
- the concepts discussed hereincan be implemented in any other type of computing device (e.g., a desktop computer, a server, a console, a set-top box, etc.).
- a desktop computere.g., a desktop computer, a server, a console, a set-top box, etc.
- any other type of computing devicee.g., a desktop computer, a server, a console, a set-top box, etc.
Landscapes
- Engineering & Computer Science (AREA)
- Computer Security & Cryptography (AREA)
- Theoretical Computer Science (AREA)
- Computer Hardware Design (AREA)
- General Engineering & Computer Science (AREA)
- Computer Networks & Wireless Communication (AREA)
- Signal Processing (AREA)
- Software Systems (AREA)
- Physics & Mathematics (AREA)
- General Physics & Mathematics (AREA)
- Computing Systems (AREA)
- Databases & Information Systems (AREA)
- Health & Medical Sciences (AREA)
- Bioethics (AREA)
- General Health & Medical Sciences (AREA)
- Multimedia (AREA)
- Information Transfer Between Computers (AREA)
- Telephonic Communication Services (AREA)
Abstract
Description
Claims (18)
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| US14/043,343US8850050B1 (en) | 2013-03-29 | 2013-10-01 | Providing a managed browser |
Applications Claiming Priority (4)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| US201361806577P | 2013-03-29 | 2013-03-29 | |
| US201361866229P | 2013-08-15 | 2013-08-15 | |
| US14/040,831US9355223B2 (en) | 2013-03-29 | 2013-09-30 | Providing a managed browser |
| US14/043,343US8850050B1 (en) | 2013-03-29 | 2013-10-01 | Providing a managed browser |
Related Parent Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| US14/040,831ContinuationUS9355223B2 (en) | 2013-03-29 | 2013-09-30 | Providing a managed browser |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| US8850050B1true US8850050B1 (en) | 2014-09-30 |
| US20140297862A1 US20140297862A1 (en) | 2014-10-02 |
Family
ID=51588300
Family Applications (10)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| US14/040,831Active2034-06-14US9355223B2 (en) | 2013-03-29 | 2013-09-30 | Providing a managed browser |
| US14/043,012ActiveUS8893221B2 (en) | 2013-03-29 | 2013-10-01 | Providing a managed browser |
| US14/043,229ActiveUS9158895B2 (en) | 2013-03-29 | 2013-10-01 | Providing a managed browser |
| US14/043,343ActiveUS8850050B1 (en) | 2013-03-29 | 2013-10-01 | Providing a managed browser |
| US14/042,984ActiveUS8850010B1 (en) | 2013-03-29 | 2013-10-01 | Providing a managed browser |
| US14/043,301ActiveUS8996709B2 (en) | 2013-03-29 | 2013-10-01 | Providing a managed browser |
| US14/043,164ActiveUS8898732B2 (en) | 2013-03-29 | 2013-10-01 | Providing a managed browser |
| US14/042,941ActiveUS8881228B2 (en) | 2013-03-29 | 2013-10-01 | Providing a managed browser |
| US14/043,086ActiveUS9112853B2 (en) | 2013-03-29 | 2013-10-01 | Providing a managed browser |
| US15/140,683Active2034-09-10US10097584B2 (en) | 2013-03-29 | 2016-04-28 | Providing a managed browser |
Family Applications Before (3)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| US14/040,831Active2034-06-14US9355223B2 (en) | 2013-03-29 | 2013-09-30 | Providing a managed browser |
| US14/043,012ActiveUS8893221B2 (en) | 2013-03-29 | 2013-10-01 | Providing a managed browser |
| US14/043,229ActiveUS9158895B2 (en) | 2013-03-29 | 2013-10-01 | Providing a managed browser |
Family Applications After (6)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| US14/042,984ActiveUS8850010B1 (en) | 2013-03-29 | 2013-10-01 | Providing a managed browser |
| US14/043,301ActiveUS8996709B2 (en) | 2013-03-29 | 2013-10-01 | Providing a managed browser |
| US14/043,164ActiveUS8898732B2 (en) | 2013-03-29 | 2013-10-01 | Providing a managed browser |
| US14/042,941ActiveUS8881228B2 (en) | 2013-03-29 | 2013-10-01 | Providing a managed browser |
| US14/043,086ActiveUS9112853B2 (en) | 2013-03-29 | 2013-10-01 | Providing a managed browser |
| US15/140,683Active2034-09-10US10097584B2 (en) | 2013-03-29 | 2016-04-28 | Providing a managed browser |
Country Status (6)
| Country | Link |
|---|---|
| US (10) | US9355223B2 (en) |
| EP (2) | EP2979218A1 (en) |
| JP (2) | JP6131381B2 (en) |
| KR (2) | KR102038842B1 (en) |
| CN (1) | CN105247531B (en) |
| WO (1) | WO2014158228A1 (en) |
Cited By (9)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US9355228B2 (en) | 2012-07-13 | 2016-05-31 | Angel Secure Networks, Inc. | System and method for policy driven protection of remote computing environments |
| US10713087B2 (en)* | 2014-01-10 | 2020-07-14 | Citrix Systems, Inc. | Management of unmanaged user accounts and tasks in a multi-account mobile application |
| US20210081362A1 (en)* | 2019-09-13 | 2021-03-18 | Citrix Systems, Inc. | Multi-web application collaboration techniques |
| US20210136059A1 (en)* | 2019-11-05 | 2021-05-06 | Salesforce.Com, Inc. | Monitoring resource utilization of an online system based on browser attributes collected for a session |
| US20210211507A1 (en)* | 2018-09-24 | 2021-07-08 | Salesforce.Com, Inc. | Multi-channel session connection management mechanism |
| US20220294788A1 (en)* | 2021-03-09 | 2022-09-15 | Oracle International Corporation | Customizing authentication and handling pre and post authentication in identity cloud service |
| US20230237171A1 (en)* | 2022-01-21 | 2023-07-27 | Vmware, Inc. | Securing web browsing on a managed user device |
| US12041041B2 (en)* | 2019-08-21 | 2024-07-16 | Truist Bank | Location-based mobile device authentication |
| US12289308B2 (en)* | 2020-11-13 | 2025-04-29 | Cyberark Software Ltd. | Native remote access to target resources using secretless connections |
Families Citing this family (106)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US9379895B2 (en)* | 2008-07-24 | 2016-06-28 | Zscaler, Inc. | HTTP authentication and authorization management |
| US9280377B2 (en) | 2013-03-29 | 2016-03-08 | Citrix Systems, Inc. | Application with multiple operation modes |
| US20140032733A1 (en) | 2011-10-11 | 2014-01-30 | Citrix Systems, Inc. | Policy-Based Application Management |
| US9215225B2 (en) | 2013-03-29 | 2015-12-15 | Citrix Systems, Inc. | Mobile device locking with context |
| US9529996B2 (en) | 2011-10-11 | 2016-12-27 | Citrix Systems, Inc. | Controlling mobile device access to enterprise resources |
| US9043480B2 (en) | 2011-10-11 | 2015-05-26 | Citrix Systems, Inc. | Policy-based application management |
| US20140108558A1 (en) | 2012-10-12 | 2014-04-17 | Citrix Systems, Inc. | Application Management Framework for Secure Data Sharing in an Orchestration Framework for Connected Devices |
| US9774658B2 (en) | 2012-10-12 | 2017-09-26 | Citrix Systems, Inc. | Orchestration framework for connected devices |
| US9516022B2 (en) | 2012-10-14 | 2016-12-06 | Getgo, Inc. | Automated meeting room |
| US8910239B2 (en) | 2012-10-15 | 2014-12-09 | Citrix Systems, Inc. | Providing virtualized private network tunnels |
| US20140109176A1 (en) | 2012-10-15 | 2014-04-17 | Citrix Systems, Inc. | Configuring and providing profiles that manage execution of mobile applications |
| EP2909715B1 (en) | 2012-10-16 | 2022-12-14 | Citrix Systems, Inc. | Application wrapping for application management framework |
| US9971585B2 (en) | 2012-10-16 | 2018-05-15 | Citrix Systems, Inc. | Wrapping unmanaged applications on a mobile device |
| US9606774B2 (en) | 2012-10-16 | 2017-03-28 | Citrix Systems, Inc. | Wrapping an application with field-programmable business logic |
| US20140108793A1 (en) | 2012-10-16 | 2014-04-17 | Citrix Systems, Inc. | Controlling mobile device access to secure data |
| US9369449B2 (en) | 2013-03-29 | 2016-06-14 | Citrix Systems, Inc. | Providing an enterprise application store |
| US9455886B2 (en) | 2013-03-29 | 2016-09-27 | Citrix Systems, Inc. | Providing mobile device management functionalities |
| US10284627B2 (en) | 2013-03-29 | 2019-05-07 | Citrix Systems, Inc. | Data management for an application with multiple operation modes |
| US9355223B2 (en) | 2013-03-29 | 2016-05-31 | Citrix Systems, Inc. | Providing a managed browser |
| US9985850B2 (en) | 2013-03-29 | 2018-05-29 | Citrix Systems, Inc. | Providing mobile device management functionalities |
| JP6448062B2 (en)* | 2013-05-07 | 2019-01-09 | ノーム ザタロブスキ、ヨーニ | A system for browsing with personalized and customizable smart browsers |
| US9342331B2 (en)* | 2013-10-21 | 2016-05-17 | International Business Machines Corporation | Secure virtualized mobile cellular device |
| US20150134725A1 (en)* | 2013-11-13 | 2015-05-14 | Adrian Cesena, Jr. | Computer-implemented methods, computer readable medium and systems for virtual application execution |
| US9870116B1 (en)* | 2013-12-09 | 2018-01-16 | Google Llc | Controlling actions for browser extensions |
| US10362026B2 (en) | 2013-12-16 | 2019-07-23 | Amazon Technologies, Inc. | Providing multi-factor authentication credentials via device notifications |
| US9473491B1 (en) | 2014-12-16 | 2016-10-18 | Amazon Technologies, Inc. | Computing device with integrated authentication token |
| US10866711B1 (en) | 2013-12-16 | 2020-12-15 | Amazon Technologies, Inc. | Providing account information to applications |
| US10841297B2 (en) | 2013-12-16 | 2020-11-17 | Amazon Technologies, Inc. | Providing multi-factor authentication credentials via device notifications |
| WO2015099699A1 (en)* | 2013-12-24 | 2015-07-02 | Intel Corporation | Context sensitive multi-mode authentication |
| US9680872B1 (en) | 2014-03-25 | 2017-06-13 | Amazon Technologies, Inc. | Trusted-code generated requests |
| US9854001B1 (en)* | 2014-03-25 | 2017-12-26 | Amazon Technologies, Inc. | Transparent policies |
| US9930095B2 (en)* | 2014-03-26 | 2018-03-27 | Google Llc | System for managing extension modifications to web pages |
| US10560439B2 (en)* | 2014-03-27 | 2020-02-11 | Arris Enterprises, Inc. | System and method for device authorization and remediation |
| US9813421B2 (en) | 2014-05-20 | 2017-11-07 | Box, Inc. | Systems and methods for secure resource access and network communication |
| US10243953B2 (en)* | 2014-05-20 | 2019-03-26 | Box, Inc. | Systems and methods for secure resource access and network communication |
| US9497197B2 (en) | 2014-05-20 | 2016-11-15 | Box, Inc. | Systems and methods for secure resource access and network communication |
| US9712520B1 (en)* | 2015-06-23 | 2017-07-18 | Amazon Technologies, Inc. | User authentication using client-side browse history |
| US9646104B1 (en) | 2014-06-23 | 2017-05-09 | Amazon Technologies, Inc. | User tracking based on client-side browse history |
| US10182046B1 (en) | 2015-06-23 | 2019-01-15 | Amazon Technologies, Inc. | Detecting a network crawler |
| KR101695639B1 (en)* | 2014-08-13 | 2017-01-16 | (주)잉카엔트웍스 | Method and system for providing application security service based on cloud |
| US10209973B2 (en)* | 2014-09-16 | 2019-02-19 | Salesforce.Com, Inc. | Private application distribution mechanisms and architectures |
| US10225245B2 (en)* | 2014-11-18 | 2019-03-05 | Auth0, Inc. | Identity infrastructure as a service |
| US20160191645A1 (en)* | 2014-12-30 | 2016-06-30 | Citrix Systems, Inc. | Containerizing Web Applications for Managed Execution |
| US10404701B2 (en)* | 2015-01-21 | 2019-09-03 | Onion ID Inc. | Context-based possession-less access of secure information |
| SG10201500698YA (en)* | 2015-01-29 | 2016-08-30 | Huawei Internat Pte Ltd | Method for data protection using isolated environment in mobile device |
| US9917920B2 (en) | 2015-02-24 | 2018-03-13 | Xor Data Exchange, Inc | System and method of reciprocal data sharing |
| EP3292475B1 (en)* | 2015-05-07 | 2020-07-08 | Appbus, Inc. | Secure container platform for resource access and placement on unmanaged and unsecured devices |
| US9882887B2 (en) | 2015-06-15 | 2018-01-30 | Airwatch Llc | Single sign-on for managed mobile devices |
| US10812464B2 (en) | 2015-06-15 | 2020-10-20 | Airwatch Llc | Single sign-on for managed mobile devices |
| US10944738B2 (en) | 2015-06-15 | 2021-03-09 | Airwatch, Llc. | Single sign-on for managed mobile devices using kerberos |
| US11057364B2 (en) | 2015-06-15 | 2021-07-06 | Airwatch Llc | Single sign-on for managed mobile devices |
| US10171447B2 (en) | 2015-06-15 | 2019-01-01 | Airwatch Llc | Single sign-on for unmanaged mobile devices |
| US10290022B1 (en) | 2015-06-23 | 2019-05-14 | Amazon Technologies, Inc. | Targeting content based on user characteristics |
| US9864852B2 (en)* | 2015-07-27 | 2018-01-09 | Amazon Technologies, Inc. | Approaches for providing multi-factor authentication credentials |
| CN107209751B (en)* | 2015-08-13 | 2020-09-08 | 华为技术有限公司 | Service processing method and device |
| US10361936B2 (en)* | 2015-08-19 | 2019-07-23 | Google Llc | Filtering content based on user mobile network and data-plan |
| US10601669B2 (en)* | 2015-10-27 | 2020-03-24 | Vmware, Inc. | Configurable client filtering rules |
| US10187374B2 (en)* | 2015-10-29 | 2019-01-22 | Airwatch Llc | Multi-factor authentication for managed applications using single sign-on technology |
| US9866546B2 (en) | 2015-10-29 | 2018-01-09 | Airwatch Llc | Selectively enabling multi-factor authentication for managed devices |
| US9854405B2 (en) | 2015-11-10 | 2017-12-26 | At&T Intellectual Property I, L.P. | Mobile application and device feature regulation based on profile data |
| US9992187B2 (en)* | 2015-12-21 | 2018-06-05 | Cisco Technology, Inc. | Single sign-on authentication via browser for client application |
| EP3335395B1 (en) | 2016-02-01 | 2021-03-24 | Google LLC | Systems and methods for dynamically restricting the rendering of unauthorized content included in information resources |
| EP3335148B1 (en) | 2016-02-01 | 2019-07-10 | Google LLC | Systems and methods for deploying countermeasures against unauthorized scripts interfering with the rendering of content elements on information resources |
| US10366243B2 (en)* | 2016-02-04 | 2019-07-30 | Airwatch, Llc | Preventing restricted content from being presented to unauthorized individuals |
| US9954894B2 (en) | 2016-03-04 | 2018-04-24 | Microsoft Technology Licensing, Llc | Webpage security |
| CN105610873A (en)* | 2016-03-22 | 2016-05-25 | 广东欧珀移动通信有限公司 | Identity verification method and device |
| US10291636B2 (en)* | 2016-05-23 | 2019-05-14 | International Business Machines Corporation | Modifying a user session lifecycle in a cloud broker environment |
| US10868883B2 (en)* | 2016-06-29 | 2020-12-15 | Nicira, Inc. | Upgrading a proxy that decouples network connections from an application during application's downtime |
| US20190182234A1 (en)* | 2016-08-16 | 2019-06-13 | Hanselware, Inc. | Storing, managing and accessing information in a repository within a security context |
| US10333930B2 (en)* | 2016-11-14 | 2019-06-25 | General Electric Company | System and method for transparent multi-factor authentication and security posture checking |
| US10848501B2 (en)* | 2016-12-30 | 2020-11-24 | Microsoft Technology Licensing, Llc | Real time pivoting on data to model governance properties |
| US11165751B2 (en) | 2017-02-16 | 2021-11-02 | Emerald Cactus Ventures, Inc. | System and method for establishing simultaneous encrypted virtual private networks from a single computing device |
| US11165825B2 (en) | 2017-02-16 | 2021-11-02 | Emerald Cactus Ventures, Inc. | System and method for creating encrypted virtual private network hotspot |
| US11122013B2 (en)* | 2017-02-16 | 2021-09-14 | Emerald Cactus Ventures, Inc. | System and method for encrypting data interactions delineated by zones |
| US11050832B2 (en) | 2017-03-29 | 2021-06-29 | Citrix Systems, Inc. | Maintaining a session across multiple web applications |
| US10614233B2 (en) | 2017-07-27 | 2020-04-07 | International Business Machines Corporation | Managing access to documents with a file monitor |
| US11070630B2 (en) | 2018-05-04 | 2021-07-20 | Citrix Systems, Inc. | Computer system providing SAAS application session state migration features and related methods |
| AU2019262187B2 (en)* | 2018-05-04 | 2022-02-24 | Citrix Systems, Inc. | Systems and methods for providing data loss prevention via an embedded browser |
| CN116560970A (en)* | 2018-05-07 | 2023-08-08 | 谷歌有限责任公司 | Immersive web-based simulator for digital assistant-based applications |
| US10887287B2 (en) | 2018-05-11 | 2021-01-05 | Citrix Systems, Inc. | Connecting client devices to anonymous sessions via helpers |
| US10599486B1 (en)* | 2018-09-21 | 2020-03-24 | Citrix Systems, Inc. | Systems and methods for intercepting and enhancing SaaS application calls via embedded browser |
| US10924545B2 (en) | 2018-10-10 | 2021-02-16 | Citrix Systems, Inc. | Computer system providing mirrored SAAS application sessions and related methods |
| US10820194B2 (en)* | 2018-10-23 | 2020-10-27 | Duo Security, Inc. | Systems and methods for securing access to computing resources by an endpoint device |
| US11074338B2 (en) | 2018-10-23 | 2021-07-27 | Citrix Systems, Inc. | Local secure rendering of web content |
| US11196714B2 (en)* | 2018-11-07 | 2021-12-07 | Citrix Systems, Inc. | Systems and methods for encrypted browser cache |
| US10996819B2 (en) | 2018-11-12 | 2021-05-04 | Citrix Systems, Inc. | Systems and methods for intellisense for SaaS application |
| US11019066B2 (en)* | 2018-11-16 | 2021-05-25 | Citrix Systems, Inc. | Systems and methods for securely managing browser plugins via embedded browser |
| US11057373B2 (en) | 2018-11-16 | 2021-07-06 | Bank Of America Corporation | System for authentication using channel dependent one-time passwords |
| US11165871B2 (en)* | 2019-02-01 | 2021-11-02 | Citrix Systems, Inc. | Computer system providing context-based Software as a Service (SaaS) application session switching and related methods |
| US11556699B2 (en)* | 2019-02-04 | 2023-01-17 | Citrix Systems, Inc. | Data migration across SaaS applications |
| US11790176B2 (en)* | 2019-03-19 | 2023-10-17 | Servicenow, Inc. | Systems and methods for a virtual agent in a cloud computing environment |
| IT201900005876A1 (en)* | 2019-04-16 | 2020-10-16 | Roberto Griggio | SYSTEM AND METHOD FOR MANAGING THE MULTI-DOMAIN ACCESS CREDENTIALS OF A USER ENABLED TO ACCESS A PLURALITY OF DOMAINS |
| US11323480B2 (en) | 2019-05-07 | 2022-05-03 | Cisco Technology, Inc. | Policy enforcement and introspection on an authentication system |
| US11038988B2 (en)* | 2019-08-26 | 2021-06-15 | Citrix Systems, Inc. | System and methods for providing user analytics and performance feedback for web applications |
| CN110912896B (en)* | 2019-11-27 | 2022-02-25 | 厦门市美亚柏科信息股份有限公司 | Non-invasive HTTP interface security policy injection method |
| US11252157B1 (en)* | 2020-03-12 | 2022-02-15 | Amazon Technologies, Inc. | Permission management for electronic resources |
| US11588801B1 (en) | 2020-03-12 | 2023-02-21 | Amazon Technologies, Inc. | Application-centric validation for electronic resources |
| US11182054B2 (en)* | 2020-03-27 | 2021-11-23 | Coupang Corp. | Web-browser plugin for consolidating requested disaggregated information |
| US12081979B2 (en)* | 2020-11-05 | 2024-09-03 | Visa International Service Association | One-time wireless authentication of an Internet-of-Things device |
| US11921872B2 (en)* | 2020-12-16 | 2024-03-05 | International Business Machines Corporation | Access control for a data object including data with different access requirements |
| JP7730377B2 (en) | 2021-04-22 | 2025-08-27 | パロ アルト ネットワークス,インコーポレイテッド | Cybersecurity Systems |
| US12218974B2 (en)* | 2022-01-21 | 2025-02-04 | Omnissa, Llc | Securing web browsing on a managed user device |
| US12284427B2 (en) | 2022-03-21 | 2025-04-22 | Samsung Electronics Co., Ltd. | Infrared detector and infrared image sensor including the same |
| KR102498461B1 (en)* | 2022-04-25 | 2023-02-13 | 주식회사 디엠테크컨설팅 | Integrated management method using single sign-on manufacturing information integrated management system |
| US11792234B1 (en) | 2022-11-11 | 2023-10-17 | Netskope, Inc. | Browser extension identification and isolation |
