US8561177B1 - Systems and methods for detecting communication channels of bots - Google Patents
Systems and methods for detecting communication channels of botsDownload PDFInfo
- Publication number
- US8561177B1 US8561177B1US11/998,605US99860507AUS8561177B1US 8561177 B1US8561177 B1US 8561177B1US 99860507 AUS99860507 AUS 99860507AUS 8561177 B1US8561177 B1US 8561177B1
- Authority
- US
- United States
- Prior art keywords
- bot
- communication channel
- suspected
- communication
- command
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Active, expires
Links
Images
Classifications
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/50—Monitoring users, programs or devices to maintain the integrity of platforms, e.g. of processors, firmware or operating systems
- G06F21/55—Detecting local intrusion or implementing counter-measures
- G06F21/554—Detecting local intrusion or implementing counter-measures involving event detection and direct action
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/50—Monitoring users, programs or devices to maintain the integrity of platforms, e.g. of processors, firmware or operating systems
- G06F21/55—Detecting local intrusion or implementing counter-measures
- G06F21/56—Computer malware detection or handling, e.g. anti-virus arrangements
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/14—Network architectures or network communication protocols for network security for detecting or protecting against malicious traffic
- H04L63/1441—Countermeasures against malicious traffic
- H04L63/145—Countermeasures against malicious traffic the attack involving the propagation of malware through the network, e.g. viruses, trojans or worms
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/14—Network architectures or network communication protocols for network security for detecting or protecting against malicious traffic
- H04L63/1441—Countermeasures against malicious traffic
- H04L63/1491—Countermeasures against malicious traffic using deception as countermeasure, e.g. honeypots, honeynets, decoys or entrapment
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F9/00—Arrangements for program control, e.g. control units
- G06F9/06—Arrangements for program control, e.g. control units using stored programs, i.e. using an internal store of processing equipment to receive or retain programs
- G06F9/44—Arrangements for executing specific programs
- G06F9/455—Emulation; Interpretation; Software simulation, e.g. virtualisation or emulation of application or operating system execution engines
- G06F9/45533—Hypervisors; Virtual machine monitors
- G06F9/45558—Hypervisor-specific management and integration aspects
- G06F2009/45591—Monitoring or debugging support
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L2463/00—Additional details relating to network architectures or network communication protocols for network security covered by H04L63/00
- H04L2463/144—Detection or countermeasures against botnets
Definitions
- the present inventionrelates generally to network security and more particularly to detecting command and control communication channels of a bot.
- malwaremalicious software
- malwaremay include any program or file that is harmful to a computer user, such as bots, computer viruses, worms, Trojan horses, spyware, or any programming that gathers information about a computer user or otherwise operates without permission.
- botscomputer viruses
- wormsworms
- Trojan horsesspyware
- Various processes and deviceshave been employed to prevent the problems that malware can cause.
- computersoften include antivirus scanning software that scans a particular client device for viruses.
- the scanningmay be performed based on a schedule specified by a user associated with the particular computer, a system administrator, and so forth.
- a virusis detected by the scanning software, some damage on the particular computer may have already occurred.
- honey potis a computer system on the Internet that is expressly set up to attract and “trap” an illicit user that attempts to penetrate another's computer system.
- the illicit usercan include a hacker, a cracker, or a script kiddy, for example.
- the honey potrecords the activities associated with the invasion of the computer system.
- the honey potis being invaded, so too are other users' computer systems on the same network.
- other users' computer systemsmay be harmed while the honey pot determines the nature of the malware invading the honey pot's own computer system.
- malwarecomprises a bot.
- a botis a software robot configured to remotely control all or a portion of a digital device (e.g., a computer) without authorization by the digital device's user.
- Bot related activitiesinclude bot propagation and attacking other computers on a network. Bots commonly propagate by scanning nodes (e.g., computers or other digital devices) available on a network to search for a vulnerable target. When a vulnerable computer is scanned, the bot may install a copy of itself. Once installed, the new bot may continue to seek other computers on a network to infect.
- scanning nodese.g., computers or other digital devices
- a botmay also, without the authority of the infected computer user, establish a command and control communication channel to receive instructions.
- Botsmay receive command and control communication from a centralized bot server or another infected computer (e.g., via a peer-to-peer (P2P) network established by a bot on the infected computer).
- P2Ppeer-to-peer
- the botmay receive instructions to perform bot related activities.
- a plurality of botsi.e., a botnet
- the infected computersi.e., zombies
- bot infected computersmay be directed to ping another computer on a network in a denial-of-service attack.
- one or more botsmay direct the infected computer to transmit spam across a network.
- a botmay also receive instructions to transmit information regarding the infected host computer.
- the botmay be instructed to act as a keylogger and record keystrokes on the infected host computer.
- the botmay also be instructed to search for personal information and email addresses of other users contained in an email or contacts file. This information may be transmitted to one or more other infected computers or a user in command of the bot or botnet.
- Systems and methods for detecting a command and control communication channel of a botare provided.
- presence of a communication channel between a first network device and a second network deviceis detected.
- a fingerprint modulemay scan for a bot oriented command communications in an IRC channel.
- the fingerprint modulescans for commands or messages that indicate that an IRC channel is being established.
- a port modulemay monitor for communications originating from a non-standard port.
- a virtual machinemay be utilized to detect C&C communication channels either in a replay virtual machine environment or in a direct entry virtual machine environment.
- intercepted or replayed network data obtained from the communication channelis transmitted to the virtual machine, and the virtual machine response is then analyzed to determine if the virtual machine is infected.
- an analysis environmentmay wait for an outbound domain name system (DNS) request, which may also identify the C&C channel.
- DNSdomain name system
- a pseudo-DNS server in the virtual machinecan respond to the request with an IP address mapped to an internal-to-virtual machine-analysis pseudo-server.
- the outbound IRC or web request made to the supplied IP addressmay confirm the C&C channel.
- a recovery processmay be initiated.
- the devices that are suspected as being infectedmay be flagged and/or proper users and administrators notified.
- icons associated with nodes coupled to a networkmay be color coded based on their association with any infection propagation, command and control communication with a bot, and/or bot attack.
- a routeri.e., switch
- a bot servere.g., from the source IP address of the bot server
- FIG. 1is a diagram of a channel detection environment in which embodiments of the present invention may be practiced.
- FIG. 2is a block diagram of an exemplary bot detector implementing some embodiments of the present invention.
- FIG. 3is a block diagram of an exemplary controller implementing some embodiments of the present invention.
- FIG. 4is a block diagram of an exemplary analysis environment, in accordance with some embodiments of the present invention.
- FIG. 5is a flowchart of an exemplary method for detecting a C&C channel of a bot.
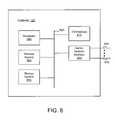
- FIG. 6is a block diagram of the controller, in accordance with one embodiment of the present invention.
- Exemplary systems and methods for detection of a command and control communication channel of a botare provided.
- the bot running on a compromised devicemay be part of a plurality of software robots (e.g., a botnet) which run autonomously on a collection of compromised devices under a common command and control (C&C) infrastructure.
- a bot on the compromised devicemay open an Internet Relay Chat (IRC) channel with another device to receive commands. This IRC channel may be referred to as a C&C communication channel.
- IRCInternet Relay Chat
- the communication channel detection systemmay comprise a dynamic honey pot.
- a dynamic honey potcan monitor network traffic to detect the presence of a C&C communication channel. If a C&C channel or a suspected C&C channel is detected, then the network data from the C&C communication channel may be intercepted. In exemplary embodiments, the network traffic does not need to be directly transmitted to the dynamic honey pot. Rather, the dynamic honey pot can detect possible bot infection attempts or command and control communication with an existing bot on other devices on the network. Upon detection, the dynamic honey pot can then intercept future network data.
- network data from a communication networkmay be copied and analyzed. If a C&C channel or a suspected C&C channel is detected, related network data may be intercepted. The intercepted network data may continue to be analyzed. If the intercepted network data comprises a network attack, command and control communication, and/or an attempt to propagate the bot, an unauthorized activity signature configured to identify the activity and/or bot may be generated.
- the botcompromises one or more compromised devices which may send spam and malware, such as viruses, worms, or Trojan horses, for example.
- a virusis an intrusive program that infects a computer file by inserting a copy of itself in the file. The copy is usually executed when the file is loaded into memory, allowing the virus to infect other files.
- a wormis a program that propagates itself across multiple computers, usually by creating copies of itself in each computer's memory. A worm may duplicate itself in a computer so many times that it causes the computer to crash.
- a Trojan horseis a destructive program disguised as a game, utility, or application. When run by a user or computer program, a Trojan horse can harm the computer system while appearing to do something useful.
- Malwaremay also include adware and spyware.
- Adwareis a program configured to direct advertisements to a computer or a particular user.
- adwareidentifies the computer and/or the user to various websites visited by a browser on the computer. The website may then use the adware to either generate pop-up advertisements or otherwise direct specific advertisements to the user's browser.
- Spywareis a program configured to collect information regarding the user, the computer, and/or a user's network habits.
- spywaremay collect information regarding the names and types of websites that the user browses and then transmit the information to another computer.
- Adware and spywareare often added to the user's computer after the user browses to a website that hosts the adware and/or spyware. The user is often unaware that these programs have been added and are similarly unaware of the adware and/or spyware's function.
- FIG. 1is a diagram of a channel detection environment 100 in which embodiments of the present invention may be practiced.
- the channel detection environment 100may comprise a bot server 105 in communication via a communication network 110 with a network device 115 .
- a tap 120may be coupled to the communication network 110 .
- the tap 120may be further coupled to a controller 125 .
- a router(not shown) may be provided for re-routing data from the communication network 110 .
- the bot server 105 and the network device 110comprise digital devices.
- a digital devicecomprises any device with a processor. Some examples of digital devices include computers, servers, laptops, personal digital assistants, and cellular telephones.
- the bot server 105is configured to transmit network data over the communication network 110 to the network device 115 , which is configured to receive the network data.
- the bot server 105may establish a C&C communication channel with the network device 115 via the communication network 110 .
- the C&C communication channelmay be utilized by the bot server 105 to control a bot on the node or the node itself on the network device 115 .
- the bot server 105may attempt to control the network device 115 by transmitting instructions or a bot to the network device 115 .
- the bot server 105is a computer controlled by an illicit user to control one or more bots or one or more network devices 115 through the use of bots.
- the bot server 105is a network device similar to the network device 115 ; the bot server 105 may be a part of a P2P communication network for transmitting instructions to a bot on another digital device.
- the network device 115may be a part of a P2P communication network whereby the network device 115 may transmit instructions to another network device similar to a bot server 105 .
- the tap 120may comprise a digital data tap configured to monitor network data and provide a copy of the network data to the controller 125 .
- the tap 120comprises a span port.
- the network datacomprises signals and data that are transmitted over the communication network 110 including data flows from the bot server 105 to the network device 115 .
- the network datamay include command and control instructions transmitted from the bot server 105 .
- the tap 120copies the network data without an appreciable decline in performance of the bot server 105 , the network device 115 , or the communication network 110 .
- the tap 120may copy any portion of the network data.
- the tap 120can receive and copy any number of data packets of the network data.
- the tap 120can monitor and copy data transmitted from multiple devices without appreciably affecting the performance of the communication network 110 or the devices coupled to the communication network 110 .
- the tap 120can sample the network data based on a sampling scheme.
- the tap 120can also capture metadata from the network data.
- the metadatacan be associated with the bot server 105 and/or the network device 115 .
- the metadatamay identify the bot server 105 and/or the network device 110 .
- the bot server 105transmits metadata, which is captured by the tap 120 .
- a heuristic moduledescribed in more detail below, can detect the bot server 105 and/or the network device 110 by analyzing data packets within the network data and generate the metadata.
- the communication network 110may comprise a public computer network such as the Internet, a private computer network such as a wireless telecommunication network, wide area network, local area network, or any other type of network enabled to provide communications between coupled devices.
- a public computer networksuch as the Internet
- a private computer networksuch as a wireless telecommunication network, wide area network, local area network, or any other type of network enabled to provide communications between coupled devices.
- FIG. 1depicts data transmitted from the bot server 105 to the network device 115 , either device can transmit and receive data from the other device.
- FIG. 1depicts data transmitted from the bot server 105 to the network device 115
- either devicecan transmit and receive data from the other device.
- FIG. 1depicts data transmitted from the bot server 105 to the network device 115
- either devicecan transmit and receive data from the other device.
- FIG. 1depicts data transmitted from the bot server 105 to the network device 115
- FIG. 1depicts data transmitted from the bot server 105 to the network device 115
- FIG. 1depicts data transmitted from the bot server 105 to the network device 115
- FIG. 1depicts data transmitted from the bot server 105 to the network device 115
- controller 125there may be any number of bot servers 105 , communication networks 110 , network devices 115 , taps 120 , and controllers 125 .
- the controller 125may comprise a processor and/or software configured to receive and analyze network data for the presence of network data sent via the C&C communication channel. In exemplary embodiments, the controller 125 receives network data over the tap 120 . If the controller 125 detects commands within network data that potentially establishes a C&C communication channel, the controller 125 may intercept the associated network data. In one example, the controller 125 may intercept network data from the same data flow as that which potentially established the C&C communication channel. In another example, the controller 125 may intercept all network data from a node on the communication network that either received or sent the commands (e.g., the bot server 105 and the network device 115 ). When network data is intercepted, the network data is no longer received by the intended recipient but rather is received by the controller 125 . In some embodiments, the associated network data is intercepted when network data is flagged as suspicious.
- the controller 125can organize the network data into one or more data flows. Data flows can then be reconstructed based on the network data samples received from the tap. The controller 125 is further discussed in more detail in connection with FIG. 3 .
- FIG. 2is a block diagram of an exemplary bot detector 200 implementing some embodiments of the present invention.
- the bot detector 200may be coupled to or comprised within the controller 125 .
- the bot detector 200is coupled to the communication network 110 .
- the bot detector 200is software that is loaded on a digital device.
- the bot detector 200may be provided to a user for installation onto their LAN or a network device (e.g., network device 115 ).
- the exemplary bot detector 200may comprise a protocol fingerprint module 205 , a protocol state description module 210 , a port module 215 , a signature module 220 , and a tracking module 225 .
- Alternative embodimentsmay comprise more, less, or functionally equivalent modules.
- the use of an IRC protocolis used for bot command and control. Therefore, detecting the existence or establishment of an IRC channel in the network may indicate a possible botnet C&C communication channel.
- the protocol fingerprint module 205is utilized to detect an IRC C&C channel.
- the exemplary protocol fingerprint module 205may comprise input/output related behavior that uniquely identifies a protocol implementation (e.g., version number, feature, vendor, etc.).
- a network tracemay map routes between the bot server 105 and the network device 115 .
- network datais scanned to detect a bot oriented IRC command, such as .advscan and SCAN, to highlight IRC channels to a potential bot server 105 .
- a bot oriented IRC commandsuch as .advscan and SCAN
- Stateful protocol fingerprinting analysis by the protocol fingerprint module 205may be performed to detect bot oriented commands in the IRC channels. For example, instead of simply scanning for .advscan in an input stream, the protocol fingerprint module 205 may first look for an IRC channel establishment (e.g., JOIN and JOIN confirm commands), and then scan for an .advscan message.
- an IRC channel establishmente.g., JOIN and JOIN confirm commands
- the protocol fingerprinting module 205may be extensible to other protocols via protocol feature description using protocol state descriptions provided by the protocol state description module 210 and regular expressions. A description of the IRC protocol is made possible using this technique. For example, if the protocol state description module 210 determines that the protocol being used is IRC, the protocol fingerprint module 205 may be configured by the protocol state description module 210 to detect IRC commands.
- the signature module 220provides signatures which identify bot related behavior, known bot servers 105 , suspected bot servers, mechanisms to block attacks, mechanisms to block bot propagation, and/or mechanisms that remove bots from network devices 115 . These signatures may be provided to the protocol fingerprint module 205 and/or the controller 125 to take corrective action.
- a higher degree of confidencecan be ascribed to a suspected bot list. For example, if traffic is observed on a suspected IRC C&C channel and immediately thereafter there is discovery of infection propagation from the IRC server (e.g., bot server 105 or network device 115 ) that provided the C&C communication, then all nodes that have communicated to the same IRC server are highly suspect. This broadens the visibility of infected systems from those that are observed actively propagating infections to systems that have not been observed actively propagating but have been in communication with a confirmed active bot server 105 .
- the IRC servere.g., bot server 105 or network device 115
- detection of a central C&C serverallows authorities and system administrators to take the central C&C server offline and/or block communications with the central C&C server. Once the C&C server has been neutralized, the bots that may otherwise receive commands from the C&C server are no longer controlled and are, in some examples, unable to function.
- bot server 105may be easily neutralized by shutting down the central C&C server, botnets controlled using a Peer-to-Peer (P2P) communications protocol have been developed. Due to the distributed nature of P2P communication channel, it becomes much harder to shut down a P2P controlled botnet.
- P2PPeer-to-Peer
- detection of a P2P C&C channelmay be performed by the port module 215 detecting communications on a seldom used (non-standard) port.
- standard well-known portsare marked. For example, all well known ports and services in a network environment may be categorized as “standard.”
- a standard listmay be compiled and stored by the port module 215 .
- the standard listmay comprise all ports defined in Internet RFCs as well as ports and services used by standard versions of Windows and Linux.
- the port module 215may “learn” standard ports through observation of network data on a communication network 110 .
- the software on multiple network devices 115may transmit and receive network data on a variety of ports.
- the network datais received by the controller 125 and the port module 215 may update the standard list based on the ports of the network devices 115 that receive and transmit data over a predetermined period of time.
- the port module 215will mark a number of nodes communicating over a non-standard port over a predetermined period of time a P2P communications channel when the number of nodes is over some threshold (e.g., 3 or 4 nodes). In one example, the port module 215 will mark a potential P2P communications channel when four network devices 115 communicate with each other over a non-standard port within 4 seconds.
- the port module 215may detect P2P chains that use a different port for each leg of the chain.
- the time difference between anomaly propagation in the chainmay be assumed to be small (e.g., less than 10 seconds). This short time difference allows the tracking module 225 to track various nodes without running into resource constraint issues.
- the tracking module 225identifies network devices 115 that communicate with other network devices 115 over the predetermined period of time. The port module 215 may identify those network devices 115 communicating over non-standard ports. Once the port module 215 detects a network device 115 communicating over a non-standard port, the port module 215 may check the tracking module 225 to determine if any other network device 115 has been communicating over non-standard ports.
- the tracking module 225tracks the source and destination of at least some communications over the communication network 110 . If a bot server 105 or a potential bot server is detected, the tracking module 225 can provide a list of network devices 115 in communication with the bot server 105 or the potential bot server. In one example, the tracking module 225 can provide a list of nodes in communication with a suspected bot server 105 over a predetermined period of time.
- P2P channelWhile existence of a P2P channel is not conclusive evidence of a botnet, network operators may benefit from notification of P2P communications on their networks. If a P2P communication can be correlated to infection propagation via one or more nodes of the P2P chain, then all nodes of the P2P network may become highly suspect as members of a P2P controlled botnet.
- systemsmay be marked in order to identify infections.
- any nodes that are not associated with any infection propagationmay be placed in a yellow category.
- These nodese.g., network devices 115
- Nodes in an IRC or P2P network where at least one of the nodes (e.g., in a chain of nodes) is observed propagating an infectionmay be placed in, for example, an orange category.
- Nodes that are observed to be actively propagating an infectionmay be placed in a red category.
- Any nodes that have not been categorized as yellow, orange, or redmay be assigned to a green category.
- icons associated with nodesmay be colored and/or associated with a color category.
- FIG. 3is a block diagram of an exemplary controller 125 implementing embodiments of the present invention.
- the controller 125may be any digital device or software that receives network data.
- the exemplary controller 125may comprise bot detection components similar to the bot detector 200 of FIG. 2 including a protocol fingerprint module 305 , a protocol state description module 310 , and a tracking module 315 .
- the functions of the tracking module 225 ( FIG. 2 ) and the port module 215 ( FIG. 2 )are combined.
- the controller 125may further comprise a heuristic module 320 , a scheduler 325 , a fingerprint module 330 , a virtual machine pool 335 , an analysis environment 340 , a signature module 345 , and a policy engine 350 .
- the controller 125comprises a tap which is further coupled to the communication network 110 .
- the controller 125is coupled to an external tap 120 or may be directly coupled to the communication network 110 .
- the exemplary heuristic module 320may receive a copy of network data from the communication network 110 .
- the heuristic module 320applies heuristics and/or probability analysis to determine if the network data may contain suspicious activity (such as bot related activity). In one example, the heuristic module 320 flags network data as suspicious.
- the network datacan then be buffered and organized into a data flow.
- the data flowis then provided to the scheduler 325 . In some embodiments, the network data is provided directly to the scheduler 325 without buffering or organizing the data flow.
- the heuristic module 320can perform any heuristic and/or probability analysis. In some embodiments, once a C&C communication channel has been detected or suspected, analysis may be performed to confirm and/or verify the C&C channel. Once the protocol fingerprint module 305 identifies a potential C&C communication channel, network data from the channel is forwarded to the scheduler 325 .
- the heuristic module 320performs a dark internet protocol (IP) heuristic.
- IPinternet protocol
- a dark IP heuristiccan flag network data coming from a bot server 105 that has not previously been identified by the heuristic module 320 .
- the dark IP heuristiccan also flag network data going to an unassigned IP address.
- an attackerscans random IP addresses of a network to identify an active server or workstation.
- the dark IP heuristiccan flag network data directed to an unassigned IP address.
- the heuristic module 320can also perform a dark port heuristic.
- a dark port heuristiccan flag network data transmitted to an unassigned or unusual port address. Such network data transmitted to an unusual port can be indicative of a port scan by a worm, hacker, or bot.
- the heuristic module 320can flag network data from the bot server 105 or network device 115 that is significantly different than traditional data traffic transmitted by the bot server 105 or network device 115 .
- the heuristic module 320can flag network data from the bot server 105 such as a laptop that begins to transmit network data that is common to a server.
- the heuristic module 320can retain data packets belonging to a particular data flow previously copied by the tap 120 . In one example, the heuristic module 320 receives data packets from the tap 120 and stores the data packets within a buffer or other memory. Once the heuristic module 320 receives a predetermined number of data packets from a particular data flow, the heuristic module 320 performs the heuristics and/or probability analysis.
- the heuristic module 320performs heuristic and/or probability analysis on a set of data packets belonging to a data flow 320 can then continue to receive new data packets belonging to the same data flow. Once a predetermined number of new data packets belonging to the same data flow are received, the heuristic and/or probability analysis can be performed upon the combination of buffered and new data packets to determine a likelihood of suspicious activity.
- an optional bufferreceives the flagged network data from the heuristic module 320 .
- the buffercan buffer and organize the flagged network data into one or more data flows before providing the one or more data flows to the scheduler 325 .
- the buffercan buffer network data and stall before providing the network data to the scheduler 325 .
- the bufferstalls the network data to allow other components of the controller 125 time to complete functions or otherwise clear data congestion.
- the scheduler 325is a module that identifies the network device 115 to receive the copied network data and retrieves a virtual machine associated with the network device 115 .
- a virtual machinemay be software that is configured to mimic the performance of a device (e.g., the network device 115 ). The virtual machine can be retrieved from the virtual machine pool 335 .
- the heuristic module 320transmits the metadata identifying the network device 115 to receive the copied network data to the scheduler 325 .
- the scheduler 325receives one or more data packets of the network data from the heuristic module 320 and analyzes the one or more data packets to identify the network device 115 .
- the metadatacan be received from the tap 120 .
- the scheduler 325can retrieve and configure the virtual machine to mimic pertinent performance characteristics of the network device 115 .
- the scheduler 325configures characteristics of the virtual machine to mimic only those features of the network device 115 that are affected by the network data copied by the tap 120 .
- the scheduler 325can determine the features of the network device 115 that are affected by the network data by receiving and analyzing the network data from the tap 120 .
- Such features of the network device 115can include ports that are to receive the network data, select device drivers that are to respond to the network data and any other devices coupled to or contained within the network device 115 that can respond to the network data.
- the heuristic module 320can determine the features of the network device 115 that are affected by the network data by receiving and analyzing the network data from the tap 120 . The heuristic module 320 can then transmit the features of the destination device to the scheduler 325 .
- the optional fingerprint module 330is configured to determine the packet format of the network data to assist the scheduler 325 in the retrieval and/or configuration of the virtual machine. In one example, the fingerprint module 330 determines that the network data is based on a transmission control protocol/internet protocol (TCP/IP). Thereafter, the scheduler 325 will configure a virtual machine with the appropriate ports to receive TCP/IP packets. In another example, the fingerprint module 330 can configure a virtual machine with appropriate ports to receive user datagram protocol/internet protocol (UDP/IP) packets. The fingerprint module 330 can determine any type of packet format of the network data.
- TCP/IPtransmission control protocol/internet protocol
- UDP/IPuser datagram protocol/internet protocol
- the optional fingerprint module 330passively determines a software profile of the network data to assist the scheduler 325 in the retrieval and/or configuration of the virtual machine.
- the software profilemay comprise the operating system (e.g., Linux RH6.2) of the bot server 105 that generated the network data. The determination can be based on analysis of the protocol information of the network data.
- the fingerprint module 330determines that the software profile of network data is Windows XP, SP1. The fingerprint module 330 can then configure a virtual machine with the appropriate ports and capabilities to receive the network data based on the software profile.
