US20040073617A1 - Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail - Google Patents
Hash-based systems and methods for detecting and preventing transmission of unwanted e-mailDownload PDFInfo
- Publication number
- US20040073617A1 US20040073617A1US10/654,771US65477103AUS2004073617A1US 20040073617 A1US20040073617 A1US 20040073617A1US 65477103 AUS65477103 AUS 65477103AUS 2004073617 A1US2004073617 A1US 2004073617A1
- Authority
- US
- United States
- Prior art keywords
- hash
- mail message
- hash values
- message
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Abandoned
Links
Images
Classifications
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/14—Network architectures or network communication protocols for network security for detecting or protecting against malicious traffic
- H04L63/1441—Countermeasures against malicious traffic
- H04L63/145—Countermeasures against malicious traffic the attack involving the propagation of malware through the network, e.g. viruses, trojans or worms
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/50—Monitoring users, programs or devices to maintain the integrity of platforms, e.g. of processors, firmware or operating systems
- G06F21/55—Detecting local intrusion or implementing counter-measures
- G06F21/56—Computer malware detection or handling, e.g. anti-virus arrangements
- G06F21/562—Static detection
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L51/00—User-to-user messaging in packet-switching networks, transmitted according to store-and-forward or real-time protocols, e.g. e-mail
- H04L51/21—Monitoring or handling of messages
- H04L51/212—Monitoring or handling of messages using filtering or selective blocking
Definitions
- the present inventionrelates generally to network security and, more particularly, to systems and methods for detecting and/or preventing the transmission of unwanted e-mails, such as e-mails containing worms and viruses, including polymorphic worms and viruses, and unsolicited commercial e-mails.
- unwanted e-mailssuch as e-mails containing worms and viruses, including polymorphic worms and viruses, and unsolicited commercial e-mails.
- Systems and methods consistent with the present inventionaddress this and other needs by providing a new defense that detects and prevents the transmission of unwanted (and potentially unwanted) e-mail, such as e-mails containing viruses, worms, and spam.
- a method for detecting transmission of potentially unwanted e-mail messagesincludes receiving e-mail messages and generating hash values based on one or more portions of the e-mail messages. The method further includes determining whether the generated hash values match hash values associated with prior e-mail messages. The method may also include determining that one of the e-mail messages is a potentially unwanted e-mail message when one or more of the generated hash values associated with the e-mail message match one or more of the hash values associated with the prior e-mail messages.
- a mail serverincludes one or more hash memories and a hash processor.
- the one or more hash memoriesis/are configured to store count values associated with hash values.
- the hash processoris configured to receive an e-mail message, hash one or more portions of the e-mail message to generate hash values, and increment the count values corresponding to the generated hash values.
- the hash processoris further configured to determine whether the e-mail message is a potentially unwanted e-mail message based on the incremented count values.
- a method for detecting transmission of unwanted e-mail messagesincludes receiving e-mail messages and detecting unwanted e-mail messages of the received e-mail messages based on hashes of previously received e-mail messages, where multiple hashes are performed on each of the e-mail messages.
- a method for detecting transmission of potentially unwanted e-mail messagesincludes receiving an e-mail message; generating hash values over blocks of the e-mail message, where the blocks include at least two of a main text portion, an attachment portion, and a header portion of the e-mail message; determining whether the generated hash values match hash values associated with prior e-mail messages; and determining that the e-mail message is a potentially unwanted e-mail message when one or more of the generated hash values associated with the email message match one or more of the hash values associated with the prior e-mail messages.
- a mail server in a network of cooperating mail serversincludes one or more hash memories and a hash processor.
- the one or more hash memoriesis/are configured to store information relating to hash values corresponding to previously-observed e-mails.
- the hash processoris configured to receive at least some of the hash values from another one or more of the cooperating mail servers and store information relating to the at least some of the hash values in at least one of the one or more hash memories.
- the hash processoris further configured to receive an e-mail message, hash one or more portions of the received e-mail message to generate hash values, determine whether the generated hash values match the hash values corresponding to previously-observed e-mails, and identify the received e-mail message as a potentially unwanted e-mail message when one or more of the generated hash values associated with the received e-mail message match one or more of the hash values corresponding to previously-observed e-mails.
- a mail serverincludes one or more hash memories and a hash processor.
- the one or more hash memoriesis/are configured to store count values associated with hash values.
- the hash processoris configured to receive e-mail messages, hash one or more portions of the received email messages to generate hash values, increment the count values corresponding to the generated hash values, as incremented count values, and generate suspicion scores for the received e-mail messages based on the incremented count values.
- a method for preventing transmission of unwanted e-mail messagesincludes receiving an e-mail message; generating hash values over portions of the e-mail message as the e-mail message is being received; and incrementally determining whether the generated hash values match hash values associated with prior e-mail messages.
- the methodfurther includes generating a suspicion score for the e-mail message based on the incremental determining; and rejecting the e-mail message when the suspicion score of the e-mail message is above a threshold.
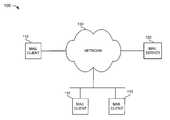
- FIG. 1is a diagram of a system in which systems and methods consistent with the present invention may be implemented
- FIG. 2is an exemplary diagram of the e-mail server of FIG. 1 according to an implementation consistent with the principles of the invention
- FIG. 3is an exemplary functional block diagram of the e-mail server of FIG. 2 according to an implementation consistent with the principles of the invention
- FIG. 4is an exemplary diagram of the hash processing block of FIG. 3 according to an implementation consistent with the principles of the invention.
- FIGS. 5 A- 5 Eare flowcharts of exemplary processing for detecting and/or preventing transmission of an unwanted e-mail message, such as an e-mail containing a virus or worm, including a polymorphic virus or worm, or an unsolicited commercial e-mail, according to an implementation consistent with the principles of the invention.
- an unwanted e-mail messagesuch as an e-mail containing a virus or worm, including a polymorphic virus or worm, or an unsolicited commercial e-mail, according to an implementation consistent with the principles of the invention.
- Systems and methods consistent with the present inventionprovide virus, worm, and unsolicited e-mail detection and/or prevention in e-mail servers. Placing these features in e-mail servers provides a number of new advantages, including the ability to align hash blocks to crucial boundaries found in e-mail messages and eliminate certain counter-measures by the attacker, such as using small Internet Protocol (IP) fragments to limit the detectable content in each packet. It also allows these features to relate e-mail header fields with the potentially-harmful segment of the message (usually an “attachment”), and decode common file-packing and encoding formats that might otherwise make a virus or worm undetectable by the packet-based technique (e.g., “.zip files”).
- IPInternet Protocol
- the ability to detect replicated content in the network at points where large quantities of traffic are presentis obtained.
- the e-mail servermay detect unknown, as well as known, viruses and worms.
- These featuresmay also be applied to detect potential unsolicited commercial e-mail (“spam”).
- E-mail servers for major Internet Service Providersmay process a million e-mail messages a day, or more, in a single server.
- ISPsInternet Service Providers
- viruses and wormsWhen viruses and worms are active in the network, a substantial fraction of this e-mail may actually be traffic generated by the virus or worm.
- an e-mail servermay have dozens to thousands of examples of a single e-mail-borne virus pass through it in a day, offering an excellent opportunity to determine the relationships between e-mail messages and detect replicated content (a feature that is indicative of virus/worm propagation) and spam, among other, more legitimate traffic (such as traffic from legitimate mailing lists).
- Systems and methods consistent with the principles of the inventionprovide mechanisms to detect and stop e-mail-borne viruses and worms before the addressed user receives them, in an environment where the virus is still inert.
- Current e-mail serversdo not normally execute any code in the e-mail being transported, so they are not usually subject to virus/worm infections from the content of the e-mails they process—though, they may be subject to infection via other forms of attack.
- spamBesides e-mail-borne viruses and worms, another common problem found in e-mail is mass-e-mailing of unsolicited commercial e-mail, colloquially referred to as “spam.” It is estimated that perhaps 25%-50% of all e-mail messages now received for delivery by major ISP e-mail servers is spam.
- Users of network e-mail servicesare desirous of mechanisms to block e-mail containing viruses or worms from reaching their machines (where the virus or worm may easily do harm before the user realizes its presence). Users are also desirous of mechanisms to block unsolicited commercial e-mail that consumes their time and resources.
- FIG. 1is a diagram of an exemplary system 100 in which systems and methods consistent with the present invention may be implemented.
- System 100includes mail clients 110 connected to a mail server 120 via a network 130 . Connections made in system 100 may be via wired, wireless, and/or optical communication paths. While FIG. 1 shows three mail clients 110 and a single mail server 120 , there can be more or fewer clients and servers in other implementations consistent with the principles of the invention.
- Network 130may facilitate communication between mail clients 110 and mail server 120 .
- network 130may include a collection of network devices, such as routers or switches, that transfer data between mail clients 110 and mail server 120 .
- network 130may take the form of a wide area network, a local area network, an intranet, the Internet, a public telephone network, a different type of network, or a combination of networks.
- Mail clients 110may include personal computers, laptops, personal digital assistants, or other types of wired or wireless devices that are capable of interacting with mail server 120 to receive e-mails. In another implementation, clients 110 may include software operating upon one of these devices. Client 110 may present e-mails to a user via a graphical user interface.
- Mail server 120may include a computer or another device that is capable of providing e-mail services for mail clients 110 .
- server 120may include software operating upon one of these devices.
- FIG. 2is an exemplary diagram of mail server 120 according to an implementation consistent with the principles of the invention.
- Server 120may include bus 210 , processor 220 , main memory 230 , read only memory (ROM) 240 , storage device 250 , input device 260 , output device 270 , and communication interface 280 .
- Bus 210permits communication among the components of server 120 .
- Processor 220may include any type of conventional processor or microprocessor that interprets and executes instructions.
- Main memory 230may include a random access memory (RAM) or another type of dynamic storage device that stores information and instructions for execution by processor 220 .
- ROM 240may include a conventional ROM device or another type of static storage device that stores static information and instructions for use by processor 220 .
- Storage device 250may include a magnetic and/or optical recording medium and its corresponding drive.
- Input device 260may include one or more conventional mechanisms that permit an operator to input information to server 120 , such as a keyboard, a mouse, a pen, voice recognition and/or biometric mechanisms, etc.
- Output device 270may include one or more conventional mechanisms that output information to the operator, such as a display, a printer, a pair of speakers, etc.
- Communication interface 280may include any transceiver-like mechanism that enables server 120 to communicate with other devices and/or systems.
- communication interface 280may include mechanisms for communicating with another device or system via a network, such as network 130 .
- server 120provides e-mail services to clients 110 , while detecting unwanted e-mails and/or preventing unwanted e-mails from reaching clients 110 .
- Server 120may perform these tasks in response to processor 220 executing sequences of instructions contained in, for example, memory 230 . These instructions may be read into memory 230 from another computer-readable medium, such as storage device 250 or a carrier wave, or from another device via communication interface 280 .
- FIG. 3is an exemplary functional block diagram of mail server 120 according to an implementation consistent with the principles of the invention.
- Server 120may include a Simple Mail Transfer Protocol (SMTP) block 310 , a Post Office Protocol (POP) block 320 , an Internet Message Access Protocol (IMAP) block 330 , and a hash processing block 340 .
- SMTPSimple Mail Transfer Protocol
- POPPost Office Protocol
- IMAPInternet Message Access Protocol
- hash processing block 340a hash processing block 340 .
- SMTP block 310may permit mail server 120 to communicate with other mail servers connected to network 130 or another network.
- SMTPis designed to efficiently and reliably transfer e-mail across networks.
- SMTPdefines the interaction between mail servers to facilitate the transfer of e-mail even when the mail servers are implemented on different types of computers or running different operating systems.
- POP block 320may permit mail clients 110 to retrieve e-mail from mail server 120 .
- POP block 320may be designed to always receive incoming e-mail. POP block 320 may then hold e-mail for mail clients 110 until mail clients 110 connect to download them.
- IMAP block 330may provide another mechanism by which mail clients 110 can retrieve e-mail from mail server 120 .
- IMAP block 330may permit mail clients 110 to access remote e-mail as if the e-mail was local to mail clients 1110 .
- Hash processing block 340may interact with SMTP block 310 , POP block 320 , and/or IMAP block 330 to detect and prevent transmission of unwanted e-mail, such as e-mails containing viruses or worms and unsolicited commercial e-mail (spam).
- unwanted e-mailsuch as e-mails containing viruses or worms and unsolicited commercial e-mail (spam).
- FIG. 4is an exemplary diagram of hash processing block 340 according to an implementation consistent with the principles of the invention.
- Hash processing block 340may include hash processor 410 and one or more hash memories 420 .
- Hash processor 410may include a conventional processor, an application specific integrated circuit (ASIC), a field-programmable gate array (FPGA), or some other type of device that generates one or more representations for each received e-mail and records the e-mail representations in hash memory 420 .
- ASICapplication specific integrated circuit
- FPGAfield-programmable gate array
- An e-mail representationwill likely not be a copy of the entire e-mail, but rather it may include a portion of the e-mail or some unique value representative of the e-mail. For example, a fixed width number may be computed across portions of the e-mail in a manner that allows the entire e-mail to be identified.
- a 32-bit hash value, or digestmay be computed across portions of each e-mail. Then the hash value may be stored in hash memory 420 or may be used as an index, or address, into hash memory 420 . Using the hash value, or an index derived therefrom, results in efficient use of hash memory 420 while still allowing the content of each e-mail passing through mail server 120 to be identified.
- Systems and methods consistent with the present inventionmay use any storage scheme that records information about one or more portions of each e-mail in a space-efficient fashion, that can definitively determine if a portion of an e-mail has not been observed, and that can respond positively (i.e., in a predictable way) when a portion of an e-mail has been observed.
- systems and methods consistent with the present inventioncan use virtually any technique for deriving representations of portions of e-mails, the remaining discussion will use hash values as exemplary representations of portions of e-mails received by mail server 120 .
- hash processor 410may hash one or more portions of a received e-mail to produce a hash value used to facilitate hash-based detection.
- hash processor 410may hash one or more of the main text within the message body, any attachments, and one or more header fields, such as sender-related fields (e.g., “From:,” “Sender:,” “Reply-To:,” “Return-Path:,” and “Error-To:”).
- Hash processor 410may perform one or more hashes on each of the e-mail portions using the same or different hash functions.
- hash processor 410may use the hash results of the hash operation to recognize duplicate occurrences of e-mails and raise a warning if the duplicate e-mail occurrences arrive within a short period of time and raise their level of suspicion above some threshold. It may also be possible to use the hash results for tracing the path of an unwanted e-mail through the network.
- Each hash valuemay be determined by taking an input block of data and processing it to obtain a numerical value that represents the given input data. Suitable hash functions are readily known in the art and will not be discussed in detail herein. Examples of hash functions include the Cyclic Redundancy Check (CRC) and Message Digest 5 (MD 5 ). The resulting hash value, also referred to as a message digest or hash digest, may include a fixed length value. The hash value may serve as a signature for the data over which it was computed.
- CRCCyclic Redundancy Check
- MD 5Message Digest 5
- the hash valuealso referred to as a message digest or hash digest, may include a fixed length value.
- the hash valuemay serve as a signature for the data over which it was computed.
- the hash valueessentially acts as a fingerprint identifying the input block of data over which it was computed. Unlike fingerprints, however, there is a chance that two very different pieces of data will hash to the same value, resulting in a hash collision.
- An acceptable hash functionshould provide a good distribution of values over a variety of data inputs in order to prevent these collisions. Because collisions occur when different input blocks result in the same hash value, an ambiguity may arise when attempting to associate a result with a particular input.
- Hash processor 410may store a representation of each e-mail it observes in hash memory 420 .
- Hash processor 410may store the actual hash values as the e-mail representations or it may use other techniques for minimizing storage requirements associated with retaining hash values and other information associated therewith.
- a technique for minimizing storage requirementsmay use one or more arrays or Bloom filters.
- hash processor 410may use the hash value as an index for addressing an array within hash memory 420 .
- the hash valueserves as the address location into the array.
- a count valuemay be incremented at the respective storage location, thus, indicating that a particular hash value, and hence a particular e-mail portion, has been seen by hash processor 410 .
- the count valueis associated with an 8-bit counter with a maximum value that sticks at 255 . While counter arrays are described by way of example, it will be appreciated by those skilled in the relevant art, that other storage techniques may be employed without departing from the spirit of the invention.
- Hash memory 420may store a suspicion count that is used to determine the overall suspiciousness of an e-mail message. For example, the count value (described above) may be compared to a threshold, and the suspicion count for the e-mail may be incremented if the threshold is exceeded. Hence, there may be a direct relationship between the count value and the suspicion count, and it may be possible for the two values to be the same. The larger the suspicion count, the more important the hit should be considered in determining the overall suspiciousness of the packet. Alternatively, the suspicion count can be combined in a “scoring function” with values from this or other hash blocks in the same message in order to determine whether the message should be considered suspicious.
- hash memory 420it is not enough, however, for hash memory 420 to simply identify that an e-mail contains content that has been seen recently. There are many legitimate sources (e.g., e-mail list servers) that produce multiple copies of the same message, addressed to multiple recipients. Similarly, individual users often e-mail messages to a group of people and, thus, multiple copies might be seen if several recipients happen to receive their mail from the same server. Also, people often forward copies of received messages to friends or co-workers.
- virus/worm authorstypically try to minimize the replicated content in each copy of the virus/worm, in order to not be detected by existing virus and worm detection technology that depends on detecting fixed sequences of bytes in a known virus or worm.
- These mutable viruses/wormsare usually known as polymorphic, and the attacker's goal is to minimize the recognizability of the virus or worm by scrambling each copy in a different way.
- the virus or wormto remain viable, however, a small part of it can be mutable in only a relatively small number of ways, because some of its code must be immediately-executable by the victim's computer, and that limits the mutation and obscurement possibilities for the critical initial code part.
- multiple hash memories 420can be employed, with separate hash memories 420 being used for specific sub-parts of a standard e-mail message.
- the outputs of different ones of hash memories 420can then be combined in an overall “scoring” or classification function to determine whether the message is undesirable or legitimate, and possibly estimate the probability that it belongs to a particular class of traffic, such as a virus/worm message, spam, e-mail list message, normal user-to-user message.
- hashing of certain individual e-mail header fields into field-specific hash memories 420may be useful.
- header fields for which this may be helpfulare: (1) various sender-related fields, such as “From:”, “Sender:”, “Reply-To:”, “Return-Path:” and “Error-To:”; (2) the “To:” field (often a fixed value for a mailing list, frequently missing or idiosyncratic in spam messages); and (3) the last few “Received:” headers (i.e., the earliest ones, since they are normally added at the top of the message), excluding any obvious timestamp data. It may also be useful to hash a combination of the “From:” field and the e-mail address of the recipient (transferred as part of the SMTP mail-transfer protocol, and not necessarily found in the message itself).
- hash memories 420may be pre-loaded with knowledge of known good or bad traffic.
- known viruses and spam contente.g., the infamous “Craig Shergold letter” or many pyramid swindle letters
- known legitimate mailing listscan be added to a “From:” hash memory 420 that passes traffic without further examination.
- hash memories 420may fill up and the possibility of overflowing an existing count value increases.
- the risk of overflowing a count valuemay be reduced if the counter arrays are periodically flushed to other storage media, such as a magnetic disk drive, optical media, solid state drive, or the like.
- the counter arraysmay be slowly and incrementally erased.
- a time-tablemay be established for flushing/erasing the counter arrays.
- the flushing/erasing cyclecan be reduced by computing hash values only for a subset of the e-mails received by mail server 120 . While this approach reduces the flushing/erasing cycle, it increases the possibility that a target e-mail may be missed (i.e., a hash value is not computed over a portion of it).
- Non-zero storage locations within hash memories 420may be decremented periodically rather than being erased. This may ensure that the “random noise” from normal e-mail traffic would not remain in a counter array indefinitely. Replicated traffic (e.g., e-mails containing a virus/worm that are propagating repeatedly across the network), however, would normally cause the relevant storage locations to stay substantially above the “background noise” level.
- One way to decrement the count values in the counter array fairlyis to keep a total count, for each hash memory 420 , of every time one of the count values is incremented. After this total count reaches some threshold value (probably in the millions), for every time a count value is incremented in hash memory 420 , another count value gets decremented.
- One way to pick the count value to decrementis to keep a counter, as a decrement pointer, that simply iterates through the storage locations sequentially.
- a decrement operationEvery time a decrement operation is performed, the following may done: (a) examine the candidate count value to be decremented and if non-zero, decrement it and increment the decrement pointer to the next storage location; and (b) if the candidate count value is zero, then examine each sequentially-following storage location until a non-zero count value is found, decrement that count value, and advance the decrement pointer to the following storage location.
- a variation of this techniquemay include randomly selecting a count value to decrement, rather than processing them cyclically. In this variation, if the chosen count value is already zero, then another one could be picked randomly, or the count values in the storage locations following the initially-chosen one could be examined in series, until a non-zero count value is found.
- FIGS. 5 A- 5 Eare flowcharts of exemplary processing for detecting and/or preventing transmission of unwanted e-mail, such as an e-mail containing a virus or worm, including a polymorphic virus or worm, or an unsolicited commercial e-mail (spam), according to an implementation consistent with the principles of the invention.
- the processing of FIGS. 5 A- 5 Ewill be described in terms of a series of acts that may be performed by mail server 120 . In implementations consistent with the principles of the invention, some of the acts may be optional and/or performed in an order different than that described. In other implementations, different acts may be substituted for described acts or added to the process.
- Processingmay begin when hash processor 410 (FIG. 4) receives, or otherwise observes, an e-mail message (act 502 ) (FIG. 5A).
- Hash processor 410may hash the main text of the message body, excluding any attachments (act 504 ).
- hash processor 410may perform one or more conventional hashes covering one or more portions, or all, of the main text.
- hash processor 410may perform hash functions on fixed or variable sized blocks of the main text. It may be beneficial for hash processor 410 to perform multiple hashes on each of the blocks using the same or different hash functions.
- HTMLHyperText Markup Language
- e-mailwhere spammers often insert random text strings in HTML comments between or within words of the text.
- polymorphic spambecause it attempts to make each message appear unique.
- This method for evading detectionmight otherwise defeat the hash detection technique, or other string-matching techniques.
- removing all HTML comments from the message before hashingit may be desirable.
- Hash processor 410may also hash any attachments, after first attempting to expand them if they appear to be known types of compressed files (e.g., “zip” files) (act 506 ).
- hash processor 410may perform one or more conventional hashes covering one or more portions, or all, of the attachment.
- hash processor 410may perform hash functions on fixed or variable sized blocks of the attachment. It may be beneficial for hash processor 410 to perform multiple hashes on each of the blocks using the same or different hash functions.
- Hash processor 410may compare the main text and attachment hashes with known viruses, worms, or spam content in a hash memory 420 that is pre-loaded with information from known viruses, worms, and spam content (acts 508 and 510 ). If there are any hits in this hash memory 420 , there is a probability that the e-mail message contains a virus or worm or is spam.
- a known polymorphic virusmay have only a small number of hashes that match in this hash memory 420 , out of the total number of hash blocks in the message.
- a non-polymorphic virusmay have a very high fraction of the hash blocks hit in hash memory 420 . For this reason, storage locations within hash memory 420 that contain entries from polymorphic viruses or worms may be given more weight during the pre-loading process, such as by giving them a high initial suspicion count value.
- a high fraction of hits in this hash memory 420may cause the message to be marked as a probable known virus/worm or spam.