| CN115883191A (en)* | 2022-11-29 | 2023-03-31 | 国家能源集团宁夏煤业有限责任公司 | Communication method, computer-readable storage medium and communication system for enterprise intranet |
Citations (270)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US5805803A (en) | 1997-05-13 | 1998-09-08 | Digital Equipment Corporation | Secure web tunnel |
| WO1999014652A1 (en) | 1997-09-16 | 1999-03-25 | Microsoft Corporation | Encrypting file system and method |
| US6151606A (en) | 1998-01-16 | 2000-11-21 | Visto Corporation | System and method for using a workspace data manager to access, manipulate and synchronize network data |
| US6154172A (en) | 1998-03-31 | 2000-11-28 | Piccionelli; Gregory A. | System and process for limiting distribution of information on a communication network based on geographic location |
| US20020112047A1 (en) | 2000-12-05 | 2002-08-15 | Rakesh Kushwaha | System and method for wireless data terminal management using general packet radio service network |
| WO2002084460A2 (en) | 2001-04-12 | 2002-10-24 | The Regents Of The University Of Michigan | Method and system to maintain portable computer data secure and authentication token for use therein |
| US20030031319A1 (en) | 2001-06-13 | 2003-02-13 | Miki Abe | Data transfer system, data transfer apparatus, data recording apparatus, edit controlling method and data processing method |
| US20030037103A1 (en) | 2001-03-14 | 2003-02-20 | Nokia Corporation | Realization of presence management |
| US20030046366A1 (en) | 2001-02-13 | 2003-03-06 | Shishir Pardikar | System and method for providing transparent access to distributed authoring and versioning files including encrypted files |
| US20030131245A1 (en) | 2002-01-04 | 2003-07-10 | Michael Linderman | Communication security system |
| US6609198B1 (en) | 1999-08-05 | 2003-08-19 | Sun Microsystems, Inc. | Log-on service providing credential level change without loss of session continuity |
| US6621766B2 (en) | 2001-08-01 | 2003-09-16 | Fossil, Inc. | Flexible timepiece in multiple environments |
| US20040006706A1 (en)* | 2002-06-06 | 2004-01-08 | Ulfar Erlingsson | Methods and systems for implementing a secure application execution environment using derived user accounts for internet content |
| US20040010579A1 (en) | 2000-08-31 | 2004-01-15 | Esko Freese | Wireless device management |
| US20040083273A1 (en) | 2001-01-18 | 2004-04-29 | Madison Justin Paul | Method and system for managing digital content, including streaming media |
| US20040111640A1 (en) | 2002-01-08 | 2004-06-10 | Baum Robert T. | IP based security applications using location, port and/or device identifier information |
| EP1465039A1 (en) | 2002-01-08 | 2004-10-06 | NTT DoCoMo, Inc. | Content delivery method and content delivery system |
| US20040205233A1 (en) | 2001-08-29 | 2004-10-14 | Dunk Craig A. | System and method for addressing a mobile device in an ip-based wireless network |
| US20040230807A1 (en) | 2001-02-12 | 2004-11-18 | Baird Leemon C. | Apparatus and method for authenticating access to a network resource |
| WO2004107646A1 (en) | 2003-05-14 | 2004-12-09 | Threatguard, Inc. | System and method for application-level virtual private network |
| US6859879B2 (en) | 2000-05-26 | 2005-02-22 | International Business Machine Corporation | Method and system for secure pervasive access |
| US20050055578A1 (en) | 2003-02-28 | 2005-03-10 | Michael Wright | Administration of protection of data accessible by a mobile device |
| US6883098B1 (en) | 2000-09-20 | 2005-04-19 | International Business Machines Corporation | Method and computer system for controlling access by applications to this and other computer systems |
| US20050097608A1 (en) | 2003-10-30 | 2005-05-05 | Xerox Corporation | Multimedia communications/collaboration hub |
| US20050172241A1 (en) | 2004-01-08 | 2005-08-04 | International Business Machines Corporation | System and method for improved direct system clipboard |
| GB2411320A (en) | 2004-02-23 | 2005-08-24 | Nec Corp | Access control management in a terminal device |
| US20050255838A1 (en) | 2004-04-30 | 2005-11-17 | Adams Neil P | System and method for handling data transfers |
| US20050273592A1 (en) | 2004-05-20 | 2005-12-08 | International Business Machines Corporation | System, method and program for protecting communication |
| US20060075123A1 (en) | 2004-09-27 | 2006-04-06 | Citrix Systems, Inc. | System and method for managing virtual ip addresses |
| US20060085826A1 (en) | 2004-10-18 | 2006-04-20 | Funk James M | Aggregated program guide for download and view video on demand service |
| US20060094400A1 (en) | 2003-02-28 | 2006-05-04 | Brent Beachem | System and method for filtering access points presented to a user and locking onto an access point |
| US7043453B2 (en) | 1994-11-23 | 2006-05-09 | Contentguard Holdings, Inc. | Method and system for conducting transactions between repositories using a repository transaction protocol |
| US20060117104A1 (en) | 2004-09-17 | 2006-06-01 | Fujitsu Limited | Setting information distribution apparatus, method, program, and medium, authentication setting transfer apparatus, method, program, and medium, and setting information reception program |
| US20060120526A1 (en) | 2003-02-28 | 2006-06-08 | Peter Boucher | Access control to files based on source information |
| US20060141985A1 (en) | 2004-12-23 | 2006-06-29 | Motorola, Inc. | Dynamic management for interface access permissions |
| US20060147043A1 (en) | 2002-09-23 | 2006-07-06 | Credant Technologies, Inc. | Server, computer memory, and method to support security policy maintenance and distribution |
| US20060161635A1 (en) | 2000-09-07 | 2006-07-20 | Sonic Solutions | Methods and system for use in network management of content |
| US20060224742A1 (en) | 2005-02-28 | 2006-10-05 | Trust Digital | Mobile data security system and methods |
| US20060225142A1 (en) | 2005-04-05 | 2006-10-05 | Cisco Technology, Inc. (A California Corporation) | Method and electronic device for triggering zeroization in a electronic device |
| US20060242685A1 (en) | 2002-09-23 | 2006-10-26 | Credant Technologies, Inc. | System and method for distribution of security policies for mobile devices |
| US7159120B2 (en) | 2001-11-19 | 2007-01-02 | Good Technology, Inc. | Method and system for protecting data within portable electronic devices |
| US20070005713A1 (en) | 2005-07-01 | 2007-01-04 | Levasseur Thierry | Secure electronic mail system |
| US20070011749A1 (en) | 2005-07-11 | 2007-01-11 | Simdesk Technologies | Secure clipboard function |
| US20070038764A1 (en) | 2005-06-07 | 2007-02-15 | Alcatel | Network equipment for supplying multimode mobile terminals with data necessary for automatically selecting radio access network interfaces during service sessions |
| US20070049297A1 (en) | 2005-08-29 | 2007-03-01 | Janakiraman Gopalan | System and method for locating mobile devices through a direct-connection protocol |
| US20070056043A1 (en) | 2005-05-19 | 2007-03-08 | Richard Onyon | Remote cell phone auto destruct |
| US20070074033A1 (en) | 2005-09-29 | 2007-03-29 | Research In Motion Limited | Account management in a system and method for providing code signing services |
| US20070109983A1 (en) | 2005-11-11 | 2007-05-17 | Computer Associates Think, Inc. | Method and System for Managing Access to a Wireless Network |
| US7240015B1 (en) | 1999-09-17 | 2007-07-03 | Mitel Networks Corporation And The University Of Ottawa | Policy representations and mechanisms for the control of software |
| US20070156897A1 (en) | 2005-12-29 | 2007-07-05 | Blue Jungle | Enforcing Control Policies in an Information Management System |
| US20070180447A1 (en) | 2006-01-24 | 2007-08-02 | Citrix Systems, Inc. | Methods and systems for interacting, via a hypermedium page, with a virtual machine |
| US7254831B2 (en) | 2002-12-04 | 2007-08-07 | Microsoft Corporation | Sharing a sign-in among software applications having secured features |
| US20070186106A1 (en) | 2006-01-26 | 2007-08-09 | Ting David M | Systems and methods for multi-factor authentication |
| US20070199051A1 (en) | 2006-02-15 | 2007-08-23 | Microsoft Corporation | Securely hosting a webbrowser control in a managed code environment |
| US20070204153A1 (en) | 2006-01-04 | 2007-08-30 | Tome Agustin J | Trusted host platform |
| US7269605B1 (en) | 2004-02-13 | 2007-09-11 | Avidian Technologies | Personal information manager data synchronization and augmentation |
| US20070214272A1 (en) | 2006-03-07 | 2007-09-13 | Novell, Inc. | Light-weight multi-user browser |
| US20070226225A1 (en) | 2006-03-22 | 2007-09-27 | Yiu Timothy C | Mobile collaboration and communication system |
| US20070226773A1 (en) | 2006-03-21 | 2007-09-27 | Novell, Inc. | System and method for using sandboxes in a managed shell |
| WO2007113709A1 (en) | 2006-03-30 | 2007-10-11 | Koninklijke Philips Electronics N.V. | Method and apparatus for assigning an application to a security restriction |
| US20080027982A1 (en) | 2006-07-27 | 2008-01-31 | Ebay Inc. | Indefinite caching expiration techniques |
| US20080047015A1 (en) | 2006-08-08 | 2008-02-21 | Andrew Cornwall | Method to provide a secure virtual machine launcher |
| US20080052395A1 (en) | 2003-02-28 | 2008-02-28 | Michael Wright | Administration of protection of data accessible by a mobile device |
| US7340772B2 (en) | 2001-06-13 | 2008-03-04 | Citrix Systems, Inc. | Systems and methods for continuing an operation interrupted from a reconnection between a client and server |
| US20080066020A1 (en) | 2004-09-16 | 2008-03-13 | Boss Gregory J | System and Method to Capture and Manage Input Values for Automatic Form Fill |
| US20080066177A1 (en) | 2006-09-08 | 2008-03-13 | International Business Machines Corporation | Methods, systems, and computer program products for implementing inter-process integrity serialization |
| US20080070495A1 (en) | 2006-08-18 | 2008-03-20 | Michael Stricklen | Mobile device management |
| US20080127292A1 (en) | 2006-08-04 | 2008-05-29 | Apple Computer, Inc. | Restriction of program process capabilities |
| US20080133729A1 (en) | 2006-08-17 | 2008-06-05 | Neustar, Inc. | System and method for managing domain policy for interconnected communication networks |
| US20080134292A1 (en) | 2003-01-08 | 2008-06-05 | Ido Ariel | Extending user relationships |
| US20080141335A1 (en) | 2006-12-08 | 2008-06-12 | Novell, Inc. | Provisioning software with policy-appropriate capabilities |
| US20080163286A1 (en) | 2006-12-29 | 2008-07-03 | Echostar Technologies Corporation | Controlling access to content and/or services |
| WO2008086611A1 (en) | 2007-01-19 | 2008-07-24 | Research In Motion Limited | Selectively wiping a remote device |
| US20080196038A1 (en) | 2007-02-08 | 2008-08-14 | Microsoft Corporation | Utilizing a first managed process to host at least a second managed process |
| US7415498B2 (en) | 2003-12-10 | 2008-08-19 | International Business Machines Corporation | Time limited collaborative community role delegation policy |
| US20080209506A1 (en) | 2006-08-14 | 2008-08-28 | Quantum Secure, Inc. | Physical access control and security monitoring system utilizing a normalized data format |
| US20080214300A1 (en) | 2000-12-07 | 2008-09-04 | Igt | Methods for electronic data security and program authentication |
| US20080235760A1 (en) | 2006-05-02 | 2008-09-25 | International Business Machines Corporation | Confidential Content Reporting System and Method with Electronic Mail Verification Functionality |
| US20080313648A1 (en) | 2007-06-14 | 2008-12-18 | Microsoft Corporation | Protection and communication abstractions for web browsers |
| US20080318616A1 (en) | 2007-06-21 | 2008-12-25 | Verizon Business Network Services, Inc. | Flexible lifestyle portable communications device |
| US20090006232A1 (en) | 2007-06-29 | 2009-01-01 | Gallagher Ken A | Secure computer and internet transaction software and hardware and uses thereof |
| US20090028049A1 (en) | 2007-07-27 | 2009-01-29 | Jesse Boudreau | Administration of policies for wireless devices in a wireless communication system |
| US20090030968A1 (en) | 2007-07-27 | 2009-01-29 | Jesse Boudreau | Remote control in a wireless communication system |
| US7490073B1 (en) | 2004-12-21 | 2009-02-10 | Zenprise, Inc. | Systems and methods for encoding knowledge for automated management of software application deployments |
| US7496954B1 (en) | 2004-11-22 | 2009-02-24 | Sprint Communications Company L.P. | Single sign-on system and method |
| US20090077638A1 (en) | 2007-09-17 | 2009-03-19 | Novell, Inc. | Setting and synching preferred credentials in a disparate credential store environment |
| US7529923B2 (en) | 2005-06-30 | 2009-05-05 | Intel Corporation | Operating system mode transfer |
| US20090119773A1 (en) | 2007-11-02 | 2009-05-07 | D Amore Tianyu Li | Apparatus and methods of configurable system event and resource arbitration management |
| US20090172789A1 (en) | 2007-12-27 | 2009-07-02 | Hewlett-Packard Development Company, L.P. | Policy Based, Delegated Limited Network Access Management |
| US20090170532A1 (en) | 2007-12-28 | 2009-07-02 | Apple Inc. | Event-based modes for electronic devices |
| US20090178111A1 (en) | 1998-10-28 | 2009-07-09 | Bea Systems, Inc. | System and method for maintaining security in a distributed computer network |
| US20090199277A1 (en) | 2008-01-31 | 2009-08-06 | Norman James M | Credential arrangement in single-sign-on environment |
| US20090221278A1 (en) | 2005-12-30 | 2009-09-03 | Telecom Italia S.P.A. | Method for Customizing the Operation of a Telephonic Terminal |
| US20090222880A1 (en) | 2008-03-03 | 2009-09-03 | Tresys Technology, Llc | Configurable access control security for virtualization |
| US20090228954A1 (en) | 2008-03-07 | 2009-09-10 | At&T Mobility Ii Llc | System and method for policy-enabled mobile service gateway |
| US20090228714A1 (en) | 2004-11-18 | 2009-09-10 | Biogy, Inc. | Secure mobile device with online vault |
| US20090228963A1 (en) | 2007-11-26 | 2009-09-10 | Nortel Networks Limited | Context-based network security |
| US7596593B2 (en) | 1999-09-07 | 2009-09-29 | Citrix Systems, Llc | Methods and apparatus for efficiently transmitting interactive application data between a client and server using markup language |
| US20090249359A1 (en) | 2008-03-25 | 2009-10-01 | Caunter Mark Leslie | Apparatus and methods for widget intercommunication in a wireless communication environment |
| US7599991B2 (en) | 2004-03-10 | 2009-10-06 | Microsoft Corporation | Rules interface for implementing message rules on a mobile computing device |
| US20090325615A1 (en) | 2008-06-29 | 2009-12-31 | Oceans' Edge, Inc. | Mobile Telephone Firewall and Compliance Enforcement System and Method |
| GB2462442A (en) | 2008-08-06 | 2010-02-10 | Zybert Computing Ltd | A remote server centrally controls access to data stored in a data container in an encrypted form |
| US20100077469A1 (en) | 2008-09-19 | 2010-03-25 | Michael Furman | Single Sign On Infrastructure |
| US7697737B2 (en) | 2005-03-25 | 2010-04-13 | Northrop Grumman Systems Corporation | Method and system for providing fingerprint enabled wireless add-on for personal identification number (PIN) accessible smartcards |
| US20100100825A1 (en) | 2008-10-16 | 2010-04-22 | Accenture Global Services Gmbh | Method, system and graphical user interface for enabling a user to access enterprise data on a portable electronic device |
| US20100100925A1 (en) | 2008-10-16 | 2010-04-22 | International Business Machines Corporation | Digital Rights Management (DRM)-Enabled Policy Management For An Identity Provider In A Federated Environment |
| US20100124196A1 (en) | 2005-06-29 | 2010-05-20 | Jumpstart Wireless Corporation | System and method for dynamic automatic communication path selection, distributed device synchronization and task delegation |
| US20100146523A1 (en) | 2008-12-05 | 2010-06-10 | Tripod Ventures Inc./ Entreprises Tripod Inc. | Browser environment application and local file server application system |
| US20100154025A1 (en) | 2008-12-12 | 2010-06-17 | Microsoft Corporation | Integrating policies from a plurality of disparate management agents |
| US20100150341A1 (en) | 2008-12-17 | 2010-06-17 | David Dodgson | Storage security using cryptographic splitting |
| US7761523B2 (en) | 2007-02-09 | 2010-07-20 | Research In Motion Limited | Schedulable e-mail filters |
| US20100192212A1 (en) | 2009-01-28 | 2010-07-29 | Gregory G. Raleigh | Automated device provisioning and activation |
| US7788535B2 (en) | 2005-01-28 | 2010-08-31 | Nxp B.V. | Means and method for debugging |
| US20100229197A1 (en) | 2007-10-31 | 2010-09-09 | Pxd, Inc. | Digital broadcast widget system |
| US20100248699A1 (en) | 2009-03-31 | 2010-09-30 | Dumais Paul Mark Joseph | Remote application storage |
| WO2010115289A1 (en) | 2009-04-09 | 2010-10-14 | Aegis Mobility, Inc. | Context based data mediation |
| US20100287619A1 (en) | 2009-05-05 | 2010-11-11 | Absolute Software Corporation | Discriminating data protection system |
| US20100299152A1 (en) | 2009-05-20 | 2010-11-25 | Mobile Iron, Inc. | Selective Management of Mobile Devices in an Enterprise Environment |
| US20100299376A1 (en) | 2009-05-20 | 2010-11-25 | Mobile Iron, Inc. | Selective Management of Mobile Devices in an Enterprise Environment |
| US20100319053A1 (en) | 2009-06-12 | 2010-12-16 | Apple Inc. | Devices with profile-based operating mode controls |
| US20100317336A1 (en) | 2009-06-16 | 2010-12-16 | Bran Ferren | Context-based limitation of mobile device operation |
| US20100325097A1 (en) | 2007-02-07 | 2010-12-23 | International Business Machines Corporation | Non-Invasive Usage Tracking, Access Control, Policy Enforcement, Audit Logging, and User Action Automation On Software Applications |
| US7904468B2 (en) | 2008-02-27 | 2011-03-08 | Research In Motion Limited | Method and software for facilitating interaction with a personal information manager application at a wireless communication device |
| US7950066B1 (en) | 2001-12-21 | 2011-05-24 | Guardian Data Storage, Llc | Method and system for restricting use of a clipboard application |
| US20110145833A1 (en) | 2009-12-15 | 2011-06-16 | At&T Mobility Ii Llc | Multiple Mode Mobile Device |
| US7966323B2 (en) | 2004-09-13 | 2011-06-21 | Research In Motion Limited | Enabling category-based filtering |
| US7966652B2 (en) | 2008-04-07 | 2011-06-21 | Safemashups Inc. | Mashauth: using mashssl for efficient delegated authentication |
| US20110154477A1 (en) | 2009-12-22 | 2011-06-23 | Cisco Technology, Inc. | Dynamic content-based routing |
| US7970386B2 (en) | 2005-06-03 | 2011-06-28 | Good Technology, Inc. | System and method for monitoring and maintaining a wireless device |
| US20110179484A1 (en) | 2006-04-06 | 2011-07-21 | Juniper Networks, Inc. | Malware detection system and method for mobile platforms |
| US8001278B2 (en) | 2007-09-28 | 2011-08-16 | Intel Corporation | Network packet payload compression |
| US20110209064A1 (en) | 2010-02-24 | 2011-08-25 | Novell, Inc. | System and method for providing virtual desktop extensions on a client desktop |
| US20110208838A1 (en) | 2001-11-02 | 2011-08-25 | Juniper Networks, Inc. | Method and system for providing secure access to private networks with client redirection |
| US8012219B2 (en) | 2002-08-09 | 2011-09-06 | Visto Corporation | System and method for preventing access to data on a compromised remote device |
| US20110219124A1 (en)* | 2010-03-05 | 2011-09-08 | Brass Monkey, Inc. | System and method for two way communication and controlling content in a web browser |
| US20110225417A1 (en) | 2006-12-13 | 2011-09-15 | Kavi Maharajh | Digital rights management in a mobile environment |
| US20110239125A1 (en) | 2010-03-24 | 2011-09-29 | Kristensen Kristian H | Using multiple display servers to protect data |
| US8037421B2 (en) | 2005-10-11 | 2011-10-11 | Research In Motion Limited | System and method for organizing application indicators on an electronic device |