- the fingerprint module 330passes the software profile of the network data to the scheduler 325 , and the scheduler 325 either selects or configures the virtual machine based on the profile.
- the virtual machine pool 335is configured to store virtual machines.
- the virtual machine pool 335may include any storage capable of storing virtual machines.
- the virtual machine pool 335stores a single virtual machine that can be configured by the scheduler 325 to mimic the performance of any network device, such as the network device 115 on the communication network 110 .
- the virtual machine pool 335can store any number of distinct virtual machines that can be configured to simulate the performance of any of the network devices 115 .
- the analysis environment 340is a module that simulates transmission of unencrypted or decrypted network data between the bot server 105 and the network device 115 to identify the effects of malware or illegitimate computer users (e.g., a hacker, computer cracker, or other computer user) by analyzing the simulation of the effects of the network data upon the network device 115 that is carried out on the virtual machine.
- malware or illegitimate computer userse.g., a hacker, computer cracker, or other computer user
- the analysis environment 340simulates transmission of the network data between the bot server 105 and the network device 115 to analyze the effects of the network data upon the network device 115 to detect unauthorized activity.
- the analysis environment 340simulates the transmission of the network data, behavior of the virtual machine can be closely monitored for unauthorized activity. If the virtual machine crashes, performs illegal operations, or performs bot related activity, the analysis environment 340 can react. In some embodiments, the analysis environment 340 performs dynamic taint analysis to identify unauthorized activity.
- the analysis environment 340can generate the unauthorized activity signature configured to identify network data containing unauthorized activity (e.g., malware attacks or bot related activity). Since the unauthorized activity signature does not necessarily require probabilistic analysis to detect unauthorized activity within network data, unauthorized activity detection based on the unauthorized activity signature may be very fast and save computing time.
- unauthorized activity signatureconfigured to identify network data containing unauthorized activity (e.g., malware attacks or bot related activity). Since the unauthorized activity signature does not necessarily require probabilistic analysis to detect unauthorized activity within network data, unauthorized activity detection based on the unauthorized activity signature may be very fast and save computing time.
- the unauthorized activity signaturemay provide code that may be used to eliminate or “patch” portions of network data containing an attack. Further, in some embodiments, the unauthorized activity signature may be used to identify and eliminate (i.e., delete) the malware causing the attack. The unauthorized activity signature may also be used to configure digital devices to eliminate vulnerabilities (e.g., correct system settings such as disabling active-x controls in a browser or updating an operating system.)
- the analysis environment 340may store the unauthorized activity signature within the signature module 345 .
- the analysis environment 340may also transmit or command the transmission of the unauthorized activity signature to one or more other controllers 125 , bot detectors 200 (e.g., to the signature module 220 ), network devices 115 , switches, and/or servers.
- bot detectors 200e.g., to the signature module 220
- network devices 115e.g., to the signature module 220
- switchese.g., switches, and/or servers.
- the signature module 345receives, authenticates, and stores unauthorized activity signatures.
- the unauthorized activity signaturesmay be generated by the analysis environment 340 or another controller 125 .
- the unauthorized activity signaturesmay then be transmitted to the signature module 345 of one, or more controllers 125 .
- the policy engine 350coupled to the heuristic module 320 and is a module that can identify network data as suspicious based upon policies contained within the policy engine 350 .
- the network device 115can be a computer designed to attract hackers and/or worms (e.g., a “honey pot”).
- the policy engine 350can contain a policy to flag any network data directed to the “honey pot” as suspicious since the “honey pot” should not be receiving any legitimate network data.
- the policy engine 350can contain a policy to flag network data directed to any network device 115 that contains highly sensitive or “mission critical” information.
- the policy engine 350can also dynamically apply a rule to copy all network data related to network data already flagged by the heuristic module 320 .
- the heuristic module 320flags a single packet of network data as suspicious.
- the policy engine 350then applies a rule to flag all data related to the single packet (e.g., associated data flows) as suspicious.
- the policy engine 350flags network data related to suspicious network data until the analysis environment 340 determines that the network data flagged as suspicious is related to unauthorized activity.
- the policy engine 350may scan network data to detect unauthorized activity based upon an unauthorized activity signature. In some embodiments, the policy engine 350 retrieves the unauthorized activity signature from the signature module 345 . The network data is then scanned for unauthorized activity based on the unauthorized activity signature.
- the policy engine 350can scan both the header and body of a packet of network data. In some embodiments, the policy engine 350 scans only the header of the packet for unauthorized activity based on the unauthorized activity signature. If unauthorized activity is found, then no further scanning may be performed. In other embodiments, the policy engine 350 scans the packet contents for unauthorized activity.
- Unauthorized activitymay be found by scanning only the header of a packet, the contents of the packet, or both the header and the contents of the packet. As a result, unauthorized activity that might otherwise evade discovery can be detected. In one example, evidence of unauthorized activity may be located within the contents of the packet. By scanning only the contents of the packet, unauthorized activity may be detected.
- the policy engine 350may take action.
- the policy engine 350may generate a rule or command an interceptor module (not shown) to intercept network data from the node that transmitted the network data and delete or bar the packet from the communication network 110 .
- the policy engine 350 and/or the interceptor modulemay also quarantine, delete, or bar other packets belonging to the same data flow as the unauthorized activity packet.
- the interceptor modulecan re-route the associated network data to a virtual machine from the virtual machine pool 335 .
- the heuristic module 320can provide information that the network data is suspicious.
- the interceptor modulecan intercept all of the network data that is initially flagged by the heuristic module 320 .
- the interceptor modulecan also base the interception of data on the detection of a malware attack by the analysis environment 340 or a policy or signature by the policy engine 350 .
- the interceptor modulecan provide the intercepted data to the heuristic module 320 for analysis with a heuristic or to the analysis environment 340 to orchestrate the transmission of the intercepted data to detect a malware attack. If no malware attack is detected, the interceptor module can transmit some or all of the intercepted data to the intended recipient (e.g., network device 115 .) If a malware attack is detected within the intercepted data, the unauthorized activity signature may be generated by the signature module 345 and transmitted to one or more controllers 125 or other digital devices.
- the interceptor modulecan redirect network data from the bot server 105 in any number of ways including, but not limited to, configuring a switch, Address Resolution Protocol (ARP) manipulation, or DHCP services.
- ARPAddress Resolution Protocol
- the interceptor modulemay send a request to a switch to redirect network data from any bot server 105 to the controller 125 .
- the switchincludes any device configured to receive and direct network data between one or more digital devices. Examples of a switch include, but is not limited to, a router, gateway, bridge, and, or server.
- executable codeis loaded onto the switch.
- the executable codeconfigures the switch to direct network data from any bot server 105 to the controller 125 .
- the executable codeallows the interceptor module to transmit a request to the switch to direct network data from the bot server 105 to the controller 125 .
- the interceptor moduleconfigures the router to intercept network data from the bot server 105 for a predetermined time. The predetermined time may be set by the interceptor module, preloaded into the switch, or configured by a user.
- the interceptor modulemay manipulate dynamic host configuration protocol (DHCP) services to intercept network data. As the bot server 105 transmits network data that is flagged as suspicious or otherwise identified as containing a malware attack.
- the interceptor modulemay manipulate DHCP services to assign new IP addresses, associate the controller 125 MAC address with the IP address of the network device 115 , or otherwise redirect network data from the bot server 105 to the controller 125 .
- DHCPdynamic host configuration protocol
- the interceptor modulecan manipulate the DHCP server to configure the bot server 105 with a gateway IP address which is the same as the controller's IP address to send all network data to the controller 125 .
- the interceptor modulemay perform DHCP services for the communication network 110 as a DHCP server.
- the heuristic module 320 or the interceptor modulescans the copied network data flagged as suspicious to identify a source IP address and a target IP address.
- the source IP addressis the IP address of the bot server 105 and the target IP address is the IP address of the network device 115 .
- the interceptor modulemay send an ARP reply to the bot server 105 .
- the ARP replyis configured to identify the MAC address of the controller 125 with the IP address of the network device 115 .
- the bot server 105may begin to send network data intended for the destination device to the controller 125 .
- a policy within the policy engine 350may indicate which IP addresses are bot servers 105 . Whenever a bot server 105 sends network data for the first time to a network device 115 , the bot server 105 may transmit an ARP request. The network data identifying the source IP address is copied by the tap 120 and the policy within the policy engine 350 can flag the source IP address as a bot server 105 . Thereafter, the interceptor module may store the ARP request, and provide the controller 125 MAC address in an ARP reply to the switch and/or the bot server 105 .
- the switch and/or the bot server 105receives the controller 125 MAC address in the ARP reply, the IP address of the digital device (e.g., network device 115 ) will be associated with the controller 125 MAC address (e.g., in memory storage or cache). Network data intended for the network device 115 may then be transmit from the bot server 105 to the controller 125 .
- the IP address of the digital devicee.g., network device 115
- the controller 125 MAC addresse.g., in memory storage or cache
- the bot server 105may send the network data to any number of digital devices. Before the attack can proceed, the bot server 105 may send a separate ARP request for the IP address of every other digital device the malware wishes to send data to.
- the controller 125detects and responds to each ARP request by sending an ARP reply to each request with the controller 125 MAC address.
- the controller 125 MAC addressmay be associated with the IP address of the other digital devices on a table within the bot server 105 , switch, and/or server (not depicted). The table may be within memory, storage, buffered, and/or cached. As a result, network data transmitted by the bot server 105 to multiple network devices 115 may be intercepted by the controller 125 .
- the network datais re-routed to the virtual machine, as discussed herein. Because the network data is re-routed, the actual machine or the network device 115 for which the network data is intended may not receive the network data and is, as a result, unaffected. A plurality of the network data can be re-routed to more than one virtual machine at one time (e.g., in parallel.) Thus, if the network data intended for a plurality of the network devices 115 is flagged as suspicious, or as coming from the device that has previously been deemed suspicious (e.g., the bot server 105 ), the interceptor module can select a plurality of virtual machines on which to test the suspicious network data.
- the interceptor modulecan select a plurality of virtual machines on which to test the suspicious network data.
- the policy engine 350may scan network data to detect unauthorized activity (e.g., including some bot related activity) based upon an unauthorized activity signature. In some embodiments, the policy engine 350 retrieves the unauthorized activity signature from the signature module 345 . The network data is then scanned for unauthorized activity based on the unauthorized activity signature. The policy engine 350 can also flag network data as suspicious based on policies, as discussed herein.
- unauthorized activitye.g., including some bot related activity
- the policy engine 350retrieves the unauthorized activity signature from the signature module 345 .
- the network datais then scanned for unauthorized activity based on the unauthorized activity signature.
- the policy engine 350can also flag network data as suspicious based on policies, as discussed herein.
- FIG. 3depicts various modules comprising the controller 125 , fewer or more modules can comprise the controller 125 and still fall within the scope of various embodiments.
- FIG. 4is a block diagram of an exemplary analysis environment 340 , in accordance with some embodiments of the present invention.
- the analysis environment 340comprises a replayer 405 , a virtual switch 410 , and a virtual machine 415 .
- the replayer 405is a module that receives network data that has been flagged by the heuristic module 320 and replays the network data in the analysis environment 340 .
- the replayer 405mimics the behavior of the infected bot server 105 in transmitting the flagged network data.
- the replayer 405dynamically modifies session variables, as is appropriate, to emulate a “live” client or server of the protocol sequence being replayed.
- dynamic variables that may be dynamically substitutedinclude dynamically assigned ports, transaction IDs, and any other variable that is dynamic to each protocol session.
- the network data received from the heuristic module 205is transmitted to the virtual machine 415 without a replayer 405 .
- the virtual switch 410is a module that is capable of forwarding packets of flagged network data to the virtual machine 415 .
- the virtual switch 410simulates network device 115 .
- the virtual switch 410can route the data packets of the data flow to the correct ports of the virtual machine 415 .
- the virtual machine 415is a representation of the network device 115 that can be provided to the analysis environment 340 by the scheduler 325 .
- the scheduler 325retrieves a virtual machine 415 from the virtual machine pool 335 and configures the virtual machine 415 to mimic the network device 115 .
- the configured virtual machine 415is then provided to the analysis environment 340 where it can receive flagged network data from the virtual switch 410 .
- the analysis environment 340simulates the transmission of the network data, behavior of the virtual machine 415 can be closely monitored for unauthorized activity. If the virtual machine 415 crashes, performs illegal operations, performs abnormally, or allows access of data to an unauthorized computer user, the analysis environment 340 can react.
- virtual machinesmay be used to detect C&C channels and botnet infected systems using the C&C channels.
- C&C channel detectionmay occur in a replay virtual machine environment or in a direct entry virtual machine environment. While replay virtual analysis of virtual machines may be leveraged to extract C&C channel information, this may not be possible for all infection protocols. For infections protocols that can be replayed to result in a full bot infection, this technique may yield positive results. For infection protocols that do not go proceed to completion due to an inability to effectively replay unknown worms protocols, for example, the replay environment may not result in a full infection of the virtual machine 415 . This may result in a denial of C&C channel information extraction, which will only become evident post-infection. In those instances, the analysis environment 340 may flag the devices involved in the suspected C&C channel as possibly infected with a bot and continue to track the nodes that communicate with those devices that participate within the suspected C&C channel.
- Passive replay virtual machine environmentsmay be effective for C&C channel discovery, since a passive worm may introduce no new worm protocol. Instead, a passive worm may merely piggyback on an existing protocol. Therefore, the existing passive worm replay may be adequate to detect a full bot infection. Passive replay of, for example, web based exploits may be extended to result in full infection and extraction of C&C channel information. Direct entry virtual machine environments are effective in extracting C&C channel information, since there is no need to replay an unknown worm protocol.
- the analysis environment 340performs dynamic taint analysis to identify unauthorized activity.
- the malware attackmay cause a value that is normally derived from a trusted source to be derived from the user's own input.
- Program valuese.g., jump addresses and format strings
- Malwaremay attempt to exploit the program by overwriting these values.
- the analysis environment 340monitors and analyzes the behavior of the virtual machine 415 in order to determine a specific type of malware or the presence of an illicit computer user.
- the analysis environment 340can also generate computer code configured to eliminate new viruses, worms, bots, or other malware.
- the analysis environment 340can generate computer code configured to identify data within the network data indicative of a malware attack, repair damage performed by malware, or the illicit computer user. By simulating the transmission of suspicious network data and analyzing the response of the virtual machine, the analysis environment 340 can identify known and previously unidentified malware and the activities of illicit computer users before a computer system is damaged or compromised.
- the environmentcan wait for an outbound domain name system (DNS) request.
- DNSdomain name system
- the requested name in the DNS requestis likely a C&C channel.
- a pseudo-DNS server in the virtual machine environmentcan respond to this request with an IP address mapped to an internal-to-virtual machine-analysis pseudo-server. If an outbound IRC or web request is made to the supplied IP address, then this confirms the existence of the C&C channel.
- all outbound DNS requiresmay be logged in a circular buffer (not shown). Once a C&C channel DNS name is identified, a search may be performed on all entries in the buffer for other source IP addresses that have requested the same DNS name. These source IP addresses are now highly suspect to be infected with the same bot or malware family that infected the virtual machine, even though these other IP addresses may not have been acknowledged as propagating an infection.
- the namemay be communicated to all other devices as well as a cloud server. This allows other distributed devices to detect attempts to connect to the same C&C channel.
- FIG. 5is a flowchart 500 of an exemplary method for detecting a C&C channel of a bot.
- the systeme.g., controller 125 and/or bot detector 200 determines if there is communication detected in the communication network 110 . The determination may be performed, in accordance with some embodiments, by the tap 120 , the bot detector 200 , and/or the controller 125 . If there is communication detected, then in step 510 , data within the communication may be scanned. In one embodiment, the data may be copied. For example, the network data from the network device 115 to the bot server 105 may be copied by the tap 120 . The network data is then sent from the tap 120 to the controller 125 for analysis. In an alternative embodiment, the data may be scanned directly by, for example, the bot detector 200 .
- a bot communication analysisis performed.
- the bot detector 200 or the controller 125may utilizes various modules (e.g., protocol fingerprint module 305 , heuristic module 320 , and analysis environment 340 ) to determine whether the copied network data contains a possible bot communication or may otherwise be potentially harmful to the network device 115 for which the copied network data may be intended. Subsequently, suspicious nodes can be flagged. If the controller 125 or bot detector 200 does not identify the copied network data as possibly containing a possible bot communication, the network data may be transmitted to the intended destination (e.g., network device 115 ).
- the intended destinatione.g., network device 115
- a fingerprint module 205 or 305may scans for a bot oriented command in an IRC channel including IRC channel establishment commands or messages.
- a port module 215may monitor the use of non-standard ports. During base-lining a list of standard ports is compiled. Communications not originating from a standard port may be considered non-standard or an anomaly. As such, associated nodes may be flagged (e.g., color coded) and tracked.
- a virtual machinemay be utilized to detect C&C communication channels.
- the C&C communication channel detectionmay occur in a replay virtual machine environment or in a direct entry virtual machine environment. Accordingly, a virtual machine is retrieved which is used to mimic the network device 115 . Intercepted or replayed network data obtained from the communication channel is transmitted to the virtual machine. The virtual machine response is then analyzed to determine if the virtual machine is infected.
- the analysis environment 340may wait for an outbound domain name system (DNS) request, which likely identifies the C&C channel.
- DNSdomain name system
- a pseudo-DNS server in the virtual machinecan respond to the request with an IP mapped to an internal-to-virtual machine-analysis pseudo-server. If the outbound IRC or web request is made to the supplied IP address, then this confirms a C&C channel.
- DNSdomain name system
- a recovery processmay be performed in step 525 .
- the associated devicesmay be flagged and/or proper users and administrators notified. For example, any nodes that are not associated with any infection propagation may be placed in a yellow category. Nodes in an IRC or P2P network where at least one of the nodes (e.g., in a chain of nodes) is observed propagating an infection may be placed in, for example, an orange category. Nodes that are observed to be actively propagating an infection may be placed in a red category. Any nodes that have not been categorized as yellow, orange, or red may be assigned to a green category.
- a routeri.e., switch
- all the network data from the bot server 105not only that which is transmitted to the network device 115 , may be intercepted.
- FIG. 6is a block diagram of the controller 125 , in accordance with one embodiment of the present invention.
- the controller 125comprises a processor 600 , a memory system 605 , a storage system 610 , an I/O interface 615 , and a communication network interface 620 which are all coupled to a system bus 625 .
- the processor 600is configured to execute executable instructions.
- the processor 600comprises circuitry or any one or more processors capable of processing the executable instructions.
- the memory system 605is any memory configured to store data. Some examples of the memory system 605 include storage devices, such as RAM or ROM.
- the storage system 610is any storage configured to retrieve and store data (e.g., a computer readable medium). Some examples of the storage system 610 are flash drives, hard drives, optical drives, and/or magnetic tape.
- the storage system 610can comprise a database or other data structure configured to hold and organize data (e.g., network data, copies of network data, buffered data.)
- the controller 125includes memory in the form of RAM and storage in the form of flash data.
- the memory system 605 and/or the storage system 610can comprise cache and buffers configured to retain network data or copies of network data.
- the input/output (I/O) interface 615is any device that can receive input and provide output to a user.
- the I/O interface 615can be, but is not limited to, a keyboard, a mouse, a touchscreen, a keypad, a biosensor, or floppy disk drive.
- the communication network interface 620can be coupled to any user device via the link 630 through link 635 .
- the communication network interface 620may support communication over a USB connection, a firewire connection, an Ethernet connection, a serial connection, a parallel connection, or an ATA connection.
- the communication network interface 620may also support wireless communication (e.g., 802.11a/b/g/n or wireless USB). It will be apparent to those skilled in the art that the communication network interface 620 can support many wired and wireless standards.
- links 630 and 635there may be any number of links.
- the other linksmay be used by the controller 125 to intercept data from one or more bot server 105 in parallel.
- the controller 125comprises multiple IP addresses that may be broadcast from different links. Network data may be intercepted from different infected devices 105 by different links.
- the above-described modulescan be comprised of instructions that are stored on storage media (e.g., computer readable media).
- the instructionscan be retrieved and executed by a processor (e.g., the processor 600 ).
- Some examples of instructionsinclude software, program code, and firmware.
- Some examples of storage mediacomprise memory devices and integrated circuits.
- the instructionsare operational when executed by the processor to direct the processor to operate in accordance with embodiments of the present invention. Those skilled in the art are familiar with instructions, processor(s), and storage media.