- the e-mail messagecan be sidetracked for remedial action, as described below.
- a message with a significant “score” from polymorphic virus/worm hash value hitsmay or may not be a virus/worm instance, and may be sidetracked for further investigation, or marked as suspicious before forwarding to the recipient. An additional check may also be made to determine the level of suspicion.
- hash processor 410may hash a concatenation of the From and To header fields of the e-mail message (act 512 ) (FIG. 5B). Hash processor 410 may then check the suspicion counts in hash memories 420 for the hashes of the main text, any attachments, and the concatenated From/To (act 514 ). Hash processor 410 may determine whether the main text or attachment suspicion count is significantly higher than the From/To suspicion count (act 516 ). If so, then the content is appearing much more frequently outside the messages between this set of users (which might otherwise be due to an e-mail exchange with repeated message quotations) and, thus, is much more suspicious.
- hash processor 410may take remedial action (act 518 ).
- the remedial action takenmight take different forms, which may be programmable or determined by an operator of mail server 120 .
- hash processor 410may discard the e-mail. This is not recommended for anything but virtually-certain virus/worm/spam identification, such as a perfect match to a known virus.
- hash processor 410may mark the e-mail with a warning in the message body, in an additional header, or other user-visible annotation, and allow the user to deal with it when it is downloaded.
- a variant of this optionis to request the user to send back a reply message to the server, classifying the suspect message as either spam or a mailing list.
- the mailing list source addresscan be added to the “known legitimate mailing lists” hash memory 420 .
- hash processor 410may subject the e-mail to more sophisticated (and possibly more resource-consuming) detection algorithms to make a more certain determination. This is recommended for potential unknown viruses/worms or possible detection of a polymorphic virus/worm.
- hash processor 410may hold the e-mail message in a special area and create a special e-mail message to notify the user of the held message (probably including From and Subject fields). Hash processor 410 may also give instructions on how to retrieve the message.
- hash processor 410may mark the e-mail message with its suspicion score result, but leave it queued for the user's retrieval. If the user's quota would overflow when a new message arrives, the score of the incoming message and the highest score of the queued messages are compared. If the highest queued message has a score above a settable threshold, and the new message's score is lower than the threshold, the queued message with the highest score may be deleted from the queue to make room for the new message. Otherwise, if the new message has a score above the threshold, it may be discarded or “bounced” (e.g., the sending e-mail server is told to hold the message and retry it later). Alternatively, if it is desired to never bounce incoming messages, mail server 120 may accept the incoming message into the user's queue and repeatedly delete messages with the highest suspicion score from the queue until the total is below the user's quota again.
- hash processor 410may apply hash-based functions as the e-mail message starts arriving from the sending server and determine the message's suspicion score incrementally as the message is read in. If the message has a high-enough suspicion score (above a threshold) during the early part of the message, mail server 120 may reject the message, optionally with either a “retry later” or a “permanent refusal” result to the sending server (which one is used may be determined by settable thresholds applied to the total suspicion score, and possibly other factors, such as server load). This results in the unwanted e-mail using up less network bandwidth and receiving server resources, and penalizes servers sending unwanted mail, relative to those that do not.
- hash processor 410may determine whether the main text or any attachment has significant replicated content (non-zero or high suspicion count values for many hash blocks in the text/attachment content in all storage locations of hash memories 420 ) (act 520 ) (FIG. 5A). If not, the message is probably a normal user-to-user e-mail. These types of messages may be “passed” without further examination. When appropriate, hash processor 410 may also record the generated hash values by incrementing the suspicion count value in the corresponding storage locations in hash memory 420 .
- hash processor 410may check one or more portions of the e-mail message against known legitimate mailing lists within hash memory 420 (act 522 ) (FIG. 5C). For example, hash processor 410 may hash the From or Sender fields of the e-mail message and compare it/them to known legitimate mailing lists within hash memory 420 . Hash processor 410 may also determine whether the e-mail actually appears to originate from the correct source for the mailing list by examining, for example, the sequence of Received headers. Hash processor 410 may further examine a combination of the From or Sender fields and the recipient address to determine if the recipient has previously received e-mail from the sender.
- the messageis probably a legitimate mailing list duplicate and may be passed with no further examination.
- the mailing list serveremploys some kind of filtering to exclude unwanted e-mail (e.g., refusing to forward e-mail that does not originate with a known list recipient or refusing e-mail with attachments).
- hash processor 410may hash the sender-related fields (e.g., From, Sender, Reply-To) (act 526 ). Hash processor 410 may then determine the suspicion count for the sender-related hashes in hash memories 420 (act 528 ).
- sender-related fieldse.g., From, Sender, Reply-To
- Hash processor 410may then determine the suspicion count for the sender-related hashes in hash memories 420 (act 528 ).
- Hash processor 410may determine whether the suspicion counts for the sender-related hashes are similar to the suspicion count(s) for the main text hash(es) (act 530 ) (FIG. 5D). If both From and Sender fields are present, then the Sender field should match with roughly the same suspicion count value as the message body hash. The From field may or may not match. For a legitimate mailing list, it may be a legitimate mailing list that is not in the known legitimate mailing lists hash memory 420 (or in the case where there is no known legitimate mailing lists hash memory 420 ). If only the From field is present, it should match about as well as the message text for a mailing list. If none of the sender-related fields match as well as the message text, the e-mail message may be considered moderately suspicious (probably spam, with a variable and fictitious From address or the like).
- hash processor 410may hash the concatenation of the sender-related field with the highest suspicion count value and the e-mail recipient's address (act 532 ). Hash processor 410 may then check the suspicion count for the concatenation in a hash memory 420 used just for this check (act 534 ). If it matches with a significant suspicion count value (act 536 ) (FIG. 5E), then the recipient has recently received multiple messages from this source, which makes it probable that it is a mailing list. The e-mail message may then be passed without further examination.
- the message text or attachmentsare mostly replicated (e.g., greater than 90% of the hash blocks), but with mostly low suspicion count values in hash memory 420 (act 538 ), then the message is probably a case of a small-scale replication of a single message to multiple recipients. In this case, the e-mail message may then be passed without further examination.
- the message text or attachmentscontain some significant degree of content replication (say, greater than 50% of the hash blocks) and at least some of the hash values have high suspicion count values in hash memory 420 (act 540 ), then the message is fairly likely to be a virus/worm or spam. A virus or worm should be considered more likely if the high-count matches are in an attachment. If the highly-replicated content is in the message text, then the message is more likely to be spam, though it is possible that e-mail text employing a scripting language (e.g., Java script) might also contain a virus.
- a scripting languagee.g., Java script
- the replicationis in the message text, and the suspicion count is substantially higher for the message text than for the From field, the message is likely to be spam (because spammers generally vary the From field to evade simpler spam filters).
- a similar checkcan be made for the concatenation of the From and To header fields, except that in this case, it is most suspicious if the From/To hash misses (finds a zero suspicion count), indicating that the sender does not ordinarily send e-mail to that recipient, making it unlikely to be a mailing list, and very likely to be a spammer (because they normally employ random or fictitious From addresses).
- hash processor 410may take remedial action (act 542 ).
- remedial actionact 542
- the particular type of action taken by hash processor 410may vary as described above.
- Systems and methods consistent with the present inventionprovide mechanisms within an e-mail server to detect and/or prevent transmission of unwanted e-mail, such as e-mail containing viruses or worms, including polymorphic viruses and worms, and unsolicited commercial e-mail (spam).
- unwanted e-mailsuch as e-mail containing viruses or worms, including polymorphic viruses and worms, and unsolicited commercial e-mail (spam).
- Implementation of a hash-based detection mechanism in an e-mail server at the e-mail message levelprovides advantages over a packet-based implementation in a router or other network node device. For example, the entire e-mail message has been re-assembled, both at the packet level (i.e., IP fragment re-assembly) and at the application level (multiple packets into a complete e-mail message). Also, the hashing algorithm can be applied more intelligently to specific parts of the e-mail message (e.g., header fields, message body, and attachments). Attachments that have been compressed for transport (e.g., “.zip” files) can be expanded for inspection. Without doing this, a polymorphic virus could easily hide inside such files with no repeatable hash signature visible at the packet transport level.
- the entire messageis likely to be longer than a single packet, thereby reducing the probability of false alarms (possibly due to insufficient hash-block sample size and too few hash blocks per packet) and increasing the probability of correct identification of a virus/worm (more hash blocks will match per message than per packet, since packets will be only parts of the entire message).
- hash blockscan be intelligently aligned with fields of the e-mail message, such as the start of the message body, or the start of an attachment block. This results in faster detection of duplicate contents than if the blocks are randomly aligned (as is the case when the method is applied to individual packets).
- E-mail-borne malicious codesuch as viruses and worms
- E-mail-borne malicious codealso usually includes a text message designed to cause the user to read the message and/or perform some other action that will activate the malicious code. It is harder for such text to be polymorphic, because automatic scrambling of the user-visible text will either render it suspicious-looking, or will be very limited in variability. This fact, combined with the ability to start a hash block at the start of the message text by parsing the e-mail header, reduces the variability in hash signatures of the message, making it easier to detect with fewer examples seen.
- the ability to extract and hash specific headers from an e-mail message separatelymay be used to help classify the type of replicated content the message body carries. Because many legitimate cases of message replication exist (e.g., topical mailing lists, such as Yahoo Groups), intelligent parsing and hashing of the message headers is very useful to reduce the false alarm rate, and to increase the accuracy of detection of real viruses, worms, and spam.
- many legitimate cases of message replication existe.g., topical mailing lists, such as Yahoo Groups
- intelligent parsing and hashing of the message headersis very useful to reduce the false alarm rate, and to increase the accuracy of detection of real viruses, worms, and spam.
- This detection techniquecompared to others which might extract and save fixed strings to be searched for in other pieces of e-mail, includes hash-based filters that are one-way functions (i.e., it is possible, given a piece of text, to determine if it has been seen before in another message). Given the state data contained in the filter, however, it is virtually impossible to reconstruct a prior message, or any piece of a prior message, that has been passed through the filter previously. Thus, this technique can maintain the privacy of e-mail, without retaining any information that can be attributed to a specific sender or receiver.
- systems and methodshave been described with regard to a mail server.
- the systems and methods described hereinmay be used within other devices, such as a mail client.
- the mail clientmay periodically obtain suspicion count values for its hash memory from one or more network devices, such as a mail server.
- blocksthat perform one or more functions. These blocks may include hardware, such as an ASIC or a FPGA, software, or a combination of hardware and software.
Landscapes
- Engineering & Computer Science (AREA)
- Computer Security & Cryptography (AREA)
- General Engineering & Computer Science (AREA)
- Computer Hardware Design (AREA)
- Computer Networks & Wireless Communication (AREA)
- General Health & Medical Sciences (AREA)
- Virology (AREA)
- Software Systems (AREA)
- Theoretical Computer Science (AREA)
- Health & Medical Sciences (AREA)
- Signal Processing (AREA)
- Physics & Mathematics (AREA)
- General Physics & Mathematics (AREA)
- Computing Systems (AREA)
- Data Exchanges In Wide-Area Networks (AREA)
- Information Transfer Between Computers (AREA)
Abstract
Description
- This application claims priority under 35 U.S.C. § 119 based on U.S. Provisional Application No. 60/407,975, filed Sep. 5, 2002, the disclosure of which is incorporated herein by reference. This application is also a continuation-in-part of U.S. patent application Ser. No. 10/251,403, filed Sep. 20, 2002, which claims priority under 35 U.S.C. § 119 based on U.S. Provisional Application No. 60/341,462, filed Dec. 14, 2001, both of which are incorporated herein by reference. This application is also a continuation-in-part of U.S. patent application Ser. No. 09/881,145, and U.S. patent application Ser. No. 09/881,074, both of which were filed on Jun. 14, 2001, and both of which claim priority under 35 U.S.C. § 119 based on U.S. Provisional Application No. 60/212,425, filed Jun. 19, 2000, all of which are incorporated herein by reference.[0001]
- 1. Field of the Invention[0002]
- The present invention relates generally to network security and, more particularly, to systems and methods for detecting and/or preventing the transmission of unwanted e-mails, such as e-mails containing worms and viruses, including polymorphic worms and viruses, and unsolicited commercial e-mails.[0003]
- 2. Description of Related Art[0004]
- Availability of low cost computers, high speed networking products, and readily available network connections has helped fuel the proliferation of the Internet. This proliferation has caused the Internet to become an essential tool for both the business community and private individuals. Dependence on the Internet arises, in part, because the Internet makes it possible for multitudes of users to access vast amounts of information and perform remote transactions expeditiously and efficiently. Along with the rapid growth of the Internet have come problems arising from attacks from within the network and the shear volume of commercial e-mail. As the size of the Internet continues to grow, so does the threat posed to users of the Internet.[0005]
- Many of the problems take the form of e-mail. Viruses and worms often masquerade within e-mail messages for execution by unsuspecting e-mail recipients. Unsolicited commercial e-mail, or “spam,” is another burdensome type of e-mail because it wastes both the time and resources of the e-mail recipient.[0006]
- Existing techniques for detecting viruses, worms, and spam examine each e-mail message individually. In the case of viruses and worms, this typically means examining attachments for byte-strings found in known viruses and worms (possibly after uncompressing or de-archiving attached files), or simulating execution of the attachment in a “safe” compartment and examining its behaviors. Similarly, existing spam filters usually examine a single e-mail message looking for heuristic traits commonly found in unsolicited commercial e-mail, such as an abundance of Uniform Resource Locators (URLs), heavy use of all-capital-letter words, use of colored text or large fonts, and the like, and then “score” the message based on the number and types of such traits found. Both the anti-virus and the anti-spam techniques can demand significant processing of each message, adding to the resource burden imposed by unwanted email. Neither technique makes use of information collected from other recent messages.[0007]
- Thus, there is need for an efficient technique that can quickly detect viruses, worms, and spam in e-mail messages arriving at e-mail servers, possibly by using information contained in multiple recent messages to detect unwanted mail more quickly and efficiently.[0008]
- Systems and methods consistent with the present invention address this and other needs by providing a new defense that detects and prevents the transmission of unwanted (and potentially unwanted) e-mail, such as e-mails containing viruses, worms, and spam.[0009]
- In accordance with an aspect of the invention as embodied and broadly described herein, a method for detecting transmission of potentially unwanted e-mail messages is provided. The method includes receiving e-mail messages and generating hash values based on one or more portions of the e-mail messages. The method further includes determining whether the generated hash values match hash values associated with prior e-mail messages. The method may also include determining that one of the e-mail messages is a potentially unwanted e-mail message when one or more of the generated hash values associated with the e-mail message match one or more of the hash values associated with the prior e-mail messages.[0010]
- In accordance with another aspect of the invention, a mail server includes one or more hash memories and a hash processor. The one or more hash memories is/are configured to store count values associated with hash values. The hash processor is configured to receive an e-mail message, hash one or more portions of the e-mail message to generate hash values, and increment the count values corresponding to the generated hash values. The hash processor is further configured to determine whether the e-mail message is a potentially unwanted e-mail message based on the incremented count values.[0011]
- In accordance with yet another aspect of the invention, a method for detecting transmission of unwanted e-mail messages is provided. The method includes receiving e-mail messages and detecting unwanted e-mail messages of the received e-mail messages based on hashes of previously received e-mail messages, where multiple hashes are performed on each of the e-mail messages.[0012]
- In accordance with a further aspect of the invention, a method for detecting transmission of potentially unwanted e-mail messages is provided. The method includes receiving an e-mail message; generating hash values over blocks of the e-mail message, where the blocks include at least two of a main text portion, an attachment portion, and a header portion of the e-mail message; determining whether the generated hash values match hash values associated with prior e-mail messages; and determining that the e-mail message is a potentially unwanted e-mail message when one or more of the generated hash values associated with the email message match one or more of the hash values associated with the prior e-mail messages.[0013]
- In accordance with another aspect of the invention, a mail server in a network of cooperating mail servers is provided. The mail server includes one or more hash memories and a hash processor. The one or more hash memories is/are configured to store information relating to hash values corresponding to previously-observed e-mails. The hash processor is configured to receive at least some of the hash values from another one or more of the cooperating mail servers and store information relating to the at least some of the hash values in at least one of the one or more hash memories. The hash processor is further configured to receive an e-mail message, hash one or more portions of the received e-mail message to generate hash values, determine whether the generated hash values match the hash values corresponding to previously-observed e-mails, and identify the received e-mail message as a potentially unwanted e-mail message when one or more of the generated hash values associated with the received e-mail message match one or more of the hash values corresponding to previously-observed e-mails.[0014]
- In accordance with yet another aspect of the invention, a mail server is provided. The mail server includes one or more hash memories and a hash processor. The one or more hash memories is/are configured to store count values associated with hash values. The hash processor is configured to receive e-mail messages, hash one or more portions of the received email messages to generate hash values, increment the count values corresponding to the generated hash values, as incremented count values, and generate suspicion scores for the received e-mail messages based on the incremented count values.[0015]
- In accordance with a further aspect of the invention, a method for preventing transmission of unwanted e-mail messages is provided. The method includes receiving an e-mail message; generating hash values over portions of the e-mail message as the e-mail message is being received; and incrementally determining whether the generated hash values match hash values associated with prior e-mail messages. The method further includes generating a suspicion score for the e-mail message based on the incremental determining; and rejecting the e-mail message when the suspicion score of the e-mail message is above a threshold.[0016]
- The accompanying drawings, which are incorporated in and constitute a part of this specification, illustrate the invention and, together with the description, explain the invention. In the drawings,[0017]
- FIG. 1 is a diagram of a system in which systems and methods consistent with the present invention may be implemented;[0018]
- FIG. 2 is an exemplary diagram of the e-mail server of FIG. 1 according to an implementation consistent with the principles of the invention;[0019]
- FIG. 3 is an exemplary functional block diagram of the e-mail server of FIG. 2 according to an implementation consistent with the principles of the invention;[0020]
- FIG. 4 is an exemplary diagram of the hash processing block of FIG. 3 according to an implementation consistent with the principles of the invention; and[0021]
- FIGS.[0022]5A-5E are flowcharts of exemplary processing for detecting and/or preventing transmission of an unwanted e-mail message, such as an e-mail containing a virus or worm, including a polymorphic virus or worm, or an unsolicited commercial e-mail, according to an implementation consistent with the principles of the invention.