| US20110252232A1 (en) | 2010-04-07 | 2011-10-13 | Apple Inc. | System and method for wiping encrypted data on a device having file-level content protection |
| US20110258301A1 (en) | 2010-04-15 | 2011-10-20 | Research In Motion Limited | Method and system for transmitting an application to a device |
| US20110271279A1 (en) | 2010-04-29 | 2011-11-03 | High Cloud Security, Inc. | Secure Virtual Machine |
| US20110276699A1 (en) | 2010-05-09 | 2011-11-10 | Pedersen Bradley J | Systems and methods for allocation of classes of service to network connections corresponding to virtual channels |
| US20110276683A1 (en) | 2010-05-06 | 2011-11-10 | Trust Digital, Llc | Distributed data revocation using data commands |
| US8060074B2 (en) | 2007-07-30 | 2011-11-15 | Mobile Iron, Inc. | Virtual instance architecture for mobile device management systems |
| US20110295970A1 (en) | 2010-05-27 | 2011-12-01 | Canon Kabushiki Kaisha | Cloud computing system, server computer, device connection method, and storage medium |
| US8085891B2 (en) | 2006-05-29 | 2011-12-27 | Research In Motion Limited | System and method for management of mobile device communication |
| US20120005745A1 (en) | 2010-06-30 | 2012-01-05 | Juniper Networks, Inc. | Vpn network client for mobile device having dynamically translated user home page |
| US20120005746A1 (en) | 2010-06-30 | 2012-01-05 | Juniper Networks, Inc. | Dual-mode multi-service vpn network client for mobile device |
| US20120005724A1 (en) | 2009-02-09 | 2012-01-05 | Imera Systems, Inc. | Method and system for protecting private enterprise resources in a cloud computing environment |
| US20120005476A1 (en) | 2010-06-30 | 2012-01-05 | Juniper Networks, Inc. | Multi-service vpn network client for mobile device having integrated acceleration |
| US8095786B1 (en) | 2006-11-09 | 2012-01-10 | Juniper Networks, Inc. | Application-specific network-layer virtual private network connections |
| US20120023506A1 (en) | 2010-07-20 | 2012-01-26 | Apple Inc. | Maintaining Data States Upon Forced Exit |
| US20120036347A1 (en) | 2010-08-06 | 2012-02-09 | Swanson Robert C | Providing fast non-volatile storage in a secure environment |
| US20120036370A1 (en) | 2010-07-28 | 2012-02-09 | Nextlabs, Inc. | Protecting Documents Using Policies and Encryption |
| US8126128B1 (en) | 2006-11-01 | 2012-02-28 | At&T Intellectual Property I, Lp | Life cycle management of user-selected applications on wireless communications devices |
| US8126506B2 (en) | 2007-02-14 | 2012-02-28 | Nuance Communications, Inc. | System and method for securely managing data stored on mobile devices, such as enterprise mobility data |
| US20120052954A1 (en) | 2010-08-31 | 2012-03-01 | Sony Computer Entertainment Inc. | Offline Progress of Console Game via Portable Device |
| EP2428894A1 (en) | 2010-09-14 | 2012-03-14 | AppSense Limited | Private application clipboard |
| US20120084184A1 (en) | 2008-06-05 | 2012-04-05 | Raleigh Gregory G | Enterprise Access Control and Accounting Allocation for Access Networks |
| US20120088540A1 (en) | 2010-10-07 | 2012-04-12 | Research In Motion Limited | Provisioning Based on Application and Device Capability |
| US20120109384A1 (en) | 2005-08-19 | 2012-05-03 | Nexstep, Inc. | Consumer electronic registration, control and support concierge device and method |
| US20120117622A1 (en) | 2007-02-05 | 2012-05-10 | Kaj Gronholm | Dynamic network access control method and apparatus |
| US20120129503A1 (en) | 2010-11-19 | 2012-05-24 | MobileIron, Inc. | Management of Mobile Applications |
| US20120131685A1 (en) | 2010-11-19 | 2012-05-24 | MobileIron, Inc. | Mobile Posture-based Policy, Remediation and Access Control for Enterprise Resources |
| US20120131116A1 (en) | 2010-11-15 | 2012-05-24 | Van Quy Tu | Controlling data transfer on mobile devices |
| US20120157166A1 (en) | 2010-12-21 | 2012-06-21 | Dongwoo Kim | Mobile terminal and method of managing information therein |
| US20120154413A1 (en) | 2010-12-21 | 2012-06-21 | Dongwoo Kim | Mobile terminal and method of controlling a mode switching therein |
| US20120159139A1 (en) | 2010-12-21 | 2012-06-21 | Dongwoo Kim | Mobile terminal and method of controlling a mode switching therein |
| US20120157165A1 (en) | 2010-12-21 | 2012-06-21 | Dongwoo Kim | Mobile terminal and method of controlling a mode switching therein |
| US20120165075A1 (en) | 2010-12-22 | 2012-06-28 | Lg Electronics Inc. | Mobile terminal and method of displaying information therein |
| US20120167118A1 (en) | 2010-12-27 | 2012-06-28 | Microsoft Corporation | Power management via coordination and selective operation of timer-related tasks |
| US20120166997A1 (en) | 2010-12-22 | 2012-06-28 | Hyunah Cho | Mobile terminal and method of sharing information therein |
| US20120166524A1 (en) | 2010-12-27 | 2012-06-28 | Takeshi Watakabe | Information Processing Apparatus and Removable Media Management Method |
| US8214887B2 (en) | 2005-03-20 | 2012-07-03 | Actividentity (Australia) Pty Ltd. | Method and system for providing user access to a secure application |
| US20120179909A1 (en) | 2011-01-06 | 2012-07-12 | Pitney Bowes Inc. | Systems and methods for providing individual electronic document secure storage, retrieval and use |
| US20120179802A1 (en) | 2011-01-10 | 2012-07-12 | Fiberlink Communications Corporation | System and method for extending cloud services into the customer premise |
| US20120185913A1 (en) | 2008-06-19 | 2012-07-19 | Servicemesh, Inc. | System and method for a cloud computing abstraction layer with security zone facilities |
| US20120185910A1 (en) | 2011-01-14 | 2012-07-19 | Nokia Corporation | Method and apparatus for adjusting context-based factors for selecting a security policy |
| US20120198570A1 (en) | 2011-02-01 | 2012-08-02 | Bank Of America Corporation | Geo-Enabled Access Control |
| US8239918B1 (en) | 2011-10-11 | 2012-08-07 | Google Inc. | Application marketplace administrative controls |
| US8238256B2 (en) | 2008-09-08 | 2012-08-07 | Nugent Raymond M | System and method for cloud computing |
| US20120204220A1 (en) | 2011-02-07 | 2012-08-09 | Tufin Software Technologies Ltd. | Method of analyzing security ruleset and system thereof |
| US20120214472A1 (en) | 2009-10-31 | 2012-08-23 | Saied Tadayon | Method and System for Controlling Mobile Device Functions via a Service or Background Process |
| US20120222120A1 (en) | 2011-02-24 | 2012-08-30 | Samsung Electronics Co. Ltd. | Malware detection method and mobile terminal realizing the same |
| US8272030B1 (en) | 2009-01-21 | 2012-09-18 | Sprint Communications Company L.P. | Dynamic security management for mobile communications device |
| US20120240183A1 (en) | 2011-03-18 | 2012-09-20 | Amit Sinha | Cloud based mobile device security and policy enforcement |
| US20120238257A1 (en) | 2011-03-16 | 2012-09-20 | Anson Douglas M | System and method for selectively restricting portable information handling system features |
| US20120254768A1 (en) | 2011-03-31 | 2012-10-04 | Google Inc. | Customizing mobile applications |
| US8296239B2 (en) | 2000-03-10 | 2012-10-23 | Sony Corporation | Data distribution system and method of same, data processing apparatus and method of same, and data recording medium |
| US20120272221A1 (en) | 2011-04-22 | 2012-10-25 | Microsoft Corporation | Rule based data driven validation |
| US20120278454A1 (en) | 2011-04-26 | 2012-11-01 | Stewart Brett B | Gateway Device Application Development System |
| US20120284325A1 (en) | 2011-05-02 | 2012-11-08 | Mitel Networks Corporation | Regulating use of a mobile computing device for a user at a selected location |
| US20120284779A1 (en) | 2011-05-04 | 2012-11-08 | Apple Inc. | Electronic devices having adaptive security profiles and methods for selecting the same |
| US20120290694A9 (en) | 2004-12-07 | 2012-11-15 | Brett Marl | Network administration tool |
| US20120303778A1 (en) | 2011-04-28 | 2012-11-29 | Approxy Inc. Ltd. | Application Distribution Network |
| US20120304310A1 (en) | 2011-03-21 | 2012-11-29 | Mocana Corporation | Secure execution of unsecured apps on a device |
| US20120303476A1 (en) | 2010-11-09 | 2012-11-29 | Openpeak Inc. | Communication devices, networks, services and accompanying methods |
| US20120311154A1 (en) | 2011-05-31 | 2012-12-06 | Morgan Christopher Edwin | Systems and methods for triggering workload movement based on policy stack having multiple selectable inputs |
| US20120311659A1 (en) | 2011-06-01 | 2012-12-06 | Mobileasap, Inc. | Real-time mobile application management |
| US8332464B2 (en) | 2002-12-13 | 2012-12-11 | Anxebusiness Corp. | System and method for remote network access |
| US20120324568A1 (en) | 2011-06-14 | 2012-12-20 | Lookout, Inc., A California Corporation | Mobile web protection |
| US20120331528A1 (en) | 2011-06-27 | 2012-12-27 | Osmosix, Inc. | Apparatus, systems and methods for secure and selective access to services in hybrid public-private infrastructures |
| US20120331527A1 (en) | 2011-06-22 | 2012-12-27 | TerraWi, Inc. | Multi-layer, geolocation-based network resource access and permissions |
| US20130002725A1 (en) | 2011-06-28 | 2013-01-03 | Dongwoo Kim | Mobile terminal and display controlling method therein |
| US20130007842A1 (en) | 2011-06-28 | 2013-01-03 | Hyekyung Park | Mobile terminal and display controlling method therein |
| US20130013653A1 (en) | 2009-08-05 | 2013-01-10 | International Business Machines Corporation | Tracking file contents |
| US20130014239A1 (en) | 2011-07-08 | 2013-01-10 | International Business Machines Corporation | Authenticating a rich client from within an existing browser session |
| US20130013688A1 (en) | 2011-07-07 | 2013-01-10 | Cisco Technology, Inc. | System and method for providing a message and an event based video services control plane |
| US20130024424A1 (en) | 2009-06-30 | 2013-01-24 | Commvault Systems, Inc. | Data object store and server for a cloud storage environment, including data deduplication and data management across multiple cloud storage sites |
| US20130024928A1 (en) | 2011-07-22 | 2013-01-24 | Robert James Burke | Secure network communications for meters |
| US8365258B2 (en) | 2006-11-16 | 2013-01-29 | Phonefactor, Inc. | Multi factor authentication |
| US20130042294A1 (en) | 2011-08-08 | 2013-02-14 | Microsoft Corporation | Identifying application reputation based on resource accesses |
| US20130055378A1 (en) | 2011-08-29 | 2013-02-28 | Pantech Co., Ltd. | Method and portable device for controlling permission settings for application |
| US20130054922A1 (en) | 2011-08-23 | 2013-02-28 | Vmware, Inc. | Cooperative memory resource management for virtualized computing devices |
| US20130054962A1 (en) | 2011-08-31 | 2013-02-28 | Deepak Chawla | Policy configuration for mobile device applications |
| US20130059284A1 (en) | 2011-09-07 | 2013-03-07 | Teegee, Llc | Interactive electronic toy and learning device system |
| US20130066960A1 (en) | 2011-02-28 | 2013-03-14 | Siemens Enterprise Communications Gmbh & Co. Kg | Apparatus and Mechanism for Dynamic Assignment of Survivability Services to Mobile Devices |
| US8402011B1 (en) | 2011-10-10 | 2013-03-19 | Google Inc. | System and method for managing user web browsing information |
| US20130074142A1 (en) | 2011-09-15 | 2013-03-21 | Microsoft Corporation | Securing data usage in computing devices |
| US20130086684A1 (en) | 2011-09-30 | 2013-04-04 | David S. Mohler | Contextual virtual machines for application quarantine and assessment method and system |
| US20130084847A1 (en) | 2009-07-21 | 2013-04-04 | Scott Ferrill Tibbitts | Method and system for controlling a mobile communication device |
| US8418238B2 (en) | 2008-03-30 | 2013-04-09 | Symplified, Inc. | System, method, and apparatus for managing access to resources across a network |
| US20130091543A1 (en) | 2011-10-10 | 2013-04-11 | Openpeak Inc. | System and method for creating secure applications |
| US20130097421A1 (en) | 2011-04-04 | 2013-04-18 | Nextlabs, Inc. | Protecting Information Using Policies and Encryption |
| US20130111540A1 (en) | 2011-10-28 | 2013-05-02 | Jason Allen Sabin | Cloud protection techniques |
| US20130117240A1 (en) | 2010-05-03 | 2013-05-09 | Panzura, Inc. | Accessing cached data from a peer cloud controller in a distributed filesystem |
| US20130117805A1 (en) | 2011-11-09 | 2013-05-09 | Microsoft Corporation | Techniques to apply and share remote policies on mobile devices |
| US20130130651A1 (en) | 2011-11-22 | 2013-05-23 | Vmware, Inc. | Provisioning work environments on personal mobile devices |
| US20130132457A1 (en) | 2011-11-18 | 2013-05-23 | Computer Associates Think, Inc. | System and method for hand-offs in cloud environments |
| US20130138810A1 (en) | 2011-09-09 | 2013-05-30 | Shuki Binyamin | Systems and Methods for Workspace Interaction with Cloud-Based Applications |
| US20130138766A1 (en) | 2011-11-29 | 2013-05-30 | Dell Products L.P. | Mode sensitive networking |
| US20130139241A1 (en) | 2011-11-29 | 2013-05-30 | Michael Leeder | Methods, systems, and computer readable media for bridging user authentication, authorization, and access between web-based and telecom domains |
| US20130142043A1 (en) | 2011-12-06 | 2013-06-06 | T-Mobile Usa, Inc. | Quality of service application controller and user equipment application profiler |
| US20130145448A1 (en) | 2011-08-05 | 2013-06-06 | Vmware, Inc. | Lock screens to access work environments on a personal mobile device |
| US8463946B2 (en) | 2004-09-17 | 2013-06-11 | Caterpillar Inc. | Method for automatic radio operational mode selection |
| US20130151598A1 (en) | 2011-02-09 | 2013-06-13 | Cliqr Technologies Inc. | Apparatus, systems and methods for deployment of interactive desktop applications on distributed infrastructures |
| US8468090B2 (en) | 2010-05-21 | 2013-06-18 | Hsbc Technologies Inc. | Account opening computer system architecture and process for implementing same |
| US20130171967A1 (en) | 2012-01-04 | 2013-07-04 | Ayman S. Ashour | Providing Secure Execution of Mobile Device Workflows |
| US20130219176A1 (en) | 2012-01-06 | 2013-08-22 | Venkata Sastry Akella | Secure Virtual File Management System |
| US20130219211A1 (en) | 2012-02-17 | 2013-08-22 | International Business Machines Corporation | Elastic Cloud-Driven Task Execution |
| US8528059B1 (en) | 2008-10-06 | 2013-09-03 | Goldman, Sachs & Co. | Apparatuses, methods and systems for a secure resource access and placement platform |
| US20130232541A1 (en) | 2012-03-02 | 2013-09-05 | International Business Machines Corporation | Policy-driven approach to managing privileged/shared identity in an enterprise |
| US20130254831A1 (en) | 2012-03-23 | 2013-09-26 | Lockheed Martin Corporation | Method and apparatus for context aware mobile security |
| US20130254660A1 (en) | 2008-03-13 | 2013-09-26 | Robb Fujioka | Tablet computer |
| US20130254262A1 (en) | 2012-03-26 | 2013-09-26 | Quickmobile Inc. | System and method for a user to dynamically update a mobile application from a generic or first application within a class of applications to create a specific or second application with said class of applications |
| US20130263209A1 (en) | 2012-03-30 | 2013-10-03 | Cognizant Business Services Limited | Apparatus and methods for managing applications in multi-cloud environments |
| US20130263208A1 (en) | 2012-04-02 | 2013-10-03 | Narsimha Reddy Challa | Managing virtual machines in a cloud computing system |
| US8560709B1 (en) | 2004-02-25 | 2013-10-15 | F5 Networks, Inc. | System and method for dynamic policy based access over a virtual private network |
| US20130291052A1 (en) | 2012-04-30 | 2013-10-31 | Ca, Inc. | Trusted public infrastructure grid cloud |
| US20130298185A1 (en) | 2012-05-02 | 2013-11-07 | Kony Solutions, Inc. | Mobile application management systems and methods thereof |
| US20130298201A1 (en) | 2012-05-05 | 2013-11-07 | Citrix Systems, Inc. | Systems and methods for network filtering in vpn |
| US20130298242A1 (en) | 2012-05-01 | 2013-11-07 | Taasera, Inc. | Systems and methods for providing mobile security based on dynamic attestation |
| US20130297604A1 (en) | 2012-05-01 | 2013-11-07 | Research In Motion Limited | Electronic device and method for classification of communication data objects |
| US20130303194A1 (en) | 2012-05-11 | 2013-11-14 | Iolo Technologies, Llc | Automatic determination of and reaction to mobile user routine behavior based on geographical and repetitive pattern analysis |
| US20130311597A1 (en) | 2012-05-16 | 2013-11-21 | Apple Inc. | Locally backed cloud-based storage |
| US20130318345A1 (en) | 2012-05-22 | 2013-11-28 | Harris Corporation | Multi-tunnel virtual private network |
| US8601562B2 (en) | 2007-12-10 | 2013-12-03 | Courion Corporation | Policy enforcement using ESSO |
| US20130333005A1 (en) | 2012-06-07 | 2013-12-12 | Sk Planet Co., Ltd. | Cloud service system based on enhanced security function and method for supporting the same |
| US8613070B1 (en) | 2012-10-12 | 2013-12-17 | Citrix Systems, Inc. | Single sign-on access in an orchestration framework for connected devices |
| US20130346268A1 (en) | 2012-06-21 | 2013-12-26 | Google Inc. | Mobile Application Management |
| US20140007183A1 (en) | 2011-10-11 | 2014-01-02 | Zenprise, Inc. | Controlling mobile device access to enterprise resources |
| US20140020073A1 (en) | 2012-07-13 | 2014-01-16 | Troy Jacob Ronda | Methods and systems for using derived credentials to authenticate a device across multiple platforms |
| US20140020062A1 (en) | 2012-07-11 | 2014-01-16 | Chandra Shekhar Rao Tumula | Techniques for protecting mobile applications |
| US20140032759A1 (en) | 2011-10-11 | 2014-01-30 | Citrix Systems, Inc. | Policy-Based Application Management |
| US20140032758A1 (en) | 2011-10-11 | 2014-01-30 | Citrix Systems, Inc. | Policy-Based Application Management |
| US20140040979A1 (en) | 2011-10-11 | 2014-02-06 | Citrix Systems, Inc. | Policy-Based Application Management |
| US20140040656A1 (en) | 2010-08-26 | 2014-02-06 | Adobe Systems Incorporated | System and method for managing cloud deployment configuration of an application |
| US8650620B2 (en) | 2010-12-20 | 2014-02-11 | At&T Intellectual Property I, L.P. | Methods and apparatus to control privileges of mobile device applications |
| US20140059642A1 (en) | 2012-08-24 | 2014-02-27 | Vmware, Inc. | Method and system for facilitating isolated workspace for applications |
| US20140059640A9 (en) | 2009-03-02 | 2014-02-27 | Gregory G. Raleigh | Adapting Network Policies Based on Device Service Processor Configuration |
Family Cites Families (357)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US5369702A (en) | 1993-10-18 | 1994-11-29 | Tecsec Incorporated | Distributed cryptographic object method |
| EP0880840A4 (en) | 1996-01-11 | 2002-10-23 | Mrj Inc | System for controlling access and distribution of digital property |
| US5898830A (en) | 1996-10-17 | 1999-04-27 | Network Engineering Software | Firewall providing enhanced network security and user transparency |
| JP3001489B2 (en)* | 1998-01-16 | 2000-01-24 | 新潟日本電気ソフトウェア株式会社 | TCP / IP communication network browser device |
| US6219694B1 (en) | 1998-05-29 | 2001-04-17 | Research In Motion Limited | System and method for pushing information from a host system to a mobile data communication device having a shared electronic address |
| US6480096B1 (en) | 1998-07-08 | 2002-11-12 | Motorola, Inc. | Method and apparatus for theft deterrence and secure data retrieval in a communication device |
| US7140005B2 (en) | 1998-12-21 | 2006-11-21 | Intel Corporation | Method and apparatus to test an instruction sequence |
| US7130831B2 (en) | 1999-02-08 | 2006-10-31 | Copyright Clearance Center, Inc. | Limited-use browser and security system |
| HRP20020180A2 (en) | 1999-08-31 | 2004-06-30 | American Express Travel Relate | Methods and apparatus for conducting electronic transactions |