Landscapes
- Engineering & Computer Science (AREA)
- Computer Security & Cryptography (AREA)
- General Engineering & Computer Science (AREA)
- Computer Hardware Design (AREA)
- Theoretical Computer Science (AREA)
- Software Systems (AREA)
- Computing Systems (AREA)
- Health & Medical Sciences (AREA)
- Computer Networks & Wireless Communication (AREA)
- Signal Processing (AREA)
- Virology (AREA)
- Physics & Mathematics (AREA)
- General Physics & Mathematics (AREA)
- General Health & Medical Sciences (AREA)
- Data Exchanges In Wide-Area Networks (AREA)
Abstract
Description
Claims (31)
Priority Applications (2)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| US11/998,605US8561177B1 (en) | 2004-04-01 | 2007-11-30 | Systems and methods for detecting communication channels of bots |
| US14/052,632US9628498B1 (en) | 2004-04-01 | 2013-10-11 | System and method for bot detection |
Applications Claiming Priority (11)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| US55919804P | 2004-04-01 | 2004-04-01 | |
| US57991004P | 2004-06-14 | 2004-06-14 | |
| US57995304P | 2004-06-14 | 2004-06-14 | |
| US11/096,287US8528086B1 (en) | 2004-04-01 | 2005-03-31 | System and method of detecting computer worms |
| US11/152,286US8006305B2 (en) | 2004-06-14 | 2005-06-13 | Computer worm defense system and method |
| US11/151,812US8549638B2 (en) | 2004-06-14 | 2005-06-13 | System and method of containing computer worms |
| US11/409,355US8171553B2 (en) | 2004-04-01 | 2006-04-20 | Heuristic based capture with replay to virtual machine |
| US11/471,072US8584239B2 (en) | 2004-04-01 | 2006-06-19 | Virtual machine with dynamic data flow analysis |
| US11/494,990US8375444B2 (en) | 2006-04-20 | 2006-07-28 | Dynamic signature creation and enforcement |
| US86832306P | 2006-12-01 | 2006-12-01 | |
| US11/998,605US8561177B1 (en) | 2004-04-01 | 2007-11-30 | Systems and methods for detecting communication channels of bots |
Related Parent Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| US11/494,990Continuation-In-PartUS8375444B2 (en) | 2004-04-01 | 2006-07-28 | Dynamic signature creation and enforcement |
Related Child Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| US14/052,632ContinuationUS9628498B1 (en) | 2004-04-01 | 2013-10-11 | System and method for bot detection |
Publications (1)
| Publication Number | Publication Date |
|---|---|
| US8561177B1true US8561177B1 (en) | 2013-10-15 |
Family
ID=49321664
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| US11/998,605Active2028-02-11US8561177B1 (en) | 2004-04-01 | 2007-11-30 | Systems and methods for detecting communication channels of bots |
Country Status (1)
| Country | Link |
|---|---|
| US (1) | US8561177B1 (en) |
Cited By (240)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US20100281539A1 (en)* | 2009-04-29 | 2010-11-04 | Juniper Networks, Inc. | Detecting malicious network software agents |
| US20110035802A1 (en)* | 2009-08-07 | 2011-02-10 | Microsoft Corporation | Representing virtual object priority based on relationships |
| US20130247194A1 (en)* | 2012-03-16 | 2013-09-19 | Niraj K. Jha | Securing medical devices through wireless monitoring and anomaly detection |
| US20130305368A1 (en)* | 2012-05-09 | 2013-11-14 | SunStone Information Defense Inc. | Methods and apparatus for identifying and removing malicious applications |
| US8776229B1 (en) | 2004-04-01 | 2014-07-08 | Fireeye, Inc. | System and method of detecting malicious traffic while reducing false positives |
| US8793787B2 (en) | 2004-04-01 | 2014-07-29 | Fireeye, Inc. | Detecting malicious network content using virtual environment components |
| US8832829B2 (en) | 2009-09-30 | 2014-09-09 | Fireeye, Inc. | Network-based binary file extraction and analysis for malware detection |
| US8850571B2 (en) | 2008-11-03 | 2014-09-30 | Fireeye, Inc. | Systems and methods for detecting malicious network content |
| US8881282B1 (en) | 2004-04-01 | 2014-11-04 | Fireeye, Inc. | Systems and methods for malware attack detection and identification |
| US8898788B1 (en) | 2004-04-01 | 2014-11-25 | Fireeye, Inc. | Systems and methods for malware attack prevention |
| US20150007250A1 (en)* | 2013-06-27 | 2015-01-01 | The Mitre Corporation | Interception and Policy Application for Malicious Communications |
| US8984638B1 (en) | 2004-04-01 | 2015-03-17 | Fireeye, Inc. | System and method for analyzing suspicious network data |
| US8990944B1 (en) | 2013-02-23 | 2015-03-24 | Fireeye, Inc. | Systems and methods for automatically detecting backdoors |
| US8997219B2 (en) | 2008-11-03 | 2015-03-31 | Fireeye, Inc. | Systems and methods for detecting malicious PDF network content |
| US9009823B1 (en) | 2013-02-23 | 2015-04-14 | Fireeye, Inc. | Framework for efficient security coverage of mobile software applications installed on mobile devices |
| US9009822B1 (en) | 2013-02-23 | 2015-04-14 | Fireeye, Inc. | Framework for multi-phase analysis of mobile applications |
| US9027135B1 (en) | 2004-04-01 | 2015-05-05 | Fireeye, Inc. | Prospective client identification using malware attack detection |
| US9071638B1 (en) | 2004-04-01 | 2015-06-30 | Fireeye, Inc. | System and method for malware containment |
| US20150207812A1 (en)* | 2014-01-17 | 2015-07-23 | Gregory Thomas BACK | Systems and methods for identifying and performing an action in response to identified malicious network traffic |
| US9106694B2 (en) | 2004-04-01 | 2015-08-11 | Fireeye, Inc. | Electronic message analysis for malware detection |
| US9104867B1 (en) | 2013-03-13 | 2015-08-11 | Fireeye, Inc. | Malicious content analysis using simulated user interaction without user involvement |
| US9159035B1 (en) | 2013-02-23 | 2015-10-13 | Fireeye, Inc. | Framework for computer application analysis of sensitive information tracking |
| US9171160B2 (en) | 2013-09-30 | 2015-10-27 | Fireeye, Inc. | Dynamically adaptive framework and method for classifying malware using intelligent static, emulation, and dynamic analyses |
| US9176843B1 (en) | 2013-02-23 | 2015-11-03 | Fireeye, Inc. | Framework for efficient security coverage of mobile software applications |
| US9189627B1 (en) | 2013-11-21 | 2015-11-17 | Fireeye, Inc. | System, apparatus and method for conducting on-the-fly decryption of encrypted objects for malware detection |
| US9195829B1 (en) | 2013-02-23 | 2015-11-24 | Fireeye, Inc. | User interface with real-time visual playback along with synchronous textual analysis log display and event/time index for anomalous behavior detection in applications |
| US9223972B1 (en) | 2014-03-31 | 2015-12-29 | Fireeye, Inc. | Dynamically remote tuning of a malware content detection system |
| US9241010B1 (en) | 2014-03-20 | 2016-01-19 | Fireeye, Inc. | System and method for network behavior detection |
| US9251343B1 (en) | 2013-03-15 | 2016-02-02 | Fireeye, Inc. | Detecting bootkits resident on compromised computers |
| US9262635B2 (en) | 2014-02-05 | 2016-02-16 | Fireeye, Inc. | Detection efficacy of virtual machine-based analysis with application specific events |
| US9294501B2 (en) | 2013-09-30 | 2016-03-22 | Fireeye, Inc. | Fuzzy hash of behavioral results |
| US9300686B2 (en) | 2013-06-28 | 2016-03-29 | Fireeye, Inc. | System and method for detecting malicious links in electronic messages |
| US9306960B1 (en) | 2004-04-01 | 2016-04-05 | Fireeye, Inc. | Systems and methods for unauthorized activity defense |
| US9306974B1 (en) | 2013-12-26 | 2016-04-05 | Fireeye, Inc. | System, apparatus and method for automatically verifying exploits within suspect objects and highlighting the display information associated with the verified exploits |
| US9311479B1 (en) | 2013-03-14 | 2016-04-12 | Fireeye, Inc. | Correlation and consolidation of analytic data for holistic view of a malware attack |
| US9325735B1 (en) | 2013-10-31 | 2016-04-26 | Palo Alto Networks, Inc. | Selective sinkholing of malware domains by a security device via DNS poisoning |
| US9355247B1 (en) | 2013-03-13 | 2016-05-31 | Fireeye, Inc. | File extraction from memory dump for malicious content analysis |
| US9363280B1 (en) | 2014-08-22 | 2016-06-07 | Fireeye, Inc. | System and method of detecting delivery of malware using cross-customer data |
| US9367681B1 (en) | 2013-02-23 | 2016-06-14 | Fireeye, Inc. | Framework for efficient security coverage of mobile software applications using symbolic execution to reach regions of interest within an application |
| US9398028B1 (en) | 2014-06-26 | 2016-07-19 | Fireeye, Inc. | System, device and method for detecting a malicious attack based on communcations between remotely hosted virtual machines and malicious web servers |
| US9405903B1 (en)* | 2013-10-31 | 2016-08-02 | Palo Alto Networks, Inc. | Sinkholing bad network domains by registering the bad network domains on the internet |
| US9432389B1 (en) | 2014-03-31 | 2016-08-30 | Fireeye, Inc. | System, apparatus and method for detecting a malicious attack based on static analysis of a multi-flow object |
| US9430646B1 (en) | 2013-03-14 | 2016-08-30 | Fireeye, Inc. | Distributed systems and methods for automatically detecting unknown bots and botnets |
| US9438613B1 (en) | 2015-03-30 | 2016-09-06 | Fireeye, Inc. | Dynamic content activation for automated analysis of embedded objects |
| US9438623B1 (en) | 2014-06-06 | 2016-09-06 | Fireeye, Inc. | Computer exploit detection using heap spray pattern matching |
| US9483644B1 (en) | 2015-03-31 | 2016-11-01 | Fireeye, Inc. | Methods for detecting file altering malware in VM based analysis |
| US9495180B2 (en) | 2013-05-10 | 2016-11-15 | Fireeye, Inc. | Optimized resource allocation for virtual machines within a malware content detection system |
| US9497213B2 (en) | 2013-03-15 | 2016-11-15 | Fireeye, Inc. | System and method to manage sinkholes |
| US9519782B2 (en) | 2012-02-24 | 2016-12-13 | Fireeye, Inc. | Detecting malicious network content |
| US9536091B2 (en) | 2013-06-24 | 2017-01-03 | Fireeye, Inc. | System and method for detecting time-bomb malware |
| US20170026387A1 (en)* | 2015-07-21 | 2017-01-26 | Attivo Networks Inc. | Monitoring access of network darkspace |
| US9560072B1 (en) | 2013-10-31 | 2017-01-31 | Palo Alto Networks, Inc. | Discovering and selecting candidates for sinkholing of network domains |
| US9565202B1 (en) | 2013-03-13 | 2017-02-07 | Fireeye, Inc. | System and method for detecting exfiltration content |
| US9591015B1 (en) | 2014-03-28 | 2017-03-07 | Fireeye, Inc. | System and method for offloading packet processing and static analysis operations |
| US9594912B1 (en) | 2014-06-06 | 2017-03-14 | Fireeye, Inc. | Return-oriented programming detection |
| US9594904B1 (en) | 2015-04-23 | 2017-03-14 | Fireeye, Inc. | Detecting malware based on reflection |
| US9626509B1 (en) | 2013-03-13 | 2017-04-18 | Fireeye, Inc. | Malicious content analysis with multi-version application support within single operating environment |
| US9628507B2 (en) | 2013-09-30 | 2017-04-18 | Fireeye, Inc. | Advanced persistent threat (APT) detection center |
| US9628498B1 (en) | 2004-04-01 | 2017-04-18 | Fireeye, Inc. | System and method for bot detection |
| US9635039B1 (en) | 2013-05-13 | 2017-04-25 | Fireeye, Inc. | Classifying sets of malicious indicators for detecting command and control communications associated with malware |
| US9690936B1 (en) | 2013-09-30 | 2017-06-27 | Fireeye, Inc. | Multistage system and method for analyzing obfuscated content for malware |
| US9690933B1 (en) | 2014-12-22 | 2017-06-27 | Fireeye, Inc. | Framework for classifying an object as malicious with machine learning for deploying updated predictive models |
| US9690606B1 (en) | 2015-03-25 | 2017-06-27 | Fireeye, Inc. | Selective system call monitoring |
| US9736179B2 (en) | 2013-09-30 | 2017-08-15 | Fireeye, Inc. | System, apparatus and method for using malware analysis results to drive adaptive instrumentation of virtual machines to improve exploit detection |
| US9747446B1 (en) | 2013-12-26 | 2017-08-29 | Fireeye, Inc. | System and method for run-time object classification |
| US9773112B1 (en) | 2014-09-29 | 2017-09-26 | Fireeye, Inc. | Exploit detection of malware and malware families |
| RU2634211C1 (en)* | 2016-07-06 | 2017-10-24 | Общество с ограниченной ответственностью "Траст" | Method and system of protocols analysis of harmful programs interaction with control centers and detection of computer attacks |
| US9825976B1 (en) | 2015-09-30 | 2017-11-21 | Fireeye, Inc. | Detection and classification of exploit kits |
| US9824209B1 (en) | 2013-02-23 | 2017-11-21 | Fireeye, Inc. | Framework for efficient security coverage of mobile software applications that is usable to harden in the field code |
| US9824216B1 (en) | 2015-12-31 | 2017-11-21 | Fireeye, Inc. | Susceptible environment detection system |
| US9825989B1 (en) | 2015-09-30 | 2017-11-21 | Fireeye, Inc. | Cyber attack early warning system |
| US9838416B1 (en) | 2004-06-14 | 2017-12-05 | Fireeye, Inc. | System and method of detecting malicious content |
| US9838417B1 (en) | 2014-12-30 | 2017-12-05 | Fireeye, Inc. | Intelligent context aware user interaction for malware detection |
| EP3161712A4 (en)* | 2014-06-24 | 2018-01-24 | Fireeye Inc. | Malware detection and remediation for endpoint deviced |
| US9888016B1 (en) | 2013-06-28 | 2018-02-06 | Fireeye, Inc. | System and method for detecting phishing using password prediction |
| US9912644B2 (en) | 2014-08-05 | 2018-03-06 | Fireeye, Inc. | System and method to communicate sensitive information via one or more untrusted intermediate nodes with resilience to disconnected network topology |
| US9921978B1 (en) | 2013-11-08 | 2018-03-20 | Fireeye, Inc. | System and method for enhanced security of storage devices |
| US9973531B1 (en) | 2014-06-06 | 2018-05-15 | Fireeye, Inc. | Shellcode detection |
| CN108076038A (en)* | 2017-06-16 | 2018-05-25 | 哈尔滨安天科技股份有限公司 | A kind of C&C servers determination methods and system based on Service-Port |
| US10027689B1 (en) | 2014-09-29 | 2018-07-17 | Fireeye, Inc. | Interactive infection visualization for improved exploit detection and signature generation for malware and malware families |
| US10033747B1 (en) | 2015-09-29 | 2018-07-24 | Fireeye, Inc. | System and method for detecting interpreter-based exploit attacks |
| US10033759B1 (en) | 2015-09-28 | 2018-07-24 | Fireeye, Inc. | System and method of threat detection under hypervisor control |
| US10050998B1 (en) | 2015-12-30 | 2018-08-14 | Fireeye, Inc. | Malicious message analysis system |
| US10075455B2 (en) | 2014-12-26 | 2018-09-11 | Fireeye, Inc. | Zero-day rotating guest image profile |
| US10089461B1 (en) | 2013-09-30 | 2018-10-02 | Fireeye, Inc. | Page replacement code injection |
| US10097567B2 (en) | 2013-05-20 | 2018-10-09 | Nippon Telegraph And Telephone Corporation | Information processing apparatus and identifying method |
| US10104102B1 (en) | 2015-04-13 | 2018-10-16 | Fireeye, Inc. | Analytic-based security with learning adaptability |
| US10129270B2 (en)* | 2012-09-28 | 2018-11-13 | Level 3 Communications, Llc | Apparatus, system and method for identifying and mitigating malicious network threats |
| US10133866B1 (en) | 2015-12-30 | 2018-11-20 | Fireeye, Inc. | System and method for triggering analysis of an object for malware in response to modification of that object |
| US10133863B2 (en) | 2013-06-24 | 2018-11-20 | Fireeye, Inc. | Zero-day discovery system |
| US10148693B2 (en) | 2015-03-25 | 2018-12-04 | Fireeye, Inc. | Exploit detection system |
| US10169585B1 (en) | 2016-06-22 | 2019-01-01 | Fireeye, Inc. | System and methods for advanced malware detection through placement of transition events |
| US10176321B2 (en) | 2015-09-22 | 2019-01-08 | Fireeye, Inc. | Leveraging behavior-based rules for malware family classification |
| US10192052B1 (en) | 2013-09-30 | 2019-01-29 | Fireeye, Inc. | System, apparatus and method for classifying a file as malicious using static scanning |
| US10210329B1 (en) | 2015-09-30 | 2019-02-19 | Fireeye, Inc. | Method to detect application execution hijacking using memory protection |
| US10216927B1 (en) | 2015-06-30 | 2019-02-26 | Fireeye, Inc. | System and method for protecting memory pages associated with a process using a virtualization layer |
| WO2019048052A1 (en)* | 2017-09-08 | 2019-03-14 | Telefonaktiebolaget Lm Ericsson (Publ) | Re-establishing a connection between a user controller device and a wireless device |
| US10242185B1 (en) | 2014-03-21 | 2019-03-26 | Fireeye, Inc. | Dynamic guest image creation and rollback |
| US10284575B2 (en) | 2015-11-10 | 2019-05-07 | Fireeye, Inc. | Launcher for setting analysis environment variations for malware detection |
| US10341365B1 (en) | 2015-12-30 | 2019-07-02 | Fireeye, Inc. | Methods and system for hiding transition events for malware detection |
| US10395029B1 (en) | 2015-06-30 | 2019-08-27 | Fireeye, Inc. | Virtual system and method with threat protection |
| US10417031B2 (en) | 2015-03-31 | 2019-09-17 | Fireeye, Inc. | Selective virtualization for security threat detection |
| US10447728B1 (en) | 2015-12-10 | 2019-10-15 | Fireeye, Inc. | Technique for protecting guest processes using a layered virtualization architecture |
| US10454950B1 (en) | 2015-06-30 | 2019-10-22 | Fireeye, Inc. | Centralized aggregation technique for detecting lateral movement of stealthy cyber-attacks |
| US10462173B1 (en) | 2016-06-30 | 2019-10-29 | Fireeye, Inc. | Malware detection verification and enhancement by coordinating endpoint and malware detection systems |
| US10476906B1 (en) | 2016-03-25 | 2019-11-12 | Fireeye, Inc. | System and method for managing formation and modification of a cluster within a malware detection system |
| US10474813B1 (en) | 2015-03-31 | 2019-11-12 | Fireeye, Inc. | Code injection technique for remediation at an endpoint of a network |
| US10491627B1 (en) | 2016-09-29 | 2019-11-26 | Fireeye, Inc. | Advanced malware detection using similarity analysis |
| US10503904B1 (en) | 2017-06-29 | 2019-12-10 | Fireeye, Inc. | Ransomware detection and mitigation |
| US10515214B1 (en) | 2013-09-30 | 2019-12-24 | Fireeye, Inc. | System and method for classifying malware within content created during analysis of a specimen |
| US10523609B1 (en) | 2016-12-27 | 2019-12-31 | Fireeye, Inc. | Multi-vector malware detection and analysis |
| US10528726B1 (en) | 2014-12-29 | 2020-01-07 | Fireeye, Inc. | Microvisor-based malware detection appliance architecture |
| US10552610B1 (en) | 2016-12-22 | 2020-02-04 | Fireeye, Inc. | Adaptive virtual machine snapshot update framework for malware behavioral analysis |
| US10554507B1 (en) | 2017-03-30 | 2020-02-04 | Fireeye, Inc. | Multi-level control for enhanced resource and object evaluation management of malware detection system |
| US10565378B1 (en) | 2015-12-30 | 2020-02-18 | Fireeye, Inc. | Exploit of privilege detection framework |
| US10572665B2 (en) | 2012-12-28 | 2020-02-25 | Fireeye, Inc. | System and method to create a number of breakpoints in a virtual machine via virtual machine trapping events |
| US10581874B1 (en) | 2015-12-31 | 2020-03-03 | Fireeye, Inc. | Malware detection system with contextual analysis |
| US10581879B1 (en) | 2016-12-22 | 2020-03-03 | Fireeye, Inc. | Enhanced malware detection for generated objects |
| US10581880B2 (en) | 2016-09-19 | 2020-03-03 | Group-Ib Tds Ltd. | System and method for generating rules for attack detection feedback system |
| US10587647B1 (en) | 2016-11-22 | 2020-03-10 | Fireeye, Inc. | Technique for malware detection capability comparison of network security devices |
| US10592678B1 (en) | 2016-09-09 | 2020-03-17 | Fireeye, Inc. | Secure communications between peers using a verified virtual trusted platform module |
| US10601848B1 (en) | 2017-06-29 | 2020-03-24 | Fireeye, Inc. | Cyber-security system and method for weak indicator detection and correlation to generate strong indicators |
| US10601865B1 (en) | 2015-09-30 | 2020-03-24 | Fireeye, Inc. | Detection of credential spearphishing attacks using email analysis |
| US10601863B1 (en) | 2016-03-25 | 2020-03-24 | Fireeye, Inc. | System and method for managing sensor enrollment |
| US10642753B1 (en) | 2015-06-30 | 2020-05-05 | Fireeye, Inc. | System and method for protecting a software component running in virtual machine using a virtualization layer |
| US10671726B1 (en) | 2014-09-22 | 2020-06-02 | Fireeye Inc. | System and method for malware analysis using thread-level event monitoring |
| US10671721B1 (en) | 2016-03-25 | 2020-06-02 | Fireeye, Inc. | Timeout management services |
| US10701091B1 (en) | 2013-03-15 | 2020-06-30 | Fireeye, Inc. | System and method for verifying a cyberthreat |
| US10706149B1 (en) | 2015-09-30 | 2020-07-07 | Fireeye, Inc. | Detecting delayed activation malware using a primary controller and plural time controllers |
| US10715542B1 (en) | 2015-08-14 | 2020-07-14 | Fireeye, Inc. | Mobile application risk analysis |
| US10713358B2 (en) | 2013-03-15 | 2020-07-14 | Fireeye, Inc. | System and method to extract and utilize disassembly features to classify software intent |
| US10721251B2 (en) | 2016-08-03 | 2020-07-21 | Group Ib, Ltd | Method and system for detecting remote access during activity on the pages of a web resource |
| US10721271B2 (en) | 2016-12-29 | 2020-07-21 | Trust Ltd. | System and method for detecting phishing web pages |
| US10726127B1 (en) | 2015-06-30 | 2020-07-28 | Fireeye, Inc. | System and method for protecting a software component running in a virtual machine through virtual interrupts by the virtualization layer |
| US10740456B1 (en) | 2014-01-16 | 2020-08-11 | Fireeye, Inc. | Threat-aware architecture |
| US10747872B1 (en) | 2017-09-27 | 2020-08-18 | Fireeye, Inc. | System and method for preventing malware evasion |
| US10762352B2 (en) | 2018-01-17 | 2020-09-01 | Group Ib, Ltd | Method and system for the automatic identification of fuzzy copies of video content |
| US10778719B2 (en) | 2016-12-29 | 2020-09-15 | Trust Ltd. | System and method for gathering information to detect phishing activity |
| US10785255B1 (en) | 2016-03-25 | 2020-09-22 | Fireeye, Inc. | Cluster configuration within a scalable malware detection system |
| US10791138B1 (en) | 2017-03-30 | 2020-09-29 | Fireeye, Inc. | Subscription-based malware detection |
| US10795991B1 (en) | 2016-11-08 | 2020-10-06 | Fireeye, Inc. | Enterprise search |
| US10798112B2 (en) | 2017-03-30 | 2020-10-06 | Fireeye, Inc. | Attribute-controlled malware detection |
| US10805340B1 (en) | 2014-06-26 | 2020-10-13 | Fireeye, Inc. | Infection vector and malware tracking with an interactive user display |
| US10805346B2 (en) | 2017-10-01 | 2020-10-13 | Fireeye, Inc. | Phishing attack detection |
| US10812501B2 (en) | 2015-06-29 | 2020-10-20 | Palo Alto Networks, Inc. | DGA behavior detection |
| US10817606B1 (en) | 2015-09-30 | 2020-10-27 | Fireeye, Inc. | Detecting delayed activation malware using a run-time monitoring agent and time-dilation logic |
| US10826931B1 (en) | 2018-03-29 | 2020-11-03 | Fireeye, Inc. | System and method for predicting and mitigating cybersecurity system misconfigurations |
| US10846117B1 (en) | 2015-12-10 | 2020-11-24 | Fireeye, Inc. | Technique for establishing secure communication between host and guest processes of a virtualization architecture |
| US10855700B1 (en) | 2017-06-29 | 2020-12-01 | Fireeye, Inc. | Post-intrusion detection of cyber-attacks during lateral movement within networks |
| US10893059B1 (en) | 2016-03-31 | 2021-01-12 | Fireeye, Inc. | Verification and enhancement using detection systems located at the network periphery and endpoint devices |
| US10893068B1 (en) | 2017-06-30 | 2021-01-12 | Fireeye, Inc. | Ransomware file modification prevention technique |
| US10904286B1 (en) | 2017-03-24 | 2021-01-26 | Fireeye, Inc. | Detection of phishing attacks using similarity analysis |
| US10902119B1 (en) | 2017-03-30 | 2021-01-26 | Fireeye, Inc. | Data extraction system for malware analysis |
| US10958684B2 (en) | 2018-01-17 | 2021-03-23 | Group Ib, Ltd | Method and computer device for identifying malicious web resources |
| US10956477B1 (en) | 2018-03-30 | 2021-03-23 | Fireeye, Inc. | System and method for detecting malicious scripts through natural language processing modeling |