- The following detailed description of the invention refers to the accompanying drawings. The same reference numbers in different drawings may identify the same or similar elements. Also, the following detailed description does not limit the invention. Instead, the scope of the invention is defined by the appended claims and equivalents.[0023]
- Systems and methods consistent with the present invention provide virus, worm, and unsolicited e-mail detection and/or prevention in e-mail servers. Placing these features in e-mail servers provides a number of new advantages, including the ability to align hash blocks to crucial boundaries found in e-mail messages and eliminate certain counter-measures by the attacker, such as using small Internet Protocol (IP) fragments to limit the detectable content in each packet. It also allows these features to relate e-mail header fields with the potentially-harmful segment of the message (usually an “attachment”), and decode common file-packing and encoding formats that might otherwise make a virus or worm undetectable by the packet-based technique (e.g., “.zip files”).[0024]
- By placing these features within an e-mail server, the ability to detect replicated content in the network at points where large quantities of traffic are present is obtained. By relating many otherwise-independent messages and finding common factors, the e-mail server may detect unknown, as well as known, viruses and worms. These features may also be applied to detect potential unsolicited commercial e-mail (“spam”).[0025]
- E-mail servers for major Internet Service Providers (ISPs) may process a million e-mail messages a day, or more, in a single server. When viruses and worms are active in the network, a substantial fraction of this e-mail may actually be traffic generated by the virus or worm. Thus, an e-mail server may have dozens to thousands of examples of a single e-mail-borne virus pass through it in a day, offering an excellent opportunity to determine the relationships between e-mail messages and detect replicated content (a feature that is indicative of virus/worm propagation) and spam, among other, more legitimate traffic (such as traffic from legitimate mailing lists).[0026]
- Systems and methods consistent with the principles of the invention provide mechanisms to detect and stop e-mail-borne viruses and worms before the addressed user receives them, in an environment where the virus is still inert. Current e-mail servers do not normally execute any code in the e-mail being transported, so they are not usually subject to virus/worm infections from the content of the e-mails they process—though, they may be subject to infection via other forms of attack.[0027]
- Besides e-mail-borne viruses and worms, another common problem found in e-mail is mass-e-mailing of unsolicited commercial e-mail, colloquially referred to as “spam.” It is estimated that perhaps 25%-50% of all e-mail messages now received for delivery by major ISP e-mail servers is spam.[0028]
- Users of network e-mail services are desirous of mechanisms to block e-mail containing viruses or worms from reaching their machines (where the virus or worm may easily do harm before the user realizes its presence). Users are also desirous of mechanisms to block unsolicited commercial e-mail that consumes their time and resources.[0029]
- Many commercial e-mail services put a limit on each user's e-mail accumulating at the server, and not yet downloaded to the customer's machine. If too much e-mail arrives between times when the user reads his e-mail, additional e-mail is either “bounced” (i.e., returned to the sender's e-mail server) or even simply discarded, both of which events can seriously inconvenience the user. Because the user has no control over arriving e-mail due to e-mail-borne viruses/worms, or spam, it is a relatively common occurrence that the user's e-mail quota overflows due to unwanted and potentially harmful messages. Similarly, the authors of e-mail-borne viruses, as well as senders of spam, have no reason to limit the size of their messages. As a result, these messages are often much larger than legitimate e-mail messages, thereby increasing the risks of such denial of service to the user by overflowing the per-user e-mail quota.[0030]
- Users are not the only group inconvenienced by spam and e-mail-borne viruses and worms. Because these types of unwanted e-mail can form a substantial fraction, even a majority, of e-mail traffic in the Internet, for extended periods of time, ISPs typically must add extra resources to handle a peak e-mail load that would otherwise be about half as large. This ratio of unwanted-to-legitimate e-mail traffic appears to be growing daily. Systems and methods consistent with the principles of the invention provide mechanisms to detect and discard unwanted e-mail in network e-mail servers.[0031]
- FIG. 1 is a diagram of an[0032]
exemplary system 100 in which systems and methods consistent with the present invention may be implemented.System 100 includesmail clients 110 connected to amail server 120 via anetwork 130. Connections made insystem 100 may be via wired, wireless, and/or optical communication paths. While FIG. 1 shows threemail clients 110 and asingle mail server 120, there can be more or fewer clients and servers in other implementations consistent with the principles of the invention. - [0033]
Network 130 may facilitate communication betweenmail clients 110 andmail server 120. Typically,network 130 may include a collection of network devices, such as routers or switches, that transfer data betweenmail clients 110 andmail server 120. In an implementation consistent with the present invention,network 130 may take the form of a wide area network, a local area network, an intranet, the Internet, a public telephone network, a different type of network, or a combination of networks. - [0034]
Mail clients 110 may include personal computers, laptops, personal digital assistants, or other types of wired or wireless devices that are capable of interacting withmail server 120 to receive e-mails. In another implementation,clients 110 may include software operating upon one of these devices.Client 110 may present e-mails to a user via a graphical user interface. - [0035]
Mail server 120 may include a computer or another device that is capable of providing e-mail services formail clients 110. In another implementation,server 120 may include software operating upon one of these devices. - FIG. 2 is an exemplary diagram of[0036]
mail server 120 according to an implementation consistent with the principles of the invention.Server 120 may includebus 210,processor 220,main memory 230, read only memory (ROM)240,storage device 250,input device 260,output device 270, andcommunication interface 280.Bus 210 permits communication among the components ofserver 120. - [0037]
Processor 220 may include any type of conventional processor or microprocessor that interprets and executes instructions.Main memory 230 may include a random access memory (RAM) or another type of dynamic storage device that stores information and instructions for execution byprocessor 220.ROM 240 may include a conventional ROM device or another type of static storage device that stores static information and instructions for use byprocessor 220.Storage device 250 may include a magnetic and/or optical recording medium and its corresponding drive. - [0038]
Input device 260 may include one or more conventional mechanisms that permit an operator to input information toserver 120, such as a keyboard, a mouse, a pen, voice recognition and/or biometric mechanisms, etc.Output device 270 may include one or more conventional mechanisms that output information to the operator, such as a display, a printer, a pair of speakers, etc.Communication interface 280 may include any transceiver-like mechanism that enablesserver 120 to communicate with other devices and/or systems. For example,communication interface 280 may include mechanisms for communicating with another device or system via a network, such asnetwork 130. - As will be described in detail below,[0039]
server 120, consistent with the present invention, provides e-mail services toclients 110, while detecting unwanted e-mails and/or preventing unwanted e-mails from reachingclients 110.Server 120 may perform these tasks in response toprocessor 220 executing sequences of instructions contained in, for example,memory 230. These instructions may be read intomemory 230 from another computer-readable medium, such asstorage device 250 or a carrier wave, or from another device viacommunication interface 280. - Execution of the sequences of instructions contained in[0040]
memory 230 may causeprocessor 220 to perform processes that will be described later. Alternatively, hardwired circuitry may be used in place of or in combination with software instructions to implement processes consistent with the present invention. Thus, processes performed byserver 120 are not limited to any specific combination of hardware circuitry and software. - FIG. 3 is an exemplary functional block diagram of[0041]
mail server 120 according to an implementation consistent with the principles of the invention.Server 120 may include a Simple Mail Transfer Protocol (SMTP) block310, a Post Office Protocol (POP) block320, an Internet Message Access Protocol (IMAP) block330, and ahash processing block 340. - SMTP block[0042]310 may permit
mail server 120 to communicate with other mail servers connected to network130 or another network. SMTP is designed to efficiently and reliably transfer e-mail across networks. SMTP defines the interaction between mail servers to facilitate the transfer of e-mail even when the mail servers are implemented on different types of computers or running different operating systems. - [0043]
POP block 320 may permitmail clients 110 to retrieve e-mail frommail server 120. POP block320 may be designed to always receive incoming e-mail. POP block320 may then hold e-mail formail clients 110 untilmail clients 110 connect to download them. - [0044]
IMAP block 330 may provide another mechanism by which mailclients 110 can retrieve e-mail frommail server 120. IMAP block330 may permitmail clients 110 to access remote e-mail as if the e-mail was local to mail clients1110. - [0045]
Hash processing block 340 may interact withSMTP block 310,POP block 320, and/or IMAP block330 to detect and prevent transmission of unwanted e-mail, such as e-mails containing viruses or worms and unsolicited commercial e-mail (spam). - FIG. 4 is an exemplary diagram of[0046]
hash processing block 340 according to an implementation consistent with the principles of the invention.Hash processing block 340 may includehash processor 410 and one ormore hash memories 420.Hash processor 410 may include a conventional processor, an application specific integrated circuit (ASIC), a field-programmable gate array (FPGA), or some other type of device that generates one or more representations for each received e-mail and records the e-mail representations inhash memory 420. - An e-mail representation will likely not be a copy of the entire e-mail, but rather it may include a portion of the e-mail or some unique value representative of the e-mail. For example, a fixed width number may be computed across portions of the e-mail in a manner that allows the entire e-mail to be identified.[0047]
- To further illustrate the use of representations, a 32-bit hash value, or digest, may be computed across portions of each e-mail. Then the hash value may be stored in[0048]
hash memory 420 or may be used as an index, or address, intohash memory 420. Using the hash value, or an index derived therefrom, results in efficient use ofhash memory 420 while still allowing the content of each e-mail passing throughmail server 120 to be identified. - Systems and methods consistent with the present invention may use any storage scheme that records information about one or more portions of each e-mail in a space-efficient fashion, that can definitively determine if a portion of an e-mail has not been observed, and that can respond positively (i.e., in a predictable way) when a portion of an e-mail has been observed. Although systems and methods consistent with the present invention can use virtually any technique for deriving representations of portions of e-mails, the remaining discussion will use hash values as exemplary representations of portions of e-mails received by[0049]
mail server 120. - In implementations consistent with the principles of the invention,[0050]
hash processor 410 may hash one or more portions of a received e-mail to produce a hash value used to facilitate hash-based detection. For example,hash processor 410 may hash one or more of the main text within the message body, any attachments, and one or more header fields, such as sender-related fields (e.g., “From:,” “Sender:,” “Reply-To:,” “Return-Path:,” and “Error-To:”).Hash processor 410 may perform one or more hashes on each of the e-mail portions using the same or different hash functions. - As described in more detail below,[0051]
hash processor 410 may use the hash results of the hash operation to recognize duplicate occurrences of e-mails and raise a warning if the duplicate e-mail occurrences arrive within a short period of time and raise their level of suspicion above some threshold. It may also be possible to use the hash results for tracing the path of an unwanted e-mail through the network. - Each hash value may be determined by taking an input block of data and processing it to obtain a numerical value that represents the given input data. Suitable hash functions are readily known in the art and will not be discussed in detail herein. Examples of hash functions include the Cyclic Redundancy Check (CRC) and Message Digest[0052]5 (MD5). The resulting hash value, also referred to as a message digest or hash digest, may include a fixed length value. The hash value may serve as a signature for the data over which it was computed.
- The hash value essentially acts as a fingerprint identifying the input block of data over which it was computed. Unlike fingerprints, however, there is a chance that two very different pieces of data will hash to the same value, resulting in a hash collision. An acceptable hash function should provide a good distribution of values over a variety of data inputs in order to prevent these collisions. Because collisions occur when different input blocks result in the same hash value, an ambiguity may arise when attempting to associate a result with a particular input.[0053]
- [0054]
Hash processor 410 may store a representation of each e-mail it observes inhash memory 420.Hash processor 410 may store the actual hash values as the e-mail representations or it may use other techniques for minimizing storage requirements associated with retaining hash values and other information associated therewith. A technique for minimizing storage requirements may use one or more arrays or Bloom filters. - Rather than storing the actual hash value, which can typically be on the order of 32 bits or more in length,[0055]
hash processor 410 may use the hash value as an index for addressing an array withinhash memory 420. In other words, whenhash processor 410 generates a hash value for a portion of an e-mail, the hash value serves as the address location into the array. At the address corresponding to the hash value, a count value may be incremented at the respective storage location, thus, indicating that a particular hash value, and hence a particular e-mail portion, has been seen byhash processor 410. In one implementation, the count value is associated with an 8-bit counter with a maximum value that sticks at255. While counter arrays are described by way of example, it will be appreciated by those skilled in the relevant art, that other storage techniques may be employed without departing from the spirit of the invention. - [0056]
Hash memory 420 may store a suspicion count that is used to determine the overall suspiciousness of an e-mail message. For example, the count value (described above) may be compared to a threshold, and the suspicion count for the e-mail may be incremented if the threshold is exceeded. Hence, there may be a direct relationship between the count value and the suspicion count, and it may be possible for the two values to be the same. The larger the suspicion count, the more important the hit should be considered in determining the overall suspiciousness of the packet. Alternatively, the suspicion count can be combined in a “scoring function” with values from this or other hash blocks in the same message in order to determine whether the message should be considered suspicious. - It is not enough, however, for[0057]
hash memory 420 to simply identify that an e-mail contains content that has been seen recently. There are many legitimate sources (e.g., e-mail list servers) that produce multiple copies of the same message, addressed to multiple recipients. Similarly, individual users often e-mail messages to a group of people and, thus, multiple copies might be seen if several recipients happen to receive their mail from the same server. Also, people often forward copies of received messages to friends or co-workers. - In addition, virus/worm authors typically try to minimize the replicated content in each copy of the virus/worm, in order to not be detected by existing virus and worm detection technology that depends on detecting fixed sequences of bytes in a known virus or worm. These mutable viruses/worms are usually known as polymorphic, and the attacker's goal is to minimize the recognizability of the virus or worm by scrambling each copy in a different way. For the virus or worm to remain viable, however, a small part of it can be mutable in only a relatively small number of ways, because some of its code must be immediately-executable by the victim's computer, and that limits the mutation and obscurement possibilities for the critical initial code part.[0058]
- In order to accomplish the proper classification of various types of legitimate and unwanted e-mail messages,[0059]
multiple hash memories 420 can be employed, withseparate hash memories 420 being used for specific sub-parts of a standard e-mail message. The outputs of different ones ofhash memories 420 can then be combined in an overall “scoring” or classification function to determine whether the message is undesirable or legitimate, and possibly estimate the probability that it belongs to a particular class of traffic, such as a virus/worm message, spam, e-mail list message, normal user-to-user message. - For e-mail following the Internet mail standard RFC 822 (and its various extensions), hashing of certain individual e-mail header fields into field-[0060]
specific hash memories 420 may be useful. Among the header fields for which this may be helpful are: (1) various sender-related fields, such as “From:”, “Sender:”, “Reply-To:”, “Return-Path:” and “Error-To:”; (2) the “To:” field (often a fixed value for a mailing list, frequently missing or idiosyncratic in spam messages); and (3) the last few “Received:” headers (i.e., the earliest ones, since they are normally added at the top of the message), excluding any obvious timestamp data. It may also be useful to hash a combination of the “From:” field and the e-mail address of the recipient (transferred as part of the SMTP mail-transfer protocol, and not necessarily found in the message itself). - Any or all of[0061]
hash memories 420 may be pre-loaded with knowledge of known good or bad traffic. For example, known viruses and spam content (e.g., the infamous “Craig Shergold letter” or many pyramid swindle letters) can be pre-hashed into therelevant hash memories 420, and/or periodically refreshed in the memory as part of a periodic “cleaning” process described below. Also, known legitimate mailing lists, such as mailing lists from legitimate e-mail list servers, can be added to a “From:”hash memory 420 that passes traffic without further examination. - Over time, hash[0062]
memories 420 may fill up and the possibility of overflowing an existing count value increases. The risk of overflowing a count value may be reduced if the counter arrays are periodically flushed to other storage media, such as a magnetic disk drive, optical media, solid state drive, or the like. Alternatively, the counter arrays may be slowly and incrementally erased. To facilitate this, a time-table may be established for flushing/erasing the counter arrays. If desired, the flushing/erasing cycle can be reduced by computing hash values only for a subset of the e-mails received bymail server 120. While this approach reduces the flushing/erasing cycle, it increases the possibility that a target e-mail may be missed (i.e., a hash value is not computed over a portion of it). - Non-zero storage locations within[0063]
hash memories 420 may be decremented periodically rather than being erased. This may ensure that the “random noise” from normal e-mail traffic would not remain in a counter array indefinitely. Replicated traffic (e.g., e-mails containing a virus/worm that are propagating repeatedly across the network), however, would normally cause the relevant storage locations to stay substantially above the “background noise” level. - One way to decrement the count values in the counter array fairly is to keep a total count, for each[0064]
hash memory 420, of every time one of the count values is incremented. After this total count reaches some threshold value (probably in the millions), for every time a count value is incremented inhash memory 420, another count value gets decremented. One way to pick the count value to decrement is to keep a counter, as a decrement pointer, that simply iterates through the storage locations sequentially. Every time a decrement operation is performed, the following may done: (a) examine the candidate count value to be decremented and if non-zero, decrement it and increment the decrement pointer to the next storage location; and (b) if the candidate count value is zero, then examine each sequentially-following storage location until a non-zero count value is found, decrement that count value, and advance the decrement pointer to the following storage location. - It may be important to avoid decrementing any counters below zero, while not biasing decrements unfairly. Because it may be assumed that the hash is random, this technique should not favor any particular storage location, since it visits each of them before starting over. This technique may be superior to a timer-based decrement because it keeps a fixed total count population across all of the storage locations, representing the most recent history of traffic, and is not subject to changes in behavior as the volume of traffic varies over time.[0065]
- A variation of this technique may include randomly selecting a count value to decrement, rather than processing them cyclically. In this variation, if the chosen count value is already zero, then another one could be picked randomly, or the count values in the storage locations following the initially-chosen one could be examined in series, until a non-zero count value is found.[0066]
- FIGS.[0067]5A-5E are flowcharts of exemplary processing for detecting and/or preventing transmission of unwanted e-mail, such as an e-mail containing a virus or worm, including a polymorphic virus or worm, or an unsolicited commercial e-mail (spam), according to an implementation consistent with the principles of the invention. The processing of FIGS.5A-5E will be described in terms of a series of acts that may be performed by
mail server 120. In implementations consistent with the principles of the invention, some of the acts may be optional and/or performed in an order different than that described. In other implementations, different acts may be substituted for described acts or added to the process. - Processing may begin when hash processor[0068]410 (FIG. 4) receives, or otherwise observes, an e-mail message (act502) (FIG. 5A).
Hash processor 410 may hash the main text of the message body, excluding any attachments (act504). When hashing the main text,hash processor 410 may perform one or more conventional hashes covering one or more portions, or all, of the main text. For example,hash processor 410 may perform hash functions on fixed or variable sized blocks of the main text. It may be beneficial forhash processor 410 to perform multiple hashes on each of the blocks using the same or different hash functions. - It may be desirable to pre-process the main text to remove attempts to fool pattern-matching mail filters. An example of this is HyperText Markup Language (HTML) e-mail, where spammers often insert random text strings in HTML comments between or within words of the text. Such e-mail may be referred to as “polymorphic spam” because it attempts to make each message appear unique. This method for evading detection might otherwise defeat the hash detection technique, or other string-matching techniques. Thus, removing all HTML comments from the message before hashing it may be desirable. It might also be useful to delete HTML tags from the message, or apply other specialized, but simple, pre-processing techniques to remove content not actually presented to the user. In general, this may be done in parallel with the hashing of the message text, since viruses and worms may be hidden in the non-visible content of the message text.[0069]
- [0070]
Hash processor 410 may also hash any attachments, after first attempting to expand them if they appear to be known types of compressed files (e.g., “zip” files) (act506). When hashing an attachment,hash processor 410 may perform one or more conventional hashes covering one or more portions, or all, of the attachment. For example,hash processor 410 may perform hash functions on fixed or variable sized blocks of the attachment. It may be beneficial forhash processor 410 to perform multiple hashes on each of the blocks using the same or different hash functions. - [0071]
Hash processor 410 may compare the main text and attachment hashes with known viruses, worms, or spam content in ahash memory 420 that is pre-loaded with information from known viruses, worms, and spam content (acts 508 and510). If there are any hits in thishash memory 420, there is a probability that the e-mail message contains a virus or worm or is spam. A known polymorphic virus may have only a small number of hashes that match in thishash memory 420, out of the total number of hash blocks in the message. A non-polymorphic virus may have a very high fraction of the hash blocks hit inhash memory 420. For this reason, storage locations withinhash memory 420 that contain entries from polymorphic viruses or worms may be given more weight during the pre-loading process, such as by giving them a high initial suspicion count value. - A high fraction of hits in this[0072]
hash memory 420 may cause the message to be marked as a probable known virus/worm or spam. In this case, the e-mail message can be sidetracked for remedial action, as described below. - A message with a significant “score” from polymorphic virus/worm hash value hits may or may not be a virus/worm instance, and may be sidetracked for further investigation, or marked as suspicious before forwarding to the recipient. An additional check may also be made to determine the level of suspicion.[0073]
- For example,[0074]
hash processor 410 may hash a concatenation of the From and To header fields of the e-mail message (act512) (FIG. 5B).Hash processor 410 may then check the suspicion counts inhash memories 420 for the hashes of the main text, any attachments, and the concatenated From/To (act514).Hash processor 410 may determine whether the main text or attachment suspicion count is significantly higher than the From/To suspicion count (act516). If so, then the content is appearing much more frequently outside the messages between this set of users (which might otherwise be due to an e-mail exchange with repeated message quotations) and, thus, is much more suspicious. - When this occurs,[0075]
hash processor 410 may take remedial action (act518). The remedial action taken might take different forms, which may be programmable or determined by an operator ofmail server 120. For example,hash processor 410 may discard the e-mail. This is not recommended for anything but virtually-certain virus/worm/spam identification, such as a perfect match to a known virus. - As an alternate technique,[0076]
hash processor 410 may mark the e-mail with a warning in the message body, in an additional header, or other user-visible annotation, and allow the user to deal with it when it is downloaded. For data that appears to be from an unknown mailing list, a variant of this option is to request the user to send back a reply message to the server, classifying the suspect message as either spam or a mailing list. In the latter case, the mailing list source address can be added to the “known legitimate mailing lists”hash memory 420. - As another technique,[0077]
hash processor 410 may subject the e-mail to more sophisticated (and possibly more resource-consuming) detection algorithms to make a more certain determination. This is recommended for potential unknown viruses/worms or possible detection of a polymorphic virus/worm. - As yet another technique,[0078]
hash processor 410 may hold the e-mail message in a special area and create a special e-mail message to notify the user of the held message (probably including From and Subject fields).Hash processor 410 may also give instructions on how to retrieve the message. - As a further technique,[0079]
hash processor 410 may mark the e-mail message with its suspicion score result, but leave it queued for the user's retrieval. If the user's quota would overflow when a new message arrives, the score of the incoming message and the highest score of the queued messages are compared. If the highest queued message has a score above a settable threshold, and the new message's score is lower than the threshold, the queued message with the highest score may be deleted from the queue to make room for the new message. Otherwise, if the new message has a score above the threshold, it may be discarded or “bounced” (e.g., the sending e-mail server is told to hold the message and retry it later). Alternatively, if it is desired to never bounce incoming messages,mail server 120 may accept the incoming message into the user's queue and repeatedly delete messages with the highest suspicion score from the queue until the total is below the user's quota again. - As another technique,[0080]
hash processor 410 may apply hash-based functions as the e-mail message starts arriving from the sending server and determine the message's suspicion score incrementally as the message is read in. If the message has a high-enough suspicion score (above a threshold) during the early part of the message,mail server 120 may reject the message, optionally with either a “retry later” or a “permanent refusal” result to the sending server (which one is used may be determined by settable thresholds applied to the total suspicion score, and possibly other factors, such as server load). This results in the unwanted e-mail using up less network bandwidth and receiving server resources, and penalizes servers sending unwanted mail, relative to those that do not. - If the suspicion count for the main text or any attachment is not significantly higher than the From/To suspicion count (act[0081]516),
hash processor 410 may determine whether the main text or any attachment has significant replicated content (non-zero or high suspicion count values for many hash blocks in the text/attachment content in all storage locations of hash memories420) (act520) (FIG. 5A). If not, the message is probably a normal user-to-user e-mail. These types of messages may be “passed” without further examination. When appropriate,hash processor 410 may also record the generated hash values by incrementing the suspicion count value in the corresponding storage locations inhash memory 420. - If the message text is substantially replicated (e.g., greater than 90%),[0082]
hash processor 410 may check one or more portions of the e-mail message against known legitimate mailing lists within hash memory420 (act522) (FIG. 5C). For example,hash processor 410 may hash the From or Sender fields of the e-mail message and compare it/them to known legitimate mailing lists withinhash memory 420.Hash processor 410 may also determine whether the e-mail actually appears to originate from the correct source for the mailing list by examining, for example, the sequence of Received headers.Hash processor 410 may further examine a combination of the From or Sender fields and the recipient address to determine if the recipient has previously received e-mail from the sender. This is typical for mailing lists, but a typical of unwanted e-mail, which will normally not have access to the actual list of recipients for the mailing list. Failure of this examination may simply pass the message on, but mark it as “suspicious,” since the recipient may simply be a new subscriber to the mailing list, or the mailings may be infrequent enough to not persist in the hash counters between mailings. - If there is a match with a legitimate mailing list (act[0083]524), then the message is probably a legitimate mailing list duplicate and may be passed with no further examination. This assumes that the mailing list server employs some kind of filtering to exclude unwanted e-mail (e.g., refusing to forward e-mail that does not originate with a known list recipient or refusing e-mail with attachments).
- If there is no match with any legitimate mailing lists within[0084]
hash memory 420,hash processor 410 may hash the sender-related fields (e.g., From, Sender, Reply-To) (act526).Hash processor 410 may then determine the suspicion count for the sender-related hashes in hash memories420 (act528). - [0085]
Hash processor 410 may determine whether the suspicion counts for the sender-related hashes are similar to the suspicion count(s) for the main text hash(es) (act530) (FIG. 5D). If both From and Sender fields are present, then the Sender field should match with roughly the same suspicion count value as the message body hash. The From field may or may not match. For a legitimate mailing list, it may be a legitimate mailing list that is not in the known legitimate mailing lists hash memory420 (or in the case where there is no known legitimate mailing lists hash memory420). If only the From field is present, it should match about as well as the message text for a mailing list. If none of the sender-related fields match as well as the message text, the e-mail message may be considered moderately suspicious (probably spam, with a variable and fictitious From address or the like). - As an additional check,[0086]
hash processor 410 may hash the concatenation of the sender-related field with the highest suspicion count value and the e-mail recipient's address (act532).Hash processor 410 may then check the suspicion count for the concatenation in ahash memory 420 used just for this check (act534). If it matches with a significant suspicion count value (act536) (FIG. 5E), then the recipient has recently received multiple messages from this source, which makes it probable that it is a mailing list. The e-mail message may then be passed without further examination. - If the message text or attachments are mostly replicated (e.g., greater than 90% of the hash blocks), but with mostly low suspicion count values in hash memory[0087]420 (act538), then the message is probably a case of a small-scale replication of a single message to multiple recipients. In this case, the e-mail message may then be passed without further examination.
- If the message text or attachments contain some significant degree of content replication (say, greater than 50% of the hash blocks) and at least some of the hash values have high suspicion count values in hash memory[0088]420 (act540), then the message is fairly likely to be a virus/worm or spam. A virus or worm should be considered more likely if the high-count matches are in an attachment. If the highly-replicated content is in the message text, then the message is more likely to be spam, though it is possible that e-mail text employing a scripting language (e.g., Java script) might also contain a virus.