| US20030236861A1 (en) | 2000-03-03 | 2003-12-25 | Johnson Scott C. | Network content delivery system with peer to peer processing components |
| EP1134643A3 (en) | 2000-03-14 | 2007-01-17 | Sony Corporation | Information providing apparatus and method, information processing apparatus and method, program storage medium, program, and information providing system |
| CA2305078A1 (en) | 2000-04-12 | 2001-10-12 | Cloakware Corporation | Tamper resistant software - mass data encoding |
| US7065652B1 (en) | 2000-06-21 | 2006-06-20 | Aladdin Knowledge Systems, Ltd. | System for obfuscating computer code upon disassembly |
| US7103915B2 (en) | 2000-11-13 | 2006-09-05 | Digital Doors, Inc. | Data security system and method |
| US7502861B1 (en) | 2001-02-16 | 2009-03-10 | Swsoft Holding, Ltd. | System and method for providing services for offline servers using the same network address |
| US20020120607A1 (en) | 2001-02-28 | 2002-08-29 | Lumenati, Inc. | File sharing system for serving content from a computer |
| US20020180790A1 (en) | 2001-05-31 | 2002-12-05 | International Business Machines Corporation | System and method for encapsulating software components in an application program interface using a proxy object |
| FI120065B (en)* | 2001-06-05 | 2009-06-15 | Sanako Oy | Activity control system for computer-aided learning in a network |
| US8218829B2 (en) | 2001-08-20 | 2012-07-10 | Polycom, Inc. | System and method for using biometrics technology in conferencing |
| US7143443B2 (en) | 2001-10-01 | 2006-11-28 | Ntt Docomo, Inc. | Secure sharing of personal devices among different users |
| US7904392B2 (en) | 2001-10-25 | 2011-03-08 | Panasonic Corporation | Content usage rule management system |
| US20030103075A1 (en) | 2001-12-03 | 2003-06-05 | Rosselot Robert Charles | System and method for control of conference facilities and equipment |
| EP3401794A1 (en) | 2002-01-08 | 2018-11-14 | Seven Networks, LLC | Connection architecture for a mobile network |
| US20030188193A1 (en) | 2002-03-28 | 2003-10-02 | International Business Machines Corporation | Single sign on for kerberos authentication |
| JP2003296210A (en) | 2002-04-03 | 2003-10-17 | Japan Research Institute Ltd | Method and apparatus for creating profile setting file |
| US6804777B2 (en) | 2002-05-15 | 2004-10-12 | Threatguard, Inc. | System and method for application-level virtual private network |
| US6950825B2 (en) | 2002-05-30 | 2005-09-27 | International Business Machines Corporation | Fine grained role-based access to system resources |
| US6946715B2 (en) | 2003-02-19 | 2005-09-20 | Micron Technology, Inc. | CMOS image sensor and method of fabrication |
| US6678828B1 (en) | 2002-07-22 | 2004-01-13 | Vormetric, Inc. | Secure network file access control system |
| US7043106B2 (en) | 2002-07-22 | 2006-05-09 | Applied Materials, Inc. | Optical ready wafers |
| US7110629B2 (en) | 2002-07-22 | 2006-09-19 | Applied Materials, Inc. | Optical ready substrates |
| CN1708751A (en) | 2002-08-23 | 2005-12-14 | 国际商业机器公司 | Processing application data |
| JP4012785B2 (en) | 2002-08-27 | 2007-11-21 | 日本板硝子株式会社 | Optical connection device |
| US7437752B2 (en) | 2002-09-23 | 2008-10-14 | Credant Technologies, Inc. | Client architecture for portable device with security policies |
| US7536562B2 (en) | 2002-10-17 | 2009-05-19 | Research In Motion Limited | System and method of security function activation for a mobile electronic device |
| FR2847752B1 (en) | 2002-11-27 | 2006-01-13 | At & T Corp | METHOD AND SYSTEM FOR MANAGING THE EXCHANGE OF FILES ATTACHED TO E-MAIL |
| US7353533B2 (en) | 2002-12-18 | 2008-04-01 | Novell, Inc. | Administration of protection of data accessible by a mobile device |
| JP4128443B2 (en) | 2002-12-27 | 2008-07-30 | 株式会社野村総合研究所 | Data area management method in web browser usage processing system |
| US7194254B2 (en)* | 2002-12-30 | 2007-03-20 | Motorola Inc. | Apparatus for restricted browser access within a wireless communication device and method therefor |
| AU2003300431A1 (en) | 2002-12-31 | 2004-07-29 | Bitfone Corporation | Management of service components installed in an electronic device in a mobile services network |
| WO2004066156A1 (en) | 2003-01-20 | 2004-08-05 | Fujitsu Limited | Copy prevention apparatus, copy prevention method, and program for causing computer to execute the method |
| JP3928561B2 (en) | 2003-01-23 | 2007-06-13 | ソニー株式会社 | Content distribution system, information processing apparatus or information processing method, and computer program |
| US7779408B1 (en) | 2003-03-24 | 2010-08-17 | Sprint Spectrum L.P. | Method and system for downloading and managing portable applications on a mobile device |
| US7509651B2 (en)* | 2003-05-23 | 2009-03-24 | Hewlett-Packard Development Company, L.P. | System and method for providing event notifications to information technology resource managers |
| US7543051B2 (en) | 2003-05-30 | 2009-06-02 | Borland Software Corporation | Method of non-intrusive analysis of secure and non-secure web application traffic in real-time |
| AU2003903501A0 (en) | 2003-07-07 | 2003-07-24 | Commonwealth Scientific And Industrial Research Organisation | A method of forming a reflective authentication device |
| US20050027862A1 (en) | 2003-07-18 | 2005-02-03 | Nguyen Tien Le | System and methods of cooperatively load-balancing clustered servers |
| US7089594B2 (en) | 2003-07-21 | 2006-08-08 | July Systems, Inc. | Application rights management in a mobile environment |
| US7574707B2 (en) | 2003-07-28 | 2009-08-11 | Sap Ag | Install-run-remove mechanism |
| US7515717B2 (en) | 2003-07-31 | 2009-04-07 | International Business Machines Corporation | Security containers for document components |
| US7349913B2 (en) | 2003-08-21 | 2008-03-25 | Microsoft Corporation | Storage platform for organizing, searching, and sharing data |
| SE527561C2 (en) | 2003-09-12 | 2006-04-11 | Secured Email Goeteborg Ab | Electronic mail transmission method in internet environment, involves storing seed for key generation provided from sender's terminal, in receiver's terminal |
| US20050076085A1 (en) | 2003-09-18 | 2005-04-07 | Vulcan Portals Inc. | Method and system for managing email attachments for an electronic device |
| US20050063637A1 (en) | 2003-09-22 | 2005-03-24 | Mershon Jayne L. | Connecting a component with an embedded optical fiber |
| CN1894897A (en) | 2003-09-29 | 2007-01-10 | 瑞姆系统公司 | Mobility device server |
| US20050086328A1 (en) | 2003-10-17 | 2005-04-21 | Landram Fredrick J. | Self configuring mobile device and system |
| US8483227B2 (en) | 2003-11-20 | 2013-07-09 | International Business Machines Corporation | Controlling bandwidth reservations method and apparatus |
| EP2184934B1 (en) | 2003-12-29 | 2012-12-05 | Telefonaktiebolaget L M Ericsson (PUBL) | Method and apparatuses for single sign-on access to a service network through an access network |
| US9224131B2 (en) | 2003-12-29 | 2015-12-29 | International Business Machines Corporation | System and method for facilitating collaboration in a shared email repository |
| US7720461B2 (en) | 2004-02-26 | 2010-05-18 | Research In Motion Limited | Mobile communications device with security features |
| US20050193222A1 (en) | 2004-03-01 | 2005-09-01 | Greene William S. | Providing secure data and policy exchange between domains in a multi-domain grid by use of a service ecosystem facilitating uses such as supply-chain integration with RIFD tagged items and barcodes |
| US7549048B2 (en) | 2004-03-19 | 2009-06-16 | Microsoft Corporation | Efficient and secure authentication of computing systems |
| US7509672B1 (en) | 2004-04-01 | 2009-03-24 | Compuware Corporation | Cross-platform single sign-on data sharing |
| US7263256B2 (en) | 2004-04-02 | 2007-08-28 | Samsung Electronics Co., Ltd. | Optical connection block, optical module, and optical axis alignment method using the same |
| US7492946B2 (en) | 2004-05-24 | 2009-02-17 | Michael James Elder | System, method and computer program for an integrated digital workflow for processing a paper form |
| US7631360B2 (en) | 2004-06-12 | 2009-12-08 | Microsoft Corporation | Hardware protection |
| JP2006013747A (en) | 2004-06-24 | 2006-01-12 | Murata Mach Ltd | Electronic mail server apparatus and electronic mail network system |
| EP2264956B1 (en) | 2004-07-23 | 2017-06-14 | Citrix Systems, Inc. | Method for securing remote access to private networks |
| US20060048142A1 (en) | 2004-09-02 | 2006-03-02 | Roese John J | System and method for rapid response network policy implementation |
| US20060080432A1 (en) | 2004-09-03 | 2006-04-13 | Spataro Jared M | Systems and methods for collaboration |
| US7949706B2 (en) | 2004-09-24 | 2011-05-24 | At&T Intellectual Property I, L.P. | Automatic electronic publishing |
| JP2006094258A (en) | 2004-09-27 | 2006-04-06 | Nippon Telegr & Teleph Corp <Ntt> | Terminal device, policy enforcement method thereof, and program thereof |
| US7721328B2 (en)* | 2004-10-01 | 2010-05-18 | Salesforce.Com Inc. | Application identity design |
| US8086519B2 (en)* | 2004-10-14 | 2011-12-27 | Cfph, Llc | System and method for facilitating a wireless financial transaction |
| US7109051B2 (en) | 2004-11-15 | 2006-09-19 | Freescale Semiconductor, Inc. | Method of integrating optical devices and electronic devices on an integrated circuit |
| US20060112428A1 (en) | 2004-11-23 | 2006-05-25 | Nokia Corporation | Device having a locking feature and a method, means and software for utilizing the feature |
| JP2006155522A (en)* | 2004-12-01 | 2006-06-15 | Canon Inc | WEB browser operation method and operation device |
| US7562226B2 (en) | 2005-01-14 | 2009-07-14 | Citrix Systems, Inc. | System and method for permission-based access using a shared account |
| US20060185004A1 (en) | 2005-02-11 | 2006-08-17 | Samsung Electronics Co., Ltd. | Method and system for single sign-on in a network |
| US20060256739A1 (en) | 2005-02-19 | 2006-11-16 | Kenneth Seier | Flexible multi-media data management |
| US8565726B2 (en) | 2008-11-06 | 2013-10-22 | Mcafee, Inc. | System, method and device for mediating connections between policy source servers, corporate repositories, and mobile devices |
| US20060200814A1 (en) | 2005-03-02 | 2006-09-07 | Nokia Corporation | Software distribution with activation control |
| US7844958B2 (en) | 2005-03-11 | 2010-11-30 | Aptana, Inc. | System and method for creating target byte code |
| US7472375B2 (en) | 2005-03-29 | 2008-12-30 | Intel Corporation | Creating managed code from native code |
| US7631297B2 (en) | 2005-04-05 | 2009-12-08 | International Business Machines Corporation | Autonomic computing: management agent utilizing action policy for operation |
| US7490352B2 (en) | 2005-04-07 | 2009-02-10 | Microsoft Corporation | Systems and methods for verifying trust of executable files |
| US20060248577A1 (en) | 2005-04-29 | 2006-11-02 | International Business Machines Corporation | Using SSO processes to manage security credentials in a provisioning management system |
| US7945788B2 (en) | 2005-05-03 | 2011-05-17 | Strong Bear L.L.C. | Removable drive with data encryption |
| US20070024646A1 (en) | 2005-05-23 | 2007-02-01 | Kalle Saarinen | Portable electronic apparatus and associated method |
| US7565689B2 (en) | 2005-06-08 | 2009-07-21 | Research In Motion Limited | Virtual private network for real-time data |
| US7591002B2 (en) | 2005-06-09 | 2009-09-15 | Microsoft Corporation | Conditional activation of security policies |
| US7793333B2 (en) | 2005-06-13 | 2010-09-07 | International Business Machines Corporation | Mobile authorization using policy based access control |
| US8010997B2 (en)* | 2005-06-30 | 2011-08-30 | Microsoft Corporation | Enforcing device settings for mobile devices |
| US20070016771A1 (en) | 2005-07-11 | 2007-01-18 | Simdesk Technologies, Inc. | Maintaining security for file copy operations |
| US20070016907A1 (en) | 2005-07-12 | 2007-01-18 | Fabio Benedetti | Method, system and computer program for automatic provisioning of resources to scheduled jobs |
| US8321953B2 (en) | 2005-07-14 | 2012-11-27 | Imation Corp. | Secure storage device with offline code entry |
| US9864628B2 (en) | 2005-08-23 | 2018-01-09 | Blackberry Limited | Method and system for transferring an application state from a first electronic device to a second electronic device |
| US20070283324A1 (en) | 2005-08-30 | 2007-12-06 | Geisinger Nile J | System and method for creating programs that comprise several execution layers |
| KR100723700B1 (en) | 2005-08-31 | 2007-05-30 | 에스케이 텔레콤주식회사 | Method and system for remotely controlling the operation of mobile communication terminal |
| US7779458B1 (en) | 2005-09-20 | 2010-08-17 | Rockwell Collins, Inc. | Situation aware mobile location ad hoc firewall |
| US20070072598A1 (en) | 2005-09-23 | 2007-03-29 | Coleman David T | Controlling wireless communication devices with media recording capabilities |
| GB2430772A (en) | 2005-10-01 | 2007-04-04 | Knowledge Support Systems Ltd | User interface method and apparatus |
| US7870493B2 (en) | 2005-10-03 | 2011-01-11 | Microsoft Corporation | Distributed clipboard |
| US8745223B2 (en) | 2005-10-14 | 2014-06-03 | Psion Inc. | System and method of distributed license management |
| KR101285024B1 (en) | 2005-10-18 | 2013-08-27 | 인터트러스트 테크놀로지즈 코포레이션 | Methods for digital rights management |
| US7437755B2 (en) | 2005-10-26 | 2008-10-14 | Cisco Technology, Inc. | Unified network and physical premises access control server |
| US20070100938A1 (en) | 2005-10-27 | 2007-05-03 | Bagley Elizabeth V | Participant-centered orchestration/timing of presentations in collaborative environments |
| WO2007053848A1 (en) | 2005-11-01 | 2007-05-10 | Mobile Armor, Llc | Centralized dynamic security control for a mobile device network |
| US8305422B2 (en) | 2005-11-08 | 2012-11-06 | Sharp Kabushiki Kaisha | Communication device, communication method, communication system, program, and computer-readable storage medium |
| US20070248085A1 (en) | 2005-11-12 | 2007-10-25 | Cranite Systems | Method and apparatus for managing hardware address resolution |
| US7921303B2 (en) | 2005-11-18 | 2011-04-05 | Qualcomm Incorporated | Mobile security system and method |
| US8045958B2 (en) | 2005-11-21 | 2011-10-25 | Research In Motion Limited | System and method for application program operation on a wireless device |
| TWI405094B (en) | 2005-11-28 | 2013-08-11 | Ibm | System for preventing unauthorized acquisition of information, and method thereof |
| US8286002B2 (en) | 2005-12-02 | 2012-10-09 | Alcatel Lucent | Method and apparatus for providing secure remote access to enterprise networks |
| US20070180509A1 (en) | 2005-12-07 | 2007-08-02 | Swartz Alon R | Practical platform for high risk applications |
| US20070136471A1 (en) | 2005-12-12 | 2007-06-14 | Ip3 Networks | Systems and methods for negotiating and enforcing access to network resources |
| GB2433794B (en) | 2005-12-21 | 2010-08-18 | Advanced Risc Mach Ltd | Interrupt controller utiilising programmable priority values |
| WO2007074420A2 (en) | 2005-12-26 | 2007-07-05 | Koninklijke Philips Electronics N.V. | Method and device for rights management |
| US7716240B2 (en) | 2005-12-29 | 2010-05-11 | Nextlabs, Inc. | Techniques and system to deploy policies intelligently |
| US8132242B1 (en) | 2006-02-13 | 2012-03-06 | Juniper Networks, Inc. | Automated authentication of software applications using a limited-use token |
| US20070226034A1 (en) | 2006-03-23 | 2007-09-27 | Kyocera Wireless Corp. | Wireless communication device meeting scheduler |
| US7774323B2 (en) | 2006-03-27 | 2010-08-10 | Sap Portals Israel Ltd. | Method and apparatus for delivering managed applications to remote locations |
| EP2002634B1 (en) | 2006-03-27 | 2014-07-02 | Telecom Italia S.p.A. | System for enforcing security policies on mobile communications devices |
| US9112897B2 (en)* | 2006-03-30 | 2015-08-18 | Advanced Network Technology Laboratories Pte Ltd. | System and method for securing a network session |
| US8151323B2 (en) | 2006-04-12 | 2012-04-03 | Citrix Systems, Inc. | Systems and methods for providing levels of access and action control via an SSL VPN appliance |
| US8181010B1 (en) | 2006-04-17 | 2012-05-15 | Oracle America, Inc. | Distributed authentication user interface system |
| US7454102B2 (en) | 2006-04-26 | 2008-11-18 | Honeywell International Inc. | Optical coupling structure |
| US8700772B2 (en) | 2006-05-03 | 2014-04-15 | Cloud Systems, Inc. | System and method for automating the management, routing, and control of multiple devices and inter-device connections |
| US7890612B2 (en) | 2006-05-08 | 2011-02-15 | Electro Guard Corp. | Method and apparatus for regulating data flow between a communications device and a network |
| US20070266421A1 (en) | 2006-05-12 | 2007-11-15 | Redcannon, Inc. | System, method and computer program product for centrally managing policies assignable to a plurality of portable end-point security devices over a network |
| US7574090B2 (en) | 2006-05-12 | 2009-08-11 | Toshiba America Electronic Components, Inc. | Semiconductor device using buried oxide layer as optical wave guides |
| US7743260B2 (en) | 2006-05-17 | 2010-06-22 | Richard Fetik | Firewall+storage apparatus, method and system |
| US20080046580A1 (en) | 2006-06-29 | 2008-02-21 | Nokia Corporation | Account creation system and call processing system |
| JP2008033751A (en) | 2006-07-31 | 2008-02-14 | Ziosoft Inc | Update method and update system |
| US20080047006A1 (en) | 2006-08-21 | 2008-02-21 | Pantech Co., Ltd. | Method for registering rights issuer and domain authority in digital rights management and method for implementing secure content exchange functions using the same |
| US8245285B1 (en) | 2006-09-22 | 2012-08-14 | Oracle America, Inc. | Transport-level web application security on a resource-constrained device |
| US8327427B2 (en) | 2006-09-25 | 2012-12-04 | Rockstar Consortium Us Lp | System and method for transparent single sign-on |
| JP2008096484A (en) | 2006-10-06 | 2008-04-24 | Sony Corp | Optical semiconductor apparatus |
| JP4959282B2 (en) | 2006-10-13 | 2012-06-20 | 中国電力株式会社 | Application operation control system and application operation control method |
| US9135444B2 (en) | 2006-10-19 | 2015-09-15 | Novell, Inc. | Trusted platform module (TPM) assisted data center management |
| US8259568B2 (en) | 2006-10-23 | 2012-09-04 | Mcafee, Inc. | System and method for controlling mobile device access to a network |
| CN101170401B (en) | 2006-10-27 | 2011-02-02 | 鸿富锦精密工业(深圳)有限公司 | Email encryption/decryption system and its method |
| US8281299B2 (en) | 2006-11-10 | 2012-10-02 | Purdue Research Foundation | Map-closure: a general purpose mechanism for nonstandard interpretation |
| GB2446199A (en) | 2006-12-01 | 2008-08-06 | David Irvine | Secure, decentralised and anonymous peer-to-peer network |
| JP5070835B2 (en) | 2006-12-26 | 2012-11-14 | 日本電気株式会社 | Function limiting method for portable terminal and portable terminal |
| CA2578472C (en) | 2007-01-12 | 2013-01-15 | Truecontext Corporation | Methods and system for orchestrating services and data sharing on mobile devices |
| JP5133973B2 (en) | 2007-01-18 | 2013-01-30 | パナソニック株式会社 | Obfuscation support device, obfuscation support method, program, and integrated circuit |
| US8214451B2 (en) | 2007-01-19 | 2012-07-03 | Alcatel Lucent | Network service version management |
| US8909702B2 (en) | 2007-01-29 | 2014-12-09 | Fuji Xerox Co., Ltd. | System and method for coordination of devices in a presentation environment |
| US7644377B1 (en) | 2007-01-31 | 2010-01-05 | Hewlett-Packard Development Company, L.P. | Generating a configuration of a system that satisfies constraints contained in models |
| US8095517B2 (en) | 2007-02-08 | 2012-01-10 | Blue Coat Systems, Inc. | Method and system for policy-based protection of application data |