| CN112788043A (en)* | 2021-01-18 | 2021-05-11 | 广州锦行网络科技有限公司 | Honeypot system service self-adaption method and self-adaption service honeypot system |
| US11005860B1 (en) | 2017-12-28 | 2021-05-11 | Fireeye, Inc. | Method and system for efficient cybersecurity analysis of endpoint events |
| US11005779B2 (en) | 2018-02-13 | 2021-05-11 | Trust Ltd. | Method of and server for detecting associated web resources |
| US11003773B1 (en) | 2018-03-30 | 2021-05-11 | Fireeye, Inc. | System and method for automatically generating malware detection rule recommendations |
| US11075930B1 (en) | 2018-06-27 | 2021-07-27 | Fireeye, Inc. | System and method for detecting repetitive cybersecurity attacks constituting an email campaign |
| US11108809B2 (en) | 2017-10-27 | 2021-08-31 | Fireeye, Inc. | System and method for analyzing binary code for malware classification using artificial neural network techniques |
| US11113086B1 (en) | 2015-06-30 | 2021-09-07 | Fireeye, Inc. | Virtual system and method for securing external network connectivity |
| US11122061B2 (en) | 2018-01-17 | 2021-09-14 | Group IB TDS, Ltd | Method and server for determining malicious files in network traffic |
| US11151581B2 (en) | 2020-03-04 | 2021-10-19 | Group-Ib Global Private Limited | System and method for brand protection based on search results |
| US11153351B2 (en) | 2018-12-17 | 2021-10-19 | Trust Ltd. | Method and computing device for identifying suspicious users in message exchange systems |
| US11176251B1 (en) | 2018-12-21 | 2021-11-16 | Fireeye, Inc. | Determining malware via symbolic function hash analysis |
| US11182473B1 (en) | 2018-09-13 | 2021-11-23 | Fireeye Security Holdings Us Llc | System and method for mitigating cyberattacks against processor operability by a guest process |
| US11200080B1 (en) | 2015-12-11 | 2021-12-14 | Fireeye Security Holdings Us Llc | Late load technique for deploying a virtualization layer underneath a running operating system |
| US11228491B1 (en) | 2018-06-28 | 2022-01-18 | Fireeye Security Holdings Us Llc | System and method for distributed cluster configuration monitoring and management |
| US11240275B1 (en) | 2017-12-28 | 2022-02-01 | Fireeye Security Holdings Us Llc | Platform and method for performing cybersecurity analyses employing an intelligence hub with a modular architecture |
| US11244056B1 (en) | 2014-07-01 | 2022-02-08 | Fireeye Security Holdings Us Llc | Verification of trusted threat-aware visualization layer |
| US11250129B2 (en) | 2019-12-05 | 2022-02-15 | Group IB TDS, Ltd | Method and system for determining affiliation of software to software families |
| US11258806B1 (en) | 2019-06-24 | 2022-02-22 | Mandiant, Inc. | System and method for automatically associating cybersecurity intelligence to cyberthreat actors |
| US11271955B2 (en) | 2017-12-28 | 2022-03-08 | Fireeye Security Holdings Us Llc | Platform and method for retroactive reclassification employing a cybersecurity-based global data store |
| US11310238B1 (en) | 2019-03-26 | 2022-04-19 | FireEye Security Holdings, Inc. | System and method for retrieval and analysis of operational data from customer, cloud-hosted virtual resources |
| US11314859B1 (en) | 2018-06-27 | 2022-04-26 | FireEye Security Holdings, Inc. | Cyber-security system and method for detecting escalation of privileges within an access token |
| US11316900B1 (en) | 2018-06-29 | 2022-04-26 | FireEye Security Holdings Inc. | System and method for automatically prioritizing rules for cyber-threat detection and mitigation |
| US11356470B2 (en) | 2019-12-19 | 2022-06-07 | Group IB TDS, Ltd | Method and system for determining network vulnerabilities |
| US11368475B1 (en) | 2018-12-21 | 2022-06-21 | Fireeye Security Holdings Us Llc | System and method for scanning remote services to locate stored objects with malware |
| US11388072B2 (en)* | 2019-08-05 | 2022-07-12 | Extrahop Networks, Inc. | Correlating network traffic that crosses opaque endpoints |
| US11392700B1 (en) | 2019-06-28 | 2022-07-19 | Fireeye Security Holdings Us Llc | System and method for supporting cross-platform data verification |
| US11431744B2 (en) | 2018-02-09 | 2022-08-30 | Extrahop Networks, Inc. | Detection of denial of service attacks |
| US11431749B2 (en) | 2018-12-28 | 2022-08-30 | Trust Ltd. | Method and computing device for generating indication of malicious web resources |
| US11438247B2 (en) | 2019-08-05 | 2022-09-06 | Extrahop Networks, Inc. | Correlating network traffic that crosses opaque endpoints |
| US11436327B1 (en) | 2019-12-24 | 2022-09-06 | Fireeye Security Holdings Us Llc | System and method for circumventing evasive code for cyberthreat detection |
| US11451580B2 (en) | 2018-01-17 | 2022-09-20 | Trust Ltd. | Method and system of decentralized malware identification |
| US11463466B2 (en) | 2020-09-23 | 2022-10-04 | Extrahop Networks, Inc. | Monitoring encrypted network traffic |
| US11463465B2 (en) | 2019-09-04 | 2022-10-04 | Extrahop Networks, Inc. | Automatic determination of user roles and asset types based on network monitoring |
| US11463299B2 (en) | 2018-02-07 | 2022-10-04 | Extrahop Networks, Inc. | Ranking alerts based on network monitoring |
| US11470115B2 (en) | 2018-02-09 | 2022-10-11 | Attivo Networks, Inc. | Implementing decoys in a network environment |
| US11475090B2 (en) | 2020-07-15 | 2022-10-18 | Group-Ib Global Private Limited | Method and system for identifying clusters of affiliated web resources |
| US11496378B2 (en) | 2018-08-09 | 2022-11-08 | Extrahop Networks, Inc. | Correlating causes and effects associated with network activity |
| US11503044B2 (en) | 2018-01-17 | 2022-11-15 | Group IB TDS, Ltd | Method computing device for detecting malicious domain names in network traffic |
| US11522884B1 (en) | 2019-12-24 | 2022-12-06 | Fireeye Security Holdings Us Llc | Subscription and key management system |
| US11526608B2 (en) | 2019-12-05 | 2022-12-13 | Group IB TDS, Ltd | Method and system for determining affiliation of software to software families |
| US11546153B2 (en) | 2017-03-22 | 2023-01-03 | Extrahop Networks, Inc. | Managing session secrets for continuous packet capture systems |
| US11552986B1 (en) | 2015-12-31 | 2023-01-10 | Fireeye Security Holdings Us Llc | Cyber-security framework for application of virtual features |
| US11556640B1 (en) | 2019-06-27 | 2023-01-17 | Mandiant, Inc. | Systems and methods for automated cybersecurity analysis of extracted binary string sets |
| US11558401B1 (en) | 2018-03-30 | 2023-01-17 | Fireeye Security Holdings Us Llc | Multi-vector malware detection data sharing system for improved detection |
| US11558413B2 (en) | 2020-09-23 | 2023-01-17 | Extrahop Networks, Inc. | Monitoring encrypted network traffic |
| US11580218B2 (en) | 2019-05-20 | 2023-02-14 | Sentinel Labs Israel Ltd. | Systems and methods for executable code detection, automatic feature extraction and position independent code detection |
| US11579857B2 (en) | 2020-12-16 | 2023-02-14 | Sentinel Labs Israel Ltd. | Systems, methods and devices for device fingerprinting and automatic deployment of software in a computing network using a peer-to-peer approach |
| US11601444B1 (en) | 2018-12-31 | 2023-03-07 | Fireeye Security Holdings Us Llc | Automated system for triage of customer issues |
| US11616812B2 (en) | 2016-12-19 | 2023-03-28 | Attivo Networks Inc. | Deceiving attackers accessing active directory data |
| US11625485B2 (en) | 2014-08-11 | 2023-04-11 | Sentinel Labs Israel Ltd. | Method of malware detection and system thereof |
| US11637862B1 (en) | 2019-09-30 | 2023-04-25 | Mandiant, Inc. | System and method for surfacing cyber-security threats with a self-learning recommendation engine |
| US11636198B1 (en) | 2019-03-30 | 2023-04-25 | Fireeye Security Holdings Us Llc | System and method for cybersecurity analyzer update and concurrent management system |
| US11665207B2 (en) | 2017-10-25 | 2023-05-30 | Extrahop Networks, Inc. | Inline secret sharing |
| US11677786B1 (en) | 2019-03-29 | 2023-06-13 | Fireeye Security Holdings Us Llc | System and method for detecting and protecting against cybersecurity attacks on servers |
| US11695800B2 (en) | 2016-12-19 | 2023-07-04 | SentinelOne, Inc. | Deceiving attackers accessing network data |
| US11706233B2 (en) | 2019-05-28 | 2023-07-18 | Extrahop Networks, Inc. | Detecting injection attacks using passive network monitoring |
| US11716341B2 (en) | 2017-08-08 | 2023-08-01 | Sentinel Labs Israel Ltd. | Methods, systems, and devices for dynamically modeling and grouping endpoints for edge networking |
| US11729134B2 (en) | 2019-09-30 | 2023-08-15 | Palo Alto Networks, Inc. | In-line detection of algorithmically generated domains |
| US11743290B2 (en) | 2018-12-21 | 2023-08-29 | Fireeye Security Holdings Us Llc | System and method for detecting cyberattacks impersonating legitimate sources |
| US11755700B2 (en) | 2017-11-21 | 2023-09-12 | Group Ib, Ltd | Method for classifying user action sequence |
| US11763004B1 (en) | 2018-09-27 | 2023-09-19 | Fireeye Security Holdings Us Llc | System and method for bootkit detection |
| US11838300B1 (en) | 2019-12-24 | 2023-12-05 | Musarubra Us Llc | Run-time configurable cybersecurity system |
| US11843606B2 (en) | 2022-03-30 | 2023-12-12 | Extrahop Networks, Inc. | Detecting abnormal data access based on data similarity |
| US11847223B2 (en) | 2020-08-06 | 2023-12-19 | Group IB TDS, Ltd | Method and system for generating a list of indicators of compromise |
| US20240031406A1 (en)* | 2018-10-09 | 2024-01-25 | Penten Pty Ltd | Methods and systems for honeyfile creation, deployment and management |
| US11886585B1 (en) | 2019-09-27 | 2024-01-30 | Musarubra Us Llc | System and method for identifying and mitigating cyberattacks through malicious position-independent code execution |
| US11886591B2 (en) | 2014-08-11 | 2024-01-30 | Sentinel Labs Israel Ltd. | Method of remediating operations performed by a program and system thereof |
| US11899782B1 (en) | 2021-07-13 | 2024-02-13 | SentinelOne, Inc. | Preserving DLL hooks |
| US11916771B2 (en) | 2021-09-23 | 2024-02-27 | Extrahop Networks, Inc. | Combining passive network analysis and active probing |
| US11934498B2 (en) | 2019-02-27 | 2024-03-19 | Group Ib, Ltd | Method and system of user identification |
| US11947572B2 (en) | 2021-03-29 | 2024-04-02 | Group IB TDS, Ltd | Method and system for clustering executable files |
| US11979428B1 (en) | 2016-03-31 | 2024-05-07 | Musarubra Us Llc | Technique for verifying exploit/malware at malware detection appliance through correlation with endpoints |
| US11985147B2 (en) | 2021-06-01 | 2024-05-14 | Trust Ltd. | System and method for detecting a cyberattack |
| US20240250968A1 (en)* | 2023-01-19 | 2024-07-25 | Palo Alto Networks, Inc. | Detecting scanning and attacking uniform resource locators in network traffic |
| US12074887B1 (en) | 2018-12-21 | 2024-08-27 | Musarubra Us Llc | System and method for selectively processing content after identification and removal of malicious content |
| US12088606B2 (en) | 2021-06-10 | 2024-09-10 | F.A.C.C.T. Network Security Llc | System and method for detection of malicious network resources |
| US12107888B2 (en) | 2019-12-17 | 2024-10-01 | Extrahop Networks, Inc. | Automated preemptive polymorphic deception |
| US12135786B2 (en) | 2020-03-10 | 2024-11-05 | F.A.C.C.T. Network Security Llc | Method and system for identifying malware |
| US12200013B2 (en) | 2019-08-07 | 2025-01-14 | Musarubra Us Llc | System and method for detecting cyberattacks impersonating legitimate sources |
| US12225030B2 (en) | 2021-06-18 | 2025-02-11 | Extrahop Networks, Inc. | Identifying network entities based on beaconing activity |
| US12229259B2 (en) | 2020-02-21 | 2025-02-18 | F.A.C.C.T. Network Security Llc | Method and system for detecting malicious files in a non-isolated environment |
| US12282863B2 (en) | 2019-04-10 | 2025-04-22 | F.A.C.C.T. Antifraud Llc | Method and system of user identification by a sequence of opened user interface windows |
| US12309192B2 (en) | 2019-07-29 | 2025-05-20 | Extrahop Networks, Inc. | Modifying triage information based on network monitoring |
| US12417282B2 (en) | 2020-01-27 | 2025-09-16 | F.A.C.C.T. Network Security Llc | Method and system for detecting malicious infrastructure |
| US12445458B1 (en) | 2019-06-28 | 2025-10-14 | Google Llc | System and method for identifying malicious hosts prior to commencement of a cyber-attack |
Citations (131)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US4292580A (en) | 1978-11-30 | 1981-09-29 | Siemens Aktiengesellschaft | Circuit arrangement for attenuation of power oscillations in networks |
| US5175732A (en) | 1991-02-15 | 1992-12-29 | Standard Microsystems Corp. | Method and apparatus for controlling data communication operations within stations of a local-area network |
| US5440723A (en) | 1993-01-19 | 1995-08-08 | International Business Machines Corporation | Automatic immune system for computers and computer networks |
| US5657473A (en) | 1990-02-21 | 1997-08-12 | Arendee Limited | Method and apparatus for controlling access to and corruption of information in computer systems |
| US5978917A (en) | 1997-08-14 | 1999-11-02 | Symantec Corporation | Detection and elimination of macro viruses |
| US6269330B1 (en) | 1997-10-07 | 2001-07-31 | Attune Networks Ltd. | Fault location and performance testing of communication networks |
| US6298445B1 (en) | 1998-04-30 | 2001-10-02 | Netect, Ltd. | Computer security |
| US20010047326A1 (en) | 2000-03-14 | 2001-11-29 | Broadbent David F. | Interface system for a mortgage loan originator compliance engine |
| WO2002006928A2 (en) | 2000-07-14 | 2002-01-24 | Vcis, Inc. | Computer immune system and method for detecting unwanted code in a computer system |
| US20020018903A1 (en) | 2000-07-21 | 2002-02-14 | Tadashi Kokubo | Anti-thrombogenic material and manufacturing method therefor |
| US6357008B1 (en) | 1997-09-23 | 2002-03-12 | Symantec Corporation | Dynamic heuristic method for detecting computer viruses using decryption exploration and evaluation phases |
| WO2002023805A2 (en) | 2000-09-13 | 2002-03-21 | Karakoram Limited | Monitoring network activity |
| US20020038430A1 (en)* | 2000-09-13 | 2002-03-28 | Charles Edwards | System and method of data collection, processing, analysis, and annotation for monitoring cyber-threats and the notification thereof to subscribers |
| US20020091819A1 (en) | 2001-01-05 | 2002-07-11 | Daniel Melchione | System and method for configuring computer applications and devices using inheritance |
| US6424627B1 (en) | 1997-02-24 | 2002-07-23 | Metrobility Optical Systems | Full-duplex medium tap apparatus and system |
| US20020144156A1 (en) | 2001-01-31 | 2002-10-03 | Copeland John A. | Network port profiling |
| US20020162015A1 (en) | 2001-04-29 | 2002-10-31 | Zhaomiao Tang | Method and system for scanning and cleaning known and unknown computer viruses, recording medium and transmission medium therefor |
| US6487666B1 (en) | 1999-01-15 | 2002-11-26 | Cisco Technology, Inc. | Intrusion detection signature analysis using regular expressions and logical operators |
| US20020184528A1 (en)* | 2001-04-12 | 2002-12-05 | Shevenell Michael P. | Method and apparatus for security management via vicarious network devices |
| US6493756B1 (en) | 1999-10-28 | 2002-12-10 | Networks Associates, Inc. | System and method for dynamically sensing an asynchronous network event within a modular framework for network event processing |
| US20020188887A1 (en) | 2000-05-19 | 2002-12-12 | Self Repairing Computers, Inc. | Computer with switchable components |
| US20020194490A1 (en) | 2001-06-18 | 2002-12-19 | Avner Halperin | System and method of virus containment in computer networks |
| US6550012B1 (en) | 1998-12-11 | 2003-04-15 | Network Associates, Inc. | Active firewall system and methodology |
| US20030074578A1 (en) | 2001-10-16 | 2003-04-17 | Richard Ford | Computer virus containment |
| US20030084318A1 (en) | 2001-10-31 | 2003-05-01 | Schertz Richard L. | System and method of graphically correlating data for an intrusion protection system |
| US20030115483A1 (en) | 2001-12-04 | 2003-06-19 | Trend Micro Incorporated | Virus epidemic damage control system and method for network environment |
| US20030188190A1 (en) | 2002-03-26 | 2003-10-02 | Aaron Jeffrey A. | System and method of intrusion detection employing broad-scope monitoring |
| US20030200460A1 (en) | 2002-02-28 | 2003-10-23 | Ntt Docomo, Inc | Server apparatus, and information processing method |
| US20040019832A1 (en) | 2002-07-23 | 2004-01-29 | International Business Machines Corporation | Method and apparatus for the automatic determination of potentially worm-like behavior of a program |
| US20040047356A1 (en) | 2002-09-06 | 2004-03-11 | Bauer Blaine D. | Network traffic monitoring |
| US20040083408A1 (en) | 2002-10-24 | 2004-04-29 | Mark Spiegel | Heuristic detection and termination of fast spreading network worm attacks |
| US20040111531A1 (en) | 2002-12-06 | 2004-06-10 | Stuart Staniford | Method and system for reducing the rate of infection of a communications network by a software worm |
| US6775657B1 (en) | 1999-12-22 | 2004-08-10 | Cisco Technology, Inc. | Multilayered intrusion detection system and method |
| US20040165588A1 (en) | 2002-06-11 | 2004-08-26 | Pandya Ashish A. | Distributed network security system and a hardware processor therefor |
| US20040236963A1 (en) | 2003-05-20 | 2004-11-25 | International Business Machines Corporation | Applying blocking measures progressively to malicious network traffic |
| US20040243349A1 (en) | 2003-05-30 | 2004-12-02 | Segue Software, Inc. | Method of non-intrusive analysis of secure and non-secure web application traffic in real-time |
| US20040249911A1 (en) | 2003-03-31 | 2004-12-09 | Alkhatib Hasan S. | Secure virtual community network system |
| US6832367B1 (en) | 2000-03-06 | 2004-12-14 | International Business Machines Corporation | Method and system for recording and replaying the execution of distributed java programs |
| US20040268147A1 (en) | 2003-06-30 | 2004-12-30 | Wiederin Shawn E | Integrated security system |
| US20050033989A1 (en) | 2002-11-04 | 2005-02-10 | Poletto Massimiliano Antonio | Detection of scanning attacks |
| US20050033960A1 (en) | 2001-02-12 | 2005-02-10 | Jukka Vialen | Message authentication |
| US20050086523A1 (en) | 2003-10-15 | 2005-04-21 | Zimmer Vincent J. | Methods and apparatus to provide network traffic support and physical security support |
| US20050091513A1 (en) | 2003-10-28 | 2005-04-28 | Fujitsu Limited | Device, method and program for detecting unauthorized access |
| US6898632B2 (en) | 2003-03-31 | 2005-05-24 | Finisar Corporation | Network security tap for use with intrusion detection system |
| US20050114663A1 (en) | 2003-11-21 | 2005-05-26 | Finisar Corporation | Secure network access devices with data encryption |
| US20050125195A1 (en) | 2001-12-21 | 2005-06-09 | Juergen Brendel | Method, apparatus and sofware for network traffic management |
| US20050157662A1 (en) | 2004-01-20 | 2005-07-21 | Justin Bingham | Systems and methods for detecting a compromised network |
| US20050183143A1 (en) | 2004-02-13 | 2005-08-18 | Anderholm Eric J. | Methods and systems for monitoring user, application or device activity |
| US20050201297A1 (en) | 2003-12-12 | 2005-09-15 | Cyrus Peikari | Diagnosis of embedded, wireless mesh networks with real-time, flexible, location-specific signaling |
| US20050210533A1 (en) | 2001-11-30 | 2005-09-22 | Copeland John A | Packet Sampling Flow-Based Detection of Network Intrusions |
| US20050238005A1 (en) | 2004-04-21 | 2005-10-27 | Yi-Fen Chen | Method and apparatus for controlling traffic in a computer network |
| US20050265331A1 (en) | 2003-11-12 | 2005-12-01 | The Trustees Of Columbia University In The City Of New York | Apparatus method and medium for tracing the origin of network transmissions using n-gram distribution of data |
| US6981279B1 (en) | 2000-08-17 | 2005-12-27 | International Business Machines Corporation | Method and apparatus for replicating and analyzing worm programs |
| US20060015715A1 (en) | 2004-07-16 | 2006-01-19 | Eric Anderson | Automatically protecting network service from network attack |
| US20060021054A1 (en) | 2004-07-21 | 2006-01-26 | Microsoft Corporation | Containment of worms |
| US7007107B1 (en) | 2001-10-22 | 2006-02-28 | United Electronic Industries | Methods and apparatus for performing data acquisition and control |
| US20060075496A1 (en) | 2003-05-20 | 2006-04-06 | International Bussiness Machines Corporation | Applying blocking measures progressively to malicious network traffic |
| US20060095968A1 (en) | 2004-10-28 | 2006-05-04 | Cisco Technology, Inc. | Intrusion detection in a data center environment |
| US7043757B2 (en) | 2001-05-22 | 2006-05-09 | Mci, Llc | System and method for malicious code detection |
| US20060101517A1 (en) | 2004-10-28 | 2006-05-11 | Banzhof Carl E | Inventory management-based computer vulnerability resolution system |
| US20060101516A1 (en) | 2004-10-12 | 2006-05-11 | Sushanthan Sudaharan | Honeynet farms as an early warning system for production networks |
| US20060117385A1 (en) | 2004-11-30 | 2006-06-01 | Mester Michael L | Monitoring propagation protection within a network |
| US20060123477A1 (en) | 2004-12-06 | 2006-06-08 | Kollivakkam Raghavan | Method and apparatus for generating a network topology representation based on inspection of application messages at a network device |
| US7069316B1 (en)* | 2002-02-19 | 2006-06-27 | Mcafee, Inc. | Automated Internet Relay Chat malware monitoring and interception |
| US7080408B1 (en) | 2001-11-30 | 2006-07-18 | Mcafee, Inc. | Delayed-delivery quarantining of network communications having suspicious contents |
| US20060161987A1 (en) | 2004-11-10 | 2006-07-20 | Guy Levy-Yurista | Detecting and remedying unauthorized computer programs |
| US20060161983A1 (en) | 2005-01-20 | 2006-07-20 | Cothrell Scott A | Inline intrusion detection |
| US20060164199A1 (en) | 2005-01-26 | 2006-07-27 | Lockdown Networks, Inc. | Network appliance for securely quarantining a node on a network |
| US20060184632A1 (en) | 2005-02-15 | 2006-08-17 | Spam Cube, Inc. | Apparatus and method for analyzing and filtering email and for providing web related services |
| US20060191010A1 (en) | 2005-02-18 | 2006-08-24 | Pace University | System for intrusion detection and vulnerability assessment in a computer network using simulation and machine learning |
| US7100201B2 (en) | 2002-01-24 | 2006-08-29 | Arxceo Corporation | Undetectable firewall |
| US20060221956A1 (en) | 2005-03-31 | 2006-10-05 | Narayan Harsha L | Methods for performing packet classification via prefix pair bit vectors |
| US20070006313A1 (en) | 2004-09-17 | 2007-01-04 | Phillip Porras | Method and apparatus for combating malicious code |
| US20070006288A1 (en) | 2005-06-30 | 2007-01-04 | Microsoft Corporation | Controlling network access |
| US20070016951A1 (en) | 2005-07-13 | 2007-01-18 | Piccard Paul L | Systems and methods for identifying sources of malware |
| US20070033645A1 (en) | 2005-07-22 | 2007-02-08 | Alcatel | DNS based enforcement for confinement and detection of network malicious activities |
| US20070038943A1 (en) | 2005-08-15 | 2007-02-15 | Cisco Technology, Inc. | Interactive text communication system |
| US20070064689A1 (en) | 2003-09-19 | 2007-03-22 | Shin Yong M | Method of controlling communication between devices in a network and apparatus for the same |
| US20070094730A1 (en) | 2005-10-20 | 2007-04-26 | Cisco Technology, Inc. | Mechanism to correlate the presence of worms in a network |
| US7231667B2 (en) | 2003-05-29 | 2007-06-12 | Computer Associates Think, Inc. | System and method for computer virus detection utilizing heuristic analysis |
| US7240364B1 (en) | 2000-05-20 | 2007-07-03 | Ciena Corporation | Network device identity authentication |
| US7240368B1 (en) | 1999-04-14 | 2007-07-03 | Verizon Corporate Services Group Inc. | Intrusion and misuse deterrence system employing a virtual network |