- If the replication is in the message text, and the suspicion count is substantially higher for the message text than for the From field, the message is likely to be spam (because spammers generally vary the From field to evade simpler spam filters). A similar check can be made for the concatenation of the From and To header fields, except that in this case, it is most suspicious if the From/To hash misses (finds a zero suspicion count), indicating that the sender does not ordinarily send e-mail to that recipient, making it unlikely to be a mailing list, and very likely to be a spammer (because they normally employ random or fictitious From addresses).[0089]
- In the above cases,[0090]
hash processor 410 may take remedial action (act542). The particular type of action taken byhash processor 410 may vary as described above. - Systems and methods consistent with the present invention provide mechanisms within an e-mail server to detect and/or prevent transmission of unwanted e-mail, such as e-mail containing viruses or worms, including polymorphic viruses and worms, and unsolicited commercial e-mail (spam).[0091]
- Implementation of a hash-based detection mechanism in an e-mail server at the e-mail message level provides advantages over a packet-based implementation in a router or other network node device. For example, the entire e-mail message has been re-assembled, both at the packet level (i.e., IP fragment re-assembly) and at the application level (multiple packets into a complete e-mail message). Also, the hashing algorithm can be applied more intelligently to specific parts of the e-mail message (e.g., header fields, message body, and attachments). Attachments that have been compressed for transport (e.g., “.zip” files) can be expanded for inspection. Without doing this, a polymorphic virus could easily hide inside such files with no repeatable hash signature visible at the packet transport level.[0092]
- With the entire message available for a single pass of the hashing process, packet boundaries and packet fragmentation do not split sequences of bytes that might otherwise provide useful hash signatures. A clever attacker might otherwise obscure a virus/worm attack by causing the IP packets carrying the malicious code to be fragmented into pieces smaller than that for which the hashing process is effective, or by forcing packet breaks in the middle of otherwise-visible fixed sequences of code in the virus/worm. Also, the entire message is likely to be longer than a single packet, thereby reducing the probability of false alarms (possibly due to insufficient hash-block sample size and too few hash blocks per packet) and increasing the probability of correct identification of a virus/worm (more hash blocks will match per message than per packet, since packets will be only parts of the entire message).[0093]
- Also, fewer hash-block alignment issues arise when the hash blocks can be intelligently aligned with fields of the e-mail message, such as the start of the message body, or the start of an attachment block. This results in faster detection of duplicate contents than if the blocks are randomly aligned (as is the case when the method is applied to individual packets).[0094]
- E-mail-borne malicious code, such as viruses and worms, also usually includes a text message designed to cause the user to read the message and/or perform some other action that will activate the malicious code. It is harder for such text to be polymorphic, because automatic scrambling of the user-visible text will either render it suspicious-looking, or will be very limited in variability. This fact, combined with the ability to start a hash block at the start of the message text by parsing the e-mail header, reduces the variability in hash signatures of the message, making it easier to detect with fewer examples seen.[0095]
- Further, the ability to extract and hash specific headers from an e-mail message separately may be used to help classify the type of replicated content the message body carries. Because many legitimate cases of message replication exist (e.g., topical mailing lists, such as Yahoo Groups), intelligent parsing and hashing of the message headers is very useful to reduce the false alarm rate, and to increase the accuracy of detection of real viruses, worms, and spam.[0096]
- This detection technique, compared to others which might extract and save fixed strings to be searched for in other pieces of e-mail, includes hash-based filters that are one-way functions (i.e., it is possible, given a piece of text, to determine if it has been seen before in another message). Given the state data contained in the filter, however, it is virtually impossible to reconstruct a prior message, or any piece of a prior message, that has been passed through the filter previously. Thus, this technique can maintain the privacy of e-mail, without retaining any information that can be attributed to a specific sender or receiver.[0097]
- The foregoing description of preferred embodiments of the present invention provides illustration and description, but is not intended to be exhaustive or to limit the invention to the precise form disclosed. Modifications and variations are possible in light of the above teachings or may be acquired from practice of the invention.[0098]
- For example, systems and methods have been described with regard to a mail server. In other implementations, the systems and methods described herein may be used within other devices, such as a mail client. In such a case, the mail client may periodically obtain suspicion count values for its hash memory from one or more network devices, such as a mail server.[0099]
- It may be possible for multiple mail servers to work together to detect and prevent unwanted e-mails. For example, high-scoring entries from the hash memory of one mail server might be distributed to other mail servers, as long as the same hash functions are used by the same cooperating servers. This may accelerate the detection process, especially for mail servers that experience relatively low volumes of traffic.[0100]
- Further, certain portions of the invention have been described as “blocks” that perform one or more functions. These blocks may include hardware, such as an ASIC or a FPGA, software, or a combination of hardware and software.[0101]
- No element, act, or instruction used in the description of the present application should be construed as critical or essential to the invention unless explicitly described as such. Also, as used herein, the article “a” is intended to include one or more items. Where only one item is intended, the term “one” or similar language is used. The scope of the invention is defined by the claims and their equivalents.[0102]
Claims (66)
Priority Applications (13)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| US10/654,771US20040073617A1 (en) | 2000-06-19 | 2003-09-04 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US12/243,785US20090031129A1 (en) | 2000-06-19 | 2008-10-01 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US12/243,778US20090031136A1 (en) | 2000-06-19 | 2008-10-01 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US12/248,790US8204945B2 (en) | 2000-06-19 | 2008-10-09 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US12/249,804US20090313339A1 (en) | 2000-06-19 | 2008-10-10 | Method and apparatus for tracing packets |
| US12/249,803US20090158435A1 (en) | 2000-06-19 | 2008-10-10 | Hash-based systems and methods for detecting, preventing, and tracing network worms and viruses |
| US12/249,823US20090158046A1 (en) | 2000-06-19 | 2008-10-10 | Hash-based systems and methods for detecting and preventing transmission of polymorphic network worms and viruses |
| US12/249,832US20090182867A1 (en) | 2000-06-19 | 2008-10-10 | Method and apparatus for identifying a packet |
| US12/762,365US20100205672A1 (en) | 2000-06-19 | 2010-04-18 | Hash-based systems and methods for detecting, preventing, and tracing network worms and viruses |
| US12/762,366US20100205670A1 (en) | 2000-06-19 | 2010-04-18 | Method and apparatus for tracing packets |
| US12/762,367US8272060B2 (en) | 2000-06-19 | 2010-04-18 | Hash-based systems and methods for detecting and preventing transmission of polymorphic network worms and viruses |
| US12/762,368US20100205265A1 (en) | 2000-06-19 | 2010-04-19 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US13/620,692US20130014261A1 (en) | 2000-06-19 | 2012-09-14 | Hash-based systems and methods for detecting and preventing transmission of polymorphic network worms and viruses |
Applications Claiming Priority (7)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| US21242500P | 2000-06-19 | 2000-06-19 | |
| US88114501A | 2001-06-14 | 2001-06-14 | |
| US09/881,074US6981158B1 (en) | 2000-06-19 | 2001-06-14 | Method and apparatus for tracing packets |
| US34146201P | 2001-12-14 | 2001-12-14 | |
| US40797502P | 2002-09-05 | 2002-09-05 | |
| US10/251,403US7328349B2 (en) | 2001-12-14 | 2002-09-20 | Hash-based systems and methods for detecting, preventing, and tracing network worms and viruses |
| US10/654,771US20040073617A1 (en) | 2000-06-19 | 2003-09-04 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
Related Parent Applications (4)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| US88114501AContinuation-In-Part | 2000-06-19 | 2001-06-14 | |
| US09/881,074Continuation-In-PartUS6981158B1 (en) | 2000-06-19 | 2001-06-14 | Method and apparatus for tracing packets |
| US10/251,403Continuation-In-PartUS7328349B2 (en) | 2000-06-19 | 2002-09-20 | Hash-based systems and methods for detecting, preventing, and tracing network worms and viruses |
| US10/654,771Continuation-In-PartUS20040073617A1 (en) | 2000-06-19 | 2003-09-04 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
Related Child Applications (9)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| US10/654,771Continuation-In-PartUS20040073617A1 (en) | 2000-06-19 | 2003-09-04 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US12/243,778ContinuationUS20090031136A1 (en) | 2000-06-19 | 2008-10-01 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US12/243,778DivisionUS20090031136A1 (en) | 2000-06-19 | 2008-10-01 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US12/243,785DivisionUS20090031129A1 (en) | 2000-06-19 | 2008-10-01 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US12/248,790ContinuationUS8204945B2 (en) | 2000-06-19 | 2008-10-09 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US12/249,832ContinuationUS20090182867A1 (en) | 2000-06-19 | 2008-10-10 | Method and apparatus for identifying a packet |
| US12/249,804ContinuationUS20090313339A1 (en) | 2000-06-19 | 2008-10-10 | Method and apparatus for tracing packets |
| US12/249,823ContinuationUS20090158046A1 (en) | 2000-06-19 | 2008-10-10 | Hash-based systems and methods for detecting and preventing transmission of polymorphic network worms and viruses |
| US12/249,803ContinuationUS20090158435A1 (en) | 2000-06-19 | 2008-10-10 | Hash-based systems and methods for detecting, preventing, and tracing network worms and viruses |
Publications (1)
| Publication Number | Publication Date |
|---|---|
| US20040073617A1true US20040073617A1 (en) | 2004-04-15 |
Family
ID=46204947
Family Applications (13)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| US10/654,771AbandonedUS20040073617A1 (en) | 2000-06-19 | 2003-09-04 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US12/243,785AbandonedUS20090031129A1 (en) | 2000-06-19 | 2008-10-01 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US12/243,778AbandonedUS20090031136A1 (en) | 2000-06-19 | 2008-10-01 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US12/248,790Expired - Fee RelatedUS8204945B2 (en) | 2000-06-19 | 2008-10-09 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US12/249,823AbandonedUS20090158046A1 (en) | 2000-06-19 | 2008-10-10 | Hash-based systems and methods for detecting and preventing transmission of polymorphic network worms and viruses |
| US12/249,804AbandonedUS20090313339A1 (en) | 2000-06-19 | 2008-10-10 | Method and apparatus for tracing packets |
| US12/249,832AbandonedUS20090182867A1 (en) | 2000-06-19 | 2008-10-10 | Method and apparatus for identifying a packet |
| US12/249,803AbandonedUS20090158435A1 (en) | 2000-06-19 | 2008-10-10 | Hash-based systems and methods for detecting, preventing, and tracing network worms and viruses |
| US12/762,365AbandonedUS20100205672A1 (en) | 2000-06-19 | 2010-04-18 | Hash-based systems and methods for detecting, preventing, and tracing network worms and viruses |
| US12/762,366AbandonedUS20100205670A1 (en) | 2000-06-19 | 2010-04-18 | Method and apparatus for tracing packets |
| US12/762,367Expired - Fee RelatedUS8272060B2 (en) | 2000-06-19 | 2010-04-18 | Hash-based systems and methods for detecting and preventing transmission of polymorphic network worms and viruses |
| US12/762,368AbandonedUS20100205265A1 (en) | 2000-06-19 | 2010-04-19 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US13/620,692AbandonedUS20130014261A1 (en) | 2000-06-19 | 2012-09-14 | Hash-based systems and methods for detecting and preventing transmission of polymorphic network worms and viruses |
Family Applications After (12)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| US12/243,785AbandonedUS20090031129A1 (en) | 2000-06-19 | 2008-10-01 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US12/243,778AbandonedUS20090031136A1 (en) | 2000-06-19 | 2008-10-01 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US12/248,790Expired - Fee RelatedUS8204945B2 (en) | 2000-06-19 | 2008-10-09 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US12/249,823AbandonedUS20090158046A1 (en) | 2000-06-19 | 2008-10-10 | Hash-based systems and methods for detecting and preventing transmission of polymorphic network worms and viruses |
| US12/249,804AbandonedUS20090313339A1 (en) | 2000-06-19 | 2008-10-10 | Method and apparatus for tracing packets |
| US12/249,832AbandonedUS20090182867A1 (en) | 2000-06-19 | 2008-10-10 | Method and apparatus for identifying a packet |
| US12/249,803AbandonedUS20090158435A1 (en) | 2000-06-19 | 2008-10-10 | Hash-based systems and methods for detecting, preventing, and tracing network worms and viruses |
| US12/762,365AbandonedUS20100205672A1 (en) | 2000-06-19 | 2010-04-18 | Hash-based systems and methods for detecting, preventing, and tracing network worms and viruses |
| US12/762,366AbandonedUS20100205670A1 (en) | 2000-06-19 | 2010-04-18 | Method and apparatus for tracing packets |
| US12/762,367Expired - Fee RelatedUS8272060B2 (en) | 2000-06-19 | 2010-04-18 | Hash-based systems and methods for detecting and preventing transmission of polymorphic network worms and viruses |
| US12/762,368AbandonedUS20100205265A1 (en) | 2000-06-19 | 2010-04-19 | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail |
| US13/620,692AbandonedUS20130014261A1 (en) | 2000-06-19 | 2012-09-14 | Hash-based systems and methods for detecting and preventing transmission of polymorphic network worms and viruses |
Country Status (1)
| Country | Link |
|---|---|
| US (13) | US20040073617A1 (en) |
Cited By (273)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US20020120575A1 (en)* | 2001-02-23 | 2002-08-29 | Hewlett-Packard Company | Method of and apparatus for ascertaining the status of a data processing environment |
| US20020124052A1 (en)* | 2001-02-17 | 2002-09-05 | Richard Brown | Secure e-mail handling using a compartmented operating system |
| US20020122543A1 (en)* | 2001-02-12 | 2002-09-05 | Rowen Chris E. | System and method of indexing unique electronic mail messages and uses for the same |
| US20020194241A1 (en)* | 2001-06-19 | 2002-12-19 | Jonathan Griffin | Performing secure and insecure computing operations in a compartmented operating system |
| US20020194493A1 (en)* | 2000-11-28 | 2002-12-19 | Hewlett-Packard Company | Demonstrating integrity of a compartment of a compartmented operating system |
| US20030023875A1 (en)* | 2001-07-26 | 2003-01-30 | Hursey Neil John | Detecting e-mail propagated malware |
| US20030079140A1 (en)* | 2001-10-24 | 2003-04-24 | Yosuke Ura | Multiple protecting system to protect personal computer data from burglary utilized flash memory drive |
| US20030084323A1 (en)* | 2001-10-31 | 2003-05-01 | Gales George S. | Network intrusion detection system and method |
| US20030149895A1 (en)* | 2001-01-31 | 2003-08-07 | Choo Tse Huong | Trusted gateway system |
| US20040003283A1 (en)* | 2002-06-26 | 2004-01-01 | Goodman Joshua Theodore | Spam detector with challenges |
| US20040111531A1 (en)* | 2002-12-06 | 2004-06-10 | Stuart Staniford | Method and system for reducing the rate of infection of a communications network by a software worm |
| US20040148506A1 (en)* | 2003-01-23 | 2004-07-29 | Prince Matthew B. | Method and apparatus for a non-revealing do-not-contact list system |
| US20040167964A1 (en)* | 2003-02-25 | 2004-08-26 | Rounthwaite Robert L. | Adaptive junk message filtering system |
| US20040177110A1 (en)* | 2003-03-03 | 2004-09-09 | Rounthwaite Robert L. | Feedback loop for spam prevention |
| US20040199595A1 (en)* | 2003-01-16 | 2004-10-07 | Scott Banister | Electronic message delivery using a virtual gateway approach |
| US20040199773A1 (en)* | 2001-06-21 | 2004-10-07 | Radatti Peter V. | Apparatus, methods and articles of manufacture for intercepting, examining and controlling code, data and files and their transfer |
| US20040205135A1 (en)* | 2003-03-25 | 2004-10-14 | Hallam-Baker Phillip Martin | Control and management of electronic messaging |
| US20040215977A1 (en)* | 2003-03-03 | 2004-10-28 | Goodman Joshua T. | Intelligent quarantining for spam prevention |
| US20040221062A1 (en)* | 2003-05-02 | 2004-11-04 | Starbuck Bryan T. | Message rendering for identification of content features |
| US20040260922A1 (en)* | 2003-06-04 | 2004-12-23 | Goodman Joshua T. | Training filters for IP address and URL learning |
| US20040260776A1 (en)* | 2003-06-23 | 2004-12-23 | Starbuck Bryan T. | Advanced spam detection techniques |
| US20050015454A1 (en)* | 2003-06-20 | 2005-01-20 | Goodman Joshua T. | Obfuscation of spam filter |
| US20050022014A1 (en)* | 2001-11-21 | 2005-01-27 | Shipman Robert A | Computer security system |
| US20050021649A1 (en)* | 2003-06-20 | 2005-01-27 | Goodman Joshua T. | Prevention of outgoing spam |
| US20050080860A1 (en)* | 2003-10-14 | 2005-04-14 | Daniell W. Todd | Phonetic filtering of undesired email messages |
| US20050080889A1 (en)* | 2003-10-14 | 2005-04-14 | Malik Dale W. | Child protection from harmful email |
| US20050080642A1 (en)* | 2003-10-14 | 2005-04-14 | Daniell W. Todd | Consolidated email filtering user interface |
| US20050091321A1 (en)* | 2003-10-14 | 2005-04-28 | Daniell W. T. | Identifying undesired email messages having attachments |
| US20050097174A1 (en)* | 2003-10-14 | 2005-05-05 | Daniell W. T. | Filtered email differentiation |
| US20050108339A1 (en)* | 2003-05-15 | 2005-05-19 | Matt Gleeson | Method and apparatus for filtering email spam using email noise reduction |
| US20050154601A1 (en)* | 2004-01-09 | 2005-07-14 | Halpern Joshua I. | Information security threat identification, analysis, and management |
| US20050188032A1 (en)* | 2004-01-14 | 2005-08-25 | Katsuyuki Yamazaki | Mass mail detection system and mail server |
| US20050193073A1 (en)* | 2004-03-01 | 2005-09-01 | Mehr John D. | (More) advanced spam detection features |
| US20050198289A1 (en)* | 2004-01-20 | 2005-09-08 | Prakash Vipul V. | Method and an apparatus to screen electronic communications |
| US20050204006A1 (en)* | 2004-03-12 | 2005-09-15 | Purcell Sean E. | Message junk rating interface |
| US20050204005A1 (en)* | 2004-03-12 | 2005-09-15 | Purcell Sean E. | Selective treatment of messages based on junk rating |
| US20050223221A1 (en)* | 2001-11-22 | 2005-10-06 | Proudler Graeme J | Apparatus and method for creating a trusted environment |
| US20050229254A1 (en)* | 2004-04-08 | 2005-10-13 | Sumeet Singh | Detecting public network attacks using signatures and fast content analysis |
| US20050240910A1 (en)* | 2004-04-26 | 2005-10-27 | Radatti Peter V | Apparatus, methods and articles of manufacture for intercepting, examining and controlling code, data, files and their transfer |
| US20050265319A1 (en)* | 2004-05-29 | 2005-12-01 | Clegg Paul J | Method and apparatus for destination domain-based bounce profiles |
| WO2005119485A1 (en)* | 2004-05-29 | 2005-12-15 | Ironport Systems, Inc. | Method and apparatus for mail flow monitoring |
| US20050283837A1 (en)* | 2004-06-16 | 2005-12-22 | Michael Olivier | Method and apparatus for managing computer virus outbreaks |
| GB2415854A (en)* | 2004-07-01 | 2006-01-04 | Ericsson Telefon Ab L M | Email Spam reduction |
| US20060010215A1 (en)* | 2004-05-29 | 2006-01-12 | Clegg Paul J | Managing connections and messages at a server by associating different actions for both different senders and different recipients |
| US20060010217A1 (en)* | 2004-06-04 | 2006-01-12 | Business Instruments Corp. | System and method for dynamic adaptive user-based prioritization and display of electronic messages |
| US20060026236A1 (en)* | 2002-12-03 | 2006-02-02 | Research In Motion Limited | Method, system and computer software product for pre-selecting a folder for a message |
| US20060031338A1 (en)* | 2004-08-09 | 2006-02-09 | Microsoft Corporation | Challenge response systems |
| US20060031314A1 (en)* | 2004-05-28 | 2006-02-09 | Robert Brahms | Techniques for determining the reputation of a message sender |
| US20060031359A1 (en)* | 2004-05-29 | 2006-02-09 | Clegg Paul J | Managing connections, messages, and directory harvest attacks at a server |
| US20060036695A1 (en)* | 2004-08-12 | 2006-02-16 | Rolnik Robert C | Timed delivery of alert notifications based on user set criteria |
| US20060036693A1 (en)* | 2004-08-12 | 2006-02-16 | Microsoft Corporation | Spam filtering with probabilistic secure hashes |
| US20060095523A1 (en)* | 2004-11-02 | 2006-05-04 | Bruno Decarpigny | System and method for sending messages into a communications network by electronic mail, based on the use of a send filter |
| US20060098585A1 (en)* | 2004-11-09 | 2006-05-11 | Cisco Technology, Inc. | Detecting malicious attacks using network behavior and header analysis |
| US20060101680A1 (en)* | 2004-05-28 | 2006-05-18 | Smith Michael J | Container contents identifier |
| US20060123476A1 (en)* | 2004-02-12 | 2006-06-08 | Karim Yaghmour | System and method for warranting electronic mail using a hybrid public key encryption scheme |
| US7076655B2 (en) | 2001-06-19 | 2006-07-11 | Hewlett-Packard Development Company, L.P. | Multiple trusted computing environments with verifiable environment identities |
| US20060161989A1 (en)* | 2004-12-13 | 2006-07-20 | Eran Reshef | System and method for deterring rogue users from attacking protected legitimate users |
| US20060161986A1 (en)* | 2004-11-09 | 2006-07-20 | Sumeet Singh | Method and apparatus for content classification |
| US20060168202A1 (en)* | 2004-12-13 | 2006-07-27 | Eran Reshef | System and method for deterring rogue users from attacking protected legitimate users |