| US8689334B2 (en) | 2007-02-28 | 2014-04-01 | Alcatel Lucent | Security protection for a customer programmable platform |
| US20080229117A1 (en) | 2007-03-07 | 2008-09-18 | Shin Kang G | Apparatus for preventing digital piracy |
| JP4973246B2 (en) | 2007-03-09 | 2012-07-11 | 日本電気株式会社 | Access right management system, server, and access right management program |
| WO2008114256A2 (en) | 2007-03-22 | 2008-09-25 | Neocleus Ltd. | Trusted local single sign-on |
| CN101281461B (en) | 2007-04-04 | 2012-07-04 | 国际商业机器公司 | Method and device for transfer applying dependent system environment |
| US8484693B2 (en) | 2007-04-27 | 2013-07-09 | Gregory W. Cox | Efficient policy conflict detection |
| US20080270240A1 (en) | 2007-04-30 | 2008-10-30 | Viva Chu | Systems and methods of managing tasks assigned to an individual |
| US20080313257A1 (en) | 2007-06-15 | 2008-12-18 | Allen James D | Method and Apparatus for Policy-Based Transfer of an Application Environment |
| US8027518B2 (en) | 2007-06-25 | 2011-09-27 | Microsoft Corporation | Automatic configuration of devices based on biometric data |
| US7895409B2 (en) | 2007-07-30 | 2011-02-22 | Hewlett-Packard Development Company, L.P. | Application inspection tool for determining a security partition |
| EP2188730A4 (en) | 2007-08-08 | 2014-09-17 | Innopath Software Inc | MANAGEMENT AND APPLICATION OF POLICIES IN MOBILE DEVICES |
| US20090049425A1 (en) | 2007-08-14 | 2009-02-19 | Aladdin Knowledge Systems Ltd. | Code Obfuscation By Reference Linking |
| US8306509B2 (en) | 2007-08-31 | 2012-11-06 | At&T Mobility Ii Llc | Enhanced messaging with language translation feature |
| EP2034687B1 (en) | 2007-09-04 | 2012-06-13 | Research In Motion Limited | System and method for processing attachments to messages sent to a mobile device |
| JP2009070073A (en) | 2007-09-12 | 2009-04-02 | Sumitomo Electric Ind Ltd | Information processing apparatus and agent computer program |
| US8554176B2 (en) | 2007-09-18 | 2013-10-08 | Qualcomm Incorporated | Method and apparatus for creating a remotely activated secure backup service for mobile handsets |
| US20090100529A1 (en) | 2007-10-11 | 2009-04-16 | Noam Livnat | Device, system, and method of file-utilization management |
| WO2009062194A1 (en) | 2007-11-09 | 2009-05-14 | Proxense, Llc | Proximity-sensor supporting multiple application services |
| US8060596B1 (en) | 2007-12-26 | 2011-11-15 | Symantec Corporation | Methods and systems for normalizing data loss prevention categorization information |
| US20090172657A1 (en) | 2007-12-28 | 2009-07-02 | Nokia, Inc. | System, Method, Apparatus, Mobile Terminal and Computer Program Product for Providing Secure Mixed-Language Components to a System Dynamically |
| US20090171906A1 (en) | 2008-01-02 | 2009-07-02 | Research In Motion Limited | System and method for providing information relating to an email being provided to an electronic device |
| ES2963388T3 (en) | 2008-01-16 | 2024-03-26 | Blackberry Ltd | Secured Presentation Layer Virtualization for Handheld Wireless Communication Devices |
| WO2009094372A1 (en) | 2008-01-22 | 2009-07-30 | Authentium, Inc. | System and method for protecting data accessed through a network connection |
| US20090199178A1 (en) | 2008-02-01 | 2009-08-06 | Microsoft Corporation | Virtual Application Management |
| CA2700689A1 (en) | 2008-02-15 | 2009-08-20 | Citrix Systems, Inc. | Systems and methods for secure handling of secure attention sequences |
| US9185554B2 (en) | 2008-02-15 | 2015-11-10 | Appcentral, Inc. | System and methods to store, retrieve, manage, augment and monitor applications on appliances |
| JPWO2009104721A1 (en) | 2008-02-21 | 2011-06-23 | 日本電気株式会社 | Mobile terminal context efficiency utilization method and system |
| US8078713B1 (en) | 2008-03-05 | 2011-12-13 | Full Armor Corporation | Delivering policy settings with virtualized applications |
| US9576157B2 (en) | 2008-04-02 | 2017-02-21 | Yougetitback Limited | Method for mitigating the unauthorized use of a device |
| US20090319772A1 (en) | 2008-04-25 | 2009-12-24 | Netapp, Inc. | In-line content based security for data at rest in a network storage system |
| CN101572678B (en) | 2008-04-30 | 2012-09-19 | 北京明朝万达科技有限公司 | Mail attachment transparent privacy control method |
| US8156204B2 (en) | 2008-05-07 | 2012-04-10 | Chalk Media Service Corp. | Method for enabling bandwidth management for mobile content delivery |
| US8549657B2 (en) | 2008-05-12 | 2013-10-01 | Microsoft Corporation | Owner privacy in a shared mobile device |
| CN101588353B (en) | 2008-05-21 | 2012-09-19 | 闪联信息技术工程中心有限公司 | Method, system and equipment for sharing files |
| JP5326363B2 (en) | 2008-05-30 | 2013-10-30 | 株式会社リコー | Image forming apparatus, authentication control method, and program |
| US8406748B2 (en) | 2009-01-28 | 2013-03-26 | Headwater Partners I Llc | Adaptive ambient services |
| US8204196B2 (en) | 2008-06-25 | 2012-06-19 | International Business Machines Corporation | Notification to absent teleconference invitees |
| JP5577527B2 (en)* | 2008-06-25 | 2014-08-27 | 日本電気株式会社 | Information processing system, personal information device, and access management method |
| US8117589B2 (en) | 2008-06-26 | 2012-02-14 | Microsoft Corporation | Metadata driven API development |
| US8156442B2 (en) | 2008-06-30 | 2012-04-10 | Nokia Corporation | Life recorder and sharing |
| US8584114B2 (en) | 2008-06-30 | 2013-11-12 | Mo'minis Ltd | Method of generating and distributing a computer application |
| US8862672B2 (en) | 2008-08-25 | 2014-10-14 | Microsoft Corporation | Content sharing and instant messaging |
| CN101350814A (en) | 2008-08-26 | 2009-01-21 | 成都卫士通信息产业股份有限公司 | Safety remote access technology and gateway thereof |
| CN101662765B (en) | 2008-08-29 | 2013-08-07 | 深圳富泰宏精密工业有限公司 | Encryption system and method of short message of mobile telephone |
| US8365183B2 (en) | 2008-09-02 | 2013-01-29 | Ca, Inc. | System and method for dynamic resource provisioning for job placement |
| US8387110B1 (en) | 2010-02-10 | 2013-02-26 | Socialware, Inc. | Method, system and computer program product for tagging content on uncontrolled web application |
| US9495538B2 (en) | 2008-09-25 | 2016-11-15 | Symantec Corporation | Graduated enforcement of restrictions according to an application's reputation |
| US20100083358A1 (en) | 2008-09-29 | 2010-04-01 | Perfios Software Solutions Pvt. Ltd | Secure Data Aggregation While Maintaining Privacy |
| US20120137364A1 (en) | 2008-10-07 | 2012-05-31 | Mocana Corporation | Remote attestation of a mobile device |
| US20100125730A1 (en) | 2008-11-17 | 2010-05-20 | David Dodgson | Block-level data storage security system |
| US20100146582A1 (en) | 2008-12-04 | 2010-06-10 | Dell Products L.P. | Encryption management in an information handling system |
| US8245223B2 (en) | 2008-12-23 | 2012-08-14 | Microsoft Corporation | Networked deployment of multi-application customizations |
| US8505078B2 (en) | 2008-12-28 | 2013-08-06 | Qualcomm Incorporated | Apparatus and methods for providing authorized device access |
| US8856909B1 (en) | 2009-01-23 | 2014-10-07 | Juniper Networks, Inc. | IF-MAP provisioning of resources and services |
| US20100228961A1 (en) | 2009-03-03 | 2010-09-09 | Erf Wireless, Inc. | Hierarchical secure networks |
| US20100228825A1 (en) | 2009-03-06 | 2010-09-09 | Microsoft Corporation | Smart meeting room |
| US20100235216A1 (en) | 2009-03-16 | 2010-09-16 | Microsoft Corporation | Integration of pre-meeting and post-meeting experience into a meeting lifecycle |
| CN101854340B (en) | 2009-04-03 | 2015-04-01 | 瞻博网络公司 | Behavior based communication analysis carried out based on access control information |
| US8666367B2 (en) | 2009-05-01 | 2014-03-04 | Apple Inc. | Remotely locating and commanding a mobile device |
| US8660530B2 (en) | 2009-05-01 | 2014-02-25 | Apple Inc. | Remotely receiving and communicating commands to a mobile device for execution by the mobile device |
| CN101888597A (en) | 2009-05-11 | 2010-11-17 | 河北省烟草公司张家口市公司 | Mobile OA system of mobile phone terminal |
| EP2251986A1 (en) | 2009-05-15 | 2010-11-17 | Nxp B.V. | A near field communication device |
| US9858925B2 (en) | 2009-06-05 | 2018-01-02 | Apple Inc. | Using context information to facilitate processing of commands in a virtual assistant |
| US9141412B2 (en) | 2009-06-16 | 2015-09-22 | Microsoft Technology Licensing, Llc | Terminal services application virtualization for compatibility |
| US9621516B2 (en) | 2009-06-24 | 2017-04-11 | Vmware, Inc. | Firewall configured with dynamic membership sets representing machine attributes |
| US8839422B2 (en) | 2009-06-30 | 2014-09-16 | George Mason Research Foundation, Inc. | Virtual browsing environment |
| US8048795B2 (en) | 2009-07-10 | 2011-11-01 | Taiwan Semiconductor Manufacturing Company, Ltd. | Self-assembly pattern for semiconductor integrated circuit |
| CA2698066A1 (en) | 2009-07-31 | 2011-01-31 | Nitobi Software Inc. | System and method for remotely compiling multi-platform native applications for mobile devices |
| US8281381B2 (en) | 2009-08-03 | 2012-10-02 | Novell, Inc. | Techniques for environment single sign on |
| WO2011018827A1 (en) | 2009-08-13 | 2011-02-17 | 株式会社日立製作所 | System and method for evaluating adequacy of applications in execution environments |
| WO2011026530A1 (en) | 2009-09-07 | 2011-03-10 | Tomtom International B.V. | Navigation apparatus and method of supporting hands-free voice communication |
| US8200626B1 (en) | 2009-09-18 | 2012-06-12 | Sprint Communications Company L.P. | Mobile device file management |
| US8972878B2 (en) | 2009-09-21 | 2015-03-03 | Avaya Inc. | Screen icon manipulation by context and frequency of Use |
| JP4527802B2 (en) | 2009-10-19 | 2010-08-18 | 日本電気株式会社 | Computer system |
| US8850423B2 (en) | 2009-10-29 | 2014-09-30 | International Business Machines Corporation | Assisting server migration |
| EP2334034B1 (en) | 2009-11-11 | 2018-06-27 | BlackBerry Limited | Using a trusted token and push for validating the request for single sign on |
| US8595284B2 (en) | 2009-12-14 | 2013-11-26 | Samsung Electronics Co., Ltd | Web application script migration |
| US9244533B2 (en) | 2009-12-17 | 2016-01-26 | Microsoft Technology Licensing, Llc | Camera navigation for presentations |
| US8495746B2 (en) | 2009-12-18 | 2013-07-23 | Verizon Patent And Licensing Inc. | Apparatuses, methods and systems of an application security management platform |
| JP2011138446A (en) | 2009-12-30 | 2011-07-14 | Takashi Oshita | File encryption system which easily operable of encrypted independent file group on dedicated operation screen |
| WO2011091056A1 (en) | 2010-01-19 | 2011-07-28 | Servicemesh, Inc. | System and method for a cloud computing abstraction layer |
| WO2011103385A1 (en) | 2010-02-22 | 2011-08-25 | Avaya Inc. | Secure, policy-based communications security and file sharing across mixed media, mixed-communications modalities and extensible to cloud computing such as soa |
| US20110208797A1 (en) | 2010-02-22 | 2011-08-25 | Full Armor Corporation | Geolocation-Based Management of Virtual Applications |
| JP2011191897A (en) | 2010-03-12 | 2011-09-29 | Murata Machinery Ltd | Image taking out management system, portable image display terminal, and image management device |
| US20110252459A1 (en) | 2010-04-12 | 2011-10-13 | Walsh Robert E | Multiple Server Access Management |
| US20110314534A1 (en) | 2010-04-14 | 2011-12-22 | Lee James | Secured Execution Environments and Methods |
| US9282097B2 (en) | 2010-05-07 | 2016-03-08 | Citrix Systems, Inc. | Systems and methods for providing single sign on access to enterprise SAAS and cloud hosted applications |
| US9461996B2 (en) | 2010-05-07 | 2016-10-04 | Citrix Systems, Inc. | Systems and methods for providing a single click access to enterprise, SAAS and cloud hosted application |
| EP2569705A4 (en) | 2010-05-09 | 2014-05-14 | Citrix Systems Inc | SYSTEMS AND METHODS FOR CREATING AND DELIVERING CRYPTED VIRTUAL DISKS |
| US20110296333A1 (en) | 2010-05-25 | 2011-12-01 | Bateman Steven S | User interaction gestures with virtual keyboard |
| US8972980B2 (en) | 2010-05-28 | 2015-03-03 | Bromium, Inc. | Automated provisioning of secure virtual execution environment using virtual machine templates based on requested activity |
| US8127350B2 (en) | 2010-06-30 | 2012-02-28 | Juniper Networks, Inc. | Multi-service VPN network client for mobile device |
| US9560036B2 (en) | 2010-07-08 | 2017-01-31 | International Business Machines Corporation | Cross-protocol federated single sign-on (F-SSO) for cloud enablement |
| US8474017B2 (en) | 2010-07-23 | 2013-06-25 | Verizon Patent And Licensing Inc. | Identity management and single sign-on in a heterogeneous composite service scenario |
| JP5732767B2 (en) | 2010-07-26 | 2015-06-10 | 富士通株式会社 | PROCESSING DEVICE, PROCESSING METHOD, PROCESSING PROGRAM, COMPUTER-READABLE RECORDING MEDIUM CONTAINING THE PROGRAM |
| US8880580B2 (en) | 2010-07-28 | 2014-11-04 | Admiemobile Llc | Systems and methods for establishing and maintaining virtual computing clouds |
| US9936333B2 (en) | 2010-08-10 | 2018-04-03 | Microsoft Technology Licensing, Llc | Location and contextual-based mobile application promotion and delivery |
| US8539561B2 (en) | 2010-08-24 | 2013-09-17 | International Business Machines Corporation | Systems and methods to control device endpoint behavior using personae and policies |
| US9582673B2 (en) | 2010-09-27 | 2017-02-28 | Microsoft Technology Licensing, Llc | Separation of duties checks from entitlement sets |
| JP5620781B2 (en) | 2010-10-14 | 2014-11-05 | キヤノン株式会社 | Information processing apparatus, control method thereof, and program |
| US20120110317A1 (en) | 2010-10-29 | 2012-05-03 | Verizon Patent And Licensing Inc. | Content download manager |
| KR20120057734A (en) | 2010-11-22 | 2012-06-07 | 삼성전자주식회사 | Server, device accessing server and control method |
| US9219744B2 (en) | 2010-12-08 | 2015-12-22 | At&T Intellectual Property I, L.P. | Mobile botnet mitigation |
| US8918834B1 (en) | 2010-12-17 | 2014-12-23 | Amazon Technologies, Inc. | Creating custom policies in a remote-computing environment |
| AU2011202838B2 (en) | 2010-12-21 | 2014-04-10 | Lg Electronics Inc. | Mobile terminal and method of controlling a mode screen display therein |
| US9110743B2 (en) | 2010-12-21 | 2015-08-18 | Microsoft Technology Licensing, Llc | Extensible system action for sharing while remaining in context |
| US8931037B2 (en) | 2010-12-27 | 2015-01-06 | Microsoft Corporation | Policy-based access to virtualized applications |
| US20120174237A1 (en) | 2010-12-31 | 2012-07-05 | Openpeak Inc. | Location aware self-locking system and method for a mobile device |
| CN102591802A (en) | 2011-01-05 | 2012-07-18 | 广州市国迈科技有限公司 | USB flash disk with stored files openable while irreproducible |
| US9612855B2 (en) | 2011-01-10 | 2017-04-04 | International Business Machines Corporation | Virtual machine migration based on the consent by the second virtual machine running of the target host |
| US9306933B2 (en) | 2011-02-11 | 2016-04-05 | Mocana Corporation | Ensuring network connection security between a wrapped app and a remote server |
| US8549656B2 (en) | 2011-02-11 | 2013-10-01 | Mocana Corporation | Securing and managing apps on a device |
| US20120209949A1 (en) | 2011-02-14 | 2012-08-16 | Alexandros Deliyannis | Methods and apparatus to monitor media content |
| US8996807B2 (en) | 2011-02-15 | 2015-03-31 | Intelligent Intellectual Property Holdings 2 Llc | Systems and methods for a multi-level cache |
| US9544396B2 (en) | 2011-02-23 | 2017-01-10 | Lookout, Inc. | Remote application installation and control for a mobile device |
| US20120233130A1 (en) | 2011-03-11 | 2012-09-13 | Nagarajan Vedachalam | System and method for archiving emails |
| US20120238206A1 (en) | 2011-03-14 | 2012-09-20 | Research In Motion Limited | Communications device providing near field communication (nfc) secure element disabling features related methods |
| US8955142B2 (en) | 2011-03-21 | 2015-02-10 | Mocana Corporation | Secure execution of unsecured apps on a device |
| US8812868B2 (en) | 2011-03-21 | 2014-08-19 | Mocana Corporation | Secure execution of unsecured apps on a device |
| WO2012128682A1 (en) | 2011-03-22 | 2012-09-27 | Telefonaktiebolaget L M Ericsson (Publ) | Methods for exchanging user profile, profile mediator device, agents, computer programs and computer program products |
| US20120246191A1 (en) | 2011-03-24 | 2012-09-27 | True Xiong | World-Wide Video Context Sharing |
| US8621620B2 (en) | 2011-03-29 | 2013-12-31 | Mcafee, Inc. | System and method for protecting and securing storage devices using below-operating system trapping |
| US20120250106A1 (en) | 2011-03-30 | 2012-10-04 | Infosys Technologies Ltd. | Method, device and system for updating an application on a mobile device |
| US8458802B2 (en) | 2011-04-02 | 2013-06-04 | Intel Corporation | Method and device for managing digital usage rights of documents |
| US8898629B2 (en) | 2011-04-06 | 2014-11-25 | Media Direct, Inc. | Systems and methods for a mobile application development and deployment platform |
| EP2523107B1 (en) | 2011-04-19 | 2018-11-07 | LG Electronics Inc. | Mobile terminal and system for managing applications using the same |
| KR20120118819A (en) | 2011-04-19 | 2012-10-29 | 엘지전자 주식회사 | Mobile terminal and system for managing applications using the same |
| US9094400B2 (en) | 2011-04-27 | 2015-07-28 | International Business Machines Corporation | Authentication in virtual private networks |
| US8839395B2 (en) | 2011-05-13 | 2014-09-16 | Cch Incorporated | Single sign-on between applications |
| US8443456B2 (en) | 2011-05-20 | 2013-05-14 | Citrix Systems, Inc. | Providing multiple layers of security to file storage by an external storage provider |
| US8687814B2 (en) | 2011-05-20 | 2014-04-01 | Citrix Systems, Inc. | Securing encrypted virtual hard disks |
| US20120311695A1 (en)* | 2011-05-31 | 2012-12-06 | Kohlenberg Tobias M | Method and apparatus for dynamic modification of authentication requirements of a processing system |
| HK1201093A1 (en) | 2011-06-01 | 2015-08-21 | 安全第一公司 | Systems and methods for secure distributed storage |
| US9201634B2 (en) | 2011-06-09 | 2015-12-01 | Samsung Electronics Co., Ltd | Method and system for controlling user experience with an application on a client device |
| US10333711B2 (en) | 2011-06-17 | 2019-06-25 | Microsoft Technology Licensing, Llc | Controlling access to protected objects |
| EP2727042B1 (en) | 2011-07-01 | 2016-04-06 | Fiberlink Communications Corporation | Rules based actions for mobile device management |
| US20130013727A1 (en) | 2011-07-05 | 2013-01-10 | Robin Edward Walker | System and method for providing a mobile persona environment |
| KR101844289B1 (en) | 2011-07-06 | 2018-04-02 | 삼성전자 주식회사 | Method and apparatus for managing security of mobile terminal based on location information in mobile communication system |
| US20130014267A1 (en) | 2011-07-07 | 2013-01-10 | Farrugia Augustin J | Computer protocol generation and obfuscation |
| US9369307B2 (en) | 2011-07-12 | 2016-06-14 | Bank Of America Corporation | Optimized service integration |
| US9015320B2 (en) | 2011-07-12 | 2015-04-21 | Bank Of America Corporation | Dynamic provisioning of service requests |
| US8719919B2 (en) | 2011-07-12 | 2014-05-06 | Bank Of America Corporation | Service mediation framework |
| US9424144B2 (en) | 2011-07-27 | 2016-08-23 | Microsoft Technology Licensing, Llc | Virtual machine migration to minimize packet loss in virtualized network |
| US9942385B2 (en) | 2011-08-04 | 2018-04-10 | International Business Machines Corporation | System and method for preventing and/or limiting use of a mobile device |
| US8949929B2 (en) | 2011-08-10 | 2015-02-03 | Qualcomm Incorporated | Method and apparatus for providing a secure virtual environment on a mobile device |