| US20070192858A1 (en) | 2006-02-16 | 2007-08-16 | Infoexpress, Inc. | Peer based network access control |
| US20070192500A1 (en) | 2006-02-16 | 2007-08-16 | Infoexpress, Inc. | Network access control including dynamic policy enforcement point |
| US20070198275A1 (en) | 2002-06-27 | 2007-08-23 | Malden Matthew S | Method and system for processing intelligence information |
| US7287278B2 (en) | 2003-08-29 | 2007-10-23 | Trend Micro, Inc. | Innoculation of computing devices against a selected computer virus |
| US20070250930A1 (en) | 2004-04-01 | 2007-10-25 | Ashar Aziz | Virtual machine with dynamic data flow analysis |
| US20080005782A1 (en) | 2004-04-01 | 2008-01-03 | Ashar Aziz | Heuristic based capture with replay to virtual machine |
| GB2439806A (en) | 2006-06-30 | 2008-01-09 | Sophos Plc | Classifying software as malware using characteristics (or "genes") |
| US20080080518A1 (en) | 2006-09-29 | 2008-04-03 | Hoeflin David A | Method and apparatus for detecting compromised host computers |
| US7356736B2 (en) | 2001-09-25 | 2008-04-08 | Norman Asa | Simulated computer system for monitoring of software performance |
| US20080120722A1 (en) | 2006-11-17 | 2008-05-22 | Caleb Sima | Web application assessment based on intelligent generation of attack strings |
| US20080141376A1 (en) | 2006-10-24 | 2008-06-12 | Pc Tools Technology Pty Ltd. | Determining maliciousness of software |
| US7392542B2 (en) | 2003-08-29 | 2008-06-24 | Seagate Technology Llc | Restoration of data corrupted by viruses using pre-infected copy of data |
| US7418729B2 (en) | 2002-07-19 | 2008-08-26 | Symantec Corporation | Heuristic detection of malicious computer code by page tracking |
| US20080222729A1 (en) | 2007-03-05 | 2008-09-11 | Songqing Chen | Containment of Unknown and Polymorphic Fast Spreading Worms |
| US7428300B1 (en) | 2002-12-09 | 2008-09-23 | Verizon Laboratories Inc. | Diagnosing fault patterns in telecommunication networks |
| US7441272B2 (en) | 2004-06-09 | 2008-10-21 | Intel Corporation | Techniques for self-isolation of networked devices |
| US7448084B1 (en) | 2002-01-25 | 2008-11-04 | The Trustees Of Columbia University In The City Of New York | System and methods for detecting intrusions in a computer system by monitoring operating system registry accesses |
| US7458098B2 (en) | 2002-03-08 | 2008-11-25 | Secure Computing Corporation | Systems and methods for enhancing electronic communication security |
| US20080295172A1 (en) | 2007-05-22 | 2008-11-27 | Khushboo Bohacek | Method, system and computer-readable media for reducing undesired intrusion alarms in electronic communications systems and networks |
| US20080301810A1 (en) | 2007-06-04 | 2008-12-04 | Agilent Technologies, Inc. | Monitoring apparatus and method therefor |
| US7464407B2 (en) | 2002-08-20 | 2008-12-09 | Nec Corporation | Attack defending system and attack defending method |
| US7480773B1 (en) | 2005-05-02 | 2009-01-20 | Sprint Communications Company L.P. | Virtual machine use and optimization of hardware configurations |
| US20090031423A1 (en) | 2006-12-20 | 2009-01-29 | Peng Liu | Proactive worm containment (pwc) for enterprise networks |
| US7496960B1 (en)* | 2000-10-30 | 2009-02-24 | Trend Micro, Inc. | Tracking and reporting of computer virus information |
| US20090083369A1 (en) | 2004-10-04 | 2009-03-26 | Netmask (El-Mar) | Dynamic content conversion |
| US20090089879A1 (en) | 2007-09-28 | 2009-04-02 | Microsoft Corporation | Securing anti-virus software with virtualization |
| US20090094697A1 (en) | 2007-10-05 | 2009-04-09 | Google Inc. | Intrusive software management |
| US7530104B1 (en) | 2004-02-09 | 2009-05-05 | Symantec Corporation | Threat analysis |
| US7540025B2 (en) | 2004-11-18 | 2009-05-26 | Cisco Technology, Inc. | Mitigating network attacks using automatic signature generation |
| US20090271867A1 (en) | 2005-12-30 | 2009-10-29 | Peng Zhang | Virtual machine to detect malicious code |
| US20090300761A1 (en) | 2008-05-28 | 2009-12-03 | John Park | Intelligent Hashes for Centralized Malware Detection |
| US20090328221A1 (en) | 2008-06-30 | 2009-12-31 | Microsoft Corporation | Malware detention for suspected malware |
| US7644441B2 (en) | 2003-09-26 | 2010-01-05 | Cigital, Inc. | Methods for identifying malicious software |
| US7676841B2 (en)* | 2005-02-01 | 2010-03-09 | Fmr Llc | Network intrusion mitigation |
| US20100083376A1 (en) | 2008-09-26 | 2010-04-01 | Symantec Corporation | Method and apparatus for reducing false positive detection of malware |
| US7698548B2 (en)* | 2005-12-08 | 2010-04-13 | Microsoft Corporation | Communications traffic segregation for security purposes |
| US20100115621A1 (en) | 2008-11-03 | 2010-05-06 | Stuart Gresley Staniford | Systems and Methods for Detecting Malicious Network Content |
| US7779463B2 (en) | 2004-05-11 | 2010-08-17 | The Trustees Of Columbia University In The City Of New York | Systems and methods for correlating and distributing intrusion alert information among collaborating computer systems |
| US7784097B1 (en) | 2004-11-24 | 2010-08-24 | The Trustees Of Columbia University In The City Of New York | Systems and methods for correlating and distributing intrusion alert information among collaborating computer systems |
| US7849506B1 (en) | 2004-10-12 | 2010-12-07 | Avaya Inc. | Switching device, method, and computer program for efficient intrusion detection |
| US7904959B2 (en) | 2005-04-18 | 2011-03-08 | The Trustees Of Columbia University In The City Of New York | Systems and methods for detecting and inhibiting attacks using honeypots |
| US7908660B2 (en) | 2007-02-06 | 2011-03-15 | Microsoft Corporation | Dynamic risk management |
| US20110093951A1 (en) | 2004-06-14 | 2011-04-21 | NetForts, Inc. | Computer worm defense system and method |
| US20110099633A1 (en) | 2004-06-14 | 2011-04-28 | NetForts, Inc. | System and method of containing computer worms |
| US8028338B1 (en) | 2008-09-30 | 2011-09-27 | Symantec Corporation | Modeling goodware characteristics to reduce false positive malware signatures |
| US20110247072A1 (en) | 2008-11-03 | 2011-10-06 | Stuart Gresley Staniford | Systems and Methods for Detecting Malicious PDF Network Content |
| US8069484B2 (en) | 2007-01-25 | 2011-11-29 | Mandiant Corporation | System and method for determining data entropy to identify malware |
| US20110314546A1 (en) | 2004-04-01 | 2011-12-22 | Ashar Aziz | Electronic Message Analysis for Malware Detection |
| US8087086B1 (en) | 2008-06-30 | 2011-12-27 | Symantec Corporation | Method for mitigating false positive generation in antivirus software |
- 2007
- 2007-11-30USUS11/998,605patent/US8561177B1/enactiveActive
Patent Citations (150)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US4292580A (en) | 1978-11-30 | 1981-09-29 | Siemens Aktiengesellschaft | Circuit arrangement for attenuation of power oscillations in networks |
| US5657473A (en) | 1990-02-21 | 1997-08-12 | Arendee Limited | Method and apparatus for controlling access to and corruption of information in computer systems |
| US5175732A (en) | 1991-02-15 | 1992-12-29 | Standard Microsystems Corp. | Method and apparatus for controlling data communication operations within stations of a local-area network |
| US5440723A (en) | 1993-01-19 | 1995-08-08 | International Business Machines Corporation | Automatic immune system for computers and computer networks |
| US6424627B1 (en) | 1997-02-24 | 2002-07-23 | Metrobility Optical Systems | Full-duplex medium tap apparatus and system |
| US5978917A (en) | 1997-08-14 | 1999-11-02 | Symantec Corporation | Detection and elimination of macro viruses |
| US6357008B1 (en) | 1997-09-23 | 2002-03-12 | Symantec Corporation | Dynamic heuristic method for detecting computer viruses using decryption exploration and evaluation phases |
| US6269330B1 (en) | 1997-10-07 | 2001-07-31 | Attune Networks Ltd. | Fault location and performance testing of communication networks |
| US6298445B1 (en) | 1998-04-30 | 2001-10-02 | Netect, Ltd. | Computer security |
| US6550012B1 (en) | 1998-12-11 | 2003-04-15 | Network Associates, Inc. | Active firewall system and methodology |
| US6487666B1 (en) | 1999-01-15 | 2002-11-26 | Cisco Technology, Inc. | Intrusion detection signature analysis using regular expressions and logical operators |
| US7240368B1 (en) | 1999-04-14 | 2007-07-03 | Verizon Corporate Services Group Inc. | Intrusion and misuse deterrence system employing a virtual network |
| US6493756B1 (en) | 1999-10-28 | 2002-12-10 | Networks Associates, Inc. | System and method for dynamically sensing an asynchronous network event within a modular framework for network event processing |
| US6775657B1 (en) | 1999-12-22 | 2004-08-10 | Cisco Technology, Inc. | Multilayered intrusion detection system and method |
| US6832367B1 (en) | 2000-03-06 | 2004-12-14 | International Business Machines Corporation | Method and system for recording and replaying the execution of distributed java programs |
| US20010047326A1 (en) | 2000-03-14 | 2001-11-29 | Broadbent David F. | Interface system for a mortgage loan originator compliance engine |
| US20020188887A1 (en) | 2000-05-19 | 2002-12-12 | Self Repairing Computers, Inc. | Computer with switchable components |
| US7240364B1 (en) | 2000-05-20 | 2007-07-03 | Ciena Corporation | Network device identity authentication |
| WO2002006928A2 (en) | 2000-07-14 | 2002-01-24 | Vcis, Inc. | Computer immune system and method for detecting unwanted code in a computer system |
| US7093239B1 (en) | 2000-07-14 | 2006-08-15 | Internet Security Systems, Inc. | Computer immune system and method for detecting unwanted code in a computer system |
| US20020018903A1 (en) | 2000-07-21 | 2002-02-14 | Tadashi Kokubo | Anti-thrombogenic material and manufacturing method therefor |
| US6981279B1 (en) | 2000-08-17 | 2005-12-27 | International Business Machines Corporation | Method and apparatus for replicating and analyzing worm programs |
| WO2002023805A2 (en) | 2000-09-13 | 2002-03-21 | Karakoram Limited | Monitoring network activity |
| US20020038430A1 (en)* | 2000-09-13 | 2002-03-28 | Charles Edwards | System and method of data collection, processing, analysis, and annotation for monitoring cyber-threats and the notification thereof to subscribers |
| US7496960B1 (en)* | 2000-10-30 | 2009-02-24 | Trend Micro, Inc. | Tracking and reporting of computer virus information |
| US20020091819A1 (en) | 2001-01-05 | 2002-07-11 | Daniel Melchione | System and method for configuring computer applications and devices using inheritance |
| US20020144156A1 (en) | 2001-01-31 | 2002-10-03 | Copeland John A. | Network port profiling |
| US20050033960A1 (en) | 2001-02-12 | 2005-02-10 | Jukka Vialen | Message authentication |
| US20020184528A1 (en)* | 2001-04-12 | 2002-12-05 | Shevenell Michael P. | Method and apparatus for security management via vicarious network devices |
| US20020162015A1 (en) | 2001-04-29 | 2002-10-31 | Zhaomiao Tang | Method and system for scanning and cleaning known and unknown computer viruses, recording medium and transmission medium therefor |
| US7043757B2 (en) | 2001-05-22 | 2006-05-09 | Mci, Llc | System and method for malicious code detection |
| US20020194490A1 (en) | 2001-06-18 | 2002-12-19 | Avner Halperin | System and method of virus containment in computer networks |
| US7356736B2 (en) | 2001-09-25 | 2008-04-08 | Norman Asa | Simulated computer system for monitoring of software performance |
| US20030074578A1 (en) | 2001-10-16 | 2003-04-17 | Richard Ford | Computer virus containment |
| US7007107B1 (en) | 2001-10-22 | 2006-02-28 | United Electronic Industries | Methods and apparatus for performing data acquisition and control |
| US20030084318A1 (en) | 2001-10-31 | 2003-05-01 | Schertz Richard L. | System and method of graphically correlating data for an intrusion protection system |
| US7080408B1 (en) | 2001-11-30 | 2006-07-18 | Mcafee, Inc. | Delayed-delivery quarantining of network communications having suspicious contents |
| US20050210533A1 (en) | 2001-11-30 | 2005-09-22 | Copeland John A | Packet Sampling Flow-Based Detection of Network Intrusions |
| US20030115483A1 (en) | 2001-12-04 | 2003-06-19 | Trend Micro Incorporated | Virus epidemic damage control system and method for network environment |
| US20050125195A1 (en) | 2001-12-21 | 2005-06-09 | Juergen Brendel | Method, apparatus and sofware for network traffic management |
| US7100201B2 (en) | 2002-01-24 | 2006-08-29 | Arxceo Corporation | Undetectable firewall |
| US7448084B1 (en) | 2002-01-25 | 2008-11-04 | The Trustees Of Columbia University In The City Of New York | System and methods for detecting intrusions in a computer system by monitoring operating system registry accesses |
| US20090083855A1 (en) | 2002-01-25 | 2009-03-26 | Frank Apap | System and methods for detecting intrusions in a computer system by monitoring operating system registry accesses |
| US7069316B1 (en)* | 2002-02-19 | 2006-06-27 | Mcafee, Inc. | Automated Internet Relay Chat malware monitoring and interception |
| US20030200460A1 (en) | 2002-02-28 | 2003-10-23 | Ntt Docomo, Inc | Server apparatus, and information processing method |
| US7458098B2 (en) | 2002-03-08 | 2008-11-25 | Secure Computing Corporation | Systems and methods for enhancing electronic communication security |
| US20030188190A1 (en) | 2002-03-26 | 2003-10-02 | Aaron Jeffrey A. | System and method of intrusion detection employing broad-scope monitoring |
| US20040165588A1 (en) | 2002-06-11 | 2004-08-26 | Pandya Ashish A. | Distributed network security system and a hardware processor therefor |
| US20070198275A1 (en) | 2002-06-27 | 2007-08-23 | Malden Matthew S | Method and system for processing intelligence information |
| US7418729B2 (en) | 2002-07-19 | 2008-08-26 | Symantec Corporation | Heuristic detection of malicious computer code by page tracking |
| US20040019832A1 (en) | 2002-07-23 | 2004-01-29 | International Business Machines Corporation | Method and apparatus for the automatic determination of potentially worm-like behavior of a program |
| US7996905B2 (en) | 2002-07-23 | 2011-08-09 | Trend Micro Incorporated | Method and apparatus for the automatic determination of potentially worm-like behavior of a program |
| US7487543B2 (en) | 2002-07-23 | 2009-02-03 | International Business Machines Corporation | Method and apparatus for the automatic determination of potentially worm-like behavior of a program |
| US7464407B2 (en) | 2002-08-20 | 2008-12-09 | Nec Corporation | Attack defending system and attack defending method |
| US20040047356A1 (en) | 2002-09-06 | 2004-03-11 | Bauer Blaine D. | Network traffic monitoring |
| US20040083408A1 (en) | 2002-10-24 | 2004-04-29 | Mark Spiegel | Heuristic detection and termination of fast spreading network worm attacks |
| US7159149B2 (en) | 2002-10-24 | 2007-01-02 | Symantec Corporation | Heuristic detection and termination of fast spreading network worm attacks |
| US20050033989A1 (en) | 2002-11-04 | 2005-02-10 | Poletto Massimiliano Antonio | Detection of scanning attacks |
| US20040111531A1 (en) | 2002-12-06 | 2004-06-10 | Stuart Staniford | Method and system for reducing the rate of infection of a communications network by a software worm |
| US7428300B1 (en) | 2002-12-09 | 2008-09-23 | Verizon Laboratories Inc. | Diagnosing fault patterns in telecommunication networks |
| US6898632B2 (en) | 2003-03-31 | 2005-05-24 | Finisar Corporation | Network security tap for use with intrusion detection system |
| US20040249911A1 (en) | 2003-03-31 | 2004-12-09 | Alkhatib Hasan S. | Secure virtual community network system |
| US20040236963A1 (en) | 2003-05-20 | 2004-11-25 | International Business Machines Corporation | Applying blocking measures progressively to malicious network traffic |
| US20060075496A1 (en) | 2003-05-20 | 2006-04-06 | International Bussiness Machines Corporation | Applying blocking measures progressively to malicious network traffic |
| US7707633B2 (en) | 2003-05-20 | 2010-04-27 | International Business Machines Corporation | Applying blocking measures progressively to malicious network traffic |
| US7464404B2 (en) | 2003-05-20 | 2008-12-09 | International Business Machines Corporation | Method of responding to a truncated secure session attack |
| US20080072326A1 (en) | 2003-05-20 | 2008-03-20 | Danford Robert W | Applying blocking measures progressively to malicious network traffic |
| US7308716B2 (en) | 2003-05-20 | 2007-12-11 | International Business Machines Corporation | Applying blocking measures progressively to malicious network traffic |
| US7231667B2 (en) | 2003-05-29 | 2007-06-12 | Computer Associates Think, Inc. | System and method for computer virus detection utilizing heuristic analysis |
| US20040243349A1 (en) | 2003-05-30 | 2004-12-02 | Segue Software, Inc. | Method of non-intrusive analysis of secure and non-secure web application traffic in real-time |
| US20040268147A1 (en) | 2003-06-30 | 2004-12-30 | Wiederin Shawn E | Integrated security system |
| US7565550B2 (en) | 2003-08-29 | 2009-07-21 | Trend Micro, Inc. | Automatic registration of a virus/worm monitor in a distributed network |
| US7287278B2 (en) | 2003-08-29 | 2007-10-23 | Trend Micro, Inc. | Innoculation of computing devices against a selected computer virus |
| US7386888B2 (en) | 2003-08-29 | 2008-06-10 | Trend Micro, Inc. | Network isolation techniques suitable for virus protection |
| US7392542B2 (en) | 2003-08-29 | 2008-06-24 | Seagate Technology Llc | Restoration of data corrupted by viruses using pre-infected copy of data |
| US7523493B2 (en) | 2003-08-29 | 2009-04-21 | Trend Micro Incorporated | Virus monitor and methods of use thereof |
| US20070064689A1 (en) | 2003-09-19 | 2007-03-22 | Shin Yong M | Method of controlling communication between devices in a network and apparatus for the same |
| US7644441B2 (en) | 2003-09-26 | 2010-01-05 | Cigital, Inc. | Methods for identifying malicious software |
| US7496961B2 (en) | 2003-10-15 | 2009-02-24 | Intel Corporation | Methods and apparatus to provide network traffic support and physical security support |
| US20050086523A1 (en) | 2003-10-15 | 2005-04-21 | Zimmer Vincent J. | Methods and apparatus to provide network traffic support and physical security support |
| US20050091513A1 (en) | 2003-10-28 | 2005-04-28 | Fujitsu Limited | Device, method and program for detecting unauthorized access |
| US20050265331A1 (en) | 2003-11-12 | 2005-12-01 | The Trustees Of Columbia University In The City Of New York | Apparatus method and medium for tracing the origin of network transmissions using n-gram distribution of data |
| US20100054278A1 (en) | 2003-11-12 | 2010-03-04 | Stolfo Salvatore J | Apparatus method and medium for detecting payload anomaly using n-gram distribution of normal data |
| US7639714B2 (en) | 2003-11-12 | 2009-12-29 | The Trustees Of Columbia University In The City Of New York | Apparatus method and medium for detecting payload anomaly using n-gram distribution of normal data |
| US20050114663A1 (en) | 2003-11-21 | 2005-05-26 | Finisar Corporation | Secure network access devices with data encryption |
| US20050201297A1 (en) | 2003-12-12 | 2005-09-15 | Cyrus Peikari | Diagnosis of embedded, wireless mesh networks with real-time, flexible, location-specific signaling |
| US20050157662A1 (en) | 2004-01-20 | 2005-07-21 | Justin Bingham | Systems and methods for detecting a compromised network |
| US7530104B1 (en) | 2004-02-09 | 2009-05-05 | Symantec Corporation | Threat analysis |
| US20050183143A1 (en) | 2004-02-13 | 2005-08-18 | Anderholm Eric J. | Methods and systems for monitoring user, application or device activity |
| US20070250930A1 (en) | 2004-04-01 | 2007-10-25 | Ashar Aziz | Virtual machine with dynamic data flow analysis |
| US20110314546A1 (en) | 2004-04-01 | 2011-12-22 | Ashar Aziz | Electronic Message Analysis for Malware Detection |
| US20080005782A1 (en) | 2004-04-01 | 2008-01-03 | Ashar Aziz | Heuristic based capture with replay to virtual machine |
| US20050238005A1 (en) | 2004-04-21 | 2005-10-27 | Yi-Fen Chen | Method and apparatus for controlling traffic in a computer network |
| US7779463B2 (en) | 2004-05-11 | 2010-08-17 | The Trustees Of Columbia University In The City Of New York | Systems and methods for correlating and distributing intrusion alert information among collaborating computer systems |
| US20100281541A1 (en) | 2004-05-11 | 2010-11-04 | The Trustees Of Columbia University In The City Of New York | Systems and Methods for Correlating and Distributing Intrusion Alert Information Among Collaborating Computer Systems |
| US7441272B2 (en) | 2004-06-09 | 2008-10-21 | Intel Corporation | Techniques for self-isolation of networked devices |
| US20110099633A1 (en) | 2004-06-14 | 2011-04-28 | NetForts, Inc. | System and method of containing computer worms |
| US20110093951A1 (en) | 2004-06-14 | 2011-04-21 | NetForts, Inc. | Computer worm defense system and method |
| US20060015715A1 (en) | 2004-07-16 | 2006-01-19 | Eric Anderson | Automatically protecting network service from network attack |
| US7603715B2 (en) | 2004-07-21 | 2009-10-13 | Microsoft Corporation | Containment of worms |
| US20060021054A1 (en) | 2004-07-21 | 2006-01-26 | Microsoft Corporation | Containment of worms |
| US20070006313A1 (en) | 2004-09-17 | 2007-01-04 | Phillip Porras | Method and apparatus for combating malicious code |
| US20090083369A1 (en) | 2004-10-04 | 2009-03-26 | Netmask (El-Mar) | Dynamic content conversion |
| US20060101516A1 (en) | 2004-10-12 | 2006-05-11 | Sushanthan Sudaharan | Honeynet farms as an early warning system for production networks |
| US7849506B1 (en) | 2004-10-12 | 2010-12-07 | Avaya Inc. | Switching device, method, and computer program for efficient intrusion detection |
| US20060101517A1 (en) | 2004-10-28 | 2006-05-11 | Banzhof Carl E | Inventory management-based computer vulnerability resolution system |
| US20060095968A1 (en) | 2004-10-28 | 2006-05-04 | Cisco Technology, Inc. | Intrusion detection in a data center environment |
| US20060161987A1 (en) | 2004-11-10 | 2006-07-20 | Guy Levy-Yurista | Detecting and remedying unauthorized computer programs |
| US7540025B2 (en) | 2004-11-18 | 2009-05-26 | Cisco Technology, Inc. | Mitigating network attacks using automatic signature generation |
| US7784097B1 (en) | 2004-11-24 | 2010-08-24 | The Trustees Of Columbia University In The City Of New York | Systems and methods for correlating and distributing intrusion alert information among collaborating computer systems |
| US20100281542A1 (en) | 2004-11-24 | 2010-11-04 | The Trustees Of Columbia University In The City Of New York | Systems and Methods for Correlating and Distributing Intrusion Alert Information Among Collaborating Computer Systems |
| US20060117385A1 (en) | 2004-11-30 | 2006-06-01 | Mester Michael L | Monitoring propagation protection within a network |
| US20060123477A1 (en) | 2004-12-06 | 2006-06-08 | Kollivakkam Raghavan | Method and apparatus for generating a network topology representation based on inspection of application messages at a network device |
| US7996556B2 (en) | 2004-12-06 | 2011-08-09 | Cisco Technology, Inc. | Method and apparatus for generating a network topology representation based on inspection of application messages at a network device |
| US20060161983A1 (en) | 2005-01-20 | 2006-07-20 | Cothrell Scott A | Inline intrusion detection |
| US20060164199A1 (en) | 2005-01-26 | 2006-07-27 | Lockdown Networks, Inc. | Network appliance for securely quarantining a node on a network |
| US7676841B2 (en)* | 2005-02-01 | 2010-03-09 | Fmr Llc | Network intrusion mitigation |
| US20060184632A1 (en) | 2005-02-15 | 2006-08-17 | Spam Cube, Inc. | Apparatus and method for analyzing and filtering email and for providing web related services |
| US20060191010A1 (en) | 2005-02-18 | 2006-08-24 | Pace University | System for intrusion detection and vulnerability assessment in a computer network using simulation and machine learning |
| US20060221956A1 (en) | 2005-03-31 | 2006-10-05 | Narayan Harsha L | Methods for performing packet classification via prefix pair bit vectors |