| US20060168059A1 (en)* | 2003-03-31 | 2006-07-27 | Affini, Inc. | System and method for providing filtering email messages |
| US20060212523A1 (en)* | 2005-03-21 | 2006-09-21 | International Business Machines Corporation | Policy based control of multiple message forwards |
| US20060262867A1 (en)* | 2005-05-17 | 2006-11-23 | Ntt Docomo, Inc. | Data communications system and data communications method |
| US20070038705A1 (en)* | 2005-07-29 | 2007-02-15 | Microsoft Corporation | Trees of classifiers for detecting email spam |
| US7197539B1 (en) | 2004-11-01 | 2007-03-27 | Symantec Corporation | Automated disablement of disposable e-mail addresses based on user actions |
| US7203964B1 (en)* | 2003-10-07 | 2007-04-10 | Elmer V. Pass | Method of stopping internet viruses |
| US20070083606A1 (en)* | 2001-12-05 | 2007-04-12 | Bellsouth Intellectual Property Corporation | Foreign Network Spam Blocker |
| US20070118874A1 (en)* | 2005-11-18 | 2007-05-24 | Research In Motion Limited | System and method for handling electronic messages |
| US20070118759A1 (en)* | 2005-10-07 | 2007-05-24 | Sheppard Scott K | Undesirable email determination |
| US20070143848A1 (en)* | 2005-12-16 | 2007-06-21 | Kraemer Jeffrey A | Methods and apparatus providing computer and network security for polymorphic attacks |
| US20070143847A1 (en)* | 2005-12-16 | 2007-06-21 | Kraemer Jeffrey A | Methods and apparatus providing automatic signature generation and enforcement |
| US20070150933A1 (en)* | 2005-12-28 | 2007-06-28 | Microsoft Corporation | Combining communication policies into common rules store |
| US20070198642A1 (en)* | 2003-06-30 | 2007-08-23 | Bellsouth Intellectual Property Corporation | Filtering Email Messages Corresponding to Undesirable Domains |
| US20070214220A1 (en)* | 2006-03-09 | 2007-09-13 | John Alsop | Method and system for recognizing desired email |
| US7287060B1 (en)* | 2003-06-12 | 2007-10-23 | Storage Technology Corporation | System and method for rating unsolicited e-mail |
| US20070256127A1 (en)* | 2005-12-16 | 2007-11-01 | Kraemer Jeffrey A | Methods and apparatus providing computer and network security utilizing probabilistic signature generation |
| US7293063B1 (en) | 2003-06-04 | 2007-11-06 | Symantec Corporation | System utilizing updated spam signatures for performing secondary signature-based analysis of a held e-mail to improve spam email detection |
| US7302698B1 (en) | 1999-09-17 | 2007-11-27 | Hewlett-Packard Development Company, L.P. | Operation of trusted state in computing platform |
| US20070282953A1 (en)* | 2006-05-31 | 2007-12-06 | Microsoft Corporation | Perimeter message filtering with extracted user-specific preferences |
| US20080033905A1 (en)* | 2006-08-05 | 2008-02-07 | Terry Lee Stokes | System and Method for the Capture and Archival of Electronic Communications |
| US20080059588A1 (en)* | 2006-09-01 | 2008-03-06 | Ratliff Emily J | Method and System for Providing Notification of Nefarious Remote Control of a Data Processing System |
| US20080059590A1 (en)* | 2006-09-05 | 2008-03-06 | Ecole Polytechnique Federale De Lausanne (Epfl) | Method to filter electronic messages in a message processing system |
| US7366919B1 (en) | 2003-04-25 | 2008-04-29 | Symantec Corporation | Use of geo-location data for spam detection |
| US20080109448A1 (en)* | 2006-11-06 | 2008-05-08 | Messageone, Inc. | System and Method for Managing Data Across Multiple Environments |
| US20080126951A1 (en)* | 2005-06-03 | 2008-05-29 | C-Mail Corp. | System and method of dynamically prioritized electronic mail graphical user interface, and measuring email productivity and collaboration trends |
| US20080134336A1 (en)* | 2004-07-13 | 2008-06-05 | Mailfrontier, Inc. | Analyzing traffic patterns to detect infectious messages |
| US20080147861A1 (en)* | 2006-12-13 | 2008-06-19 | Takumi Oishi | Data distribution network and an apparatus of index holding |
| US20080162135A1 (en)* | 2006-12-30 | 2008-07-03 | Emc Corporation | Analyzing network traffic |
| US20080275957A1 (en)* | 2007-05-03 | 2008-11-06 | Microsoft Corporation | Identifying and correlating electronic mail messages |
| US20080313708A1 (en)* | 2007-06-12 | 2008-12-18 | Alcatel Lucent | Data content matching |
| US7490244B1 (en) | 2004-09-14 | 2009-02-10 | Symantec Corporation | Blocking e-mail propagation of suspected malicious computer code |
| US20090077182A1 (en)* | 2007-09-17 | 2009-03-19 | Iconix, Inc | System and method for identifying email campaigns |
| US20090084713A1 (en)* | 2007-09-29 | 2009-04-02 | Miller John P | Systems and Methods for Segregating Undesired Mail |
| US20090100079A1 (en)* | 2007-10-12 | 2009-04-16 | Fujitsu Limited | E-mail information management apparatus, and e-mail information management method |
| US7530106B1 (en)* | 2008-07-02 | 2009-05-05 | Kaspersky Lab, Zao | System and method for security rating of computer processes |
| US7546349B1 (en) | 2004-11-01 | 2009-06-09 | Symantec Corporation | Automatic generation of disposable e-mail addresses |
| US7548956B1 (en)* | 2003-12-30 | 2009-06-16 | Aol Llc | Spam control based on sender account characteristics |
| US20090158429A1 (en)* | 2003-09-19 | 2009-06-18 | Marshall Van Alstyne | Methods and systems for enabling analysis of communication content while preserving confidentiality |
| US20090164506A1 (en)* | 2007-12-19 | 2009-06-25 | Casdex, Inc. | System and Method for Content-Based Email Authentication |
| US7555524B1 (en) | 2004-09-16 | 2009-06-30 | Symantec Corporation | Bulk electronic message detection by header similarity analysis |
| US20090183257A1 (en)* | 2008-01-15 | 2009-07-16 | Microsoft Corporation | Preventing secure data from leaving the network perimeter |
| US20090187629A1 (en)* | 2008-01-17 | 2009-07-23 | International Business Machines Corporation | Embedding a unque serial number into the content of an email for tracking information dispersion |
| US20090254992A1 (en)* | 2001-07-30 | 2009-10-08 | Schultz Matthew G | Systems and methods for detection of new malicious executables |
| US7617285B1 (en) | 2005-09-29 | 2009-11-10 | Symantec Corporation | Adaptive threshold based spam classification |
| US20090300761A1 (en)* | 2008-05-28 | 2009-12-03 | John Park | Intelligent Hashes for Centralized Malware Detection |
| WO2009146536A1 (en) | 2008-06-02 | 2009-12-10 | Corporation De L'ecole Polytechnique De Montreal | File presence detection and monitoring |
| US7640590B1 (en) | 2004-12-21 | 2009-12-29 | Symantec Corporation | Presentation of network source and executable characteristics |
| US7650382B1 (en) | 2003-04-24 | 2010-01-19 | Symantec Corporation | Detecting spam e-mail with backup e-mail server traps |
| US7653695B2 (en) | 2004-02-17 | 2010-01-26 | Ironport Systems, Inc. | Collecting, aggregating, and managing information relating to electronic messages |
| US7664819B2 (en) | 2004-06-29 | 2010-02-16 | Microsoft Corporation | Incremental anti-spam lookup and update service |
| US20100049848A1 (en)* | 2007-09-24 | 2010-02-25 | Barracuda Networks, Inc | Distributed frequency data collection via indicator embedded with dns request |
| US20100058023A1 (en)* | 2008-08-29 | 2010-03-04 | Microsoft Corporation | Efficiently managing modular data storage systems |
| US7680886B1 (en) | 2003-04-09 | 2010-03-16 | Symantec Corporation | Suppressing spam using a machine learning based spam filter |
| US20100077480A1 (en)* | 2006-11-13 | 2010-03-25 | Samsung Sds Co., Ltd. | Method for Inferring Maliciousness of Email and Detecting a Virus Pattern |
| US20100106677A1 (en)* | 2004-03-09 | 2010-04-29 | Gozoom.Com, Inc. | Email analysis using fuzzy matching of text |
| US7739494B1 (en) | 2003-04-25 | 2010-06-15 | Symantec Corporation | SSL validation and stripping using trustworthiness factors |
| US7757288B1 (en) | 2005-05-23 | 2010-07-13 | Symantec Corporation | Malicious e-mail attack inversion filter |
| US7788329B2 (en) | 2000-05-16 | 2010-08-31 | Aol Inc. | Throttling electronic communications from one or more senders |
| US7788576B1 (en)* | 2006-10-04 | 2010-08-31 | Trend Micro Incorporated | Grouping of documents that contain markup language code |
| US20100242111A1 (en)* | 2005-12-16 | 2010-09-23 | Kraemer Jeffrey A | Methods and apparatus providing computer and network security utilizing probabilistic policy reposturing |
| US20100318612A1 (en)* | 2009-06-11 | 2010-12-16 | Vivek Agarwal | Apparatus and Method for Email Storage |
| US7856090B1 (en) | 2005-08-08 | 2010-12-21 | Symantec Corporation | Automatic spim detection |
| US7877799B2 (en) | 2000-08-18 | 2011-01-25 | Hewlett-Packard Development Company, L.P. | Performance of a service on a computing platform |
| US7912907B1 (en) | 2005-10-07 | 2011-03-22 | Symantec Corporation | Spam email detection based on n-grams with feature selection |
| US7921159B1 (en) | 2003-10-14 | 2011-04-05 | Symantec Corporation | Countering spam that uses disguised characters |
| US20110099291A1 (en)* | 2009-10-23 | 2011-04-28 | Comcast Cable Communications, Llc | Address Couplet Communication Filtering |
| US7941490B1 (en)* | 2004-05-11 | 2011-05-10 | Symantec Corporation | Method and apparatus for detecting spam in email messages and email attachments |
| US7975010B1 (en) | 2005-03-23 | 2011-07-05 | Symantec Corporation | Countering spam through address comparison |
| US20110202620A1 (en)* | 2008-12-02 | 2011-08-18 | Tencent Technology (Shenzhen) Company Limited | Method and device for intercepting junk mail |
| US8056128B1 (en)* | 2004-09-30 | 2011-11-08 | Google Inc. | Systems and methods for detecting potential communications fraud |
| US8065370B2 (en) | 2005-11-03 | 2011-11-22 | Microsoft Corporation | Proofs to filter spam |
| WO2012007202A1 (en)* | 2010-07-13 | 2012-01-19 | F-Secure Corporation | Identifying polymorphic malware |
| US8145710B2 (en) | 2003-06-18 | 2012-03-27 | Symantec Corporation | System and method for filtering spam messages utilizing URL filtering module |
| US8166310B2 (en) | 2004-05-29 | 2012-04-24 | Ironport Systems, Inc. | Method and apparatus for providing temporary access to a network device |
| US8201254B1 (en) | 2005-08-30 | 2012-06-12 | Symantec Corporation | Detection of e-mail threat acceleration |
| US20120158729A1 (en)* | 2010-05-18 | 2012-06-21 | Lsi Corporation | Concurrent linked-list traversal for real-time hash processing in multi-core, multi-thread network processors |
| US8218765B2 (en) | 2001-02-23 | 2012-07-10 | Hewlett-Packard Development Company, L.P. | Information system |
| US8224905B2 (en) | 2006-12-06 | 2012-07-17 | Microsoft Corporation | Spam filtration utilizing sender activity data |
| WO2012162676A2 (en) | 2011-05-25 | 2012-11-29 | Microsoft Corporation | Dynamic rule reordering for message classification |
| US8332947B1 (en) | 2006-06-27 | 2012-12-11 | Symantec Corporation | Security threat reporting in light of local security tools |
| US8495037B1 (en)* | 2006-02-21 | 2013-07-23 | Symantec Operating Corporation | Efficient isolation of backup versions of data objects affected by malicious software |
| US8495144B1 (en)* | 2004-10-06 | 2013-07-23 | Trend Micro Incorporated | Techniques for identifying spam e-mail |
| US8539587B2 (en) | 2005-03-22 | 2013-09-17 | Hewlett-Packard Development Company, L.P. | Methods, devices and data structures for trusted data |
| US20130246378A1 (en)* | 2007-04-30 | 2013-09-19 | Stephen Owen Hearnden | Partial hash system, method, and computer program product |
| US8700913B1 (en) | 2011-09-23 | 2014-04-15 | Trend Micro Incorporated | Detection of fake antivirus in computers |
| US8719356B2 (en) | 2012-04-17 | 2014-05-06 | Return Path, Inc | Methods, systems, and computer readable media for monitoring deliverability of electronic mail based on subscriber and seed deliverability data |
| US8850566B2 (en) | 2004-07-13 | 2014-09-30 | Sonicwall, Inc. | Time zero detection of infectious messages |
| US20140331310A1 (en)* | 2008-06-22 | 2014-11-06 | Microsoft Corporation | Signed ephemeral email addresses |
| US8892673B1 (en)* | 2003-08-08 | 2014-11-18 | Radix Holdings, Llc | Hybrid challenge-response |
| EP2811699A1 (en)* | 2013-06-06 | 2014-12-10 | Kaspersky Lab, ZAO | System and method for spam filtering using shingles |
| US8996638B2 (en) | 2013-06-06 | 2015-03-31 | Kaspersky Lab Zao | System and method for spam filtering using shingles |
| US20150222650A1 (en)* | 2014-01-31 | 2015-08-06 | Juniper Networks, Inc. | Intermediate responses for non-html downloads |
| US20150256461A1 (en)* | 2014-03-10 | 2015-09-10 | Palo Alto Research Center Incorporated | Concurrent hashes and sub-hashes on data streams |
| US9152706B1 (en) | 2006-12-30 | 2015-10-06 | Emc Corporation | Anonymous identification tokens |
| US20150295869A1 (en)* | 2014-04-14 | 2015-10-15 | Microsoft Corporation | Filtering Electronic Messages |
| US20150347753A1 (en)* | 2006-04-06 | 2015-12-03 | Juniper Networks, Inc. | Malware detection system and method for mobile platforms |
| US9224000B1 (en)* | 2011-06-14 | 2015-12-29 | Ionic Security, Inc. | Systems and methods for providing information security using context-based keys |
| US9223971B1 (en)* | 2014-01-28 | 2015-12-29 | Exelis Inc. | User reporting and automatic threat processing of suspicious email |
| US20150381539A1 (en)* | 2012-01-25 | 2015-12-31 | Bitdefender IPR Management Ltd. | Systems and Methods for Spam Detection Using Frequency Spectra of Character Strings |
| US9264418B1 (en)* | 2014-02-20 | 2016-02-16 | Amazon Technologies, Inc. | Client-side spam detection and prevention |
| US9336380B2 (en) | 2010-12-15 | 2016-05-10 | Microsoft Technology Licensing Llc | Applying activity actions to frequent activities |
| US9461930B2 (en) | 2009-04-27 | 2016-10-04 | Intel Corporation | Modifying data streams without reordering in a multi-thread, multi-flow network processor |
| US9473576B2 (en) | 2014-04-07 | 2016-10-18 | Palo Alto Research Center Incorporated | Service discovery using collection synchronization with exact names |
| US9497205B1 (en)* | 2008-05-19 | 2016-11-15 | Emc Corporation | Global commonality and network logging |
| US20170041293A1 (en)* | 2005-04-22 | 2017-02-09 | Blue Coat Systems, Inc. | Methods and apparatus for blocking unwanted software downloads |
| US9590948B2 (en) | 2014-12-15 | 2017-03-07 | Cisco Systems, Inc. | CCN routing using hardware-assisted hash tables |
| US9590887B2 (en) | 2014-07-18 | 2017-03-07 | Cisco Systems, Inc. | Method and system for keeping interest alive in a content centric network |
| US9609014B2 (en) | 2014-05-22 | 2017-03-28 | Cisco Systems, Inc. | Method and apparatus for preventing insertion of malicious content at a named data network router |
| US9608810B1 (en) | 2015-02-05 | 2017-03-28 | Ionic Security Inc. | Systems and methods for encryption and provision of information security using platform services |
| US9621354B2 (en) | 2014-07-17 | 2017-04-11 | Cisco Systems, Inc. | Reconstructable content objects |
| US9626413B2 (en) | 2014-03-10 | 2017-04-18 | Cisco Systems, Inc. | System and method for ranking content popularity in a content-centric network |
| US9660825B2 (en) | 2014-12-24 | 2017-05-23 | Cisco Technology, Inc. | System and method for multi-source multicasting in content-centric networks |
| US9686194B2 (en) | 2009-10-21 | 2017-06-20 | Cisco Technology, Inc. | Adaptive multi-interface use for content networking |
| US9699198B2 (en) | 2014-07-07 | 2017-07-04 | Cisco Technology, Inc. | System and method for parallel secure content bootstrapping in content-centric networks |
| US9716622B2 (en) | 2014-04-01 | 2017-07-25 | Cisco Technology, Inc. | System and method for dynamic name configuration in content-centric networks |
| US9729662B2 (en) | 2014-08-11 | 2017-08-08 | Cisco Technology, Inc. | Probabilistic lazy-forwarding technique without validation in a content centric network |
| US9729616B2 (en) | 2014-07-18 | 2017-08-08 | Cisco Technology, Inc. | Reputation-based strategy for forwarding and responding to interests over a content centric network |
| US20170289082A1 (en)* | 2016-03-31 | 2017-10-05 | Alibaba Group Holding Limited | Method and device for identifying spam mail |
| US9800637B2 (en) | 2014-08-19 | 2017-10-24 | Cisco Technology, Inc. | System and method for all-in-one content stream in content-centric networks |
| US9811664B1 (en) | 2011-08-15 | 2017-11-07 | Trend Micro Incorporated | Methods and systems for detecting unwanted web contents |
| US9832291B2 (en) | 2015-01-12 | 2017-11-28 | Cisco Technology, Inc. | Auto-configurable transport stack |
| US9832116B2 (en) | 2016-03-14 | 2017-11-28 | Cisco Technology, Inc. | Adjusting entries in a forwarding information base in a content centric network |
| US9832123B2 (en) | 2015-09-11 | 2017-11-28 | Cisco Technology, Inc. | Network named fragments in a content centric network |
| US9836540B2 (en) | 2014-03-04 | 2017-12-05 | Cisco Technology, Inc. | System and method for direct storage access in a content-centric network |
| US9882964B2 (en) | 2014-08-08 | 2018-01-30 | Cisco Technology, Inc. | Explicit strategy feedback in name-based forwarding |
| US9912776B2 (en) | 2015-12-02 | 2018-03-06 | Cisco Technology, Inc. | Explicit content deletion commands in a content centric network |
| US9916457B2 (en) | 2015-01-12 | 2018-03-13 | Cisco Technology, Inc. | Decoupled name security binding for CCN objects |
| US9928465B2 (en)* | 2014-05-20 | 2018-03-27 | Oath Inc. | Machine learning and validation of account names, addresses, and/or identifiers |
| US9930146B2 (en) | 2016-04-04 | 2018-03-27 | Cisco Technology, Inc. | System and method for compressing content centric networking messages |
| US9946743B2 (en) | 2015-01-12 | 2018-04-17 | Cisco Technology, Inc. | Order encoded manifests in a content centric network |
| US9954678B2 (en) | 2014-02-06 | 2018-04-24 | Cisco Technology, Inc. | Content-based transport security |
| US9954795B2 (en) | 2015-01-12 | 2018-04-24 | Cisco Technology, Inc. | Resource allocation using CCN manifests |
| US20180124007A1 (en)* | 2016-10-28 | 2018-05-03 | Hewlett Packard Enterprise Development Lp | Hashes of email text |
| US9977809B2 (en) | 2015-09-24 | 2018-05-22 | Cisco Technology, Inc. | Information and data framework in a content centric network |
| US9986034B2 (en) | 2015-08-03 | 2018-05-29 | Cisco Technology, Inc. | Transferring state in content centric network stacks |
| US9992281B2 (en) | 2014-05-01 | 2018-06-05 | Cisco Technology, Inc. | Accountable content stores for information centric networks |
| US9992097B2 (en) | 2016-07-11 | 2018-06-05 | Cisco Technology, Inc. | System and method for piggybacking routing information in interests in a content centric network |
| US10003520B2 (en) | 2014-12-22 | 2018-06-19 | Cisco Technology, Inc. | System and method for efficient name-based content routing using link-state information in information-centric networks |
| US10003507B2 (en) | 2016-03-04 | 2018-06-19 | Cisco Technology, Inc. | Transport session state protocol |
| US10009266B2 (en) | 2016-07-05 | 2018-06-26 | Cisco Technology, Inc. | Method and system for reference counted pending interest tables in a content centric network |
| US10027578B2 (en) | 2016-04-11 | 2018-07-17 | Cisco Technology, Inc. | Method and system for routable prefix queries in a content centric network |
| US10033639B2 (en) | 2016-03-25 | 2018-07-24 | Cisco Technology, Inc. | System and method for routing packets in a content centric network using anonymous datagrams |
| US10033642B2 (en) | 2016-09-19 | 2018-07-24 | Cisco Technology, Inc. | System and method for making optimal routing decisions based on device-specific parameters in a content centric network |
| US10038633B2 (en) | 2016-03-04 | 2018-07-31 | Cisco Technology, Inc. | Protocol to query for historical network information in a content centric network |
| US10043016B2 (en) | 2016-02-29 | 2018-08-07 | Cisco Technology, Inc. | Method and system for name encryption agreement in a content centric network |
| US10051071B2 (en) | 2016-03-04 | 2018-08-14 | Cisco Technology, Inc. | Method and system for collecting historical network information in a content centric network |
| US10063414B2 (en) | 2016-05-13 | 2018-08-28 | Cisco Technology, Inc. | Updating a transport stack in a content centric network |
| US10069729B2 (en) | 2016-08-08 | 2018-09-04 | Cisco Technology, Inc. | System and method for throttling traffic based on a forwarding information base in a content centric network |
| US10069933B2 (en) | 2014-10-23 | 2018-09-04 | Cisco Technology, Inc. | System and method for creating virtual interfaces based on network characteristics |
| US10067948B2 (en) | 2016-03-18 | 2018-09-04 | Cisco Technology, Inc. | Data deduping in content centric networking manifests |
| US20180255010A1 (en)* | 2017-03-02 | 2018-09-06 | Linkedin Corporation | High confidence digital content treatment |
| US10075402B2 (en) | 2015-06-24 | 2018-09-11 | Cisco Technology, Inc. | Flexible command and control in content centric networks |
| US10075401B2 (en) | 2015-03-18 | 2018-09-11 | Cisco Technology, Inc. | Pending interest table behavior |
| US20180268474A1 (en)* | 2017-03-16 | 2018-09-20 | Amobee, Inc. | Sketch-based bid fraud detection |
| US10084764B2 (en) | 2016-05-13 | 2018-09-25 | Cisco Technology, Inc. | System for a secure encryption proxy in a content centric network |
| US10091330B2 (en) | 2016-03-23 | 2018-10-02 | Cisco Technology, Inc. | Interest scheduling by an information and data framework in a content centric network |
| US10097346B2 (en) | 2015-12-09 | 2018-10-09 | Cisco Technology, Inc. | Key catalogs in a content centric network |
| US10098051B2 (en) | 2014-01-22 | 2018-10-09 | Cisco Technology, Inc. | Gateways and routing in software-defined manets |
| US10103989B2 (en) | 2016-06-13 | 2018-10-16 | Cisco Technology, Inc. | Content object return messages in a content centric network |
| US10104041B2 (en) | 2008-05-16 | 2018-10-16 | Cisco Technology, Inc. | Controlling the spread of interests and content in a content centric network |
| US10122624B2 (en) | 2016-07-25 | 2018-11-06 | Cisco Technology, Inc. | System and method for ephemeral entries in a forwarding information base in a content centric network |
| US10135948B2 (en) | 2016-10-31 | 2018-11-20 | Cisco Technology, Inc. | System and method for process migration in a content centric network |
| US10148572B2 (en) | 2016-06-27 | 2018-12-04 | Cisco Technology, Inc. | Method and system for interest groups in a content centric network |
| US20190012338A1 (en)* | 2009-06-19 | 2019-01-10 | International Business Machines Corporation | Hierarchical diff files |
| US10212248B2 (en) | 2016-10-03 | 2019-02-19 | Cisco Technology, Inc. | Cache management on high availability routers in a content centric network |
| US10212196B2 (en) | 2016-03-16 | 2019-02-19 | Cisco Technology, Inc. | Interface discovery and authentication in a name-based network |
| US10237189B2 (en) | 2014-12-16 | 2019-03-19 | Cisco Technology, Inc. | System and method for distance-based interest forwarding |
| US10243851B2 (en) | 2016-11-21 | 2019-03-26 | Cisco Technology, Inc. | System and method for forwarder connection information in a content centric network |