| WO2013020177A1 (en)* | 2011-08-11 | 2013-02-14 | Cocoon Data Holdings Limited | System and method for accessing securely stored data |
| DE112012003731T5 (en) | 2011-09-09 | 2014-08-07 | Stoneware Inc. | Method and apparatus for key sharing in conjunction with the Remote Desktop Protocol |
| US9652738B2 (en) | 2011-09-14 | 2017-05-16 | Avaya Inc. | System and method for a communication session identifier |
| US8825863B2 (en) | 2011-09-20 | 2014-09-02 | International Business Machines Corporation | Virtual machine placement within a server farm |
| US8554179B2 (en) | 2011-09-23 | 2013-10-08 | Blackberry Limited | Managing mobile device applications |
| US9451451B2 (en) | 2011-09-30 | 2016-09-20 | Tutela Technologies Ltd. | System for regulating wireless device operations in wireless networks |
| US9544158B2 (en) | 2011-10-05 | 2017-01-10 | Microsoft Technology Licensing, Llc | Workspace collaboration via a wall-type computing device |
| US8682973B2 (en) | 2011-10-05 | 2014-03-25 | Microsoft Corporation | Multi-user and multi-device collaboration |
| US9131147B2 (en) | 2011-10-07 | 2015-09-08 | Fuji Xerox Co., Ltd. | System and method for detecting and acting on multiple people crowding a small display for information sharing |
| US9280377B2 (en) | 2013-03-29 | 2016-03-08 | Citrix Systems, Inc. | Application with multiple operation modes |
| US8971842B2 (en) | 2011-10-12 | 2015-03-03 | Verizon Patent And Licensing Inc. | Enterprise mobile application store |
| US20130097660A1 (en) | 2011-10-17 | 2013-04-18 | Mcafee, Inc. | System and method for whitelisting applications in a mobile network environment |
| US20130097296A1 (en) | 2011-10-18 | 2013-04-18 | Telefonaktiebolaget L M Ericsson (Publ) | Secure cloud-based virtual machine migration |
| KR101834995B1 (en) | 2011-10-21 | 2018-03-07 | 삼성전자주식회사 | Method and apparatus for sharing contents between devices |
| US8347349B1 (en)* | 2011-10-28 | 2013-01-01 | Google Inc. | Configuring browser policy settings on client computing devices |
| US9106650B2 (en) | 2011-11-09 | 2015-08-11 | Microsoft Technology Licensing, Llc | User-driven access control |
| US8990558B2 (en) | 2011-11-09 | 2015-03-24 | Safer Point Ltd | Securing information in a cloud computing system |
| WO2013070126A1 (en) | 2011-11-10 | 2013-05-16 | Telefonaktiebolaget L M Ericsson (Publ) | Policy controlled preload and consumption of software application |
| US20130144934A1 (en) | 2011-12-01 | 2013-06-06 | Microsoft Corporation | Web Content Targeting Based on Client Application Availability |
| US8935375B2 (en) | 2011-12-12 | 2015-01-13 | Microsoft Corporation | Increasing availability of stateful applications |
| US20130305354A1 (en) | 2011-12-23 | 2013-11-14 | Microsoft Corporation | Restricted execution modes |
| US9507630B2 (en) | 2012-02-09 | 2016-11-29 | Cisco Technology, Inc. | Application context transfer for distributed computing resources |
| US8793344B2 (en) | 2012-02-17 | 2014-07-29 | Oracle International Corporation | System and method for generating a response plan for a hypothetical event |
| US8918881B2 (en) | 2012-02-24 | 2014-12-23 | Appthority, Inc. | Off-device anti-malware protection for mobile devices |
| US9323563B2 (en) | 2012-02-28 | 2016-04-26 | Red Hat Israel, Ltd. | Determining virtual machine migration in view of a migration rule |
| US9047107B2 (en) | 2012-02-29 | 2015-06-02 | Red Hat, Inc. | Applying a custom security type label to multi-tenant applications of a node in a platform-as-a-service environment |
| EP2661095A4 (en) | 2012-03-05 | 2015-07-22 | Mtek C & K Co Ltd | Method and apparatus for controlling automatic interworking of multiple devices |
| US20130237152A1 (en) | 2012-03-09 | 2013-09-12 | Kulveer Taggar | Methods and systems for hardware and software related to a near field communications task launcher |
| US20130260730A1 (en) | 2012-03-28 | 2013-10-03 | Enterproid Hk Ltd | Custom application container for mobile operating systems and/or devices |
| CN102662840A (en)* | 2012-03-31 | 2012-09-12 | 天津大学 | Automatic detecting system and method for extension behavior of Firefox browser |
| JP5697626B2 (en)* | 2012-04-03 | 2015-04-08 | 株式会社野村総合研究所 | Access authority management system |
| US20130268676A1 (en) | 2012-04-06 | 2013-10-10 | Telefonaktiebolaget L M Ericsson (Publ) | Application programming interface routing system and method of operating the same |
| US20130283335A1 (en) | 2012-04-19 | 2013-10-24 | AppSense, Inc. | Systems and methods for applying policy wrappers to computer applications |
| US9253209B2 (en) | 2012-04-26 | 2016-02-02 | International Business Machines Corporation | Policy-based dynamic information flow control on mobile devices |
| US9112918B2 (en) | 2012-04-30 | 2015-08-18 | Verizon Patent And Licensing Inc. | Multi-mode user device and network-based control and monitoring |
| CA2872051A1 (en) | 2012-05-01 | 2013-11-07 | Agora Mobile Inc. | System and method for providing an application development and distribution social platform |
| US8849904B2 (en) | 2012-05-17 | 2014-09-30 | Cloudflare, Inc. | Incorporating web applications into web pages at the network level |
| US20130347130A1 (en) | 2012-06-08 | 2013-12-26 | Bluebox | Methods and apparatus for dynamically providing modified versions of electronic device applications |
| US20140007215A1 (en) | 2012-06-15 | 2014-01-02 | Lockheed Martin Corporation | Mobile applications platform |
| US8713633B2 (en) | 2012-07-13 | 2014-04-29 | Sophos Limited | Security access protection for user data stored in a cloud computing facility |
| US20140047413A1 (en) | 2012-08-09 | 2014-02-13 | Modit, Inc. | Developing, Modifying, and Using Applications |
| US9032506B2 (en) | 2012-08-09 | 2015-05-12 | Cisco Technology, Inc. | Multiple application containerization in a single container |
| US8850434B1 (en) | 2012-09-14 | 2014-09-30 | Adaptive Computing Enterprises, Inc. | System and method of constraining auto live migration of virtual machines using group tags |
| US9507949B2 (en)* | 2012-09-28 | 2016-11-29 | Intel Corporation | Device and methods for management and access of distributed data sources |
| US20140109176A1 (en) | 2012-10-15 | 2014-04-17 | Citrix Systems, Inc. | Configuring and providing profiles that manage execution of mobile applications |
| EP2909715B1 (en) | 2012-10-16 | 2022-12-14 | Citrix Systems, Inc. | Application wrapping for application management framework |
| US9355253B2 (en) | 2012-10-18 | 2016-05-31 | Broadcom Corporation | Set top box architecture with application based security definitions |
| US8875304B2 (en) | 2012-11-08 | 2014-10-28 | International Business Machines Corporation | Application and data removal system |
| US20140149599A1 (en) | 2012-11-29 | 2014-05-29 | Ricoh Co., Ltd. | Unified Application Programming Interface for Communicating with Devices and Their Clouds |
| US9326145B2 (en) | 2012-12-16 | 2016-04-26 | Aruba Networks, Inc. | System and method for application usage controls through policy enforcement |
| US8910262B2 (en) | 2012-12-21 | 2014-12-09 | Cellco Partnership | Supporting multiple messaging services on mobile devices in a single user experience |
| US9535674B2 (en) | 2012-12-21 | 2017-01-03 | Bmc Software, Inc. | Application wrapping system and method |
| US9374369B2 (en) | 2012-12-28 | 2016-06-21 | Lookout, Inc. | Multi-factor authentication and comprehensive login system for client-server networks |
| US9094445B2 (en) | 2013-03-15 | 2015-07-28 | Centripetal Networks, Inc. | Protecting networks from cyber attacks and overloading |
| US9355223B2 (en) | 2013-03-29 | 2016-05-31 | Citrix Systems, Inc. | Providing a managed browser |
| US9455886B2 (en) | 2013-03-29 | 2016-09-27 | Citrix Systems, Inc. | Providing mobile device management functionalities |
| US9369449B2 (en) | 2013-03-29 | 2016-06-14 | Citrix Systems, Inc. | Providing an enterprise application store |
| US10284627B2 (en) | 2013-03-29 | 2019-05-07 | Citrix Systems, Inc. | Data management for an application with multiple operation modes |
| WO2014171938A1 (en) | 2013-04-17 | 2014-10-23 | Empire Technology Development, Llc | Datacenter border-issued analytics for monitoring federated services |
| TWI499932B (en) | 2013-07-17 | 2015-09-11 | Ind Tech Res Inst | Method for application management, corresponding system, and user device |
| US9356895B2 (en) | 2014-05-07 | 2016-05-31 | Mitake Information Corporation | Message transmission system and method for a structure of a plurality of organizations |
- 2013
- 2013-09-30USUS14/040,831patent/US9355223B2/enactiveActive
- 2013-10-01USUS14/043,012patent/US8893221B2/enactiveActive
- 2013-10-01USUS14/043,229patent/US9158895B2/enactiveActive
- 2013-10-01USUS14/043,343patent/US8850050B1/enactiveActive
- 2013-10-01USUS14/042,984patent/US8850010B1/enactiveActive
- 2013-10-01USUS14/043,301patent/US8996709B2/enactiveActive
- 2013-10-01USUS14/043,164patent/US8898732B2/enactiveActive
- 2013-10-01USUS14/042,941patent/US8881228B2/enactiveActive
- 2013-10-01USUS14/043,086patent/US9112853B2/enactiveActive
- 2013-10-10WOPCT/US2013/064319patent/WO2014158228A1/enactiveApplication Filing
- 2013-10-10EPEP13780489.4Apatent/EP2979218A1/ennot_activeWithdrawn
- 2013-10-10CNCN201380076889.5Apatent/CN105247531B/ennot_activeExpired - Fee Related
- 2013-10-10KRKR1020177010314Apatent/KR102038842B1/ennot_activeExpired - Fee Related
- 2013-10-10KRKR1020157031152Apatent/KR101728899B1/ennot_activeExpired - Fee Related
- 2013-10-10JPJP2016505457Apatent/JP6131381B2/ennot_activeExpired - Fee Related
- 2013-10-10EPEP18185793.9Apatent/EP3413227A1/ennot_activeWithdrawn
- 2016
- 2016-04-28USUS15/140,683patent/US10097584B2/enactiveActive
- 2017
- 2017-04-17JPJP2017081342Apatent/JP6397957B2/ennot_activeExpired - Fee Related
Patent Citations (294)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US7043453B2 (en) | 1994-11-23 | 2006-05-09 | Contentguard Holdings, Inc. | Method and system for conducting transactions between repositories using a repository transaction protocol |
| US5805803A (en) | 1997-05-13 | 1998-09-08 | Digital Equipment Corporation | Secure web tunnel |
| WO1999014652A1 (en) | 1997-09-16 | 1999-03-25 | Microsoft Corporation | Encrypting file system and method |
| US6151606A (en) | 1998-01-16 | 2000-11-21 | Visto Corporation | System and method for using a workspace data manager to access, manipulate and synchronize network data |
| US6154172A (en) | 1998-03-31 | 2000-11-28 | Piccionelli; Gregory A. | System and process for limiting distribution of information on a communication network based on geographic location |
| US20090178111A1 (en) | 1998-10-28 | 2009-07-09 | Bea Systems, Inc. | System and method for maintaining security in a distributed computer network |
| US6609198B1 (en) | 1999-08-05 | 2003-08-19 | Sun Microsystems, Inc. | Log-on service providing credential level change without loss of session continuity |
| US7596593B2 (en) | 1999-09-07 | 2009-09-29 | Citrix Systems, Llc | Methods and apparatus for efficiently transmitting interactive application data between a client and server using markup language |
| US7240015B1 (en) | 1999-09-17 | 2007-07-03 | Mitel Networks Corporation And The University Of Ottawa | Policy representations and mechanisms for the control of software |
| US8296239B2 (en) | 2000-03-10 | 2012-10-23 | Sony Corporation | Data distribution system and method of same, data processing apparatus and method of same, and data recording medium |
| US6859879B2 (en) | 2000-05-26 | 2005-02-22 | International Business Machine Corporation | Method and system for secure pervasive access |
| US20040010579A1 (en) | 2000-08-31 | 2004-01-15 | Esko Freese | Wireless device management |
| US20060161635A1 (en) | 2000-09-07 | 2006-07-20 | Sonic Solutions | Methods and system for use in network management of content |
| US6883098B1 (en) | 2000-09-20 | 2005-04-19 | International Business Machines Corporation | Method and computer system for controlling access by applications to this and other computer systems |
| US20020112047A1 (en) | 2000-12-05 | 2002-08-15 | Rakesh Kushwaha | System and method for wireless data terminal management using general packet radio service network |
| US20080214300A1 (en) | 2000-12-07 | 2008-09-04 | Igt | Methods for electronic data security and program authentication |
| US20040083273A1 (en) | 2001-01-18 | 2004-04-29 | Madison Justin Paul | Method and system for managing digital content, including streaming media |
| US20040230807A1 (en) | 2001-02-12 | 2004-11-18 | Baird Leemon C. | Apparatus and method for authenticating access to a network resource |
| US20030046366A1 (en) | 2001-02-13 | 2003-03-06 | Shishir Pardikar | System and method for providing transparent access to distributed authoring and versioning files including encrypted files |
| US20030037103A1 (en) | 2001-03-14 | 2003-02-20 | Nokia Corporation | Realization of presence management |
| WO2002084460A2 (en) | 2001-04-12 | 2002-10-24 | The Regents Of The University Of Michigan | Method and system to maintain portable computer data secure and authentication token for use therein |
| US20030031319A1 (en) | 2001-06-13 | 2003-02-13 | Miki Abe | Data transfer system, data transfer apparatus, data recording apparatus, edit controlling method and data processing method |
| US7340772B2 (en) | 2001-06-13 | 2008-03-04 | Citrix Systems, Inc. | Systems and methods for continuing an operation interrupted from a reconnection between a client and server |
| US6621766B2 (en) | 2001-08-01 | 2003-09-16 | Fossil, Inc. | Flexible timepiece in multiple environments |
| US20040205233A1 (en) | 2001-08-29 | 2004-10-14 | Dunk Craig A. | System and method for addressing a mobile device in an ip-based wireless network |
| US20110208838A1 (en) | 2001-11-02 | 2011-08-25 | Juniper Networks, Inc. | Method and system for providing secure access to private networks with client redirection |
| US7159120B2 (en) | 2001-11-19 | 2007-01-02 | Good Technology, Inc. | Method and system for protecting data within portable electronic devices |
| US7950066B1 (en) | 2001-12-21 | 2011-05-24 | Guardian Data Storage, Llc | Method and system for restricting use of a clipboard application |
| US20030131245A1 (en) | 2002-01-04 | 2003-07-10 | Michael Linderman | Communication security system |
| US20040111640A1 (en) | 2002-01-08 | 2004-06-10 | Baum Robert T. | IP based security applications using location, port and/or device identifier information |
| EP1465039A1 (en) | 2002-01-08 | 2004-10-06 | NTT DoCoMo, Inc. | Content delivery method and content delivery system |
| US20040006706A1 (en)* | 2002-06-06 | 2004-01-08 | Ulfar Erlingsson | Methods and systems for implementing a secure application execution environment using derived user accounts for internet content |
| US8012219B2 (en) | 2002-08-09 | 2011-09-06 | Visto Corporation | System and method for preventing access to data on a compromised remote device |
| US20060147043A1 (en) | 2002-09-23 | 2006-07-06 | Credant Technologies, Inc. | Server, computer memory, and method to support security policy maintenance and distribution |
| US20060242685A1 (en) | 2002-09-23 | 2006-10-26 | Credant Technologies, Inc. | System and method for distribution of security policies for mobile devices |
| US7254831B2 (en) | 2002-12-04 | 2007-08-07 | Microsoft Corporation | Sharing a sign-in among software applications having secured features |
| US8332464B2 (en) | 2002-12-13 | 2012-12-11 | Anxebusiness Corp. | System and method for remote network access |
| US20080134292A1 (en) | 2003-01-08 | 2008-06-05 | Ido Ariel | Extending user relationships |
| US20080052395A1 (en) | 2003-02-28 | 2008-02-28 | Michael Wright | Administration of protection of data accessible by a mobile device |
| US20060094400A1 (en) | 2003-02-28 | 2006-05-04 | Brent Beachem | System and method for filtering access points presented to a user and locking onto an access point |
| US20060120526A1 (en) | 2003-02-28 | 2006-06-08 | Peter Boucher | Access control to files based on source information |
| US7526800B2 (en) | 2003-02-28 | 2009-04-28 | Novell, Inc. | Administration of protection of data accessible by a mobile device |
| US20050055578A1 (en) | 2003-02-28 | 2005-03-10 | Michael Wright | Administration of protection of data accessible by a mobile device |
| WO2004107646A1 (en) | 2003-05-14 | 2004-12-09 | Threatguard, Inc. | System and method for application-level virtual private network |
| US20050097608A1 (en) | 2003-10-30 | 2005-05-05 | Xerox Corporation | Multimedia communications/collaboration hub |
| US7415498B2 (en) | 2003-12-10 | 2008-08-19 | International Business Machines Corporation | Time limited collaborative community role delegation policy |
| US20050172241A1 (en) | 2004-01-08 | 2005-08-04 | International Business Machines Corporation | System and method for improved direct system clipboard |
| US7269605B1 (en) | 2004-02-13 | 2007-09-11 | Avidian Technologies | Personal information manager data synchronization and augmentation |
| GB2411320A (en) | 2004-02-23 | 2005-08-24 | Nec Corp | Access control management in a terminal device |
| US8560709B1 (en) | 2004-02-25 | 2013-10-15 | F5 Networks, Inc. | System and method for dynamic policy based access over a virtual private network |
| US7599991B2 (en) | 2004-03-10 | 2009-10-06 | Microsoft Corporation | Rules interface for implementing message rules on a mobile computing device |
| US20050255838A1 (en) | 2004-04-30 | 2005-11-17 | Adams Neil P | System and method for handling data transfers |
| US20050273592A1 (en) | 2004-05-20 | 2005-12-08 | International Business Machines Corporation | System, method and program for protecting communication |
| US7966323B2 (en) | 2004-09-13 | 2011-06-21 | Research In Motion Limited | Enabling category-based filtering |
| US20080066020A1 (en) | 2004-09-16 | 2008-03-13 | Boss Gregory J | System and Method to Capture and Manage Input Values for Automatic Form Fill |
| US8463946B2 (en) | 2004-09-17 | 2013-06-11 | Caterpillar Inc. | Method for automatic radio operational mode selection |
| US20060117104A1 (en) | 2004-09-17 | 2006-06-01 | Fujitsu Limited | Setting information distribution apparatus, method, program, and medium, authentication setting transfer apparatus, method, program, and medium, and setting information reception program |
| US20060075123A1 (en) | 2004-09-27 | 2006-04-06 | Citrix Systems, Inc. | System and method for managing virtual ip addresses |
| US20060085826A1 (en) | 2004-10-18 | 2006-04-20 | Funk James M | Aggregated program guide for download and view video on demand service |
| US20090228714A1 (en) | 2004-11-18 | 2009-09-10 | Biogy, Inc. | Secure mobile device with online vault |
| US7496954B1 (en) | 2004-11-22 | 2009-02-24 | Sprint Communications Company L.P. | Single sign-on system and method |
| US20120290694A9 (en) | 2004-12-07 | 2012-11-15 | Brett Marl | Network administration tool |
| US7490073B1 (en) | 2004-12-21 | 2009-02-10 | Zenprise, Inc. | Systems and methods for encoding knowledge for automated management of software application deployments |
| US7788536B1 (en) | 2004-12-21 | 2010-08-31 | Zenprise, Inc. | Automated detection of problems in software application deployments |
| US7865888B1 (en) | 2004-12-21 | 2011-01-04 | Zenprise, Inc. | Systems and methods for gathering deployment state for automated management of software application deployments |
| US20060141985A1 (en) | 2004-12-23 | 2006-06-29 | Motorola, Inc. | Dynamic management for interface access permissions |
| US7788535B2 (en) | 2005-01-28 | 2010-08-31 | Nxp B.V. | Means and method for debugging |
| US20060224742A1 (en) | 2005-02-28 | 2006-10-05 | Trust Digital | Mobile data security system and methods |
| US8214887B2 (en) | 2005-03-20 | 2012-07-03 | Actividentity (Australia) Pty Ltd. | Method and system for providing user access to a secure application |
| US7697737B2 (en) | 2005-03-25 | 2010-04-13 | Northrop Grumman Systems Corporation | Method and system for providing fingerprint enabled wireless add-on for personal identification number (PIN) accessible smartcards |