| US7904959B2 (en) | 2005-04-18 | 2011-03-08 | The Trustees Of Columbia University In The City Of New York | Systems and methods for detecting and inhibiting attacks using honeypots |
| US7480773B1 (en) | 2005-05-02 | 2009-01-20 | Sprint Communications Company L.P. | Virtual machine use and optimization of hardware configurations |
| US20070006288A1 (en) | 2005-06-30 | 2007-01-04 | Microsoft Corporation | Controlling network access |
| US20070016951A1 (en) | 2005-07-13 | 2007-01-18 | Piccard Paul L | Systems and methods for identifying sources of malware |
| US20070033645A1 (en) | 2005-07-22 | 2007-02-08 | Alcatel | DNS based enforcement for confinement and detection of network malicious activities |
| US20070038943A1 (en) | 2005-08-15 | 2007-02-15 | Cisco Technology, Inc. | Interactive text communication system |
| US20070094730A1 (en) | 2005-10-20 | 2007-04-26 | Cisco Technology, Inc. | Mechanism to correlate the presence of worms in a network |
| US7698548B2 (en)* | 2005-12-08 | 2010-04-13 | Microsoft Corporation | Communications traffic segregation for security purposes |
| US20090271867A1 (en) | 2005-12-30 | 2009-10-29 | Peng Zhang | Virtual machine to detect malicious code |
| US20070192858A1 (en) | 2006-02-16 | 2007-08-16 | Infoexpress, Inc. | Peer based network access control |
| US20070192500A1 (en) | 2006-02-16 | 2007-08-16 | Infoexpress, Inc. | Network access control including dynamic policy enforcement point |
| GB2439806A (en) | 2006-06-30 | 2008-01-09 | Sophos Plc | Classifying software as malware using characteristics (or "genes") |
| US20080080518A1 (en) | 2006-09-29 | 2008-04-03 | Hoeflin David A | Method and apparatus for detecting compromised host computers |
| US20080141376A1 (en) | 2006-10-24 | 2008-06-12 | Pc Tools Technology Pty Ltd. | Determining maliciousness of software |
| US20080120722A1 (en) | 2006-11-17 | 2008-05-22 | Caleb Sima | Web application assessment based on intelligent generation of attack strings |
| US20090031423A1 (en) | 2006-12-20 | 2009-01-29 | Peng Liu | Proactive worm containment (pwc) for enterprise networks |
| US8069484B2 (en) | 2007-01-25 | 2011-11-29 | Mandiant Corporation | System and method for determining data entropy to identify malware |
| US7908660B2 (en) | 2007-02-06 | 2011-03-15 | Microsoft Corporation | Dynamic risk management |
| US20080222729A1 (en) | 2007-03-05 | 2008-09-11 | Songqing Chen | Containment of Unknown and Polymorphic Fast Spreading Worms |
| US20080295172A1 (en) | 2007-05-22 | 2008-11-27 | Khushboo Bohacek | Method, system and computer-readable media for reducing undesired intrusion alarms in electronic communications systems and networks |
| US20080301810A1 (en) | 2007-06-04 | 2008-12-04 | Agilent Technologies, Inc. | Monitoring apparatus and method therefor |
| US20090089879A1 (en) | 2007-09-28 | 2009-04-02 | Microsoft Corporation | Securing anti-virus software with virtualization |
| US20090094697A1 (en) | 2007-10-05 | 2009-04-09 | Google Inc. | Intrusive software management |
| US20090300761A1 (en) | 2008-05-28 | 2009-12-03 | John Park | Intelligent Hashes for Centralized Malware Detection |
| US20090328221A1 (en) | 2008-06-30 | 2009-12-31 | Microsoft Corporation | Malware detention for suspected malware |
| US8087086B1 (en) | 2008-06-30 | 2011-12-27 | Symantec Corporation | Method for mitigating false positive generation in antivirus software |
| US20100083376A1 (en) | 2008-09-26 | 2010-04-01 | Symantec Corporation | Method and apparatus for reducing false positive detection of malware |
| US8028338B1 (en) | 2008-09-30 | 2011-09-27 | Symantec Corporation | Modeling goodware characteristics to reduce false positive malware signatures |
| US20100115621A1 (en) | 2008-11-03 | 2010-05-06 | Stuart Gresley Staniford | Systems and Methods for Detecting Malicious Network Content |
| US20110247072A1 (en) | 2008-11-03 | 2011-10-06 | Stuart Gresley Staniford | Systems and Methods for Detecting Malicious PDF Network Content |
Non-Patent Citations (26)
| Title |
|---|
| "Packet", Microsoft Computer Dictionary, Microsoft Press, Mar. 2002, 1 pg. |
| Advisory Action mailed Jul. 26, 2011; Final-Office Action mailed Aug. 23, 2011; and Notices of Allowance mailed Dec. 15, 2011 and Feb. 7, 2012 in U.S. Appl. No. 11/409,355, filed Apr. 20, 2006. |
| AltaVista Advanced Search Results. "attack vector identifier". http://www.altavista.com/web/results?itag=ody&pg=aq&aqmode=s&aqa=attack+vector+ide . . . Accessed on Sep. 15, 2009. |
| AltaVista Advanced Search Results. "Event Orchestrator". http://www.altavista.com/web/results?itag=ody&pg=aq&aqmode=s&aqa=Event+Orchestrator . . . Accessed on Sep. 3, 2009. |
| Chaudet, C. et al. "Optimal Positioning of Active and Passive Monitoring Devices," International Conference on Emerging Networking Experiments and Technologies, Proceedings of the 2005 ACM Conference on Emerging Network Experiment and Technology, Oct. 2005, pp. 71-82, CoNEXT '05, Toulousse, France. |
| Costa, M. et al. "Vigilante: End-to-End Containment of Internet Worms," SOSP '05, Oct. 23-26, 2005, Association for Computing Machinery, Inc., Brighton U.K. |
| Crandall, J.R. et al., "Minos:Control Data Attack Prevention Orthognal to Memory Model," 37th International Symposium on Microarchitecture, Dec. 2004, Portland, Oregon. |
| Final-Office Action mailed Aug. 19, 2011 in U.S. Appl. No. 11/471,072, filed Jun. 19, 2006. |
| Final-Office Action mailed Aug. 26, 2011 and Advisory Action mailed Nov. 9, 2011 in U.S. Appl. No. 12/,263,971, filed Nov. 3, 2008. |
| Final-Office Action mailed Aug. 29, 2011 in U.S. Appl. No. 11/151,812, filed Jun. 13, 2005. |
| IEEE Xplore Digital Library Search results for "detection of unknown computer worms". http://ieeexplore.ieee.org/search/searchresult.jsp?SortField=Score&SortOrder=desc&ResultC . . . Accessed on Aug. 28, 2009. |
| Kim, H. et al., "Autograph: Toward Automated, Distributed Worm Signature Detection," Proceedings of the 13th Usenix Security Symposium (Security 2004), Aug. 2004, pp. 271-286, San Diego. |
| Kreibich, C. et al., "Honeycomb-Creating Intrusion Detection Signatures Using Honeypots," 2nd Workshop on Hot Topics in Networks (HotNets-11), 2003, Boston, USA. |
| Kristoff, J. "Botnets, Detection and Mitigation: DNS-Based Techniques," NU Security Day 2005, 23 pages. |
| Margolis, P.E., Random House Webster's "Computer & Internet Dictionary 3rd Edition," ISBN 0375703519, Dec. 1998. |
| Moore, D. et al., "Internet Quarantine: Requirements for Containing Self-Propagating Code", INFOCOM, Mar. 30-Apr. 3, 2003, vol. 3, pp. 1901-1910. |
| Newsome, J. et al., "Dynamic Taint Analysis for Automatic Detection, Analysis, and Signature Generation of Exploits on Commodity Software," In Proceedings of the 12th Annual Network and Distributed System Security, Symposium (NDSS '05), Feb. 2005. |
| Newsome, J. et al., "Polygraph: Automatically Generating Signatures for Polymorphic Worms," In Proceedings of the IEEE Symposium on Security and Privacy, May 2005. |
| Nojiri, D. et al., "Cooperative Response Strategies for Large Scale Attack Mitigation", DARPA Information Survivability Conference and Exposition, Apr. 22-24, 2003, vol. 1, pp. 293-302. |
| Non-Final Office Action mailed Dec. 20, 2011 in U.S. Appl. No. 11/717,408, filed Mar. 12, 2007. |
| Non-Final Office Action mailed Jan. 31, 2012 in U.S. Appl. No. 11/709,570, filed Feb. 21, 2007. |
| Notice of Allowance mailed Mar. 23, 2012 in U.S. Appl. No. 11/998,750, filed Nov. 30, 2007. |
| Silicon Defense, "Worm Containment in the Internal Network", Mar. 2003, pp. 1-25. |
| Singh, S. et al., "Automated Worm Fingerprinting," Proceedings of the ACM/USENIX Symposium on Operating System Design and Implementation, Dec. 2004, San Francisco, California. |
| Whyte et al. "DNS-Based Detection of Scannin Works in an Enterprise Network," Proceedings of the 12th Annual Network and Distributed System Security Symposium, Feb. 2005. 15 pages. |
| Williamson, Matthew M., "Throttling Viruses: Restricting Propagation to Defeat Malicious Mobile Code", ACSAC Conference, Dec. 2002, Las Vegas, NV, USA, pp. 1-9. |
Cited By (410)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US9106694B2 (en) | 2004-04-01 | 2015-08-11 | Fireeye, Inc. | Electronic message analysis for malware detection |
| US10165000B1 (en) | 2004-04-01 | 2018-12-25 | Fireeye, Inc. | Systems and methods for malware attack prevention by intercepting flows of information |
| US9356944B1 (en) | 2004-04-01 | 2016-05-31 | Fireeye, Inc. | System and method for detecting malicious traffic using a virtual machine configured with a select software environment |
| US9912684B1 (en) | 2004-04-01 | 2018-03-06 | Fireeye, Inc. | System and method for virtual analysis of network data |
| US8776229B1 (en) | 2004-04-01 | 2014-07-08 | Fireeye, Inc. | System and method of detecting malicious traffic while reducing false positives |
| US8793787B2 (en) | 2004-04-01 | 2014-07-29 | Fireeye, Inc. | Detecting malicious network content using virtual environment components |
| US10623434B1 (en) | 2004-04-01 | 2020-04-14 | Fireeye, Inc. | System and method for virtual analysis of network data |
| US9306960B1 (en) | 2004-04-01 | 2016-04-05 | Fireeye, Inc. | Systems and methods for unauthorized activity defense |
| US8881282B1 (en) | 2004-04-01 | 2014-11-04 | Fireeye, Inc. | Systems and methods for malware attack detection and identification |
| US8898788B1 (en) | 2004-04-01 | 2014-11-25 | Fireeye, Inc. | Systems and methods for malware attack prevention |
| US9516057B2 (en) | 2004-04-01 | 2016-12-06 | Fireeye, Inc. | Systems and methods for computer worm defense |
| US10027690B2 (en) | 2004-04-01 | 2018-07-17 | Fireeye, Inc. | Electronic message analysis for malware detection |
| US10587636B1 (en) | 2004-04-01 | 2020-03-10 | Fireeye, Inc. | System and method for bot detection |
| US9282109B1 (en) | 2004-04-01 | 2016-03-08 | Fireeye, Inc. | System and method for analyzing packets |
| US10068091B1 (en) | 2004-04-01 | 2018-09-04 | Fireeye, Inc. | System and method for malware containment |
| US10511614B1 (en) | 2004-04-01 | 2019-12-17 | Fireeye, Inc. | Subscription based malware detection under management system control |
| US11082435B1 (en) | 2004-04-01 | 2021-08-03 | Fireeye, Inc. | System and method for threat detection and identification |
| US10097573B1 (en) | 2004-04-01 | 2018-10-09 | Fireeye, Inc. | Systems and methods for malware defense |
| US9838411B1 (en) | 2004-04-01 | 2017-12-05 | Fireeye, Inc. | Subscriber based protection system |
| US9027135B1 (en) | 2004-04-01 | 2015-05-05 | Fireeye, Inc. | Prospective client identification using malware attack detection |
| US9071638B1 (en) | 2004-04-01 | 2015-06-30 | Fireeye, Inc. | System and method for malware containment |
| US9591020B1 (en) | 2004-04-01 | 2017-03-07 | Fireeye, Inc. | System and method for signature generation |
| US10567405B1 (en) | 2004-04-01 | 2020-02-18 | Fireeye, Inc. | System for detecting a presence of malware from behavioral analysis |
| US10757120B1 (en) | 2004-04-01 | 2020-08-25 | Fireeye, Inc. | Malicious network content detection |
| US8984638B1 (en) | 2004-04-01 | 2015-03-17 | Fireeye, Inc. | System and method for analyzing suspicious network data |
| US10284574B1 (en) | 2004-04-01 | 2019-05-07 | Fireeye, Inc. | System and method for threat detection and identification |
| US11637857B1 (en) | 2004-04-01 | 2023-04-25 | Fireeye Security Holdings Us Llc | System and method for detecting malicious traffic using a virtual machine configured with a select software environment |
| US9661018B1 (en) | 2004-04-01 | 2017-05-23 | Fireeye, Inc. | System and method for detecting anomalous behaviors using a virtual machine environment |
| US11153341B1 (en) | 2004-04-01 | 2021-10-19 | Fireeye, Inc. | System and method for detecting malicious network content using virtual environment components |
| US9628498B1 (en) | 2004-04-01 | 2017-04-18 | Fireeye, Inc. | System and method for bot detection |
| US9197664B1 (en) | 2004-04-01 | 2015-11-24 | Fire Eye, Inc. | System and method for malware containment |
| US9838416B1 (en) | 2004-06-14 | 2017-12-05 | Fireeye, Inc. | System and method of detecting malicious content |
| US8990939B2 (en) | 2008-11-03 | 2015-03-24 | Fireeye, Inc. | Systems and methods for scheduling analysis of network content for malware |
| US8997219B2 (en) | 2008-11-03 | 2015-03-31 | Fireeye, Inc. | Systems and methods for detecting malicious PDF network content |
| US9118715B2 (en) | 2008-11-03 | 2015-08-25 | Fireeye, Inc. | Systems and methods for detecting malicious PDF network content |
| US8850571B2 (en) | 2008-11-03 | 2014-09-30 | Fireeye, Inc. | Systems and methods for detecting malicious network content |
| US9438622B1 (en) | 2008-11-03 | 2016-09-06 | Fireeye, Inc. | Systems and methods for analyzing malicious PDF network content |
| US9954890B1 (en) | 2008-11-03 | 2018-04-24 | Fireeye, Inc. | Systems and methods for analyzing PDF documents |
| US8914878B2 (en)* | 2009-04-29 | 2014-12-16 | Juniper Networks, Inc. | Detecting malicious network software agents |
| US20100281539A1 (en)* | 2009-04-29 | 2010-11-04 | Juniper Networks, Inc. | Detecting malicious network software agents |
| US9344445B2 (en) | 2009-04-29 | 2016-05-17 | Juniper Networks, Inc. | Detecting malicious network software agents |
| US20110035802A1 (en)* | 2009-08-07 | 2011-02-10 | Microsoft Corporation | Representing virtual object priority based on relationships |
| US11381578B1 (en) | 2009-09-30 | 2022-07-05 | Fireeye Security Holdings Us Llc | Network-based binary file extraction and analysis for malware detection |
| US8935779B2 (en) | 2009-09-30 | 2015-01-13 | Fireeye, Inc. | Network-based binary file extraction and analysis for malware detection |
| US8832829B2 (en) | 2009-09-30 | 2014-09-09 | Fireeye, Inc. | Network-based binary file extraction and analysis for malware detection |
| US10282548B1 (en) | 2012-02-24 | 2019-05-07 | Fireeye, Inc. | Method for detecting malware within network content |
| US9519782B2 (en) | 2012-02-24 | 2016-12-13 | Fireeye, Inc. | Detecting malicious network content |
| US20130247194A1 (en)* | 2012-03-16 | 2013-09-19 | Niraj K. Jha | Securing medical devices through wireless monitoring and anomaly detection |
| US10135849B2 (en)* | 2012-03-16 | 2018-11-20 | Purdue Research Foundation | Securing medical devices through wireless monitoring and anomaly detection |
| US20130305368A1 (en)* | 2012-05-09 | 2013-11-14 | SunStone Information Defense Inc. | Methods and apparatus for identifying and removing malicious applications |
| US11687653B2 (en) | 2012-05-09 | 2023-06-27 | SunStone Information Defense, Inc. | Methods and apparatus for identifying and removing malicious applications |
| US10235524B2 (en) | 2012-05-09 | 2019-03-19 | SunStone Information Defense, Inc. | Methods and apparatus for identifying and removing malicious applications |
| US9659175B2 (en)* | 2012-05-09 | 2017-05-23 | SunStone Information Defense Inc. | Methods and apparatus for identifying and removing malicious applications |
| US10721243B2 (en)* | 2012-09-28 | 2020-07-21 | Level 3 Communications, Llc | Apparatus, system and method for identifying and mitigating malicious network threats |
| US10129270B2 (en)* | 2012-09-28 | 2018-11-13 | Level 3 Communications, Llc | Apparatus, system and method for identifying and mitigating malicious network threats |
| US20190104136A1 (en)* | 2012-09-28 | 2019-04-04 | Level 3 Communications, Llc | Apparatus, system and method for identifying and mitigating malicious network threats |
| US10572665B2 (en) | 2012-12-28 | 2020-02-25 | Fireeye, Inc. | System and method to create a number of breakpoints in a virtual machine via virtual machine trapping events |
| US9824209B1 (en) | 2013-02-23 | 2017-11-21 | Fireeye, Inc. | Framework for efficient security coverage of mobile software applications that is usable to harden in the field code |
| US9792196B1 (en) | 2013-02-23 | 2017-10-17 | Fireeye, Inc. | Framework for efficient security coverage of mobile software applications |
| US9367681B1 (en) | 2013-02-23 | 2016-06-14 | Fireeye, Inc. | Framework for efficient security coverage of mobile software applications using symbolic execution to reach regions of interest within an application |
| US10019338B1 (en) | 2013-02-23 | 2018-07-10 | Fireeye, Inc. | User interface with real-time visual playback along with synchronous textual analysis log display and event/time index for anomalous behavior detection in applications |
| US10181029B1 (en) | 2013-02-23 | 2019-01-15 | Fireeye, Inc. | Security cloud service framework for hardening in the field code of mobile software applications |
| US10929266B1 (en) | 2013-02-23 | 2021-02-23 | Fireeye, Inc. | Real-time visual playback with synchronous textual analysis log display and event/time indexing |
| US9159035B1 (en) | 2013-02-23 | 2015-10-13 | Fireeye, Inc. | Framework for computer application analysis of sensitive information tracking |
| US9176843B1 (en) | 2013-02-23 | 2015-11-03 | Fireeye, Inc. | Framework for efficient security coverage of mobile software applications |
| US10296437B2 (en) | 2013-02-23 | 2019-05-21 | Fireeye, Inc. | Framework for efficient security coverage of mobile software applications |
| US9195829B1 (en) | 2013-02-23 | 2015-11-24 | Fireeye, Inc. | User interface with real-time visual playback along with synchronous textual analysis log display and event/time index for anomalous behavior detection in applications |
| US9225740B1 (en) | 2013-02-23 | 2015-12-29 | Fireeye, Inc. | Framework for iterative analysis of mobile software applications |
| US8990944B1 (en) | 2013-02-23 | 2015-03-24 | Fireeye, Inc. | Systems and methods for automatically detecting backdoors |
| US9009822B1 (en) | 2013-02-23 | 2015-04-14 | Fireeye, Inc. | Framework for multi-phase analysis of mobile applications |
| US9594905B1 (en) | 2013-02-23 | 2017-03-14 | Fireeye, Inc. | Framework for efficient security coverage of mobile software applications using machine learning |
| US9009823B1 (en) | 2013-02-23 | 2015-04-14 | Fireeye, Inc. | Framework for efficient security coverage of mobile software applications installed on mobile devices |
| US9626509B1 (en) | 2013-03-13 | 2017-04-18 | Fireeye, Inc. | Malicious content analysis with multi-version application support within single operating environment |
| US10467414B1 (en) | 2013-03-13 | 2019-11-05 | Fireeye, Inc. | System and method for detecting exfiltration content |
| US11210390B1 (en) | 2013-03-13 | 2021-12-28 | Fireeye Security Holdings Us Llc | Multi-version application support and registration within a single operating system environment |
| US9355247B1 (en) | 2013-03-13 | 2016-05-31 | Fireeye, Inc. | File extraction from memory dump for malicious content analysis |
| US10198574B1 (en) | 2013-03-13 | 2019-02-05 | Fireeye, Inc. | System and method for analysis of a memory dump associated with a potentially malicious content suspect |
| US9565202B1 (en) | 2013-03-13 | 2017-02-07 | Fireeye, Inc. | System and method for detecting exfiltration content |
| US9104867B1 (en) | 2013-03-13 | 2015-08-11 | Fireeye, Inc. | Malicious content analysis using simulated user interaction without user involvement |
| US10025927B1 (en) | 2013-03-13 | 2018-07-17 | Fireeye, Inc. | Malicious content analysis with multi-version application support within single operating environment |
| US10848521B1 (en) | 2013-03-13 | 2020-11-24 | Fireeye, Inc. | Malicious content analysis using simulated user interaction without user involvement |
| US9934381B1 (en) | 2013-03-13 | 2018-04-03 | Fireeye, Inc. | System and method for detecting malicious activity based on at least one environmental property |
| US9912698B1 (en) | 2013-03-13 | 2018-03-06 | Fireeye, Inc. | Malicious content analysis using simulated user interaction without user involvement |
| US9311479B1 (en) | 2013-03-14 | 2016-04-12 | Fireeye, Inc. | Correlation and consolidation of analytic data for holistic view of a malware attack |
| US10812513B1 (en) | 2013-03-14 | 2020-10-20 | Fireeye, Inc. | Correlation and consolidation holistic views of analytic data pertaining to a malware attack |
| US10200384B1 (en) | 2013-03-14 | 2019-02-05 | Fireeye, Inc. | Distributed systems and methods for automatically detecting unknown bots and botnets |
| US10122746B1 (en) | 2013-03-14 | 2018-11-06 | Fireeye, Inc. | Correlation and consolidation of analytic data for holistic view of malware attack |
| US9430646B1 (en) | 2013-03-14 | 2016-08-30 | Fireeye, Inc. | Distributed systems and methods for automatically detecting unknown bots and botnets |
| US9641546B1 (en) | 2013-03-14 | 2017-05-02 | Fireeye, Inc. | Electronic device for aggregation, correlation and consolidation of analysis attributes |
| US10713358B2 (en) | 2013-03-15 | 2020-07-14 | Fireeye, Inc. | System and method to extract and utilize disassembly features to classify software intent |
| US10701091B1 (en) | 2013-03-15 | 2020-06-30 | Fireeye, Inc. | System and method for verifying a cyberthreat |
| US9497213B2 (en) | 2013-03-15 | 2016-11-15 | Fireeye, Inc. | System and method to manage sinkholes |
| US9251343B1 (en) | 2013-03-15 | 2016-02-02 | Fireeye, Inc. | Detecting bootkits resident on compromised computers |
| US9495180B2 (en) | 2013-05-10 | 2016-11-15 | Fireeye, Inc. | Optimized resource allocation for virtual machines within a malware content detection system |
| US10469512B1 (en) | 2013-05-10 | 2019-11-05 | Fireeye, Inc. | Optimized resource allocation for virtual machines within a malware content detection system |
| US10033753B1 (en) | 2013-05-13 | 2018-07-24 | Fireeye, Inc. | System and method for detecting malicious activity and classifying a network communication based on different indicator types |
| US9635039B1 (en) | 2013-05-13 | 2017-04-25 | Fireeye, Inc. | Classifying sets of malicious indicators for detecting command and control communications associated with malware |
| US10637880B1 (en) | 2013-05-13 | 2020-04-28 | Fireeye, Inc. | Classifying sets of malicious indicators for detecting command and control communications associated with malware |
| US10097567B2 (en) | 2013-05-20 | 2018-10-09 | Nippon Telegraph And Telephone Corporation | Information processing apparatus and identifying method |
| US10335738B1 (en) | 2013-06-24 | 2019-07-02 | Fireeye, Inc. | System and method for detecting time-bomb malware |
| US10083302B1 (en) | 2013-06-24 | 2018-09-25 | Fireeye, Inc. | System and method for detecting time-bomb malware |
| US9536091B2 (en) | 2013-06-24 | 2017-01-03 | Fireeye, Inc. | System and method for detecting time-bomb malware |
| US10133863B2 (en) | 2013-06-24 | 2018-11-20 | Fireeye, Inc. | Zero-day discovery system |
| US20150007250A1 (en)* | 2013-06-27 | 2015-01-01 | The Mitre Corporation | Interception and Policy Application for Malicious Communications |
| US9443075B2 (en)* | 2013-06-27 | 2016-09-13 | The Mitre Corporation | Interception and policy application for malicious communications |
| US10505956B1 (en) | 2013-06-28 | 2019-12-10 | Fireeye, Inc. | System and method for detecting malicious links in electronic messages |
| US9888019B1 (en) | 2013-06-28 | 2018-02-06 | Fireeye, Inc. | System and method for detecting malicious links in electronic messages |
| US9888016B1 (en) | 2013-06-28 | 2018-02-06 | Fireeye, Inc. | System and method for detecting phishing using password prediction |
| US9300686B2 (en) | 2013-06-28 | 2016-03-29 | Fireeye, Inc. | System and method for detecting malicious links in electronic messages |
| US10657251B1 (en) | 2013-09-30 | 2020-05-19 | Fireeye, Inc. | Multistage system and method for analyzing obfuscated content for malware |
| US9690936B1 (en) | 2013-09-30 | 2017-06-27 | Fireeye, Inc. | Multistage system and method for analyzing obfuscated content for malware |
| US10218740B1 (en) | 2013-09-30 | 2019-02-26 | Fireeye, Inc. | Fuzzy hash of behavioral results |
| US10713362B1 (en) | 2013-09-30 | 2020-07-14 | Fireeye, Inc. | Dynamically adaptive framework and method for classifying malware using intelligent static, emulation, and dynamic analyses |
| US10735458B1 (en) | 2013-09-30 | 2020-08-04 | Fireeye, Inc. | Detection center to detect targeted malware |