| US10257271B2 (en) | 2016-01-11 | 2019-04-09 | Cisco Technology, Inc. | Chandra-Toueg consensus in a content centric network |
| US10263965B2 (en) | 2015-10-16 | 2019-04-16 | Cisco Technology, Inc. | Encrypted CCNx |
| US20190129924A1 (en)* | 2017-10-27 | 2019-05-02 | International Business Machines Corporation | Displaying electronic text-based messages according to their typographic features |
| US10305864B2 (en) | 2016-01-25 | 2019-05-28 | Cisco Technology, Inc. | Method and system for interest encryption in a content centric network |
| US10305865B2 (en) | 2016-06-21 | 2019-05-28 | Cisco Technology, Inc. | Permutation-based content encryption with manifests in a content centric network |
| US10313227B2 (en) | 2015-09-24 | 2019-06-04 | Cisco Technology, Inc. | System and method for eliminating undetected interest looping in information-centric networks |
| US10320675B2 (en) | 2016-05-04 | 2019-06-11 | Cisco Technology, Inc. | System and method for routing packets in a stateless content centric network |
| US10320760B2 (en) | 2016-04-01 | 2019-06-11 | Cisco Technology, Inc. | Method and system for mutating and caching content in a content centric network |
| US10333840B2 (en) | 2015-02-06 | 2019-06-25 | Cisco Technology, Inc. | System and method for on-demand content exchange with adaptive naming in information-centric networks |
| US10355999B2 (en) | 2015-09-23 | 2019-07-16 | Cisco Technology, Inc. | Flow control with network named fragments |
| US10404450B2 (en) | 2016-05-02 | 2019-09-03 | Cisco Technology, Inc. | Schematized access control in a content centric network |
| US10425503B2 (en) | 2016-04-07 | 2019-09-24 | Cisco Technology, Inc. | Shared pending interest table in a content centric network |
| US10447805B2 (en) | 2016-10-10 | 2019-10-15 | Cisco Technology, Inc. | Distributed consensus in a content centric network |
| US10454820B2 (en) | 2015-09-29 | 2019-10-22 | Cisco Technology, Inc. | System and method for stateless information-centric networking |
| US10503730B1 (en) | 2015-12-28 | 2019-12-10 | Ionic Security Inc. | Systems and methods for cryptographically-secure queries using filters generated by multiple parties |
| US10547589B2 (en) | 2016-05-09 | 2020-01-28 | Cisco Technology, Inc. | System for implementing a small computer systems interface protocol over a content centric network |
| US10565183B1 (en)* | 2016-05-02 | 2020-02-18 | Pure Storage, Inc. | Efficient deduplication signature utilization |
| WO2020061051A1 (en)* | 2018-09-17 | 2020-03-26 | Valimail Inc. | Entity-separated email domain authentication for known and open sign-up domains |
| US10701038B2 (en) | 2015-07-27 | 2020-06-30 | Cisco Technology, Inc. | Content negotiation in a content centric network |
| US10742596B2 (en) | 2016-03-04 | 2020-08-11 | Cisco Technology, Inc. | Method and system for reducing a collision probability of hash-based names using a publisher identifier |
| US10805270B2 (en) | 2016-09-26 | 2020-10-13 | Agari Data, Inc. | Mitigating communication risk by verifying a sender of a message |
| US10805314B2 (en) | 2017-05-19 | 2020-10-13 | Agari Data, Inc. | Using message context to evaluate security of requested data |
| US10805251B2 (en)* | 2013-10-30 | 2020-10-13 | Mesh Labs Inc. | Method and system for filtering electronic communications |
| US10880322B1 (en) | 2016-09-26 | 2020-12-29 | Agari Data, Inc. | Automated tracking of interaction with a resource of a message |
| US20210067515A1 (en)* | 2018-11-21 | 2021-03-04 | Capital One Services, Llc | Method and System for Electronic Mail Attachment Management |
| US10956412B2 (en) | 2016-08-09 | 2021-03-23 | Cisco Technology, Inc. | Method and system for conjunctive normal form attribute matching in a content centric network |
| US11005989B1 (en) | 2013-11-07 | 2021-05-11 | Rightquestion, Llc | Validating automatic number identification data |
| US11019076B1 (en) | 2017-04-26 | 2021-05-25 | Agari Data, Inc. | Message security assessment using sender identity profiles |
| US11044267B2 (en) | 2016-11-30 | 2021-06-22 | Agari Data, Inc. | Using a measure of influence of sender in determining a security risk associated with an electronic message |
| US11095586B2 (en)* | 2014-04-29 | 2021-08-17 | At&T Intellectual Property I, L.P. | Detection of spam messages |
| US11102244B1 (en)* | 2017-06-07 | 2021-08-24 | Agari Data, Inc. | Automated intelligence gathering |
| US11132335B2 (en)* | 2017-12-12 | 2021-09-28 | Interset Software, Inc. | Systems and methods for file fingerprinting |
| US20210314748A1 (en)* | 2020-04-01 | 2021-10-07 | Lg Electronics Inc. | Verification of messages using hash chaining |
| US11151087B2 (en) | 2017-12-12 | 2021-10-19 | Interset Software Inc. | Tracking file movement in a network environment |
| US11210412B1 (en) | 2017-02-01 | 2021-12-28 | Ionic Security Inc. | Systems and methods for requiring cryptographic data protection as a precondition of system access |
| US11232216B1 (en) | 2015-12-28 | 2022-01-25 | Ionic Security Inc. | Systems and methods for generation of secure indexes for cryptographically-secure queries |
| US20220141165A1 (en)* | 2020-10-29 | 2022-05-05 | Proofpoint, Inc. | Bulk Messaging Detection and Enforcement |
| US11436656B2 (en) | 2016-03-18 | 2022-09-06 | Palo Alto Research Center Incorporated | System and method for a real-time egocentric collaborative filter on large datasets |
| US11516248B2 (en)* | 2017-08-25 | 2022-11-29 | Ecrime Management Strategies, Inc. | Security system for detection and mitigation of malicious communications |
| US20220417278A1 (en)* | 2016-10-31 | 2022-12-29 | KnowBe4, Inc. | Systems and methods for an artificial intelligence driven agent |
| US11582190B2 (en)* | 2020-02-10 | 2023-02-14 | Proofpoint, Inc. | Electronic message processing systems and methods |
| US11641331B2 (en)* | 2019-06-04 | 2023-05-02 | Microsoft Technology Licensing, Llc | System and method for blocking distribution of non-acceptable attachments |
| US11722513B2 (en) | 2016-11-30 | 2023-08-08 | Agari Data, Inc. | Using a measure of influence of sender in determining a security risk associated with an electronic message |
| US11757914B1 (en)* | 2017-06-07 | 2023-09-12 | Agari Data, Inc. | Automated responsive message to determine a security risk of a message sender |
| US20230370436A1 (en)* | 2020-05-27 | 2023-11-16 | Step Software Inc. | Systems and methods for data communications |
| US11936604B2 (en) | 2016-09-26 | 2024-03-19 | Agari Data, Inc. | Multi-level security analysis and intermediate delivery of an electronic message |
Families Citing this family (105)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US6628194B1 (en)* | 1999-08-31 | 2003-09-30 | At&T Wireless Services, Inc. | Filtered in-box for voice mail, e-mail, pages, web-based information, and faxes |
| US7194464B2 (en) | 2001-12-07 | 2007-03-20 | Websense, Inc. | System and method for adapting an internet filter |
| US20040193691A1 (en)* | 2003-03-31 | 2004-09-30 | Chang William I. | System and method for providing an open eMail directory |
| US7814545B2 (en) | 2003-07-22 | 2010-10-12 | Sonicwall, Inc. | Message classification using classifiers |
| US7912905B2 (en)* | 2004-05-18 | 2011-03-22 | Computer Associates Think, Inc. | System and method for filtering network messages |
| US7565445B2 (en)* | 2004-06-18 | 2009-07-21 | Fortinet, Inc. | Systems and methods for categorizing network traffic content |
| FR2875317A1 (en)* | 2004-09-10 | 2006-03-17 | France Telecom | METHOD FOR MONITORING ELECTRONIC COURIERES ISSUED AND / OR RECEIVED BY A CLIENT OF AN INTERNET ACCESS PROVIDER WITHIN A TELECOMMUNICATION NETWORK |
| US7630381B1 (en)* | 2004-09-27 | 2009-12-08 | Radix Holdings, Llc | Distributed patch distribution |
| US20060227772A1 (en)* | 2005-03-30 | 2006-10-12 | Fujitsu Limited | Method and system for packet data communication between networks |
| US7873998B1 (en)* | 2005-07-19 | 2011-01-18 | Trustwave Holdings, Inc. | Rapidly propagating threat detection |
| US8615800B2 (en) | 2006-07-10 | 2013-12-24 | Websense, Inc. | System and method for analyzing web content |
| US8020206B2 (en) | 2006-07-10 | 2011-09-13 | Websense, Inc. | System and method of analyzing web content |
| US8856920B2 (en)* | 2006-09-18 | 2014-10-07 | Alcatel Lucent | System and method of securely processing lawfully intercepted network traffic |
| US9654495B2 (en) | 2006-12-01 | 2017-05-16 | Websense, Llc | System and method of analyzing web addresses |
| GB2458094A (en) | 2007-01-09 | 2009-09-09 | Surfcontrol On Demand Ltd | URL interception and categorization in firewalls |
| GB0709527D0 (en) | 2007-05-18 | 2007-06-27 | Surfcontrol Plc | Electronic messaging system, message processing apparatus and message processing method |
| US8489610B2 (en)* | 2008-03-28 | 2013-07-16 | Nec Corporation | Method, system and program for information re-organization |
| US8161188B2 (en)* | 2008-05-04 | 2012-04-17 | Check Point Software Technologies, Ltd | Devices and methods for providing network access control utilizing traffic-regulation hardware |
| US8214977B2 (en)* | 2008-05-21 | 2012-07-10 | Symantec Corporation | Centralized scanner database with optimal definition distribution using network queries |
| EP2318955A1 (en) | 2008-06-30 | 2011-05-11 | Websense, Inc. | System and method for dynamic and real-time categorization of webpages |
| US9177144B2 (en)* | 2008-10-30 | 2015-11-03 | Mcafee, Inc. | Structural recognition of malicious code patterns |
| US20100325372A1 (en)* | 2009-06-17 | 2010-12-23 | Housty Oswin E | Parallel training of dynamic random access memory channel controllers |
| US8489685B2 (en) | 2009-07-17 | 2013-07-16 | Aryaka Networks, Inc. | Application acceleration as a service system and method |
| US8874663B2 (en)* | 2009-08-28 | 2014-10-28 | Facebook, Inc. | Comparing similarity between documents for filtering unwanted documents |
| CN102045305B (en)* | 2009-10-20 | 2015-06-10 | 中兴通讯股份有限公司 | Method and system for monitoring and tracking multimedia resource transmission |
| US8751808B2 (en)* | 2009-11-12 | 2014-06-10 | Roy Gelbard | Method and system for sharing trusted contact information |
| KR20120066465A (en)* | 2010-12-14 | 2012-06-22 | 한국전자통신연구원 | Method for blocking denial-of-service attack |
| US9058492B1 (en)* | 2011-02-14 | 2015-06-16 | Symantec Corporation | Techniques for reducing executable code vulnerability |
| US8458796B2 (en)* | 2011-03-08 | 2013-06-04 | Hewlett-Packard Development Company, L.P. | Methods and systems for full pattern matching in hardware |
| US8462781B2 (en) | 2011-04-06 | 2013-06-11 | Anue Systems, Inc. | Systems and methods for in-line removal of duplicate network packets |
| US8806647B1 (en)* | 2011-04-25 | 2014-08-12 | Twitter, Inc. | Behavioral scanning of mobile applications |
| US8621630B2 (en)* | 2011-06-17 | 2013-12-31 | Microsoft Corporation | System, method and device for cloud-based content inspection for mobile devices |
| US9553817B1 (en)* | 2011-07-14 | 2017-01-24 | Sprint Communications Company L.P. | Diverse transmission of packet content |
| US8543543B2 (en)* | 2011-09-13 | 2013-09-24 | Microsoft Corporation | Hash-based file comparison |
| US20130184878A1 (en)* | 2012-01-13 | 2013-07-18 | General Electric Company | Systems and Methods for Tracing Nodes in an Electrical Network |
| US8954519B2 (en) | 2012-01-25 | 2015-02-10 | Bitdefender IPR Management Ltd. | Systems and methods for spam detection using character histograms |
| US9497149B2 (en)* | 2012-02-03 | 2016-11-15 | Richard Kramer | System and method for reducing unsolicited E-mails |
| CN102664875B (en)* | 2012-03-31 | 2014-12-17 | 华中科技大学 | Malicious code type detection method based on cloud mode |
| US8347391B1 (en) | 2012-05-23 | 2013-01-01 | TrustPipe LLC | System and method for detecting network activity of interest |
| US20140007229A1 (en)* | 2012-06-29 | 2014-01-02 | Christopher T. Smith | System and method for identifying installed software products |
| US9491069B2 (en) | 2012-07-29 | 2016-11-08 | Verint Systems Ltd. | System and method of high volume rule engine |
| KR101336278B1 (en) | 2012-09-19 | 2013-12-03 | 충북대학교 산학협력단 | Light-weight hash algorithm for data security in wireless sensor networks |
| US10346369B2 (en) | 2012-10-11 | 2019-07-09 | Delphix Corp. | Retrieving point-in-time copies of a source database for creating virtual databases |
| EP2720416A1 (en)* | 2012-10-12 | 2014-04-16 | Anam Technologies Limited | Method for user reporting of spam mobile messages and filter node |
| US9241259B2 (en) | 2012-11-30 | 2016-01-19 | Websense, Inc. | Method and apparatus for managing the transfer of sensitive information to mobile devices |
| US9202050B1 (en)* | 2012-12-14 | 2015-12-01 | Symantec Corporation | Systems and methods for detecting malicious files |
| US9332028B2 (en) | 2013-01-25 | 2016-05-03 | REMTCS Inc. | System, method, and apparatus for providing network security |
| US9525700B1 (en) | 2013-01-25 | 2016-12-20 | REMTCS Inc. | System and method for detecting malicious activity and harmful hardware/software modifications to a vehicle |
| US8856324B2 (en) | 2013-01-28 | 2014-10-07 | TrustPipe LLC | System and method for detecting a compromised computing system |
| US8935783B2 (en) | 2013-03-08 | 2015-01-13 | Bitdefender IPR Management Ltd. | Document classification using multiscale text fingerprints |
| US8959595B2 (en) | 2013-03-15 | 2015-02-17 | Bullaproof, Inc. | Methods and systems for providing secure transactions |
| US9792436B1 (en)* | 2013-04-29 | 2017-10-17 | Symantec Corporation | Techniques for remediating an infected file |
| US9544256B2 (en)* | 2013-06-28 | 2017-01-10 | Td Ameritrade Ip Company, Inc. | Crowdsourcing e-mail filtering |
| US9319425B2 (en)* | 2013-07-23 | 2016-04-19 | Crypteia Networks S.A. | Systems and methods for self-tuning network intrusion detection and prevention |
| US10075460B2 (en) | 2013-10-16 | 2018-09-11 | REMTCS Inc. | Power grid universal detection and countermeasure overlay intelligence ultra-low latency hypervisor |
| US9392007B2 (en) | 2013-11-04 | 2016-07-12 | Crypteia Networks S.A. | System and method for identifying infected networks and systems from unknown attacks |
| US9853885B1 (en) | 2014-03-18 | 2017-12-26 | Amazon Technologies, Inc. | Using packet duplication in a packet-switched network to increase reliability |
| US9871720B1 (en)* | 2014-03-18 | 2018-01-16 | Amazon Technologies, Inc. | Using packet duplication with encapsulation in a packet-switched network to increase reliability |
| WO2015142250A1 (en)* | 2014-03-21 | 2015-09-24 | Telefonaktiebolaget L M Ericsson (Publ) | Addressing for device to device communications |
| US10057850B2 (en)* | 2014-03-24 | 2018-08-21 | Acer Incorporated | Methods for deferring communications between a mobile communication device and a service network |
| US9443108B1 (en)* | 2014-06-27 | 2016-09-13 | Amazon Technologies, Inc. | Secure timestamping |
| US10721267B1 (en)* | 2014-07-18 | 2020-07-21 | NortonLifeLock Inc. | Systems and methods for detecting system attacks |
| US9363280B1 (en) | 2014-08-22 | 2016-06-07 | Fireeye, Inc. | System and method of detecting delivery of malware using cross-customer data |
| US9876806B2 (en)* | 2014-09-25 | 2018-01-23 | Mcafee, Llc | Behavioral detection of malware agents |
| US10091174B2 (en)* | 2014-09-29 | 2018-10-02 | Dropbox, Inc. | Identifying related user accounts based on authentication data |
| US9942182B2 (en) | 2014-11-17 | 2018-04-10 | At&T Intellectual Property I, L.P. | System and method for cloud based IP mobile messaging spam detection and defense |
| US9160680B1 (en) | 2014-11-18 | 2015-10-13 | Kaspersky Lab Zao | System and method for dynamic network resource categorization re-assignment |
| US10044625B2 (en) | 2014-11-25 | 2018-08-07 | Keysight Technologies Singapore (Holdings) Pte Ltd | Hash level load balancing for deduplication of network packets |
| US9646159B2 (en)* | 2015-03-31 | 2017-05-09 | Juniper Networks, Inc. | Multi-file malware analysis |
| US9781131B2 (en)* | 2015-04-22 | 2017-10-03 | Aktiebolaget Skf | Systems and methods for securing remote configuration |
| US9641543B2 (en)* | 2015-04-22 | 2017-05-02 | Aktiebolaget AKF | Systems and methods for securing remote configuration |
| CA2931455C (en) | 2015-05-27 | 2017-06-06 | OTC Systems Ltd. | System for analyzing email for compliance with rules |
| RU2629444C2 (en) | 2015-06-30 | 2017-08-29 | Общество С Ограниченной Ответственностью "Яндекс" | Method and server for determining spam activity in cloud system |
| CN105160268B (en)* | 2015-08-06 | 2018-06-01 | 武汉亚星电子技术有限责任公司 | Data tracking and monitoring system, intelligent router and its data tracking monitoring method |
| US20230308459A1 (en)* | 2015-10-28 | 2023-09-28 | Qomplx, Inc. | Authentication attack detection and mitigation with embedded authentication and delegation |
| US10558822B2 (en)* | 2015-12-15 | 2020-02-11 | Oath Inc. | Enforcing anonymity in the auditing of electronic documents |
| US10038603B1 (en) | 2016-02-23 | 2018-07-31 | Area 1 Security, Inc. | Packet capture collection tasking system |
| US10187400B1 (en) | 2016-02-23 | 2019-01-22 | Area 1 Security, Inc. | Packet filters in security appliances with modes and intervals |
| US10778721B1 (en) | 2016-02-26 | 2020-09-15 | Arista Networks, Inc. | Hash-based ACL lookup offload |
| RU2634180C1 (en) | 2016-06-24 | 2017-10-24 | Акционерное общество "Лаборатория Касперского" | System and method for determining spam-containing message by topic of message sent via e-mail |
| US10241847B2 (en)* | 2016-07-19 | 2019-03-26 | 2236008 Ontario Inc. | Anomaly detection using sequences of system calls |
| EP3297221B1 (en)* | 2016-09-19 | 2018-11-14 | retarus GmbH | Technique for detecting suspicious electronic messages |
| US10657182B2 (en)* | 2016-09-20 | 2020-05-19 | International Business Machines Corporation | Similar email spam detection |
| US10708272B1 (en)* | 2017-02-10 | 2020-07-07 | Arista Networks, Inc. | Optimized hash-based ACL lookup offload |
| US10142263B2 (en) | 2017-02-21 | 2018-11-27 | Keysight Technologies Singapore (Holdings) Pte Ltd | Packet deduplication for network packet monitoring in virtual processing environments |
| CN107196931B (en)* | 2017-05-17 | 2020-09-08 | 南京南瑞继保电气有限公司 | Deep packet inspection method based on network isolation device |
| US10834099B2 (en)* | 2017-05-23 | 2020-11-10 | Juniper Networks, Inc. | Identifying a file using metadata and determining a security classification of the file before completing receipt of the file |
| US10708283B2 (en)* | 2017-06-30 | 2020-07-07 | Fortinet, Inc. | Detection and mitigation of time-delay based network attacks |
| US10594725B2 (en)* | 2017-07-27 | 2020-03-17 | Cypress Semiconductor Corporation | Generating and analyzing network profile data |
| US10747729B2 (en) | 2017-09-01 | 2020-08-18 | Microsoft Technology Licensing, Llc | Device specific chunked hash size tuning |
| CN109660487B (en)* | 2017-10-10 | 2021-11-09 | 武汉斗鱼网络科技有限公司 | Authorization method based on H5 webpage, storage medium, electronic device and system |
| US11477222B2 (en)* | 2018-02-20 | 2022-10-18 | Darktrace Holdings Limited | Cyber threat defense system protecting email networks with machine learning models using a range of metadata from observed email communications |
| US11038900B2 (en)* | 2018-09-04 | 2021-06-15 | Cisco Technology, Inc. | Structural command and control detection of polymorphic malware |
| US12058776B2 (en)* | 2019-02-14 | 2024-08-06 | Telefonaktiebolaget Lm Ericsson (Publ) | Methods, apparatus and computer-readable mediums relating to capability reporting in a wireless network |
| CN109889891B (en)* | 2019-03-05 | 2023-03-24 | 腾讯科技(深圳)有限公司 | Method, device and storage medium for acquiring target media file |
| US11777712B2 (en)* | 2019-03-22 | 2023-10-03 | International Business Machines Corporation | Information management in a database |
| US11101979B2 (en) | 2019-05-30 | 2021-08-24 | Kira Inc. | Method and system for creating word-level differential privacy using feature hashing techniques |
| US11363064B2 (en)* | 2019-07-12 | 2022-06-14 | Adobe Inc. | Identifying spam using near-duplicate detection for text and images |
| US11086947B1 (en)* | 2019-10-11 | 2021-08-10 | Tubular Labs, Inc. | Efficient uniques querying |
| US12375527B2 (en)* | 2020-06-24 | 2025-07-29 | Fortinet, Inc. | Leveraging network security scanning to obtain enhanced information regarding an attack chain involving a decoy file |
| US20230418954A1 (en)* | 2022-06-27 | 2023-12-28 | Micron Technology, Inc. | Detecting information modification in a memory system |
| US12299410B2 (en)* | 2022-06-30 | 2025-05-13 | International Business Machines Corporation | String similarity based weighted min-hashing |
| US20240039730A1 (en) | 2022-07-27 | 2024-02-01 | Rapid7, Inc. | Hashing techniques for associating assets related to events with addressable computer network assets |
| US12072961B2 (en) | 2022-07-29 | 2024-08-27 | Bank Of America Corporation | Systems and methods for password spraying identification and prevention using hash signature segmentation and behavior clustering analysis |
| CN115604026B (en)* | 2022-11-24 | 2023-05-16 | 清华大学 | Interactive security analysis method and system for TCP/IP layered network model |
Citations (95)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US4641274A (en)* | 1982-12-03 | 1987-02-03 | International Business Machines Corporation | Method for communicating changes made to text form a text processor to a remote host |
| US4996711A (en)* | 1989-06-21 | 1991-02-26 | Chaum David L | Selected-exponent signature systems |
| US5276869A (en)* | 1990-09-10 | 1994-01-04 | International Business Machines Corporation | System for selecting document recipients as determined by technical content of document and for electronically corroborating receipt of document |
| US5276737A (en)* | 1992-04-20 | 1994-01-04 | Silvio Micali | Fair cryptosystems and methods of use |
| US5276736A (en)* | 1990-01-29 | 1994-01-04 | David Chaum | Optionally moderated transaction systems |
| US5276901A (en)* | 1991-12-16 | 1994-01-04 | International Business Machines Corporation | System for controlling group access to objects using group access control folder and group identification as individual user |
| US5276735A (en)* | 1992-04-17 | 1994-01-04 | Secure Computing Corporation | Data enclave and trusted path system |
| US5278901A (en)* | 1992-04-30 | 1994-01-11 | International Business Machines Corporation | Pattern-oriented intrusion-detection system and method |
| US5280527A (en)* | 1992-04-14 | 1994-01-18 | Kamahira Safe Co., Inc. | Biometric token for authorizing access to a host system |
| US5283887A (en)* | 1990-12-19 | 1994-02-01 | Bull Hn Information Systems Inc. | Automatic document format conversion in an electronic mail system based upon user preference |
| US5379374A (en)* | 1990-11-21 | 1995-01-03 | Hitachi, Ltd. | Collaborative information processing system and workstation |
| US5379340A (en)* | 1991-08-02 | 1995-01-03 | Betterprize Limited | Text communication system |