| US20060225142A1 (en) | 2005-04-05 | 2006-10-05 | Cisco Technology, Inc. (A California Corporation) | Method and electronic device for triggering zeroization in a electronic device |
| US20070056043A1 (en) | 2005-05-19 | 2007-03-08 | Richard Onyon | Remote cell phone auto destruct |
| US7970386B2 (en) | 2005-06-03 | 2011-06-28 | Good Technology, Inc. | System and method for monitoring and maintaining a wireless device |
| US20070038764A1 (en) | 2005-06-07 | 2007-02-15 | Alcatel | Network equipment for supplying multimode mobile terminals with data necessary for automatically selecting radio access network interfaces during service sessions |
| US20100124196A1 (en) | 2005-06-29 | 2010-05-20 | Jumpstart Wireless Corporation | System and method for dynamic automatic communication path selection, distributed device synchronization and task delegation |
| US7529923B2 (en) | 2005-06-30 | 2009-05-05 | Intel Corporation | Operating system mode transfer |
| US20070005713A1 (en) | 2005-07-01 | 2007-01-04 | Levasseur Thierry | Secure electronic mail system |
| US20070011749A1 (en) | 2005-07-11 | 2007-01-11 | Simdesk Technologies | Secure clipboard function |
| US20120109384A1 (en) | 2005-08-19 | 2012-05-03 | Nexstep, Inc. | Consumer electronic registration, control and support concierge device and method |
| US20070049297A1 (en) | 2005-08-29 | 2007-03-01 | Janakiraman Gopalan | System and method for locating mobile devices through a direct-connection protocol |
| US20070074033A1 (en) | 2005-09-29 | 2007-03-29 | Research In Motion Limited | Account management in a system and method for providing code signing services |
| US8037421B2 (en) | 2005-10-11 | 2011-10-11 | Research In Motion Limited | System and method for organizing application indicators on an electronic device |
| US20070109983A1 (en) | 2005-11-11 | 2007-05-17 | Computer Associates Think, Inc. | Method and System for Managing Access to a Wireless Network |
| US20070156897A1 (en) | 2005-12-29 | 2007-07-05 | Blue Jungle | Enforcing Control Policies in an Information Management System |
| US20090221278A1 (en) | 2005-12-30 | 2009-09-03 | Telecom Italia S.P.A. | Method for Customizing the Operation of a Telephonic Terminal |
| US20070204153A1 (en) | 2006-01-04 | 2007-08-30 | Tome Agustin J | Trusted host platform |
| US20070204166A1 (en) | 2006-01-04 | 2007-08-30 | Tome Agustin J | Trusted host platform |
| US20070180447A1 (en) | 2006-01-24 | 2007-08-02 | Citrix Systems, Inc. | Methods and systems for interacting, via a hypermedium page, with a virtual machine |
| US20070198656A1 (en) | 2006-01-24 | 2007-08-23 | Citrix Systems, Inc. | Methods and servers for establishing a connection between a client system and a virtual machine executing in a terminal services session and hosting a requested computing environment |
| US8051180B2 (en) | 2006-01-24 | 2011-11-01 | Citrix Systems, Inc. | Methods and servers for establishing a connection between a client system and a virtual machine executing in a terminal services session and hosting a requested computing environment |
| US20070186106A1 (en) | 2006-01-26 | 2007-08-09 | Ting David M | Systems and methods for multi-factor authentication |
| US20070199051A1 (en) | 2006-02-15 | 2007-08-23 | Microsoft Corporation | Securely hosting a webbrowser control in a managed code environment |
| US20070214272A1 (en) | 2006-03-07 | 2007-09-13 | Novell, Inc. | Light-weight multi-user browser |
| US20070226773A1 (en) | 2006-03-21 | 2007-09-27 | Novell, Inc. | System and method for using sandboxes in a managed shell |
| US20070226225A1 (en) | 2006-03-22 | 2007-09-27 | Yiu Timothy C | Mobile collaboration and communication system |
| WO2007113709A1 (en) | 2006-03-30 | 2007-10-11 | Koninklijke Philips Electronics N.V. | Method and apparatus for assigning an application to a security restriction |
| US20110179484A1 (en) | 2006-04-06 | 2011-07-21 | Juniper Networks, Inc. | Malware detection system and method for mobile platforms |
| US20080235760A1 (en) | 2006-05-02 | 2008-09-25 | International Business Machines Corporation | Confidential Content Reporting System and Method with Electronic Mail Verification Functionality |
| US8085891B2 (en) | 2006-05-29 | 2011-12-27 | Research In Motion Limited | System and method for management of mobile device communication |
| US20080027982A1 (en) | 2006-07-27 | 2008-01-31 | Ebay Inc. | Indefinite caching expiration techniques |
| US20080127292A1 (en) | 2006-08-04 | 2008-05-29 | Apple Computer, Inc. | Restriction of program process capabilities |
| US20080047015A1 (en) | 2006-08-08 | 2008-02-21 | Andrew Cornwall | Method to provide a secure virtual machine launcher |
| US20080209506A1 (en) | 2006-08-14 | 2008-08-28 | Quantum Secure, Inc. | Physical access control and security monitoring system utilizing a normalized data format |
| US20080133729A1 (en) | 2006-08-17 | 2008-06-05 | Neustar, Inc. | System and method for managing domain policy for interconnected communication networks |
| US20080070495A1 (en) | 2006-08-18 | 2008-03-20 | Michael Stricklen | Mobile device management |
| US20080066177A1 (en) | 2006-09-08 | 2008-03-13 | International Business Machines Corporation | Methods, systems, and computer program products for implementing inter-process integrity serialization |
| US20120079475A1 (en) | 2006-11-01 | 2012-03-29 | Hicks Iii John Alson | Life Cycle Management of User-Selected Applications on Wireless Communications Devices |
| US8126128B1 (en) | 2006-11-01 | 2012-02-28 | At&T Intellectual Property I, Lp | Life cycle management of user-selected applications on wireless communications devices |
| US8095786B1 (en) | 2006-11-09 | 2012-01-10 | Juniper Networks, Inc. | Application-specific network-layer virtual private network connections |
| US8365258B2 (en) | 2006-11-16 | 2013-01-29 | Phonefactor, Inc. | Multi factor authentication |
| US20080141335A1 (en) | 2006-12-08 | 2008-06-12 | Novell, Inc. | Provisioning software with policy-appropriate capabilities |
| US20110225417A1 (en) | 2006-12-13 | 2011-09-15 | Kavi Maharajh | Digital rights management in a mobile environment |
| US20080163286A1 (en) | 2006-12-29 | 2008-07-03 | Echostar Technologies Corporation | Controlling access to content and/or services |
| WO2008086611A1 (en) | 2007-01-19 | 2008-07-24 | Research In Motion Limited | Selectively wiping a remote device |
| US20120117622A1 (en) | 2007-02-05 | 2012-05-10 | Kaj Gronholm | Dynamic network access control method and apparatus |
| US20100325097A1 (en) | 2007-02-07 | 2010-12-23 | International Business Machines Corporation | Non-Invasive Usage Tracking, Access Control, Policy Enforcement, Audit Logging, and User Action Automation On Software Applications |
| US20080196038A1 (en) | 2007-02-08 | 2008-08-14 | Microsoft Corporation | Utilizing a first managed process to host at least a second managed process |
| US7761523B2 (en) | 2007-02-09 | 2010-07-20 | Research In Motion Limited | Schedulable e-mail filters |
| US8126506B2 (en) | 2007-02-14 | 2012-02-28 | Nuance Communications, Inc. | System and method for securely managing data stored on mobile devices, such as enterprise mobility data |
| US20080313648A1 (en) | 2007-06-14 | 2008-12-18 | Microsoft Corporation | Protection and communication abstractions for web browsers |
| US20080318616A1 (en) | 2007-06-21 | 2008-12-25 | Verizon Business Network Services, Inc. | Flexible lifestyle portable communications device |
| US20090006232A1 (en) | 2007-06-29 | 2009-01-01 | Gallagher Ken A | Secure computer and internet transaction software and hardware and uses thereof |
| US20090030968A1 (en) | 2007-07-27 | 2009-01-29 | Jesse Boudreau | Remote control in a wireless communication system |
| US20090028049A1 (en) | 2007-07-27 | 2009-01-29 | Jesse Boudreau | Administration of policies for wireless devices in a wireless communication system |
| US8060074B2 (en) | 2007-07-30 | 2011-11-15 | Mobile Iron, Inc. | Virtual instance architecture for mobile device management systems |
| US20090077638A1 (en) | 2007-09-17 | 2009-03-19 | Novell, Inc. | Setting and synching preferred credentials in a disparate credential store environment |
| US8001278B2 (en) | 2007-09-28 | 2011-08-16 | Intel Corporation | Network packet payload compression |
| US20100229197A1 (en) | 2007-10-31 | 2010-09-09 | Pxd, Inc. | Digital broadcast widget system |
| US20090119773A1 (en) | 2007-11-02 | 2009-05-07 | D Amore Tianyu Li | Apparatus and methods of configurable system event and resource arbitration management |
| US20090228963A1 (en) | 2007-11-26 | 2009-09-10 | Nortel Networks Limited | Context-based network security |
| US8601562B2 (en) | 2007-12-10 | 2013-12-03 | Courion Corporation | Policy enforcement using ESSO |
| US20090172789A1 (en) | 2007-12-27 | 2009-07-02 | Hewlett-Packard Development Company, L.P. | Policy Based, Delegated Limited Network Access Management |
| US20090170532A1 (en) | 2007-12-28 | 2009-07-02 | Apple Inc. | Event-based modes for electronic devices |
| US20090199277A1 (en) | 2008-01-31 | 2009-08-06 | Norman James M | Credential arrangement in single-sign-on environment |
| US7904468B2 (en) | 2008-02-27 | 2011-03-08 | Research In Motion Limited | Method and software for facilitating interaction with a personal information manager application at a wireless communication device |
| US20090222880A1 (en) | 2008-03-03 | 2009-09-03 | Tresys Technology, Llc | Configurable access control security for virtualization |
| US20090228954A1 (en) | 2008-03-07 | 2009-09-10 | At&T Mobility Ii Llc | System and method for policy-enabled mobile service gateway |
| US20130254660A1 (en) | 2008-03-13 | 2013-09-26 | Robb Fujioka | Tablet computer |
| US20090249359A1 (en) | 2008-03-25 | 2009-10-01 | Caunter Mark Leslie | Apparatus and methods for widget intercommunication in a wireless communication environment |
| US8418238B2 (en) | 2008-03-30 | 2013-04-09 | Symplified, Inc. | System, method, and apparatus for managing access to resources across a network |
| US7966652B2 (en) | 2008-04-07 | 2011-06-21 | Safemashups Inc. | Mashauth: using mashssl for efficient delegated authentication |
| US20120084184A1 (en) | 2008-06-05 | 2012-04-05 | Raleigh Gregory G | Enterprise Access Control and Accounting Allocation for Access Networks |
| US20120185913A1 (en) | 2008-06-19 | 2012-07-19 | Servicemesh, Inc. | System and method for a cloud computing abstraction layer with security zone facilities |
| US20090325615A1 (en) | 2008-06-29 | 2009-12-31 | Oceans' Edge, Inc. | Mobile Telephone Firewall and Compliance Enforcement System and Method |
| GB2462442A (en) | 2008-08-06 | 2010-02-10 | Zybert Computing Ltd | A remote server centrally controls access to data stored in a data container in an encrypted form |
| US8238256B2 (en) | 2008-09-08 | 2012-08-07 | Nugent Raymond M | System and method for cloud computing |
| US20100077469A1 (en) | 2008-09-19 | 2010-03-25 | Michael Furman | Single Sign On Infrastructure |
| US8528059B1 (en) | 2008-10-06 | 2013-09-03 | Goldman, Sachs & Co. | Apparatuses, methods and systems for a secure resource access and placement platform |
| US20100100925A1 (en) | 2008-10-16 | 2010-04-22 | International Business Machines Corporation | Digital Rights Management (DRM)-Enabled Policy Management For An Identity Provider In A Federated Environment |
| US20100100825A1 (en) | 2008-10-16 | 2010-04-22 | Accenture Global Services Gmbh | Method, system and graphical user interface for enabling a user to access enterprise data on a portable electronic device |
| US20100146523A1 (en) | 2008-12-05 | 2010-06-10 | Tripod Ventures Inc./ Entreprises Tripod Inc. | Browser environment application and local file server application system |
| US20100154025A1 (en) | 2008-12-12 | 2010-06-17 | Microsoft Corporation | Integrating policies from a plurality of disparate management agents |
| US20100150341A1 (en) | 2008-12-17 | 2010-06-17 | David Dodgson | Storage security using cryptographic splitting |
| US8272030B1 (en) | 2009-01-21 | 2012-09-18 | Sprint Communications Company L.P. | Dynamic security management for mobile communications device |
| US20130227659A1 (en) | 2009-01-28 | 2013-08-29 | Headwater Partners I Llc | Automated device provisioning and activation |
| US20100192212A1 (en) | 2009-01-28 | 2010-07-29 | Gregory G. Raleigh | Automated device provisioning and activation |
| US20120005724A1 (en) | 2009-02-09 | 2012-01-05 | Imera Systems, Inc. | Method and system for protecting private enterprise resources in a cloud computing environment |
| US20140059640A9 (en) | 2009-03-02 | 2014-02-27 | Gregory G. Raleigh | Adapting Network Policies Based on Device Service Processor Configuration |
| US20100248699A1 (en) | 2009-03-31 | 2010-09-30 | Dumais Paul Mark Joseph | Remote application storage |
| WO2010115289A1 (en) | 2009-04-09 | 2010-10-14 | Aegis Mobility, Inc. | Context based data mediation |
| US20100287619A1 (en) | 2009-05-05 | 2010-11-11 | Absolute Software Corporation | Discriminating data protection system |
| US20100299376A1 (en) | 2009-05-20 | 2010-11-25 | Mobile Iron, Inc. | Selective Management of Mobile Devices in an Enterprise Environment |
| US20100299152A1 (en) | 2009-05-20 | 2010-11-25 | Mobile Iron, Inc. | Selective Management of Mobile Devices in an Enterprise Environment |
| US20100319053A1 (en) | 2009-06-12 | 2010-12-16 | Apple Inc. | Devices with profile-based operating mode controls |
| US20100317336A1 (en) | 2009-06-16 | 2010-12-16 | Bran Ferren | Context-based limitation of mobile device operation |
| US20130024424A1 (en) | 2009-06-30 | 2013-01-24 | Commvault Systems, Inc. | Data object store and server for a cloud storage environment, including data deduplication and data management across multiple cloud storage sites |
| US20130084847A1 (en) | 2009-07-21 | 2013-04-04 | Scott Ferrill Tibbitts | Method and system for controlling a mobile communication device |
| US20130013653A1 (en) | 2009-08-05 | 2013-01-10 | International Business Machines Corporation | Tracking file contents |
| US20120214472A1 (en) | 2009-10-31 | 2012-08-23 | Saied Tadayon | Method and System for Controlling Mobile Device Functions via a Service or Background Process |
| US20110145833A1 (en) | 2009-12-15 | 2011-06-16 | At&T Mobility Ii Llc | Multiple Mode Mobile Device |
| US20110154477A1 (en) | 2009-12-22 | 2011-06-23 | Cisco Technology, Inc. | Dynamic content-based routing |
| US20110209064A1 (en) | 2010-02-24 | 2011-08-25 | Novell, Inc. | System and method for providing virtual desktop extensions on a client desktop |
| US8468455B2 (en) | 2010-02-24 | 2013-06-18 | Novell, Inc. | System and method for providing virtual desktop extensions on a client desktop |
| US20110219124A1 (en)* | 2010-03-05 | 2011-09-08 | Brass Monkey, Inc. | System and method for two way communication and controlling content in a web browser |
| US20110239125A1 (en) | 2010-03-24 | 2011-09-29 | Kristensen Kristian H | Using multiple display servers to protect data |
| US20110252232A1 (en) | 2010-04-07 | 2011-10-13 | Apple Inc. | System and method for wiping encrypted data on a device having file-level content protection |
| US20110258301A1 (en) | 2010-04-15 | 2011-10-20 | Research In Motion Limited | Method and system for transmitting an application to a device |
| US20110271279A1 (en) | 2010-04-29 | 2011-11-03 | High Cloud Security, Inc. | Secure Virtual Machine |
| US20130117240A1 (en) | 2010-05-03 | 2013-05-09 | Panzura, Inc. | Accessing cached data from a peer cloud controller in a distributed filesystem |
| US20110276683A1 (en) | 2010-05-06 | 2011-11-10 | Trust Digital, Llc | Distributed data revocation using data commands |
| US20110276699A1 (en) | 2010-05-09 | 2011-11-10 | Pedersen Bradley J | Systems and methods for allocation of classes of service to network connections corresponding to virtual channels |
| US8468090B2 (en) | 2010-05-21 | 2013-06-18 | Hsbc Technologies Inc. | Account opening computer system architecture and process for implementing same |
| US20110295970A1 (en) | 2010-05-27 | 2011-12-01 | Canon Kabushiki Kaisha | Cloud computing system, server computer, device connection method, and storage medium |
| US20120005745A1 (en) | 2010-06-30 | 2012-01-05 | Juniper Networks, Inc. | Vpn network client for mobile device having dynamically translated user home page |
| US20120005746A1 (en) | 2010-06-30 | 2012-01-05 | Juniper Networks, Inc. | Dual-mode multi-service vpn network client for mobile device |
| US20120005476A1 (en) | 2010-06-30 | 2012-01-05 | Juniper Networks, Inc. | Multi-service vpn network client for mobile device having integrated acceleration |
| US20120023506A1 (en) | 2010-07-20 | 2012-01-26 | Apple Inc. | Maintaining Data States Upon Forced Exit |
| US20120036370A1 (en) | 2010-07-28 | 2012-02-09 | Nextlabs, Inc. | Protecting Documents Using Policies and Encryption |
| US20120036347A1 (en) | 2010-08-06 | 2012-02-09 | Swanson Robert C | Providing fast non-volatile storage in a secure environment |
| US20140040656A1 (en) | 2010-08-26 | 2014-02-06 | Adobe Systems Incorporated | System and method for managing cloud deployment configuration of an application |
| US20120052954A1 (en) | 2010-08-31 | 2012-03-01 | Sony Computer Entertainment Inc. | Offline Progress of Console Game via Portable Device |
| EP2428894A1 (en) | 2010-09-14 | 2012-03-14 | AppSense Limited | Private application clipboard |
| US20120066691A1 (en) | 2010-09-14 | 2012-03-15 | Paul Keith Branton | Private application clipboard |
| US20120088540A1 (en) | 2010-10-07 | 2012-04-12 | Research In Motion Limited | Provisioning Based on Application and Device Capability |
| US20120303476A1 (en) | 2010-11-09 | 2012-11-29 | Openpeak Inc. | Communication devices, networks, services and accompanying methods |
| US20120131116A1 (en) | 2010-11-15 | 2012-05-24 | Van Quy Tu | Controlling data transfer on mobile devices |
| US20120131685A1 (en) | 2010-11-19 | 2012-05-24 | MobileIron, Inc. | Mobile Posture-based Policy, Remediation and Access Control for Enterprise Resources |
| US20130132941A1 (en) | 2010-11-19 | 2013-05-23 | Mobile Iron, Inc. | Management of mobile applications |
| US20120129503A1 (en) | 2010-11-19 | 2012-05-24 | MobileIron, Inc. | Management of Mobile Applications |
| US8359016B2 (en) | 2010-11-19 | 2013-01-22 | Mobile Iron, Inc. | Management of mobile applications |
| US8650620B2 (en) | 2010-12-20 | 2014-02-11 | At&T Intellectual Property I, L.P. | Methods and apparatus to control privileges of mobile device applications |
| US20120154413A1 (en) | 2010-12-21 | 2012-06-21 | Dongwoo Kim | Mobile terminal and method of controlling a mode switching therein |
| US20120159139A1 (en) | 2010-12-21 | 2012-06-21 | Dongwoo Kim | Mobile terminal and method of controlling a mode switching therein |
| US20120157165A1 (en) | 2010-12-21 | 2012-06-21 | Dongwoo Kim | Mobile terminal and method of controlling a mode switching therein |
| US20120157166A1 (en) | 2010-12-21 | 2012-06-21 | Dongwoo Kim | Mobile terminal and method of managing information therein |
| US20120166997A1 (en) | 2010-12-22 | 2012-06-28 | Hyunah Cho | Mobile terminal and method of sharing information therein |
| US20120165075A1 (en) | 2010-12-22 | 2012-06-28 | Lg Electronics Inc. | Mobile terminal and method of displaying information therein |
| US20120166524A1 (en) | 2010-12-27 | 2012-06-28 | Takeshi Watakabe | Information Processing Apparatus and Removable Media Management Method |
| US20120167118A1 (en) | 2010-12-27 | 2012-06-28 | Microsoft Corporation | Power management via coordination and selective operation of timer-related tasks |
| US20120179909A1 (en) | 2011-01-06 | 2012-07-12 | Pitney Bowes Inc. | Systems and methods for providing individual electronic document secure storage, retrieval and use |