| US9910988B1 (en) | 2013-09-30 | 2018-03-06 | Fireeye, Inc. | Malware analysis in accordance with an analysis plan |
| US9912691B2 (en) | 2013-09-30 | 2018-03-06 | Fireeye, Inc. | Fuzzy hash of behavioral results |
| US9736179B2 (en) | 2013-09-30 | 2017-08-15 | Fireeye, Inc. | System, apparatus and method for using malware analysis results to drive adaptive instrumentation of virtual machines to improve exploit detection |
| US9171160B2 (en) | 2013-09-30 | 2015-10-27 | Fireeye, Inc. | Dynamically adaptive framework and method for classifying malware using intelligent static, emulation, and dynamic analyses |
| US10192052B1 (en) | 2013-09-30 | 2019-01-29 | Fireeye, Inc. | System, apparatus and method for classifying a file as malicious using static scanning |
| US10515214B1 (en) | 2013-09-30 | 2019-12-24 | Fireeye, Inc. | System and method for classifying malware within content created during analysis of a specimen |
| US9628507B2 (en) | 2013-09-30 | 2017-04-18 | Fireeye, Inc. | Advanced persistent threat (APT) detection center |
| US10089461B1 (en) | 2013-09-30 | 2018-10-02 | Fireeye, Inc. | Page replacement code injection |
| US11075945B2 (en) | 2013-09-30 | 2021-07-27 | Fireeye, Inc. | System, apparatus and method for reconfiguring virtual machines |
| US9294501B2 (en) | 2013-09-30 | 2016-03-22 | Fireeye, Inc. | Fuzzy hash of behavioral results |
| US9405903B1 (en)* | 2013-10-31 | 2016-08-02 | Palo Alto Networks, Inc. | Sinkholing bad network domains by registering the bad network domains on the internet |
| US11128656B2 (en) | 2013-10-31 | 2021-09-21 | Palo Alto Networks, Inc. | Selective sinkholing of malware domains by a security device via DNS poisoning |
| US9325735B1 (en) | 2013-10-31 | 2016-04-26 | Palo Alto Networks, Inc. | Selective sinkholing of malware domains by a security device via DNS poisoning |
| US10305927B2 (en) | 2013-10-31 | 2019-05-28 | Palo Alto Networks, Inc. | Sinkholing bad network domains by registering the bad network domains on the internet |
| US9560072B1 (en) | 2013-10-31 | 2017-01-31 | Palo Alto Networks, Inc. | Discovering and selecting candidates for sinkholing of network domains |
| US9921978B1 (en) | 2013-11-08 | 2018-03-20 | Fireeye, Inc. | System and method for enhanced security of storage devices |
| US9560059B1 (en) | 2013-11-21 | 2017-01-31 | Fireeye, Inc. | System, apparatus and method for conducting on-the-fly decryption of encrypted objects for malware detection |
| US9189627B1 (en) | 2013-11-21 | 2015-11-17 | Fireeye, Inc. | System, apparatus and method for conducting on-the-fly decryption of encrypted objects for malware detection |
| US9306974B1 (en) | 2013-12-26 | 2016-04-05 | Fireeye, Inc. | System, apparatus and method for automatically verifying exploits within suspect objects and highlighting the display information associated with the verified exploits |
| US11089057B1 (en) | 2013-12-26 | 2021-08-10 | Fireeye, Inc. | System, apparatus and method for automatically verifying exploits within suspect objects and highlighting the display information associated with the verified exploits |
| US10467411B1 (en) | 2013-12-26 | 2019-11-05 | Fireeye, Inc. | System and method for generating a malware identifier |
| US10476909B1 (en) | 2013-12-26 | 2019-11-12 | Fireeye, Inc. | System, apparatus and method for automatically verifying exploits within suspect objects and highlighting the display information associated with the verified exploits |
| US9747446B1 (en) | 2013-12-26 | 2017-08-29 | Fireeye, Inc. | System and method for run-time object classification |
| US9756074B2 (en) | 2013-12-26 | 2017-09-05 | Fireeye, Inc. | System and method for IPS and VM-based detection of suspicious objects |
| US10740456B1 (en) | 2014-01-16 | 2020-08-11 | Fireeye, Inc. | Threat-aware architecture |
| US20150207812A1 (en)* | 2014-01-17 | 2015-07-23 | Gregory Thomas BACK | Systems and methods for identifying and performing an action in response to identified malicious network traffic |
| US10432658B2 (en)* | 2014-01-17 | 2019-10-01 | Watchguard Technologies, Inc. | Systems and methods for identifying and performing an action in response to identified malicious network traffic |
| US10534906B1 (en) | 2014-02-05 | 2020-01-14 | Fireeye, Inc. | Detection efficacy of virtual machine-based analysis with application specific events |
| US9916440B1 (en) | 2014-02-05 | 2018-03-13 | Fireeye, Inc. | Detection efficacy of virtual machine-based analysis with application specific events |
| US9262635B2 (en) | 2014-02-05 | 2016-02-16 | Fireeye, Inc. | Detection efficacy of virtual machine-based analysis with application specific events |
| US9241010B1 (en) | 2014-03-20 | 2016-01-19 | Fireeye, Inc. | System and method for network behavior detection |
| US10432649B1 (en) | 2014-03-20 | 2019-10-01 | Fireeye, Inc. | System and method for classifying an object based on an aggregated behavior results |
| US11068587B1 (en) | 2014-03-21 | 2021-07-20 | Fireeye, Inc. | Dynamic guest image creation and rollback |
| US10242185B1 (en) | 2014-03-21 | 2019-03-26 | Fireeye, Inc. | Dynamic guest image creation and rollback |
| US11082436B1 (en) | 2014-03-28 | 2021-08-03 | Fireeye, Inc. | System and method for offloading packet processing and static analysis operations |
| US10454953B1 (en) | 2014-03-28 | 2019-10-22 | Fireeye, Inc. | System and method for separated packet processing and static analysis |
| US9787700B1 (en) | 2014-03-28 | 2017-10-10 | Fireeye, Inc. | System and method for offloading packet processing and static analysis operations |
| US9591015B1 (en) | 2014-03-28 | 2017-03-07 | Fireeye, Inc. | System and method for offloading packet processing and static analysis operations |
| US10341363B1 (en) | 2014-03-31 | 2019-07-02 | Fireeye, Inc. | Dynamically remote tuning of a malware content detection system |
| US11297074B1 (en) | 2014-03-31 | 2022-04-05 | FireEye Security Holdings, Inc. | Dynamically remote tuning of a malware content detection system |
| US11949698B1 (en) | 2014-03-31 | 2024-04-02 | Musarubra Us Llc | Dynamically remote tuning of a malware content detection system |
| US9223972B1 (en) | 2014-03-31 | 2015-12-29 | Fireeye, Inc. | Dynamically remote tuning of a malware content detection system |
| US9432389B1 (en) | 2014-03-31 | 2016-08-30 | Fireeye, Inc. | System, apparatus and method for detecting a malicious attack based on static analysis of a multi-flow object |
| US9594912B1 (en) | 2014-06-06 | 2017-03-14 | Fireeye, Inc. | Return-oriented programming detection |
| US9438623B1 (en) | 2014-06-06 | 2016-09-06 | Fireeye, Inc. | Computer exploit detection using heap spray pattern matching |
| US9973531B1 (en) | 2014-06-06 | 2018-05-15 | Fireeye, Inc. | Shellcode detection |
| EP3161712A4 (en)* | 2014-06-24 | 2018-01-24 | Fireeye Inc. | Malware detection and remediation for endpoint deviced |
| US10084813B2 (en) | 2014-06-24 | 2018-09-25 | Fireeye, Inc. | Intrusion prevention and remedy system |
| US10757134B1 (en) | 2014-06-24 | 2020-08-25 | Fireeye, Inc. | System and method for detecting and remediating a cybersecurity attack |
| US9398028B1 (en) | 2014-06-26 | 2016-07-19 | Fireeye, Inc. | System, device and method for detecting a malicious attack based on communcations between remotely hosted virtual machines and malicious web servers |
| US10805340B1 (en) | 2014-06-26 | 2020-10-13 | Fireeye, Inc. | Infection vector and malware tracking with an interactive user display |
| US9838408B1 (en) | 2014-06-26 | 2017-12-05 | Fireeye, Inc. | System, device and method for detecting a malicious attack based on direct communications between remotely hosted virtual machines and malicious web servers |
| US9661009B1 (en) | 2014-06-26 | 2017-05-23 | Fireeye, Inc. | Network-based malware detection |
| US11244056B1 (en) | 2014-07-01 | 2022-02-08 | Fireeye Security Holdings Us Llc | Verification of trusted threat-aware visualization layer |
| US9912644B2 (en) | 2014-08-05 | 2018-03-06 | Fireeye, Inc. | System and method to communicate sensitive information via one or more untrusted intermediate nodes with resilience to disconnected network topology |
| US12026257B2 (en) | 2014-08-11 | 2024-07-02 | Sentinel Labs Israel Ltd. | Method of malware detection and system thereof |
| US11625485B2 (en) | 2014-08-11 | 2023-04-11 | Sentinel Labs Israel Ltd. | Method of malware detection and system thereof |
| US12235962B2 (en) | 2014-08-11 | 2025-02-25 | Sentinel Labs Israel Ltd. | Method of remediating operations performed by a program and system thereof |
| US11886591B2 (en) | 2014-08-11 | 2024-01-30 | Sentinel Labs Israel Ltd. | Method of remediating operations performed by a program and system thereof |
| US9363280B1 (en) | 2014-08-22 | 2016-06-07 | Fireeye, Inc. | System and method of detecting delivery of malware using cross-customer data |
| US10404725B1 (en) | 2014-08-22 | 2019-09-03 | Fireeye, Inc. | System and method of detecting delivery of malware using cross-customer data |
| US9609007B1 (en) | 2014-08-22 | 2017-03-28 | Fireeye, Inc. | System and method of detecting delivery of malware based on indicators of compromise from different sources |
| US10027696B1 (en) | 2014-08-22 | 2018-07-17 | Fireeye, Inc. | System and method for determining a threat based on correlation of indicators of compromise from other sources |
| US10671726B1 (en) | 2014-09-22 | 2020-06-02 | Fireeye Inc. | System and method for malware analysis using thread-level event monitoring |
| US10868818B1 (en) | 2014-09-29 | 2020-12-15 | Fireeye, Inc. | Systems and methods for generation of signature generation using interactive infection visualizations |
| US10027689B1 (en) | 2014-09-29 | 2018-07-17 | Fireeye, Inc. | Interactive infection visualization for improved exploit detection and signature generation for malware and malware families |
| US9773112B1 (en) | 2014-09-29 | 2017-09-26 | Fireeye, Inc. | Exploit detection of malware and malware families |
| US9690933B1 (en) | 2014-12-22 | 2017-06-27 | Fireeye, Inc. | Framework for classifying an object as malicious with machine learning for deploying updated predictive models |
| US10902117B1 (en) | 2014-12-22 | 2021-01-26 | Fireeye, Inc. | Framework for classifying an object as malicious with machine learning for deploying updated predictive models |
| US10366231B1 (en) | 2014-12-22 | 2019-07-30 | Fireeye, Inc. | Framework for classifying an object as malicious with machine learning for deploying updated predictive models |
| US10075455B2 (en) | 2014-12-26 | 2018-09-11 | Fireeye, Inc. | Zero-day rotating guest image profile |
| US10528726B1 (en) | 2014-12-29 | 2020-01-07 | Fireeye, Inc. | Microvisor-based malware detection appliance architecture |
| US10798121B1 (en) | 2014-12-30 | 2020-10-06 | Fireeye, Inc. | Intelligent context aware user interaction for malware detection |
| US9838417B1 (en) | 2014-12-30 | 2017-12-05 | Fireeye, Inc. | Intelligent context aware user interaction for malware detection |
| US10666686B1 (en) | 2015-03-25 | 2020-05-26 | Fireeye, Inc. | Virtualized exploit detection system |
| US10148693B2 (en) | 2015-03-25 | 2018-12-04 | Fireeye, Inc. | Exploit detection system |
| US9690606B1 (en) | 2015-03-25 | 2017-06-27 | Fireeye, Inc. | Selective system call monitoring |
| US9438613B1 (en) | 2015-03-30 | 2016-09-06 | Fireeye, Inc. | Dynamic content activation for automated analysis of embedded objects |
| US9483644B1 (en) | 2015-03-31 | 2016-11-01 | Fireeye, Inc. | Methods for detecting file altering malware in VM based analysis |
| US11868795B1 (en) | 2015-03-31 | 2024-01-09 | Musarubra Us Llc | Selective virtualization for security threat detection |
| US10474813B1 (en) | 2015-03-31 | 2019-11-12 | Fireeye, Inc. | Code injection technique for remediation at an endpoint of a network |
| US9846776B1 (en) | 2015-03-31 | 2017-12-19 | Fireeye, Inc. | System and method for detecting file altering behaviors pertaining to a malicious attack |
| US10417031B2 (en) | 2015-03-31 | 2019-09-17 | Fireeye, Inc. | Selective virtualization for security threat detection |
| US11294705B1 (en) | 2015-03-31 | 2022-04-05 | Fireeye Security Holdings Us Llc | Selective virtualization for security threat detection |
| US10728263B1 (en) | 2015-04-13 | 2020-07-28 | Fireeye, Inc. | Analytic-based security monitoring system and method |
| US10104102B1 (en) | 2015-04-13 | 2018-10-16 | Fireeye, Inc. | Analytic-based security with learning adaptability |
| US9594904B1 (en) | 2015-04-23 | 2017-03-14 | Fireeye, Inc. | Detecting malware based on reflection |
| US11032297B2 (en) | 2015-06-29 | 2021-06-08 | Palo Alto Networks, Inc. | DGA behavior detection |
| US10812501B2 (en) | 2015-06-29 | 2020-10-20 | Palo Alto Networks, Inc. | DGA behavior detection |
| US10395029B1 (en) | 2015-06-30 | 2019-08-27 | Fireeye, Inc. | Virtual system and method with threat protection |
| US10642753B1 (en) | 2015-06-30 | 2020-05-05 | Fireeye, Inc. | System and method for protecting a software component running in virtual machine using a virtualization layer |
| US11113086B1 (en) | 2015-06-30 | 2021-09-07 | Fireeye, Inc. | Virtual system and method for securing external network connectivity |
| US10216927B1 (en) | 2015-06-30 | 2019-02-26 | Fireeye, Inc. | System and method for protecting memory pages associated with a process using a virtualization layer |
| US10726127B1 (en) | 2015-06-30 | 2020-07-28 | Fireeye, Inc. | System and method for protecting a software component running in a virtual machine through virtual interrupts by the virtualization layer |
| US10454950B1 (en) | 2015-06-30 | 2019-10-22 | Fireeye, Inc. | Centralized aggregation technique for detecting lateral movement of stealthy cyber-attacks |
| US10476891B2 (en)* | 2015-07-21 | 2019-11-12 | Attivo Networks Inc. | Monitoring access of network darkspace |
| US20170026387A1 (en)* | 2015-07-21 | 2017-01-26 | Attivo Networks Inc. | Monitoring access of network darkspace |
| US10715542B1 (en) | 2015-08-14 | 2020-07-14 | Fireeye, Inc. | Mobile application risk analysis |
| US10176321B2 (en) | 2015-09-22 | 2019-01-08 | Fireeye, Inc. | Leveraging behavior-based rules for malware family classification |
| US10033759B1 (en) | 2015-09-28 | 2018-07-24 | Fireeye, Inc. | System and method of threat detection under hypervisor control |
| US10887328B1 (en) | 2015-09-29 | 2021-01-05 | Fireeye, Inc. | System and method for detecting interpreter-based exploit attacks |
| US10033747B1 (en) | 2015-09-29 | 2018-07-24 | Fireeye, Inc. | System and method for detecting interpreter-based exploit attacks |
| US10706149B1 (en) | 2015-09-30 | 2020-07-07 | Fireeye, Inc. | Detecting delayed activation malware using a primary controller and plural time controllers |
| US10873597B1 (en) | 2015-09-30 | 2020-12-22 | Fireeye, Inc. | Cyber attack early warning system |
| US9825976B1 (en) | 2015-09-30 | 2017-11-21 | Fireeye, Inc. | Detection and classification of exploit kits |
| US10210329B1 (en) | 2015-09-30 | 2019-02-19 | Fireeye, Inc. | Method to detect application execution hijacking using memory protection |
| US9825989B1 (en) | 2015-09-30 | 2017-11-21 | Fireeye, Inc. | Cyber attack early warning system |
| US10601865B1 (en) | 2015-09-30 | 2020-03-24 | Fireeye, Inc. | Detection of credential spearphishing attacks using email analysis |
| US10817606B1 (en) | 2015-09-30 | 2020-10-27 | Fireeye, Inc. | Detecting delayed activation malware using a run-time monitoring agent and time-dilation logic |
| US11244044B1 (en) | 2015-09-30 | 2022-02-08 | Fireeye Security Holdings Us Llc | Method to detect application execution hijacking using memory protection |
| US10834107B1 (en) | 2015-11-10 | 2020-11-10 | Fireeye, Inc. | Launcher for setting analysis environment variations for malware detection |
| US10284575B2 (en) | 2015-11-10 | 2019-05-07 | Fireeye, Inc. | Launcher for setting analysis environment variations for malware detection |
| US10447728B1 (en) | 2015-12-10 | 2019-10-15 | Fireeye, Inc. | Technique for protecting guest processes using a layered virtualization architecture |
| US10846117B1 (en) | 2015-12-10 | 2020-11-24 | Fireeye, Inc. | Technique for establishing secure communication between host and guest processes of a virtualization architecture |
| US11200080B1 (en) | 2015-12-11 | 2021-12-14 | Fireeye Security Holdings Us Llc | Late load technique for deploying a virtualization layer underneath a running operating system |
| US10341365B1 (en) | 2015-12-30 | 2019-07-02 | Fireeye, Inc. | Methods and system for hiding transition events for malware detection |
| US10872151B1 (en) | 2015-12-30 | 2020-12-22 | Fireeye, Inc. | System and method for triggering analysis of an object for malware in response to modification of that object |
| US10133866B1 (en) | 2015-12-30 | 2018-11-20 | Fireeye, Inc. | System and method for triggering analysis of an object for malware in response to modification of that object |
| US10050998B1 (en) | 2015-12-30 | 2018-08-14 | Fireeye, Inc. | Malicious message analysis system |
| US10565378B1 (en) | 2015-12-30 | 2020-02-18 | Fireeye, Inc. | Exploit of privilege detection framework |
| US10581898B1 (en) | 2015-12-30 | 2020-03-03 | Fireeye, Inc. | Malicious message analysis system |
| US11552986B1 (en) | 2015-12-31 | 2023-01-10 | Fireeye Security Holdings Us Llc | Cyber-security framework for application of virtual features |
| US10445502B1 (en)* | 2015-12-31 | 2019-10-15 | Fireeye, Inc. | Susceptible environment detection system |
| US9824216B1 (en) | 2015-12-31 | 2017-11-21 | Fireeye, Inc. | Susceptible environment detection system |
| US10581874B1 (en) | 2015-12-31 | 2020-03-03 | Fireeye, Inc. | Malware detection system with contextual analysis |
| US10616266B1 (en) | 2016-03-25 | 2020-04-07 | Fireeye, Inc. | Distributed malware detection system and submission workflow thereof |
| US10476906B1 (en) | 2016-03-25 | 2019-11-12 | Fireeye, Inc. | System and method for managing formation and modification of a cluster within a malware detection system |
| US10601863B1 (en) | 2016-03-25 | 2020-03-24 | Fireeye, Inc. | System and method for managing sensor enrollment |
| US10671721B1 (en) | 2016-03-25 | 2020-06-02 | Fireeye, Inc. | Timeout management services |
| US11632392B1 (en) | 2016-03-25 | 2023-04-18 | Fireeye Security Holdings Us Llc | Distributed malware detection system and submission workflow thereof |
| US10785255B1 (en) | 2016-03-25 | 2020-09-22 | Fireeye, Inc. | Cluster configuration within a scalable malware detection system |
| US11979428B1 (en) | 2016-03-31 | 2024-05-07 | Musarubra Us Llc | Technique for verifying exploit/malware at malware detection appliance through correlation with endpoints |
| US11936666B1 (en) | 2016-03-31 | 2024-03-19 | Musarubra Us Llc | Risk analyzer for ascertaining a risk of harm to a network and generating alerts regarding the ascertained risk |
| US10893059B1 (en) | 2016-03-31 | 2021-01-12 | Fireeye, Inc. | Verification and enhancement using detection systems located at the network periphery and endpoint devices |
| US10169585B1 (en) | 2016-06-22 | 2019-01-01 | Fireeye, Inc. | System and methods for advanced malware detection through placement of transition events |
| US12166786B1 (en) | 2016-06-30 | 2024-12-10 | Musarubra Us Llc | Malware detection verification and enhancement by coordinating endpoint and malware detection systems |
| US10462173B1 (en) | 2016-06-30 | 2019-10-29 | Fireeye, Inc. | Malware detection verification and enhancement by coordinating endpoint and malware detection systems |
| US11240262B1 (en) | 2016-06-30 | 2022-02-01 | Fireeye Security Holdings Us Llc | Malware detection verification and enhancement by coordinating endpoint and malware detection systems |
| US10430588B2 (en) | 2016-07-06 | 2019-10-01 | Trust Ltd. | Method of and system for analysis of interaction patterns of malware with control centers for detection of cyber attack |
| RU2634211C1 (en)* | 2016-07-06 | 2017-10-24 | Общество с ограниченной ответственностью "Траст" | Method and system of protocols analysis of harmful programs interaction with control centers and detection of computer attacks |
| EP3267350A1 (en)* | 2016-07-06 | 2018-01-10 | Trust Ltd. | Method of and system for analysis of interaction patterns of malware with control centers for detection of cyber attack |
| US10721251B2 (en) | 2016-08-03 | 2020-07-21 | Group Ib, Ltd | Method and system for detecting remote access during activity on the pages of a web resource |
| US10592678B1 (en) | 2016-09-09 | 2020-03-17 | Fireeye, Inc. | Secure communications between peers using a verified virtual trusted platform module |
| US10581880B2 (en) | 2016-09-19 | 2020-03-03 | Group-Ib Tds Ltd. | System and method for generating rules for attack detection feedback system |
| US10491627B1 (en) | 2016-09-29 | 2019-11-26 | Fireeye, Inc. | Advanced malware detection using similarity analysis |
| US12130909B1 (en) | 2016-11-08 | 2024-10-29 | Musarubra Us Llc | Enterprise search |
| US10795991B1 (en) | 2016-11-08 | 2020-10-06 | Fireeye, Inc. | Enterprise search |
| US10587647B1 (en) | 2016-11-22 | 2020-03-10 | Fireeye, Inc. | Technique for malware detection capability comparison of network security devices |
| US11997139B2 (en) | 2016-12-19 | 2024-05-28 | SentinelOne, Inc. | Deceiving attackers accessing network data |
| US11695800B2 (en) | 2016-12-19 | 2023-07-04 | SentinelOne, Inc. | Deceiving attackers accessing network data |
| US11616812B2 (en) | 2016-12-19 | 2023-03-28 | Attivo Networks Inc. | Deceiving attackers accessing active directory data |
| US12432253B2 (en) | 2016-12-19 | 2025-09-30 | SentinelOne, Inc. | Deceiving attackers accessing network data |
| US12418565B2 (en) | 2016-12-19 | 2025-09-16 | SentinelOne, Inc. | Deceiving attackers accessing network data |
| US12261884B2 (en) | 2016-12-19 | 2025-03-25 | SentinelOne, Inc. | Deceiving attackers accessing active directory data |
| US10552610B1 (en) | 2016-12-22 | 2020-02-04 | Fireeye, Inc. | Adaptive virtual machine snapshot update framework for malware behavioral analysis |
| US10581879B1 (en) | 2016-12-22 | 2020-03-03 | Fireeye, Inc. | Enhanced malware detection for generated objects |
| US10523609B1 (en) | 2016-12-27 | 2019-12-31 | Fireeye, Inc. | Multi-vector malware detection and analysis |
| US10721271B2 (en) | 2016-12-29 | 2020-07-21 | Trust Ltd. | System and method for detecting phishing web pages |
| US10778719B2 (en) | 2016-12-29 | 2020-09-15 | Trust Ltd. | System and method for gathering information to detect phishing activity |
| US11546153B2 (en) | 2017-03-22 | 2023-01-03 | Extrahop Networks, Inc. | Managing session secrets for continuous packet capture systems |
| US11570211B1 (en) | 2017-03-24 | 2023-01-31 | Fireeye Security Holdings Us Llc | Detection of phishing attacks using similarity analysis |
| US10904286B1 (en) | 2017-03-24 | 2021-01-26 | Fireeye, Inc. | Detection of phishing attacks using similarity analysis |
| US12348561B1 (en) | 2017-03-24 | 2025-07-01 | Musarubra Us Llc | Detection of phishing attacks using similarity analysis |
| US12278834B1 (en) | 2017-03-30 | 2025-04-15 | Musarubra Us Llc | Subscription-based malware detection |
| US10554507B1 (en) | 2017-03-30 | 2020-02-04 | Fireeye, Inc. | Multi-level control for enhanced resource and object evaluation management of malware detection system |
| US11863581B1 (en) | 2017-03-30 | 2024-01-02 | Musarubra Us Llc | Subscription-based malware detection |
| US10902119B1 (en) | 2017-03-30 | 2021-01-26 | Fireeye, Inc. | Data extraction system for malware analysis |
| US11997111B1 (en) | 2017-03-30 | 2024-05-28 | Musarubra Us Llc | Attribute-controlled malware detection |
| US11399040B1 (en) | 2017-03-30 | 2022-07-26 | Fireeye Security Holdings Us Llc | Subscription-based malware detection |
| US10848397B1 (en) | 2017-03-30 | 2020-11-24 | Fireeye, Inc. | System and method for enforcing compliance with subscription requirements for cyber-attack detection service |
| US10791138B1 (en) | 2017-03-30 | 2020-09-29 | Fireeye, Inc. | Subscription-based malware detection |
| US10798112B2 (en) | 2017-03-30 | 2020-10-06 | Fireeye, Inc. | Attribute-controlled malware detection |
| CN108076038A (en)* | 2017-06-16 | 2018-05-25 | 哈尔滨安天科技股份有限公司 | A kind of C&C servers determination methods and system based on Service-Port |