| US5386470A (en)* | 1989-12-06 | 1995-01-31 | 3Com Ireland | Repeaters for secure local area networks |
| US5388189A (en)* | 1989-12-06 | 1995-02-07 | Racal-Datacom, Inc. | Alarm filter in an expert system for communications network |
| US5481312A (en)* | 1994-09-12 | 1996-01-02 | At&T Corp. | Method of and apparatus for the transmission of high and low priority segments of a video bitstream over packet networks |
| US5481613A (en)* | 1994-04-15 | 1996-01-02 | Northern Telecom Limited | Computer network cryptographic key distribution system |
| US5483466A (en)* | 1992-11-13 | 1996-01-09 | Hitachi, Ltd. | Client/server system and mail reception/display control method |
| US5485460A (en)* | 1994-08-19 | 1996-01-16 | Microsoft Corporation | System and method for running multiple incompatible network protocol stacks |
| US5485409A (en)* | 1992-04-30 | 1996-01-16 | International Business Machines Corporation | Automated penetration analysis system and method |
| US5491750A (en)* | 1993-12-30 | 1996-02-13 | International Business Machines Corporation | Method and apparatus for three-party entity authentication and key distribution using message authentication codes |
| US5495610A (en)* | 1989-11-30 | 1996-02-27 | Seer Technologies, Inc. | Software distribution system to build and distribute a software release |
| US5602918A (en)* | 1995-12-22 | 1997-02-11 | Virtual Open Network Environment Corp. | Application level security system and method |
| US5604490A (en)* | 1994-09-09 | 1997-02-18 | International Business Machines Corporation | Method and system for providing a user access to multiple secured subsystems |
| US5606668A (en)* | 1993-12-15 | 1997-02-25 | Checkpoint Software Technologies Ltd. | System for securing inbound and outbound data packet flow in a computer network |
| US5706507A (en)* | 1995-07-05 | 1998-01-06 | International Business Machines Corporation | System and method for controlling access to data located on a content server |
| US5706442A (en)* | 1995-12-20 | 1998-01-06 | Block Financial Corporation | System for on-line financial services using distributed objects |
| US5708780A (en)* | 1995-06-07 | 1998-01-13 | Open Market, Inc. | Internet server access control and monitoring systems |
| US5708826A (en)* | 1995-05-16 | 1998-01-13 | Fujitsu Limited | Apparatus and method for converting presentation data |
| US5710883A (en)* | 1995-03-10 | 1998-01-20 | Stanford University | Hypertext document transport mechanism for firewall-compatible distributed world-wide web publishing |
| US5717758A (en)* | 1995-11-02 | 1998-02-10 | Micall; Silvio | Witness-based certificate revocation system |
| US5717757A (en)* | 1996-08-29 | 1998-02-10 | Micali; Silvio | Certificate issue lists |
| US5857022A (en)* | 1994-01-13 | 1999-01-05 | Certco Llc | Enhanced cryptographic system and method with key escrow feature |
| US5860068A (en)* | 1997-12-04 | 1999-01-12 | Petabyte Corporation | Method and system for custom manufacture and delivery of a data product |
| US5859966A (en)* | 1995-10-10 | 1999-01-12 | Data General Corporation | Security system for computer systems |
| US5862325A (en)* | 1996-02-29 | 1999-01-19 | Intermind Corporation | Computer-based communication system and method using metadata defining a control structure |
| US5864667A (en)* | 1995-04-05 | 1999-01-26 | Diversinet Corp. | Method for safe communications |
| US5864852A (en)* | 1996-04-26 | 1999-01-26 | Netscape Communications Corporation | Proxy server caching mechanism that provides a file directory structure and a mapping mechanism within the file directory structure |
| US5864683A (en)* | 1994-10-12 | 1999-01-26 | Secure Computing Corporartion | System for providing secure internetwork by connecting type enforcing secure computers to external network for limiting access to data based on user and process access rights |
| US5872844A (en)* | 1996-11-18 | 1999-02-16 | Microsoft Corporation | System and method for detecting fraudulent expenditure of transferable electronic assets |
| US5872931A (en)* | 1996-08-13 | 1999-02-16 | Veritas Software, Corp. | Management agent automatically executes corrective scripts in accordance with occurrences of specified events regardless of conditions of management interface and management engine |
| US6012144A (en)* | 1996-10-08 | 2000-01-04 | Pickett; Thomas E. | Transaction security method and apparatus |
| US6014651A (en)* | 1993-11-04 | 2000-01-11 | Crawford; Christopher M. | Commercial online software distribution systems and methods using encryption for security |
| US6021510A (en)* | 1997-11-24 | 2000-02-01 | Symantec Corporation | Antivirus accelerator |
| US6023723A (en)* | 1997-12-22 | 2000-02-08 | Accepted Marketing, Inc. | Method and system for filtering unwanted junk e-mail utilizing a plurality of filtering mechanisms |
| US6026414A (en)* | 1998-03-05 | 2000-02-15 | International Business Machines Corporation | System including a proxy client to backup files in a distributed computing environment |
| US6029256A (en)* | 1997-12-31 | 2000-02-22 | Network Associates, Inc. | Method and system for allowing computer programs easy access to features of a virus scanning engine |
| US6178509B1 (en)* | 1996-06-13 | 2001-01-23 | Intel Corporation | Tamper resistant methods and apparatus |
| US6178242B1 (en)* | 1997-02-07 | 2001-01-23 | Nds Limited | Digital recording protection system |
| US6182226B1 (en)* | 1998-03-18 | 2001-01-30 | Secure Computing Corporation | System and method for controlling interactions between networks |
| US6182142B1 (en)* | 1998-07-10 | 2001-01-30 | Encommerce, Inc. | Distributed access management of information resources |
| US6185678B1 (en)* | 1997-10-02 | 2001-02-06 | Trustees Of The University Of Pennsylvania | Secure and reliable bootstrap architecture |
| US6185682B1 (en)* | 1997-06-03 | 2001-02-06 | U.S. Philips Corporation | Authentication system |
| US6185689B1 (en)* | 1998-06-24 | 2001-02-06 | Richard S. Carson & Assoc., Inc. | Method for network self security assessment |
| US6192407B1 (en)* | 1996-10-24 | 2001-02-20 | Tumbleweed Communications Corp. | Private, trackable URLs for directed document delivery |
| US6192360B1 (en)* | 1998-06-23 | 2001-02-20 | Microsoft Corporation | Methods and apparatus for classifying text and for building a text classifier |
| US20020001384A1 (en)* | 2000-04-13 | 2002-01-03 | Broadcom Corporation | Authentication engine architecture and method |
| US6338141B1 (en)* | 1998-09-30 | 2002-01-08 | Cybersoft, Inc. | Method and apparatus for computer virus detection, analysis, and removal in real time |
| US20020004902A1 (en)* | 2000-07-07 | 2002-01-10 | Eng-Whatt Toh | Secure and reliable document delivery |
| US6341369B1 (en)* | 1998-12-03 | 2002-01-22 | International Business Machines Corporation | Method and data processing system for specifying and applying rules to classification-based decision points in an application system |
| US20020016910A1 (en)* | 2000-02-11 | 2002-02-07 | Wright Robert P. | Method for secure distribution of documents over electronic networks |
| US20020016826A1 (en)* | 1998-02-07 | 2002-02-07 | Olof Johansson | Firewall apparatus and method of controlling network data packet traffic between internal and external networks |
| US20020019945A1 (en)* | 2000-04-28 | 2002-02-14 | Internet Security System, Inc. | System and method for managing security events on a network |
| US20020023140A1 (en)* | 2000-06-08 | 2002-02-21 | Hile John K. | Electronic document delivery system |
| US20020026591A1 (en)* | 1998-06-15 | 2002-02-28 | Hartley Bruce V. | Method and apparatus for assessing the security of a computer system |
| US20030004689A1 (en)* | 2001-06-13 | 2003-01-02 | Gupta Ramesh M. | Hierarchy-based method and apparatus for detecting attacks on a computer system |
| US20030005326A1 (en)* | 2001-06-29 | 2003-01-02 | Todd Flemming | Method and system for implementing a security application services provider |
| US20030009554A1 (en)* | 2001-07-09 | 2003-01-09 | Burch Hal Joseph | Method and apparatus for tracing packets in a communications network |
| US20030009693A1 (en)* | 2001-07-09 | 2003-01-09 | International Business Machines Corporation | Dynamic intrusion detection for computer systems |
| US20030009696A1 (en)* | 2001-05-18 | 2003-01-09 | Bunker V. Nelson Waldo | Network security testing |
| US6507851B1 (en)* | 1998-12-03 | 2003-01-14 | Sony Corporation | Customer information retrieving method, a customer information retrieving apparatus, a data preparation method, and a database |
| US20030014664A1 (en)* | 2001-06-29 | 2003-01-16 | Daavid Hentunen | Intrusion detection method and system |
| US6510466B1 (en)* | 1998-12-14 | 2003-01-21 | International Business Machines Corporation | Methods, systems and computer program products for centralized management of application programs on a network |
| US6510431B1 (en)* | 1999-06-28 | 2003-01-21 | International Business Machines Corporation | Method and system for the routing of requests using an automated classification and profile matching in a networked environment |
| US6510464B1 (en)* | 1999-12-14 | 2003-01-21 | Verizon Corporate Services Group Inc. | Secure gateway having routing feature |
| US20030023692A1 (en)* | 2001-07-27 | 2003-01-30 | Fujitsu Limited | Electronic message delivery system, electronic message delivery managment server, and recording medium in which electronic message delivery management program is recorded |
| US20030021280A1 (en)* | 2001-07-26 | 2003-01-30 | Makinson Graham Arthur | Malware scanning using a network bridge |
| US20030023873A1 (en)* | 2001-03-16 | 2003-01-30 | Yuval Ben-Itzhak | Application-layer security method and system |
| US20030023874A1 (en)* | 2001-07-16 | 2003-01-30 | Rudy Prokupets | System for integrating security and access for facilities and information systems |
| US20030023875A1 (en)* | 2001-07-26 | 2003-01-30 | Hursey Neil John | Detecting e-mail propagated malware |
| US20030023695A1 (en)* | 1999-02-26 | 2003-01-30 | Atabok Japan, Inc. | Modifying an electronic mail system to produce a secure delivery system |
| US6675209B1 (en)* | 1999-07-19 | 2004-01-06 | Hewlett-Packard Development Company, L.P. | Method and system for assigning priority among network segments |
| US6675153B1 (en)* | 1999-07-06 | 2004-01-06 | Zix Corporation | Transaction authorization system |
| US6681331B1 (en)* | 1999-05-11 | 2004-01-20 | Cylant, Inc. | Dynamic software system intrusion detection |
| US20040015554A1 (en)* | 2002-07-16 | 2004-01-22 | Brian Wilson | Active e-mail filter with challenge-response |
| US6684335B1 (en)* | 1999-08-19 | 2004-01-27 | Epstein, Iii Edwin A. | Resistance cell architecture |
| US6842860B1 (en)* | 1999-07-23 | 2005-01-11 | Networks Associates Technology, Inc. | System and method for selectively authenticating data |
| US6842861B1 (en)* | 2000-03-24 | 2005-01-11 | Networks Associates Technology, Inc. | Method and system for detecting viruses on handheld computers |
| US6845449B1 (en)* | 1999-07-23 | 2005-01-18 | Networks Associates Technology, Inc. | System and method for fast nested message authentication codes and error correction codes |
| US20050014749A1 (en)* | 2003-06-20 | 2005-01-20 | Amgen Inc. | Piperazine derivatives and methods of use |
| US6847888B2 (en)* | 2002-08-07 | 2005-01-25 | Hrl Laboratories, Llc | Method and apparatus for geographic shape preservation for identification |
| US20050021738A1 (en)* | 2002-11-12 | 2005-01-27 | Kenneth Goeller | Network geo-location system |
| US20050021736A1 (en)* | 2003-01-07 | 2005-01-27 | International Business Machines Corporation | Method and system for monitoring performance of distributed applications |
| US6985923B1 (en)* | 2000-06-13 | 2006-01-10 | International Business Machines Corporation | Method, article of manufacture and apparatus for processing redundant electronic mail messages |
| US6993660B1 (en)* | 2001-08-03 | 2006-01-31 | Mcafee, Inc. | System and method for performing efficient computer virus scanning of transient messages using checksums in a distributed computing environment |
| US7159237B2 (en)* | 2000-03-16 | 2007-01-02 | Counterpane Internet Security, Inc. | Method and system for dynamic network intrusion monitoring, detection and response |
Family Cites Families (783)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| FR2258112A5 (en) | 1973-11-30 | 1975-08-08 | Honeywell Bull Soc Ind | |
| US3956615A (en) | 1974-06-25 | 1976-05-11 | Ibm Corporation | Transaction execution system with secure data storage and communications |
| US4104721A (en) | 1976-12-30 | 1978-08-01 | International Business Machines Corporation | Hierarchical security mechanism for dynamically assigning security levels to object programs |
| US4200770A (en) | 1977-09-06 | 1980-04-29 | Stanford University | Cryptographic apparatus and method |
| US4405829A (en) | 1977-12-14 | 1983-09-20 | Massachusetts Institute Of Technology | Cryptographic communications system and method |
| US4289930A (en) | 1978-11-30 | 1981-09-15 | The General Electric Company Limited | Electronic apparatus for the display of information received over a line |
| US4386416A (en) | 1980-06-02 | 1983-05-31 | Mostek Corporation | Data compression, encryption, and in-line transmission system |
| US4384325A (en) | 1980-06-23 | 1983-05-17 | Sperry Corporation | Apparatus and method for searching a data base using variable search criteria |
| US4386233A (en) | 1980-09-29 | 1983-05-31 | Smid Miles E | Crytographic key notarization methods and apparatus |
| US4442484A (en) | 1980-10-14 | 1984-04-10 | Intel Corporation | Microprocessor memory management and protection mechanism |
| US4648031A (en) | 1982-06-21 | 1987-03-03 | International Business Machines Corporation | Method and apparatus for restarting a computing system |
| US4532588A (en) | 1982-11-09 | 1985-07-30 | International Business Machines Corporation | Electronic document distribution network with uniform data stream |
| NL8301458A (en) | 1983-04-26 | 1984-11-16 | Philips Nv | METHOD FOR DISTRIBUTING AND USING ENCRYPTION KEYS. |
| US4870571A (en) | 1983-05-04 | 1989-09-26 | The Johns Hopkins University | Intercomputer communications based on message broadcasting with receiver selection |
| US4590470A (en) | 1983-07-11 | 1986-05-20 | At&T Bell Laboratories | User authentication system employing encryption functions |
| US4926480A (en) | 1983-08-22 | 1990-05-15 | David Chaum | Card-computer moderated systems |
| US4947430A (en) | 1987-11-23 | 1990-08-07 | David Chaum | Undeniable signature systems |
| US4584639A (en) | 1983-12-23 | 1986-04-22 | Key Logic, Inc. | Computer security system |
| US4621321A (en) | 1984-02-16 | 1986-11-04 | Honeywell Inc. | Secure data processing system architecture |
| US4710763A (en) | 1984-10-19 | 1987-12-01 | Texas Instruments Incorporated | Method for generating and displaying tree structures in a limited display area |
| US4713753A (en) | 1985-02-21 | 1987-12-15 | Honeywell Inc. | Secure data processing system architecture with format control |
| US4713780A (en) | 1985-04-15 | 1987-12-15 | Express Communications, Inc. | Electronic mail |
| US4754428A (en) | 1985-04-15 | 1988-06-28 | Express Communications, Inc. | Apparatus and method of distributing documents to remote terminals with different formats |
| US4914568A (en) | 1986-10-24 | 1990-04-03 | National Instruments, Inc. | Graphical system for modelling a process and associated method |
| US4837798A (en) | 1986-06-02 | 1989-06-06 | American Telephone And Telegraph Company | Communication system having unified messaging |
| NL8602418A (en) | 1986-09-25 | 1988-04-18 | Philips Nv | DEVICE FOR DISPLAYING A PCM MODULATED SIGNAL WITH A MUTE CIRCUIT. |
| JP2702927B2 (en) | 1987-06-15 | 1998-01-26 | 株式会社日立製作所 | String search device |
| DE3851724T2 (en) | 1987-07-08 | 1995-05-04 | Matsushita Electric Ind Co Ltd | Method and device for protecting copy signals. |
| FR2618002B1 (en) | 1987-07-10 | 1991-07-05 | Schlumberger Ind Sa | METHOD AND SYSTEM FOR AUTHENTICATING ELECTRONIC MEMORY CARDS |
| US4853961A (en) | 1987-12-18 | 1989-08-01 | Pitney Bowes Inc. | Reliable document authentication system |
| US4885789A (en) | 1988-02-01 | 1989-12-05 | International Business Machines Corporation | Remote trusted path mechanism for telnet |
| US5214702A (en) | 1988-02-12 | 1993-05-25 | Fischer Addison M | Public key/signature cryptosystem with enhanced digital signature certification |
| US5005200A (en) | 1988-02-12 | 1991-04-02 | Fischer Addison M | Public key/signature cryptosystem with enhanced digital signature certification |
| US4868877A (en) | 1988-02-12 | 1989-09-19 | Fischer Addison M | Public key/signature cryptosystem with enhanced digital signature certification |
| CA1314101C (en) | 1988-02-17 | 1993-03-02 | Henry Shao-Lin Teng | Expert system for security inspection of a digital computer system in a network environment |
| US4951196A (en) | 1988-05-04 | 1990-08-21 | Supply Tech, Inc. | Method and apparatus for electronic data interchange |
| US5008814A (en) | 1988-08-15 | 1991-04-16 | Network Equipment Technologies, Inc. | Method and apparatus for updating system software for a plurality of data processing units in a communication network |
| US5144660A (en) | 1988-08-31 | 1992-09-01 | Rose Anthony M | Securing a computer against undesired write operations to or read operations from a mass storage device |
| US5054096A (en) | 1988-10-24 | 1991-10-01 | Empire Blue Cross/Blue Shield | Method and apparatus for converting documents into electronic data for transaction processing |
| US4975950A (en) | 1988-11-03 | 1990-12-04 | Lentz Stephen A | System and method of protecting integrity of computer data and software |
| US5313637A (en) | 1988-11-29 | 1994-05-17 | Rose David K | Method and apparatus for validating authorization to access information in an information processing system |
| US5167011A (en) | 1989-02-15 | 1992-11-24 | W. H. Morris | Method for coodinating information storage and retrieval |
| US5210824A (en) | 1989-03-03 | 1993-05-11 | Xerox Corporation | Encoding-format-desensitized methods and means for interchanging electronic document as appearances |
| US5020059A (en) | 1989-03-31 | 1991-05-28 | At&T Bell Laboratories | Reconfigurable signal processor |
| US5191611A (en) | 1989-04-03 | 1993-03-02 | Lang Gerald S | Method and apparatus for protecting material on storage media and for transferring material on storage media to various recipients |
| US5144659A (en) | 1989-04-19 | 1992-09-01 | Richard P. Jones | Computer file protection system |
| US5119465A (en) | 1989-06-19 | 1992-06-02 | Digital Equipment Corporation | System for selectively converting plurality of source data structures through corresponding source intermediate structures, and target intermediate structures into selected target structure |
| GB8918553D0 (en) | 1989-08-15 | 1989-09-27 | Digital Equipment Int | Message control system |
| US5105184B1 (en) | 1989-11-09 | 1997-06-17 | Noorali Pirani | Methods for displaying and integrating commercial advertisements with computer software |
| DE68925695D1 (en) | 1989-12-13 | 1996-03-28 | Ibm | Computer system security device |
| US5093914A (en) | 1989-12-15 | 1992-03-03 | At&T Bell Laboratories | Method of controlling the execution of object-oriented programs |
| US5263157A (en) | 1990-02-15 | 1993-11-16 | International Business Machines Corporation | Method and system for providing user access control within a distributed data processing system by the exchange of access control profiles |
| JP3080382B2 (en) | 1990-02-21 | 2000-08-28 | 株式会社日立製作所 | Cryptographic communication system |
| EP0451384B1 (en) | 1990-04-10 | 1997-09-24 | International Business Machines Corporation | Hypertext data processing system and method |
| US5319776A (en) | 1990-04-19 | 1994-06-07 | Hilgraeve Corporation | In transit detection of computer virus with safeguard |
| US5210825A (en) | 1990-04-26 | 1993-05-11 | Teknekron Communications Systems, Inc. | Method and an apparatus for displaying graphical data received from a remote computer by a local computer |
| US5822527A (en) | 1990-05-04 | 1998-10-13 | Digital Equipment Corporation | Method and apparatus for information stream filtration using tagged information access and action registration |
| US5226080A (en) | 1990-06-22 | 1993-07-06 | Grid Systems Corporation | Method and apparatus for password protection of a computer |
| US5204961A (en) | 1990-06-25 | 1993-04-20 | Digital Equipment Corporation | Computer network operating with multilevel hierarchical security with selectable common trust realms and corresponding security protocols |
| US5070528A (en) | 1990-06-29 | 1991-12-03 | Digital Equipment Corporation | Generic encryption technique for communication networks |
| GB9015799D0 (en) | 1990-07-18 | 1991-06-12 | Plessey Telecomm | A data communication system |
| US5124984A (en) | 1990-08-07 | 1992-06-23 | Concord Communications, Inc. | Access controller for local area network |
| US5144557A (en) | 1990-08-13 | 1992-09-01 | International Business Machines Corporation | Method and system for document distribution by reference to a first group and particular document to a second group of user in a data processing system |
| US5247661A (en) | 1990-09-10 | 1993-09-21 | International Business Machines Corporation | Method and apparatus for automated document distribution in a data processing system |
| US5790198A (en) | 1990-09-10 | 1998-08-04 | Starsight Telecast, Inc. | Television schedule information transmission and utilization system and process |
| US5224163A (en) | 1990-09-28 | 1993-06-29 | Digital Equipment Corporation | Method for delegating authorization from one entity to another through the use of session encryption keys |
| US5315657A (en) | 1990-09-28 | 1994-05-24 | Digital Equipment Corporation | Compound principals in access control lists |
| US5239466A (en) | 1990-10-04 | 1993-08-24 | Motorola, Inc. | System for selectively routing and merging independent annotations to a document at remote locations |
| US5153918A (en) | 1990-11-19 | 1992-10-06 | Vorec Corporation | Security system for data communications |
| US5263147A (en) | 1991-03-01 | 1993-11-16 | Hughes Training, Inc. | System for providing high security for personal computers and workstations |
| JP3177684B2 (en) | 1991-03-14 | 2001-06-18 | 株式会社日立製作所 | Email system |
| US5424724A (en) | 1991-03-27 | 1995-06-13 | International Business Machines Corporation | Method and apparatus for enhanced electronic mail distribution |
| US5272754A (en) | 1991-03-28 | 1993-12-21 | Secure Computing Corporation | Secure computer interface |
| US5513323A (en) | 1991-06-14 | 1996-04-30 | International Business Machines Corporation | Method and apparatus for multistage document format transformation in a data processing system |
| US5228083A (en) | 1991-06-28 | 1993-07-13 | Digital Equipment Corporation | Cryptographic processing in a communication network, using a single cryptographic engine |
| US5577209A (en) | 1991-07-11 | 1996-11-19 | Itt Corporation | Apparatus and method for providing multi-level security for communication among computers and terminals on a network |