| US20120179802A1 (en) | 2011-01-10 | 2012-07-12 | Fiberlink Communications Corporation | System and method for extending cloud services into the customer premise |
| US20120185910A1 (en) | 2011-01-14 | 2012-07-19 | Nokia Corporation | Method and apparatus for adjusting context-based factors for selecting a security policy |
| US20120198570A1 (en) | 2011-02-01 | 2012-08-02 | Bank Of America Corporation | Geo-Enabled Access Control |
| US20120204220A1 (en) | 2011-02-07 | 2012-08-09 | Tufin Software Technologies Ltd. | Method of analyzing security ruleset and system thereof |
| US20130151598A1 (en) | 2011-02-09 | 2013-06-13 | Cliqr Technologies Inc. | Apparatus, systems and methods for deployment of interactive desktop applications on distributed infrastructures |
| US20120222120A1 (en) | 2011-02-24 | 2012-08-30 | Samsung Electronics Co. Ltd. | Malware detection method and mobile terminal realizing the same |
| US20130066960A1 (en) | 2011-02-28 | 2013-03-14 | Siemens Enterprise Communications Gmbh & Co. Kg | Apparatus and Mechanism for Dynamic Assignment of Survivability Services to Mobile Devices |
| US20120238257A1 (en) | 2011-03-16 | 2012-09-20 | Anson Douglas M | System and method for selectively restricting portable information handling system features |
| US20120240183A1 (en) | 2011-03-18 | 2012-09-20 | Amit Sinha | Cloud based mobile device security and policy enforcement |
| US20120304310A1 (en) | 2011-03-21 | 2012-11-29 | Mocana Corporation | Secure execution of unsecured apps on a device |
| US20120254768A1 (en) | 2011-03-31 | 2012-10-04 | Google Inc. | Customizing mobile applications |
| US20130097421A1 (en) | 2011-04-04 | 2013-04-18 | Nextlabs, Inc. | Protecting Information Using Policies and Encryption |
| US20120272221A1 (en) | 2011-04-22 | 2012-10-25 | Microsoft Corporation | Rule based data driven validation |
| US20120278454A1 (en) | 2011-04-26 | 2012-11-01 | Stewart Brett B | Gateway Device Application Development System |
| US20120303778A1 (en) | 2011-04-28 | 2012-11-29 | Approxy Inc. Ltd. | Application Distribution Network |
| US20120284325A1 (en) | 2011-05-02 | 2012-11-08 | Mitel Networks Corporation | Regulating use of a mobile computing device for a user at a selected location |
| US20120284779A1 (en) | 2011-05-04 | 2012-11-08 | Apple Inc. | Electronic devices having adaptive security profiles and methods for selecting the same |
| US20120311154A1 (en) | 2011-05-31 | 2012-12-06 | Morgan Christopher Edwin | Systems and methods for triggering workload movement based on policy stack having multiple selectable inputs |
| US20120311659A1 (en) | 2011-06-01 | 2012-12-06 | Mobileasap, Inc. | Real-time mobile application management |
| US8578443B2 (en) | 2011-06-01 | 2013-11-05 | Mobileasap, Inc. | Real-time mobile application management |
| US20120324568A1 (en) | 2011-06-14 | 2012-12-20 | Lookout, Inc., A California Corporation | Mobile web protection |
| US20120331527A1 (en) | 2011-06-22 | 2012-12-27 | TerraWi, Inc. | Multi-layer, geolocation-based network resource access and permissions |
| US20120331528A1 (en) | 2011-06-27 | 2012-12-27 | Osmosix, Inc. | Apparatus, systems and methods for secure and selective access to services in hybrid public-private infrastructures |
| US20130002725A1 (en) | 2011-06-28 | 2013-01-03 | Dongwoo Kim | Mobile terminal and display controlling method therein |
| US20130007842A1 (en) | 2011-06-28 | 2013-01-03 | Hyekyung Park | Mobile terminal and display controlling method therein |
| US20130013688A1 (en) | 2011-07-07 | 2013-01-10 | Cisco Technology, Inc. | System and method for providing a message and an event based video services control plane |
| US20130014239A1 (en) | 2011-07-08 | 2013-01-10 | International Business Machines Corporation | Authenticating a rich client from within an existing browser session |
| US20130024928A1 (en) | 2011-07-22 | 2013-01-24 | Robert James Burke | Secure network communications for meters |
| US20130145448A1 (en) | 2011-08-05 | 2013-06-06 | Vmware, Inc. | Lock screens to access work environments on a personal mobile device |
| US20130042294A1 (en) | 2011-08-08 | 2013-02-14 | Microsoft Corporation | Identifying application reputation based on resource accesses |
| US20130054922A1 (en) | 2011-08-23 | 2013-02-28 | Vmware, Inc. | Cooperative memory resource management for virtualized computing devices |
| US20130055378A1 (en) | 2011-08-29 | 2013-02-28 | Pantech Co., Ltd. | Method and portable device for controlling permission settings for application |
| US20130054962A1 (en) | 2011-08-31 | 2013-02-28 | Deepak Chawla | Policy configuration for mobile device applications |
| US20130059284A1 (en) | 2011-09-07 | 2013-03-07 | Teegee, Llc | Interactive electronic toy and learning device system |
| US20130138810A1 (en) | 2011-09-09 | 2013-05-30 | Shuki Binyamin | Systems and Methods for Workspace Interaction with Cloud-Based Applications |
| US20130074142A1 (en) | 2011-09-15 | 2013-03-21 | Microsoft Corporation | Securing data usage in computing devices |
| US20130086684A1 (en) | 2011-09-30 | 2013-04-04 | David S. Mohler | Contextual virtual machines for application quarantine and assessment method and system |
| US8402011B1 (en) | 2011-10-10 | 2013-03-19 | Google Inc. | System and method for managing user web browsing information |
| US20130091543A1 (en) | 2011-10-10 | 2013-04-11 | Openpeak Inc. | System and method for creating secure applications |
| US20140032691A1 (en) | 2011-10-11 | 2014-01-30 | Citrix Systems, Inc. | Policy-Based Application Management |
| US20140040977A1 (en) | 2011-10-11 | 2014-02-06 | Citrix Systems, Inc. | Policy-Based Application Management |
| US20140033271A1 (en) | 2011-10-11 | 2014-01-30 | Citrix Systems, Inc. | Policy-Based Application Management |
| US20140032733A1 (en) | 2011-10-11 | 2014-01-30 | Citrix Systems, Inc. | Policy-Based Application Management |
| US20140032758A1 (en) | 2011-10-11 | 2014-01-30 | Citrix Systems, Inc. | Policy-Based Application Management |
| US20140040638A1 (en) | 2011-10-11 | 2014-02-06 | Citrix Systems, Inc. | Policy-Based Application Management |
| US20140032759A1 (en) | 2011-10-11 | 2014-01-30 | Citrix Systems, Inc. | Policy-Based Application Management |
| US20140006347A1 (en) | 2011-10-11 | 2014-01-02 | Zenprise, Inc. | Secure container for protecting enterprise data on a mobile device |
| US20140040979A1 (en) | 2011-10-11 | 2014-02-06 | Citrix Systems, Inc. | Policy-Based Application Management |
| US20140007183A1 (en) | 2011-10-11 | 2014-01-02 | Zenprise, Inc. | Controlling mobile device access to enterprise resources |
| US20140040978A1 (en) | 2011-10-11 | 2014-02-06 | Citrix Systems, Inc. | Policy-Based Application Management |
| US8239918B1 (en) | 2011-10-11 | 2012-08-07 | Google Inc. | Application marketplace administrative controls |
| US20130111540A1 (en) | 2011-10-28 | 2013-05-02 | Jason Allen Sabin | Cloud protection techniques |
| US20130117805A1 (en) | 2011-11-09 | 2013-05-09 | Microsoft Corporation | Techniques to apply and share remote policies on mobile devices |
| US20130132457A1 (en) | 2011-11-18 | 2013-05-23 | Computer Associates Think, Inc. | System and method for hand-offs in cloud environments |
| US20130130651A1 (en) | 2011-11-22 | 2013-05-23 | Vmware, Inc. | Provisioning work environments on personal mobile devices |
| US20130130652A1 (en) | 2011-11-22 | 2013-05-23 | Vmware, Inc. | Controlling use of a business environment on a mobile device |
| US20130133061A1 (en) | 2011-11-22 | 2013-05-23 | Vmware, Inc. | Method and system for vpn isolation using network namespaces |
| US20130139241A1 (en) | 2011-11-29 | 2013-05-30 | Michael Leeder | Methods, systems, and computer readable media for bridging user authentication, authorization, and access between web-based and telecom domains |
| US20130138766A1 (en) | 2011-11-29 | 2013-05-30 | Dell Products L.P. | Mode sensitive networking |
| US20130142043A1 (en) | 2011-12-06 | 2013-06-06 | T-Mobile Usa, Inc. | Quality of service application controller and user equipment application profiler |
| US20130171967A1 (en) | 2012-01-04 | 2013-07-04 | Ayman S. Ashour | Providing Secure Execution of Mobile Device Workflows |
| US20130297662A1 (en) | 2012-01-06 | 2013-11-07 | Rahul Sharma | Secure Virtual File Management System |
| US20130219176A1 (en) | 2012-01-06 | 2013-08-22 | Venkata Sastry Akella | Secure Virtual File Management System |
| US20130219456A1 (en) | 2012-01-06 | 2013-08-22 | Rahul Sharma | Secure Virtual File Management System |
| US20130219211A1 (en) | 2012-02-17 | 2013-08-22 | International Business Machines Corporation | Elastic Cloud-Driven Task Execution |
| US20130232541A1 (en) | 2012-03-02 | 2013-09-05 | International Business Machines Corporation | Policy-driven approach to managing privileged/shared identity in an enterprise |
| US20130254831A1 (en) | 2012-03-23 | 2013-09-26 | Lockheed Martin Corporation | Method and apparatus for context aware mobile security |
| US20130254262A1 (en) | 2012-03-26 | 2013-09-26 | Quickmobile Inc. | System and method for a user to dynamically update a mobile application from a generic or first application within a class of applications to create a specific or second application with said class of applications |
| US20130263209A1 (en) | 2012-03-30 | 2013-10-03 | Cognizant Business Services Limited | Apparatus and methods for managing applications in multi-cloud environments |
| US20130263208A1 (en) | 2012-04-02 | 2013-10-03 | Narsimha Reddy Challa | Managing virtual machines in a cloud computing system |
| US20130291052A1 (en) | 2012-04-30 | 2013-10-31 | Ca, Inc. | Trusted public infrastructure grid cloud |
| US20130298242A1 (en) | 2012-05-01 | 2013-11-07 | Taasera, Inc. | Systems and methods for providing mobile security based on dynamic attestation |
| US20130297604A1 (en) | 2012-05-01 | 2013-11-07 | Research In Motion Limited | Electronic device and method for classification of communication data objects |
| US20130298185A1 (en) | 2012-05-02 | 2013-11-07 | Kony Solutions, Inc. | Mobile application management systems and methods thereof |
| US20130298201A1 (en) | 2012-05-05 | 2013-11-07 | Citrix Systems, Inc. | Systems and methods for network filtering in vpn |
| US20130303194A1 (en) | 2012-05-11 | 2013-11-14 | Iolo Technologies, Llc | Automatic determination of and reaction to mobile user routine behavior based on geographical and repetitive pattern analysis |
| US20130311597A1 (en) | 2012-05-16 | 2013-11-21 | Apple Inc. | Locally backed cloud-based storage |
| US20130318345A1 (en) | 2012-05-22 | 2013-11-28 | Harris Corporation | Multi-tunnel virtual private network |
| US20130333005A1 (en) | 2012-06-07 | 2013-12-12 | Sk Planet Co., Ltd. | Cloud service system based on enhanced security function and method for supporting the same |
| US20130346268A1 (en) | 2012-06-21 | 2013-12-26 | Google Inc. | Mobile Application Management |
| US20140020062A1 (en) | 2012-07-11 | 2014-01-16 | Chandra Shekhar Rao Tumula | Techniques for protecting mobile applications |
| US20140020073A1 (en) | 2012-07-13 | 2014-01-16 | Troy Jacob Ronda | Methods and systems for using derived credentials to authenticate a device across multiple platforms |
| US20140059642A1 (en) | 2012-08-24 | 2014-02-27 | Vmware, Inc. | Method and system for facilitating isolated workspace for applications |
| US8613070B1 (en) | 2012-10-12 | 2013-12-17 | Citrix Systems, Inc. | Single sign-on access in an orchestration framework for connected devices |
Non-Patent Citations (19)
| Title |
|---|
| "Citrix XenMobile Technology Overview: White Paper," Citrix White Papers online, Jul. 31, 2012, pp. 1-14; retrieved from http://insight.com/content/aam/insight/en-US/pdfs/citrix/xenmobile-tech-overview.pdf, retrieved Jan. 27, 2014. |
| Apple Inc., iPad User Guide for iOS 6.1 Software, Jan. 2013, Chapter 26, Accessibility, pp. 107-108. |
| International Search Report and Written Opinion dated Feb. 4, 2014 in Application No. PCT/US2013/064349. |
| International Search Report and Written Opinion mailed Jan. 21, 2014 in International Application No. PCT/US2013/063856. |
| International Search Report and Written Opinion mailed Nov. 26, 2013 in Internation Application No. PCT/US2013/060388. |
| Lowe, "Application-Specific VPNs," Dec. 13, 2005. |
| Mysore et al., "The Liquid Media System-a Multi-Device Streaming Media Orchestration Framework", Ubicomp 2003 Workshop, pp. 1-4. |
| Na et al., "Personal Cloud Computing Security Framework," 2010 IEEE Asia-Pacific Computing Conference, 2010, pp. 671-675. |
| Non-Final Office Action dated Dec. 20, 2013, in U.S. Appl. No. 14/043,301. |
| Non-Final Office Action dated Dec. 27, 2013, in U.S. Appl. No. 14/042,941. |
| Non-Final Office Action dated Dec. 27, 2013, in U.S. Appl. No. 14/043,012. |
| Non-Final Office Action dated Dec. 30, 2013, in U.S. Appl. No. 14/043,164. |
| Non-Final Office Action dated Dec. 31, 2013, in U.S. Appl. No. 14/042,984. |
| Non-Final Office Action dated Jan. 6, 2014, in U.S. Appl. No. 14/043,229. |
| Ranjan et al., "Programming Cloud Resource Orchestration Framework: Operations and Research Challenges", arvix.org, 2012, pp. 1-19. |
| Wilson et al., "Unified Security Framework", In proceedings of the 1st International Symposium on Information and Communication Technologies, pp. 500-505. Trinity College Dublin, 2003. |
| Written Opinion and International Search Report, PCT/US2013/062636, Jan. 10, 2014. |
| Xuetao Wei, et al., "Malicious Android Applications in the Enterprise: What Do They Do and How Do We Fix It?,". ICDE Workshop on Secure Data Management on Smartphones and Mobiles, Apr. 2012, 4 pages. |
| Xuetao Wei, et al., "Malicious Android Applications in the Enterprise: What Do They Do and How Do We Fix It?,"• ICDE Workshop on Secure Data Management on Smartphones and Mobiles, Apr. 2012, 4 pages. |
Cited By (12)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US9355228B2 (en) | 2012-07-13 | 2016-05-31 | Angel Secure Networks, Inc. | System and method for policy driven protection of remote computing environments |
| US10713087B2 (en)* | 2014-01-10 | 2020-07-14 | Citrix Systems, Inc. | Management of unmanaged user accounts and tasks in a multi-account mobile application |
| US20210211507A1 (en)* | 2018-09-24 | 2021-07-08 | Salesforce.Com, Inc. | Multi-channel session connection management mechanism |
| US12041041B2 (en)* | 2019-08-21 | 2024-07-16 | Truist Bank | Location-based mobile device authentication |
| US20210081362A1 (en)* | 2019-09-13 | 2021-03-18 | Citrix Systems, Inc. | Multi-web application collaboration techniques |
| US11669497B2 (en)* | 2019-09-13 | 2023-06-06 | Citrix Systems, Inc. | Multi-web application collaboration techniques |
| US20210136059A1 (en)* | 2019-11-05 | 2021-05-06 | Salesforce.Com, Inc. | Monitoring resource utilization of an online system based on browser attributes collected for a session |
| US12047373B2 (en)* | 2019-11-05 | 2024-07-23 | Salesforce.Com, Inc. | Monitoring resource utilization of an online system based on browser attributes collected for a session |
| US12289308B2 (en)* | 2020-11-13 | 2025-04-29 | Cyberark Software Ltd. | Native remote access to target resources using secretless connections |
| US20220294788A1 (en)* | 2021-03-09 | 2022-09-15 | Oracle International Corporation | Customizing authentication and handling pre and post authentication in identity cloud service |
| US12238101B2 (en)* | 2021-03-09 | 2025-02-25 | Oracle International Corporation | Customizing authentication and handling pre and post authentication in identity cloud service |
| US20230237171A1 (en)* | 2022-01-21 | 2023-07-27 | Vmware, Inc. | Securing web browsing on a managed user device |
Also Published As
| Publication number | Publication date |
|---|---|
| JP6397957B2 (en) | 2018-09-26 |
| US8850010B1 (en) | 2014-09-30 |
| US20160241599A1 (en) | 2016-08-18 |
| US8898732B2 (en) | 2014-11-25 |
| US8893221B2 (en) | 2014-11-18 |
| US9355223B2 (en) | 2016-05-31 |
| KR20170045372A (en) | 2017-04-26 |
| KR101728899B1 (en) | 2017-04-20 |
| US20140298405A1 (en) | 2014-10-02 |
| US8996709B2 (en) | 2015-03-31 |
| US8881228B2 (en) | 2014-11-04 |
| US20140297861A1 (en) | 2014-10-02 |
| US9158895B2 (en) | 2015-10-13 |
| US20140297860A1 (en) | 2014-10-02 |
| CN105247531A (en) | 2016-01-13 |
| US20140298404A1 (en) | 2014-10-02 |
| JP2016519817A (en) | 2016-07-07 |
| CN105247531B (en) | 2018-03-20 |
| US20140297862A1 (en) | 2014-10-02 |
| EP3413227A1 (en) | 2018-12-12 |
| JP2017168111A (en) | 2017-09-21 |
| US20140297819A1 (en) | 2014-10-02 |
| US20140298348A1 (en) | 2014-10-02 |
| US20140297756A1 (en) | 2014-10-02 |
| US20140298442A1 (en) | 2014-10-02 |
| EP2979218A1 (en) | 2016-02-03 |
| US10097584B2 (en) | 2018-10-09 |
| KR102038842B1 (en) | 2019-10-31 |
| KR20160018476A (en) | 2016-02-17 |
| WO2014158228A1 (en) | 2014-10-02 |
| JP6131381B2 (en) | 2017-05-17 |
| US9112853B2 (en) | 2015-08-18 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| US10097584B2 (en) | Providing a managed browser | |
| EP3531662B1 (en) | Providing mobile device management functionalities | |
| US8910264B2 (en) | Providing mobile device management functionalities | |
| US9985850B2 (en) | Providing mobile device management functionalities | |
| US8849978B1 (en) | Providing an enterprise application store | |
| US8813179B1 (en) | Providing mobile device management functionalities |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| AS | Assignment | Owner name:CITRIX SYSTEMS, INC., FLORIDA Free format text:ASSIGNMENT OF ASSIGNORS INTEREST;ASSIGNOR:QURESHI, WAHEED;REEL/FRAME:031451/0153 Effective date:20130929 | |
| STCF | Information on status: patent grant | Free format text:PATENTED CASE | |
| MAFP | Maintenance fee payment | Free format text:PAYMENT OF MAINTENANCE FEE, 4TH YEAR, LARGE ENTITY (ORIGINAL EVENT CODE: M1551) Year of fee payment:4 | |
| MAFP | Maintenance fee payment | Free format text:PAYMENT OF MAINTENANCE FEE, 8TH YEAR, LARGE ENTITY (ORIGINAL EVENT CODE: M1552); ENTITY STATUS OF PATENT OWNER: LARGE ENTITY Year of fee payment:8 | |
| AS | Assignment | Owner name:WILMINGTON TRUST, NATIONAL ASSOCIATION, DELAWARE Free format text:SECURITY INTEREST;ASSIGNOR:CITRIX SYSTEMS, INC.;REEL/FRAME:062079/0001 Effective date:20220930 | |
| AS | Assignment | Owner name:GOLDMAN SACHS BANK USA, AS COLLATERAL AGENT, NEW YORK Free format text:SECOND LIEN PATENT SECURITY AGREEMENT;ASSIGNORS:TIBCO SOFTWARE INC.;CITRIX SYSTEMS, INC.;REEL/FRAME:062113/0001 Effective date:20220930 Owner name:WILMINGTON TRUST, NATIONAL ASSOCIATION, AS NOTES COLLATERAL AGENT, DELAWARE Free format text:PATENT SECURITY AGREEMENT;ASSIGNORS:TIBCO SOFTWARE INC.;CITRIX SYSTEMS, INC.;REEL/FRAME:062113/0470 Effective date:20220930 Owner name:BANK OF AMERICA, N.A., AS COLLATERAL AGENT, NORTH CAROLINA Free format text:PATENT SECURITY AGREEMENT;ASSIGNORS:TIBCO SOFTWARE INC.;CITRIX SYSTEMS, INC.;REEL/FRAME:062112/0262 Effective date:20220930 | |
| AS | Assignment | Owner name:CLOUD SOFTWARE GROUP, INC. (F/K/A TIBCO SOFTWARE INC.), FLORIDA Free format text:RELEASE AND REASSIGNMENT OF SECURITY INTEREST IN PATENT (REEL/FRAME 062113/0001);ASSIGNOR:GOLDMAN SACHS BANK USA, AS COLLATERAL AGENT;REEL/FRAME:063339/0525 Effective date:20230410 Owner name:CITRIX SYSTEMS, INC., FLORIDA Free format text:RELEASE AND REASSIGNMENT OF SECURITY INTEREST IN PATENT (REEL/FRAME 062113/0001);ASSIGNOR:GOLDMAN SACHS BANK USA, AS COLLATERAL AGENT;REEL/FRAME:063339/0525 Effective date:20230410 Owner name:WILMINGTON TRUST, NATIONAL ASSOCIATION, AS NOTES COLLATERAL AGENT, DELAWARE Free format text:PATENT SECURITY AGREEMENT;ASSIGNORS:CLOUD SOFTWARE GROUP, INC. (F/K/A TIBCO SOFTWARE INC.);CITRIX SYSTEMS, INC.;REEL/FRAME:063340/0164 Effective date:20230410 | |
| AS | Assignment | Owner name:WILMINGTON TRUST, NATIONAL ASSOCIATION, AS NOTES COLLATERAL AGENT, DELAWARE Free format text:SECURITY INTEREST;ASSIGNORS:CLOUD SOFTWARE GROUP, INC. (F/K/A TIBCO SOFTWARE INC.);CITRIX SYSTEMS, INC.;REEL/FRAME:067662/0568 Effective date:20240522 |