| US10855700B1 (en) | 2017-06-29 | 2020-12-01 | Fireeye, Inc. | Post-intrusion detection of cyber-attacks during lateral movement within networks |
| US10601848B1 (en) | 2017-06-29 | 2020-03-24 | Fireeye, Inc. | Cyber-security system and method for weak indicator detection and correlation to generate strong indicators |
| US10503904B1 (en) | 2017-06-29 | 2019-12-10 | Fireeye, Inc. | Ransomware detection and mitigation |
| US10893068B1 (en) | 2017-06-30 | 2021-01-12 | Fireeye, Inc. | Ransomware file modification prevention technique |
| US12363151B2 (en) | 2017-08-08 | 2025-07-15 | Sentinel Labs Israel Ltd. | Methods, systems, and devices for dynamically modeling and grouping endpoints for edge networking |
| US12244626B2 (en) | 2017-08-08 | 2025-03-04 | Sentinel Labs Israel Ltd. | Methods, systems, and devices for dynamically modeling and grouping endpoints for edge networking |
| US12206698B2 (en) | 2017-08-08 | 2025-01-21 | Sentinel Labs Israel Ltd. | Methods, systems, and devices for dynamically modeling and grouping endpoints for edge networking |
| US12177241B2 (en) | 2017-08-08 | 2024-12-24 | Sentinel Labs Israel Ltd. | Methods, systems, and devices for dynamically modeling and grouping endpoints for edge networking |
| US11838306B2 (en) | 2017-08-08 | 2023-12-05 | Sentinel Labs Israel Ltd. | Methods, systems, and devices for dynamically modeling and grouping endpoints for edge networking |
| US11838305B2 (en) | 2017-08-08 | 2023-12-05 | Sentinel Labs Israel Ltd. | Methods, systems, and devices for dynamically modeling and grouping endpoints for edge networking |
| US11722506B2 (en) | 2017-08-08 | 2023-08-08 | Sentinel Labs Israel Ltd. | Methods, systems, and devices for dynamically modeling and grouping endpoints for edge networking |
| US11973781B2 (en) | 2017-08-08 | 2024-04-30 | Sentinel Labs Israel Ltd. | Methods, systems, and devices for dynamically modeling and grouping endpoints for edge networking |
| US11716341B2 (en) | 2017-08-08 | 2023-08-01 | Sentinel Labs Israel Ltd. | Methods, systems, and devices for dynamically modeling and grouping endpoints for edge networking |
| US11876819B2 (en) | 2017-08-08 | 2024-01-16 | Sentinel Labs Israel Ltd. | Methods, systems, and devices for dynamically modeling and grouping endpoints for edge networking |
| US11716342B2 (en) | 2017-08-08 | 2023-08-01 | Sentinel Labs Israel Ltd. | Methods, systems, and devices for dynamically modeling and grouping endpoints for edge networking |
| US12356195B2 (en)* | 2017-09-08 | 2025-07-08 | Telefonaktiebolaget Lm Ericsson (Publ) | Re-establishing a connection between a user controller device and a wireless device |
| US20200275280A1 (en)* | 2017-09-08 | 2020-08-27 | Telefonaktiebolaget Lm Ericsson (Publ) | Re-Establishing a Connection Between a User Controller Device and a Wireless Device |
| WO2019048052A1 (en)* | 2017-09-08 | 2019-03-14 | Telefonaktiebolaget Lm Ericsson (Publ) | Re-establishing a connection between a user controller device and a wireless device |
| US10747872B1 (en) | 2017-09-27 | 2020-08-18 | Fireeye, Inc. | System and method for preventing malware evasion |
| US10805346B2 (en) | 2017-10-01 | 2020-10-13 | Fireeye, Inc. | Phishing attack detection |
| US11665207B2 (en) | 2017-10-25 | 2023-05-30 | Extrahop Networks, Inc. | Inline secret sharing |
| US12069087B2 (en) | 2017-10-27 | 2024-08-20 | Google Llc | System and method for analyzing binary code for malware classification using artificial neural network techniques |
| US11108809B2 (en) | 2017-10-27 | 2021-08-31 | Fireeye, Inc. | System and method for analyzing binary code for malware classification using artificial neural network techniques |
| US11637859B1 (en) | 2017-10-27 | 2023-04-25 | Mandiant, Inc. | System and method for analyzing binary code for malware classification using artificial neural network techniques |
| US11755700B2 (en) | 2017-11-21 | 2023-09-12 | Group Ib, Ltd | Method for classifying user action sequence |
| US11949692B1 (en) | 2017-12-28 | 2024-04-02 | Google Llc | Method and system for efficient cybersecurity analysis of endpoint events |
| US11240275B1 (en) | 2017-12-28 | 2022-02-01 | Fireeye Security Holdings Us Llc | Platform and method for performing cybersecurity analyses employing an intelligence hub with a modular architecture |
| US11005860B1 (en) | 2017-12-28 | 2021-05-11 | Fireeye, Inc. | Method and system for efficient cybersecurity analysis of endpoint events |
| US11271955B2 (en) | 2017-12-28 | 2022-03-08 | Fireeye Security Holdings Us Llc | Platform and method for retroactive reclassification employing a cybersecurity-based global data store |
| US10958684B2 (en) | 2018-01-17 | 2021-03-23 | Group Ib, Ltd | Method and computer device for identifying malicious web resources |
| US11122061B2 (en) | 2018-01-17 | 2021-09-14 | Group IB TDS, Ltd | Method and server for determining malicious files in network traffic |
| US11503044B2 (en) | 2018-01-17 | 2022-11-15 | Group IB TDS, Ltd | Method computing device for detecting malicious domain names in network traffic |
| US10762352B2 (en) | 2018-01-17 | 2020-09-01 | Group Ib, Ltd | Method and system for the automatic identification of fuzzy copies of video content |
| US11475670B2 (en) | 2018-01-17 | 2022-10-18 | Group Ib, Ltd | Method of creating a template of original video content |
| US11451580B2 (en) | 2018-01-17 | 2022-09-20 | Trust Ltd. | Method and system of decentralized malware identification |
| US11463299B2 (en) | 2018-02-07 | 2022-10-04 | Extrahop Networks, Inc. | Ranking alerts based on network monitoring |
| US11470115B2 (en) | 2018-02-09 | 2022-10-11 | Attivo Networks, Inc. | Implementing decoys in a network environment |
| US11431744B2 (en) | 2018-02-09 | 2022-08-30 | Extrahop Networks, Inc. | Detection of denial of service attacks |
| US11888897B2 (en) | 2018-02-09 | 2024-01-30 | SentinelOne, Inc. | Implementing decoys in a network environment |
| US12341814B2 (en) | 2018-02-09 | 2025-06-24 | SentinelOne, Inc. | Implementing decoys in a network environment |
| US11005779B2 (en) | 2018-02-13 | 2021-05-11 | Trust Ltd. | Method of and server for detecting associated web resources |
| US10826931B1 (en) | 2018-03-29 | 2020-11-03 | Fireeye, Inc. | System and method for predicting and mitigating cybersecurity system misconfigurations |
| US11856011B1 (en) | 2018-03-30 | 2023-12-26 | Musarubra Us Llc | Multi-vector malware detection data sharing system for improved detection |
| US11558401B1 (en) | 2018-03-30 | 2023-01-17 | Fireeye Security Holdings Us Llc | Multi-vector malware detection data sharing system for improved detection |
| US10956477B1 (en) | 2018-03-30 | 2021-03-23 | Fireeye, Inc. | System and method for detecting malicious scripts through natural language processing modeling |
| US11003773B1 (en) | 2018-03-30 | 2021-05-11 | Fireeye, Inc. | System and method for automatically generating malware detection rule recommendations |
| US11075930B1 (en) | 2018-06-27 | 2021-07-27 | Fireeye, Inc. | System and method for detecting repetitive cybersecurity attacks constituting an email campaign |
| US11314859B1 (en) | 2018-06-27 | 2022-04-26 | FireEye Security Holdings, Inc. | Cyber-security system and method for detecting escalation of privileges within an access token |
| US11882140B1 (en) | 2018-06-27 | 2024-01-23 | Musarubra Us Llc | System and method for detecting repetitive cybersecurity attacks constituting an email campaign |
| US11228491B1 (en) | 2018-06-28 | 2022-01-18 | Fireeye Security Holdings Us Llc | System and method for distributed cluster configuration monitoring and management |
| US11316900B1 (en) | 2018-06-29 | 2022-04-26 | FireEye Security Holdings Inc. | System and method for automatically prioritizing rules for cyber-threat detection and mitigation |
| US11496378B2 (en) | 2018-08-09 | 2022-11-08 | Extrahop Networks, Inc. | Correlating causes and effects associated with network activity |
| US11182473B1 (en) | 2018-09-13 | 2021-11-23 | Fireeye Security Holdings Us Llc | System and method for mitigating cyberattacks against processor operability by a guest process |
| US11763004B1 (en) | 2018-09-27 | 2023-09-19 | Fireeye Security Holdings Us Llc | System and method for bootkit detection |
| US20240031406A1 (en)* | 2018-10-09 | 2024-01-25 | Penten Pty Ltd | Methods and systems for honeyfile creation, deployment and management |
| US11153351B2 (en) | 2018-12-17 | 2021-10-19 | Trust Ltd. | Method and computing device for identifying suspicious users in message exchange systems |
| US12074887B1 (en) | 2018-12-21 | 2024-08-27 | Musarubra Us Llc | System and method for selectively processing content after identification and removal of malicious content |
| US11368475B1 (en) | 2018-12-21 | 2022-06-21 | Fireeye Security Holdings Us Llc | System and method for scanning remote services to locate stored objects with malware |
| US11743290B2 (en) | 2018-12-21 | 2023-08-29 | Fireeye Security Holdings Us Llc | System and method for detecting cyberattacks impersonating legitimate sources |
| US11176251B1 (en) | 2018-12-21 | 2021-11-16 | Fireeye, Inc. | Determining malware via symbolic function hash analysis |
| US11431749B2 (en) | 2018-12-28 | 2022-08-30 | Trust Ltd. | Method and computing device for generating indication of malicious web resources |
| US11985149B1 (en) | 2018-12-31 | 2024-05-14 | Musarubra Us Llc | System and method for automated system for triage of cybersecurity threats |
| US11601444B1 (en) | 2018-12-31 | 2023-03-07 | Fireeye Security Holdings Us Llc | Automated system for triage of customer issues |
| US11934498B2 (en) | 2019-02-27 | 2024-03-19 | Group Ib, Ltd | Method and system of user identification |
| US11310238B1 (en) | 2019-03-26 | 2022-04-19 | FireEye Security Holdings, Inc. | System and method for retrieval and analysis of operational data from customer, cloud-hosted virtual resources |
| US11750618B1 (en) | 2019-03-26 | 2023-09-05 | Fireeye Security Holdings Us Llc | System and method for retrieval and analysis of operational data from customer, cloud-hosted virtual resources |
| US11677786B1 (en) | 2019-03-29 | 2023-06-13 | Fireeye Security Holdings Us Llc | System and method for detecting and protecting against cybersecurity attacks on servers |
| US12248563B1 (en) | 2019-03-30 | 2025-03-11 | Musarubra Us Llc | System and method for cybersecurity analyzer update and concurrent management system |
| US11636198B1 (en) | 2019-03-30 | 2023-04-25 | Fireeye Security Holdings Us Llc | System and method for cybersecurity analyzer update and concurrent management system |
| US12282863B2 (en) | 2019-04-10 | 2025-04-22 | F.A.C.C.T. Antifraud Llc | Method and system of user identification by a sequence of opened user interface windows |
| US11580218B2 (en) | 2019-05-20 | 2023-02-14 | Sentinel Labs Israel Ltd. | Systems and methods for executable code detection, automatic feature extraction and position independent code detection |
| US12169556B2 (en) | 2019-05-20 | 2024-12-17 | Sentinel Labs Israel Ltd. | Systems and methods for executable code detection, automatic feature extraction and position independent code detection |
| US11790079B2 (en) | 2019-05-20 | 2023-10-17 | Sentinel Labs Israel Ltd. | Systems and methods for executable code detection, automatic feature extraction and position independent code detection |
| US11706233B2 (en) | 2019-05-28 | 2023-07-18 | Extrahop Networks, Inc. | Detecting injection attacks using passive network monitoring |
| US12063229B1 (en) | 2019-06-24 | 2024-08-13 | Google Llc | System and method for associating cybersecurity intelligence to cyberthreat actors through a similarity matrix |
| US11258806B1 (en) | 2019-06-24 | 2022-02-22 | Mandiant, Inc. | System and method for automatically associating cybersecurity intelligence to cyberthreat actors |
| US11556640B1 (en) | 2019-06-27 | 2023-01-17 | Mandiant, Inc. | Systems and methods for automated cybersecurity analysis of extracted binary string sets |
| US11392700B1 (en) | 2019-06-28 | 2022-07-19 | Fireeye Security Holdings Us Llc | System and method for supporting cross-platform data verification |
| US12445458B1 (en) | 2019-06-28 | 2025-10-14 | Google Llc | System and method for identifying malicious hosts prior to commencement of a cyber-attack |
| US12309192B2 (en) | 2019-07-29 | 2025-05-20 | Extrahop Networks, Inc. | Modifying triage information based on network monitoring |
| US11438247B2 (en) | 2019-08-05 | 2022-09-06 | Extrahop Networks, Inc. | Correlating network traffic that crosses opaque endpoints |
| US11652714B2 (en) | 2019-08-05 | 2023-05-16 | Extrahop Networks, Inc. | Correlating network traffic that crosses opaque endpoints |
| US11388072B2 (en)* | 2019-08-05 | 2022-07-12 | Extrahop Networks, Inc. | Correlating network traffic that crosses opaque endpoints |
| US12200013B2 (en) | 2019-08-07 | 2025-01-14 | Musarubra Us Llc | System and method for detecting cyberattacks impersonating legitimate sources |
| US11463465B2 (en) | 2019-09-04 | 2022-10-04 | Extrahop Networks, Inc. | Automatic determination of user roles and asset types based on network monitoring |
| US11886585B1 (en) | 2019-09-27 | 2024-01-30 | Musarubra Us Llc | System and method for identifying and mitigating cyberattacks through malicious position-independent code execution |
| US12388865B2 (en) | 2019-09-30 | 2025-08-12 | Google Llc | System and method for surfacing cyber-security threats with a self-learning recommendation engine |
| US11729134B2 (en) | 2019-09-30 | 2023-08-15 | Palo Alto Networks, Inc. | In-line detection of algorithmically generated domains |
| US11637862B1 (en) | 2019-09-30 | 2023-04-25 | Mandiant, Inc. | System and method for surfacing cyber-security threats with a self-learning recommendation engine |
| US11526608B2 (en) | 2019-12-05 | 2022-12-13 | Group IB TDS, Ltd | Method and system for determining affiliation of software to software families |
| US11250129B2 (en) | 2019-12-05 | 2022-02-15 | Group IB TDS, Ltd | Method and system for determining affiliation of software to software families |
| US12355816B2 (en) | 2019-12-17 | 2025-07-08 | Extrahop Networks, Inc. | Automated preemptive polymorphic deception |
| US12107888B2 (en) | 2019-12-17 | 2024-10-01 | Extrahop Networks, Inc. | Automated preemptive polymorphic deception |
| US11356470B2 (en) | 2019-12-19 | 2022-06-07 | Group IB TDS, Ltd | Method and system for determining network vulnerabilities |
| US11888875B1 (en) | 2019-12-24 | 2024-01-30 | Musarubra Us Llc | Subscription and key management system |
| US11522884B1 (en) | 2019-12-24 | 2022-12-06 | Fireeye Security Holdings Us Llc | Subscription and key management system |
| US11838300B1 (en) | 2019-12-24 | 2023-12-05 | Musarubra Us Llc | Run-time configurable cybersecurity system |
| US11436327B1 (en) | 2019-12-24 | 2022-09-06 | Fireeye Security Holdings Us Llc | System and method for circumventing evasive code for cyberthreat detection |
| US12363145B1 (en) | 2019-12-24 | 2025-07-15 | Musarubra Us Llc | Run-time configurable cybersecurity system |
| US11947669B1 (en) | 2019-12-24 | 2024-04-02 | Musarubra Us Llc | System and method for circumventing evasive code for cyberthreat detection |
| US12417282B2 (en) | 2020-01-27 | 2025-09-16 | F.A.C.C.T. Network Security Llc | Method and system for detecting malicious infrastructure |
| US12229259B2 (en) | 2020-02-21 | 2025-02-18 | F.A.C.C.T. Network Security Llc | Method and system for detecting malicious files in a non-isolated environment |
| US11151581B2 (en) | 2020-03-04 | 2021-10-19 | Group-Ib Global Private Limited | System and method for brand protection based on search results |
| US12135786B2 (en) | 2020-03-10 | 2024-11-05 | F.A.C.C.T. Network Security Llc | Method and system for identifying malware |
| US11475090B2 (en) | 2020-07-15 | 2022-10-18 | Group-Ib Global Private Limited | Method and system for identifying clusters of affiliated web resources |
| US11847223B2 (en) | 2020-08-06 | 2023-12-19 | Group IB TDS, Ltd | Method and system for generating a list of indicators of compromise |
| US11463466B2 (en) | 2020-09-23 | 2022-10-04 | Extrahop Networks, Inc. | Monitoring encrypted network traffic |
| US11558413B2 (en) | 2020-09-23 | 2023-01-17 | Extrahop Networks, Inc. | Monitoring encrypted network traffic |
| US11748083B2 (en) | 2020-12-16 | 2023-09-05 | Sentinel Labs Israel Ltd. | Systems, methods and devices for device fingerprinting and automatic deployment of software in a computing network using a peer-to-peer approach |
| US12423078B2 (en) | 2020-12-16 | 2025-09-23 | Sentinel Labs Israel Ltd. | Systems, methods and devices for device fingerprinting and automatic deployment of software in a computing network using a peer-to-peer approach |
| US11579857B2 (en) | 2020-12-16 | 2023-02-14 | Sentinel Labs Israel Ltd. | Systems, methods and devices for device fingerprinting and automatic deployment of software in a computing network using a peer-to-peer approach |
| CN112788043A (en)* | 2021-01-18 | 2021-05-11 | 广州锦行网络科技有限公司 | Honeypot system service self-adaption method and self-adaption service honeypot system |
| US11947572B2 (en) | 2021-03-29 | 2024-04-02 | Group IB TDS, Ltd | Method and system for clustering executable files |
| US11985147B2 (en) | 2021-06-01 | 2024-05-14 | Trust Ltd. | System and method for detecting a cyberattack |
| US12088606B2 (en) | 2021-06-10 | 2024-09-10 | F.A.C.C.T. Network Security Llc | System and method for detection of malicious network resources |
| US12225030B2 (en) | 2021-06-18 | 2025-02-11 | Extrahop Networks, Inc. | Identifying network entities based on beaconing activity |
| US12259967B2 (en) | 2021-07-13 | 2025-03-25 | SentinelOne, Inc. | Preserving DLL hooks |
| US11899782B1 (en) | 2021-07-13 | 2024-02-13 | SentinelOne, Inc. | Preserving DLL hooks |
| US11916771B2 (en) | 2021-09-23 | 2024-02-27 | Extrahop Networks, Inc. | Combining passive network analysis and active probing |
| US11843606B2 (en) | 2022-03-30 | 2023-12-12 | Extrahop Networks, Inc. | Detecting abnormal data access based on data similarity |
| US20240250968A1 (en)* | 2023-01-19 | 2024-07-25 | Palo Alto Networks, Inc. | Detecting scanning and attacking uniform resource locators in network traffic |
| US12445481B1 (en) | 2023-04-17 | 2025-10-14 | Musarubra Us Llc | Distributed malware detection system and submission workflow thereof |
| US12445410B2 (en) | 2023-06-21 | 2025-10-14 | Palo Alto Networks, Inc. | In-line detection of algorithmically generated domains |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| US10587636B1 (en) | System and method for bot detection | |
| US8561177B1 (en) | Systems and methods for detecting communication channels of bots | |
| US8204984B1 (en) | Systems and methods for detecting encrypted bot command and control communication channels | |
| US10165000B1 (en) | Systems and methods for malware attack prevention by intercepting flows of information | |
| US9027135B1 (en) | Prospective client identification using malware attack detection | |
| US10068091B1 (en) | System and method for malware containment | |
| US8539582B1 (en) | Malware containment and security analysis on connection | |
| US10200384B1 (en) | Distributed systems and methods for automatically detecting unknown bots and botnets | |
| US10097573B1 (en) | Systems and methods for malware defense | |
| Nawrocki et al. | A survey on honeypot software and data analysis | |
| US9356950B2 (en) | Evaluating URLS for malicious content | |
| US9942270B2 (en) | Database deception in directory services | |
| US7953969B2 (en) | Reduction of false positive reputations through collection of overrides from customer deployments | |
| EP2147390B1 (en) | Detection of adversaries through collection and correlation of assessments | |
| US9654494B2 (en) | Detecting and marking client devices | |
| US20170026387A1 (en) | Monitoring access of network darkspace | |
| Hindy et al. | A taxonomy of malicious traffic for intrusion detection systems | |
| Simkhada et al. | Security threats/attacks via botnets and botnet detection & prevention techniques in computer networks: a review | |
| US20250240313A1 (en) | Large language model (llm) powered detection reasoning solution | |
| Tang et al. | Concept, characteristics and defending mechanism of worms | |
| Durairaj et al. | A study on securing cloud environment from DDoS attack to preserve data availability | |
| Goel et al. | Botnets: the anatomy of a case | |
| Singh et al. | Communication based vulnerabilities and script based solvabilities | |
| Pandya | The enemy (The intruder’s Genesis) | |
| Durairaj et al. | THE INTERNATIONAL JOURNAL OF SCIENCE & TECHNOLEDGE |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| AS | Assignment | Owner name:FIREEYE, INC., CALIFORNIA Free format text:ASSIGNMENT OF ASSIGNORS INTEREST;ASSIGNORS:AZIZ, ASHAR;LAI, WEI-LUNG;MANNI, JAYARAMAN;REEL/FRAME:020247/0497 Effective date:20071130 | |
| STCF | Information on status: patent grant | Free format text:PATENTED CASE | |
| FPAY | Fee payment | Year of fee payment:4 | |
| FEPP | Fee payment procedure | Free format text:7.5 YR SURCHARGE - LATE PMT W/IN 6 MO, LARGE ENTITY (ORIGINAL EVENT CODE: M1555); ENTITY STATUS OF PATENT OWNER: LARGE ENTITY | |
| MAFP | Maintenance fee payment | Free format text:PAYMENT OF MAINTENANCE FEE, 8TH YEAR, LARGE ENTITY (ORIGINAL EVENT CODE: M1552); ENTITY STATUS OF PATENT OWNER: LARGE ENTITY Year of fee payment:8 | |
| AS | Assignment | Owner name:UBS AG, STAMFORD BRANCH, AS COLLATERAL AGENT, CONNECTICUT Free format text:SECOND LIEN PATENT SECURITY AGREEMENT;ASSIGNOR:FIREEYE SECURITY HOLDINGS US LLC;REEL/FRAME:057772/0791 Effective date:20211008 Owner name:UBS AG, STAMFORD BRANCH, AS COLLATERAL AGENT, CONNECTICUT Free format text:FIRST LIEN PATENT SECURITY AGREEMENT;ASSIGNOR:FIREEYE SECURITY HOLDINGS US LLC;REEL/FRAME:057772/0681 Effective date:20211008 | |
| AS | Assignment | Owner name:FIREEYE SECURITY HOLDINGS US LLC, CALIFORNIA Free format text:ASSIGNMENT OF ASSIGNORS INTEREST;ASSIGNOR:MANDIANT, INC.;REEL/FRAME:061447/0039 Effective date:20211008 | |
| AS | Assignment | Owner name:MANDIANT, INC., CALIFORNIA Free format text:CHANGE OF NAME;ASSIGNOR:FIREEYE, INC.;REEL/FRAME:062636/0058 Effective date:20211004 | |
| AS | Assignment | Owner name:STG PARTNERS, LLC, CALIFORNIA Free format text:SECURITY INTEREST;ASSIGNORS:MUSARUBRA US LLC;SKYHIGH SECURITY LLC;REEL/FRAME:068324/0731 Effective date:20240730 | |
| AS | Assignment | Owner name:MUSARUBRA US LLC, TEXAS Free format text:MERGER;ASSIGNOR:FIREEYE SECURITY HOLDINGS US LLC;REEL/FRAME:068581/0279 Effective date:20230509 | |
| AS | Assignment | Owner name:MAGENTA SECURITY HOLDINGS LLC, TEXAS Free format text:INTELLECTUAL PROPERTY ASSIGNMENT AGREEMENT;ASSIGNOR:MAGENTA SECURITY INTERMEDIATE HOLDINGS LLC;REEL/FRAME:068656/0920 Effective date:20240814 Owner name:MAGENTA SECURITY HOLDINGS LLC, TEXAS Free format text:ASSIGNMENT OF ASSIGNORS INTEREST;ASSIGNOR:MAGENTA SECURITY INTERMEDIATE HOLDINGS LLC;REEL/FRAME:068657/0843 Effective date:20240814 Owner name:MAGENTA SECURITY INTERMEDIATE HOLDINGS LLC, TEXAS Free format text:ASSIGNMENT OF ASSIGNORS INTEREST;ASSIGNOR:MUSARUBRA US LLC;REEL/FRAME:068657/0764 Effective date:20240814 Owner name:UBS AG, STAMFORD BRANCH, AS COLLATERAL AGENT, CONNECTICUT Free format text:FIRST LIEN PATENT SECURITY AGREEMENT;ASSIGNORS:MAGENTA SECURITY HOLDINGS LLC;SKYHIGH SECURITY LLC;REEL/FRAME:068657/0666 Effective date:20240814 Owner name:MAGENTA SECURITY INTERMEDIATE HOLDINGS LLC, TEXAS Free format text:INTELLECTUAL PROPERTY ASSIGNMENT AGREEMENT;ASSIGNOR:MUSARUBRA US LLC;REEL/FRAME:068656/0098 Effective date:20240814 | |
| AS | Assignment | Owner name:SKYHIGH SECURITY LLC, TEXAS Free format text:RELEASE BY SECURED PARTY;ASSIGNOR:STG PARTNERS, LLC;REEL/FRAME:068671/0435 Effective date:20240814 Owner name:MUSARUBRA US LLC, TEXAS Free format text:RELEASE BY SECURED PARTY;ASSIGNOR:STG PARTNERS, LLC;REEL/FRAME:068671/0435 Effective date:20240814 | |
| MAFP | Maintenance fee payment | Free format text:PAYMENT OF MAINTENANCE FEE, 12TH YEAR, LARGE ENTITY (ORIGINAL EVENT CODE: M1553); ENTITY STATUS OF PATENT OWNER: LARGE ENTITY Year of fee payment:12 |