| US5621579A (en) | 1991-08-19 | 1997-04-15 | Index Systems, Inc. | Method for selectively playing back programs recorded on a video tape |
| US5367621A (en) | 1991-09-06 | 1994-11-22 | International Business Machines Corporation | Data processing method to provide a generalized link from a reference point in an on-line book to an arbitrary multimedia object which can be dynamically updated |
| JPH06102822A (en) | 1991-09-26 | 1994-04-15 | Rooreru Intelligent Syst:Kk | File security system |
| US5355474A (en) | 1991-09-27 | 1994-10-11 | Thuraisngham Bhavani M | System for multilevel secure database management using a knowledge base with release-based and other security constraints for query, response and update modification |
| US5200999A (en) | 1991-09-27 | 1993-04-06 | International Business Machines Corporation | Public key cryptosystem key management based on control vectors |
| US5177788A (en) | 1991-10-15 | 1993-01-05 | Ungermann-Bass, Inc. | Network message security method and apparatus |
| US5164988A (en) | 1991-10-31 | 1992-11-17 | International Business Machines Corporation | Method to establish and enforce a network cryptographic security policy in a public key cryptosystem |
| US5265164A (en) | 1991-10-31 | 1993-11-23 | International Business Machines Corporation | Cryptographic facility environment backup/restore and replication in a public key cryptosystem |
| US5325370A (en) | 1991-11-12 | 1994-06-28 | Storage Technology Corporation | Method and apparatus for recording data on magnetic tape media |
| US5210795A (en) | 1992-01-10 | 1993-05-11 | Digital Equipment Corporation | Secure user authentication from personal computer |
| DK170490B1 (en) | 1992-04-28 | 1995-09-18 | Multi Inform As | Data Processing Plant |
| FR2686755A1 (en) | 1992-01-28 | 1993-07-30 | Electricite De France | METHOD FOR ENCRYPTING MESSAGES TRANSMITTED BETWEEN INTERCONNECTED NETWORKS, ENCRYPTION APPARATUS AND DEVICE FOR COMMUNICATING ENCRYPTED DATA USING SUCH A METHOD. |
| GB9205774D0 (en) | 1992-03-17 | 1992-04-29 | Int Computers Ltd | Computer security system |
| US5333266A (en) | 1992-03-27 | 1994-07-26 | International Business Machines Corporation | Method and apparatus for message handling in computer systems |
| US5649095A (en) | 1992-03-30 | 1997-07-15 | Cozza; Paul D. | Method and apparatus for detecting computer viruses through the use of a scan information cache |
| US5278460A (en) | 1992-04-07 | 1994-01-11 | Micron Technology, Inc. | Voltage compensating CMOS input buffer |
| US5313521A (en) | 1992-04-15 | 1994-05-17 | Fujitsu Limited | Key distribution protocol for file transfer in the local area network |
| US5315658B1 (en) | 1992-04-20 | 1995-09-12 | Silvio Micali | Fair cryptosystems and methods of use |
| US5311593A (en) | 1992-05-13 | 1994-05-10 | Chipcom Corporation | Security system for a network concentrator |
| US5412717A (en) | 1992-05-15 | 1995-05-02 | Fischer; Addison M. | Computer system security method and apparatus having program authorization information data structures |
| US5241594A (en) | 1992-06-02 | 1993-08-31 | Hughes Aircraft Company | One-time logon means and methods for distributed computing systems |
| GB9212655D0 (en) | 1992-06-15 | 1992-07-29 | Digital Equipment Int | Communications system |
| WO1993026109A1 (en) | 1992-06-17 | 1993-12-23 | The Trustees Of The University Of Pennsylvania | Apparatus for providing cryptographic support in a network |
| US5359659A (en) | 1992-06-19 | 1994-10-25 | Doren Rosenthal | Method for securing software against corruption by computer viruses |
| GB9213169D0 (en) | 1992-06-22 | 1992-08-05 | Ncr Int Inc | Cryptographic key management apparatus and method |
| US5235642A (en) | 1992-07-21 | 1993-08-10 | Digital Equipment Corporation | Access control subsystem and method for distributed computer system using locally cached authentication credentials |
| IL102843A (en) | 1992-08-17 | 1996-06-18 | Zisapel Yehuda | Carrier sensing multiple access/collision detection local area networks |
| US5418908A (en) | 1992-10-15 | 1995-05-23 | International Business Machines Corporation | System for automatically establishing a link between an electronic mail item and a remotely stored reference through a place mark inserted into the item |
| US5432932A (en) | 1992-10-23 | 1995-07-11 | International Business Machines Corporation | System and method for dynamically controlling remote processes from a performance monitor |
| US5675733A (en) | 1992-11-30 | 1997-10-07 | International Business Machines Corporation | Statistical analysis and display of reception status of electronic messages |
| US5666530A (en) | 1992-12-02 | 1997-09-09 | Compaq Computer Corporation | System for automatic synchronization of common file between portable computer and host computer via communication channel selected from a plurality of usable channels there between |
| US5410326A (en) | 1992-12-04 | 1995-04-25 | Goldstein; Steven W. | Programmable remote control device for interacting with a plurality of remotely controlled devices |
| US5341426A (en) | 1992-12-15 | 1994-08-23 | Motorola, Inc. | Cryptographic key management apparatus and method |
| JPH08504326A (en) | 1992-12-15 | 1996-05-14 | コモンウェルス サイエンティフィック アンド インダストリアル リサーチ オーガナイゼーション | DNA molecule encoding an inducible plant promoter and tomato ADH2 enzyme |
| US5828893A (en) | 1992-12-24 | 1998-10-27 | Motorola, Inc. | System and method of communicating between trusted and untrusted computer systems |
| US5544320A (en) | 1993-01-08 | 1996-08-06 | Konrad; Allan M. | Remote information service access system based on a client-server-service model |
| US5440723A (en) | 1993-01-19 | 1995-08-08 | International Business Machines Corporation | Automatic immune system for computers and computer networks |
| US5351293A (en) | 1993-02-01 | 1994-09-27 | Wave Systems Corp. | System method and apparatus for authenticating an encrypted signal |
| US5406557A (en) | 1993-02-01 | 1995-04-11 | National Semiconductor Corporation | Interenterprise electronic mail hub |
| US5586260A (en) | 1993-02-12 | 1996-12-17 | Digital Equipment Corporation | Method and apparatus for authenticating a client to a server in computer systems which support different security mechanisms |
| US5299263A (en) | 1993-03-04 | 1994-03-29 | Bell Communications Research, Inc. | Two-way public key authentication and key agreement for low-cost terminals |
| US5479411A (en) | 1993-03-10 | 1995-12-26 | At&T Corp. | Multi-media integrated message arrangement |
| US5414650A (en) | 1993-03-24 | 1995-05-09 | Compression Research Group, Inc. | Parsing information onto packets using context-insensitive parsing rules based on packet characteristics |
| US5404231A (en) | 1993-05-24 | 1995-04-04 | Audiofax, Inc. | Sender-based facsimile store and forward facility |
| FR2706652B1 (en) | 1993-06-09 | 1995-08-18 | Alsthom Cge Alcatel | Device for detecting intrusions and suspicious users for a computer system and security system comprising such a device. |
| JPH0764788A (en) | 1993-06-14 | 1995-03-10 | Mitsubishi Electric Corp | Microcomputer |
| JPH0737087A (en) | 1993-07-19 | 1995-02-07 | Matsushita Electric Ind Co Ltd | Image processing device |
| JPH0779298A (en) | 1993-09-08 | 1995-03-20 | Hitachi Ltd | Facsimile server system |
| US5983012A (en) | 1993-09-28 | 1999-11-09 | Bull Hn Information Systems Inc. | Executing programs of a first system on a second system |
| US5436972A (en) | 1993-10-04 | 1995-07-25 | Fischer; Addison M. | Method for preventing inadvertent betrayal by a trustee of escrowed digital secrets |
| US5513126A (en) | 1993-10-04 | 1996-04-30 | Xerox Corporation | Network having selectively accessible recipient prioritized communication channel profiles |
| US5657461A (en) | 1993-10-04 | 1997-08-12 | Xerox Corporation | User interface for defining and automatically transmitting data according to preferred communication channels |
| US5414833A (en) | 1993-10-27 | 1995-05-09 | International Business Machines Corporation | Network security system and method using a parallel finite state machine adaptive active monitor and responder |
| US5371794A (en) | 1993-11-02 | 1994-12-06 | Sun Microsystems, Inc. | Method and apparatus for privacy and authentication in wireless networks |
| US5499294A (en) | 1993-11-24 | 1996-03-12 | The United States Of America As Represented By The Administrator Of The National Aeronautics And Space Administration | Digital camera with apparatus for authentication of images produced from an image file |
| FR2713419B1 (en) | 1993-12-02 | 1996-07-05 | Gemplus Card Int | Method for generating DSA signatures with low cost portable devices. |
| AU1265195A (en) | 1993-12-06 | 1995-06-27 | Telequip Corporation | Secure computer memory card |
| DE69330065T2 (en) | 1993-12-08 | 2001-08-09 | International Business Machines Corp., Armonk | Method and system for key distribution and authentication in a data transmission system |
| US5509074A (en) | 1994-01-27 | 1996-04-16 | At&T Corp. | Method of protecting electronically published materials using cryptographic protocols |
| US5485455A (en) | 1994-01-28 | 1996-01-16 | Cabletron Systems, Inc. | Network having secure fast packet switching and guaranteed quality of service |
| US6381694B1 (en) | 1994-02-18 | 2002-04-30 | Apple Computer, Inc. | System for automatic recovery from software problems that cause computer failure |
| US5557742A (en) | 1994-03-07 | 1996-09-17 | Haystack Labs, Inc. | Method and system for detecting intrusion into and misuse of a data processing system |
| US5974141A (en) | 1995-03-31 | 1999-10-26 | Mitsubishi Corporation | Data management system |
| US5572590A (en) | 1994-04-12 | 1996-11-05 | International Business Machines Corporation | Discrimination of malicious changes to digital information using multiple signatures |
| US5627977A (en) | 1994-04-19 | 1997-05-06 | Orchid Systems, Inc. | Trainable user interface translator |
| US5541993A (en) | 1994-05-10 | 1996-07-30 | Fan; Eric | Structure and method for secure image transmission |
| US5675507A (en) | 1995-04-28 | 1997-10-07 | Bobo, Ii; Charles R. | Message storage and delivery system |
| US5511122A (en) | 1994-06-03 | 1996-04-23 | The United States Of America As Represented By The Secretary Of The Navy | Intermediate network authentication |
| US5416842A (en) | 1994-06-10 | 1995-05-16 | Sun Microsystems, Inc. | Method and apparatus for key-management scheme for use with internet protocols at site firewalls |
| US5561703A (en) | 1994-07-06 | 1996-10-01 | Rolm Company | System and method for integration of a paging server into a private branch exchange environment |
| US5535276A (en) | 1994-11-09 | 1996-07-09 | Bell Atlantic Network Services, Inc. | Yaksha, an improved system and method for securing communications using split private key asymmetric cryptography |
| US5615340A (en) | 1994-07-21 | 1997-03-25 | Allied Telesyn Int'l Corp. | Network interfacing apparatus and method using repeater and cascade interface with scrambling |
| US5557346A (en) | 1994-08-11 | 1996-09-17 | Trusted Information Systems, Inc. | System and method for key escrow encryption |
| US5557765A (en) | 1994-08-11 | 1996-09-17 | Trusted Information Systems, Inc. | System and method for data recovery |
| US5537533A (en) | 1994-08-11 | 1996-07-16 | Miralink Corporation | System and method for remote mirroring of digital data from a primary network server to a remote network server |
| JPH10511471A (en) | 1994-08-12 | 1998-11-04 | リートン,フランク、タムスン | Fail-safe key marking system |
| US5548646A (en) | 1994-09-15 | 1996-08-20 | Sun Microsystems, Inc. | System for signatureless transmission and reception of data packets between computer networks |
| US5740231A (en) | 1994-09-16 | 1998-04-14 | Octel Communications Corporation | Network-based multimedia communications and directory system and method of operation |
| US5933478A (en) | 1994-09-28 | 1999-08-03 | Hitachi, Ltd. | Data transfer system and handheld terminal device used therefor |
| JPH0897159A (en) | 1994-09-29 | 1996-04-12 | Handotai Process Kenkyusho:Kk | Method and system for epitaxial growth |
| US5802371A (en) | 1994-09-29 | 1998-09-01 | International Business Machines Corporation | Method of walking-up a call stack for a client/server program that uses remote procedure call |
| GB2295299B (en) | 1994-11-16 | 1999-04-28 | Network Services Inc Enterpris | Enterprise network management method and apparatus |
| US5623601A (en) | 1994-11-18 | 1997-04-22 | Milkway Networks Corporation | Apparatus and method for providing a secure gateway for communication and data exchanges between networks |
| US5623598A (en) | 1994-11-22 | 1997-04-22 | Hewlett-Packard Company | Method for identifying ways to improve performance in computer data storage systems |
| US5805719A (en) | 1994-11-28 | 1998-09-08 | Smarttouch | Tokenless identification of individuals |
| US6154879A (en) | 1994-11-28 | 2000-11-28 | Smarttouch, Inc. | Tokenless biometric ATM access system |
| US5758257A (en) | 1994-11-29 | 1998-05-26 | Herz; Frederick | System and method for scheduling broadcast of and access to video programs and other data using customer profiles |
| US5619648A (en) | 1994-11-30 | 1997-04-08 | Lucent Technologies Inc. | Message filtering techniques |
| US5608874A (en) | 1994-12-02 | 1997-03-04 | Autoentry Online, Inc. | System and method for automatic data file format translation and transmission having advanced features |
| US5550984A (en) | 1994-12-07 | 1996-08-27 | Matsushita Electric Corporation Of America | Security system for preventing unauthorized communications between networks by translating communications received in ip protocol to non-ip protocol to remove address and routing services information |
| US5646997A (en) | 1994-12-14 | 1997-07-08 | Barton; James M. | Method and apparatus for embedding authentication information within digital data |
| US5530852A (en) | 1994-12-20 | 1996-06-25 | Sun Microsystems, Inc. | Method for extracting profiles and topics from a first file written in a first markup language and generating files in different markup languages containing the profiles and topics for use in accessing data described by the profiles and topics |
| US5566170A (en) | 1994-12-29 | 1996-10-15 | Storage Technology Corporation | Method and apparatus for accelerated packet forwarding |
| US5694616A (en) | 1994-12-30 | 1997-12-02 | International Business Machines Corporation | Method and system for prioritization of email items by selectively associating priority attribute with at least one and fewer than all of the recipients |
| US5638487A (en) | 1994-12-30 | 1997-06-10 | Purespeech, Inc. | Automatic speech recognition |
| US5878230A (en) | 1995-01-05 | 1999-03-02 | International Business Machines Corporation | System for email messages wherein the sender designates whether the recipient replies or forwards to addresses also designated by the sender |
| US5504454A (en) | 1995-01-30 | 1996-04-02 | Westinghouse Elec. Corp. | Demodulator for powerline carrier communications |
| US5583995A (en) | 1995-01-30 | 1996-12-10 | Mrj, Inc. | Apparatus and method for data storage and retrieval using bandwidth allocation |
| US6658568B1 (en) | 1995-02-13 | 2003-12-02 | Intertrust Technologies Corporation | Trusted infrastructure support system, methods and techniques for secure electronic commerce transaction and rights management |
| US5943422A (en) | 1996-08-12 | 1999-08-24 | Intertrust Technologies Corp. | Steganographic techniques for securely delivering electronic digital rights management control information over insecure communication channels |
| US6272632B1 (en) | 1995-02-21 | 2001-08-07 | Network Associates, Inc. | System and method for controlling access to a user secret using a key recovery field |
| US5835758A (en) | 1995-02-28 | 1998-11-10 | Vidya Technologies, Inc. | Method and system for respresenting and processing physical and conceptual entities |
| US5655081A (en) | 1995-03-08 | 1997-08-05 | Bmc Software, Inc. | System for monitoring and managing computer resources and applications across a distributed computing environment using an intelligent autonomous agent architecture |
| US5564106A (en) | 1995-03-09 | 1996-10-08 | Motorola, Inc. | Method for providing blind access to an encryption key |
| US5553145A (en) | 1995-03-21 | 1996-09-03 | Micali; Silvia | Simultaneous electronic transactions with visible trusted parties |
| US5699513A (en) | 1995-03-31 | 1997-12-16 | Motorola, Inc. | Method for secure network access via message intercept |
| US5790793A (en) | 1995-04-04 | 1998-08-04 | Higley; Thomas | Method and system to create, transmit, receive and process information, including an address to further information |
| US5677955A (en) | 1995-04-07 | 1997-10-14 | Financial Services Technology Consortium | Electronic funds transfer instruments |
| US5852665A (en) | 1995-04-13 | 1998-12-22 | Fortress U & T Ltd. | Internationally regulated system for one to one cryptographic communications with national sovereignty without key escrow |
| US5724512A (en) | 1995-04-17 | 1998-03-03 | Lucent Technologies Inc. | Methods and apparatus for storage and retrieval of name space information in a distributed computing system |
| DE69628882T2 (en) | 1995-04-25 | 2004-05-27 | Canon K.K. | Data transmission device and method |
| US5790856A (en) | 1995-05-08 | 1998-08-04 | Apple Computer, Inc. | Methods, apparatus, and data structures for data driven computer patches and static analysis of same |
| US5632011A (en) | 1995-05-22 | 1997-05-20 | Sterling Commerce, Inc. | Electronic mail management system for operation on a host computer system |
| KR19990022451A (en) | 1995-06-05 | 1999-03-25 | 피터 씨. 프레운드 | Multilevel digital signature method and system |
| US5812776A (en) | 1995-06-07 | 1998-09-22 | Open Market, Inc. | Method of providing internet pages by mapping telephone number provided by client to URL and returning the same in a redirect command by server |
| US5636371A (en) | 1995-06-07 | 1997-06-03 | Bull Hn Information Systems Inc. | Virtual network mechanism to access well known port application programs running on a single host system |
| US5689565A (en) | 1995-06-29 | 1997-11-18 | Microsoft Corporation | Cryptography system and method for providing cryptographic services for a computer application |
| US5761531A (en) | 1995-06-30 | 1998-06-02 | Fujitsu Limited | Input/output control apparatus and method for transfering track data from cache module to channel unit during the staging of the data track from device adapter |
| GB2303947A (en) | 1995-07-31 | 1997-03-05 | Ibm | Boot sector virus protection in computer systems |
| JPH0954699A (en) | 1995-08-11 | 1997-02-25 | Fujitsu Ltd | Computer process scheduler |
| US5742759A (en) | 1995-08-18 | 1998-04-21 | Sun Microsystems, Inc. | Method and system for facilitating access control to system resources in a distributed computer system |
| EP0762337A3 (en) | 1995-09-08 | 2000-01-19 | Francotyp-Postalia Aktiengesellschaft & Co. | Method and device for enhancing manipulation-proof of critical data |
| US5631961A (en) | 1995-09-15 | 1997-05-20 | The United States Of America As Represented By The Director Of The National Security Agency | Device for and method of cryptography that allows third party access |
| US6134551A (en) | 1995-09-15 | 2000-10-17 | Intel Corporation | Method of caching digital certificate revocation lists |
| US5889943A (en) | 1995-09-26 | 1999-03-30 | Trend Micro Incorporated | Apparatus and method for electronic mail virus detection and elimination |
| US5623600A (en) | 1995-09-26 | 1997-04-22 | Trend Micro, Incorporated | Virus detection and removal apparatus for computer networks |
| US5854916A (en) | 1995-09-28 | 1998-12-29 | Symantec Corporation | State-based cache for antivirus software |
| US5765030A (en) | 1996-07-19 | 1998-06-09 | Symantec Corp | Processor emulator module having a variable pre-fetch queue size for program execution |
| US5826013A (en) | 1995-09-28 | 1998-10-20 | Symantec Corporation | Polymorphic virus detection module |
| US6067410A (en) | 1996-02-09 | 2000-05-23 | Symantec Corporation | Emulation repair system |
| US5696822A (en) | 1995-09-28 | 1997-12-09 | Symantec Corporation | Polymorphic virus detection module |
| US6766450B2 (en) | 1995-10-24 | 2004-07-20 | Corestreet, Ltd. | Certificate revocation system |
| US6487658B1 (en) | 1995-10-02 | 2002-11-26 | Corestreet Security, Ltd. | Efficient certificate revocation |
| US5793868A (en) | 1996-08-29 | 1998-08-11 | Micali; Silvio | Certificate revocation system |
| US5666416A (en) | 1995-10-24 | 1997-09-09 | Micali; Silvio | Certificate revocation system |
| US6097811A (en) | 1995-11-02 | 2000-08-01 | Micali; Silvio | Tree-based certificate revocation system |
| US5572643A (en) | 1995-10-19 | 1996-11-05 | Judson; David H. | Web browser with dynamic display of information objects during linking |
| US5689566A (en) | 1995-10-24 | 1997-11-18 | Nguyen; Minhtam C. | Network with secure communications sessions |
| US5687235A (en) | 1995-10-26 | 1997-11-11 | Novell, Inc. | Certificate revocation performance optimization |
| US5948062A (en) | 1995-10-27 | 1999-09-07 | Emc Corporation | Network file server using a cached disk array storing a network file directory including file locking information and data mover computers each having file system software for shared read-write file access |
| US5826029A (en) | 1995-10-31 | 1998-10-20 | International Business Machines Corporation | Secured gateway interface |
| US5724428A (en) | 1995-11-01 | 1998-03-03 | Rsa Data Security, Inc. | Block encryption algorithm with data-dependent rotations |
| US5793763A (en) | 1995-11-03 | 1998-08-11 | Cisco Technology, Inc. | Security system for network address translation systems |
| US5923846A (en) | 1995-11-06 | 1999-07-13 | Microsoft Corporation | Method of uploading a message containing a file reference to a server and downloading a file from the server using the file reference |
| US5764906A (en) | 1995-11-07 | 1998-06-09 | Netword Llc | Universal electronic resource denotation, request and delivery system |
| US5699431A (en) | 1995-11-13 | 1997-12-16 | Northern Telecom Limited | Method for efficient management of certificate revocation lists and update information |
| US5671279A (en) | 1995-11-13 | 1997-09-23 | Netscape Communications Corporation | Electronic commerce using a secure courier system |
| JPH09153050A (en) | 1995-11-29 | 1997-06-10 | Hitachi Ltd | Document information collecting method and document information collecting device |
| JP3688830B2 (en) | 1995-11-30 | 2005-08-31 | 株式会社東芝 | Packet transfer method and packet processing apparatus |
| US5812844A (en) | 1995-12-07 | 1998-09-22 | Microsoft Corporation | Method and system for scheduling the execution of threads using optional time-specific scheduling constraints |
| US5937164A (en) | 1995-12-07 | 1999-08-10 | Hyperlock Technologies, Inc. | Method and apparatus of secure server control of local media via a trigger through a network for instant local access of encrypted data on local media within a platform independent networking system |
| US5892825A (en) | 1996-05-15 | 1999-04-06 | Hyperlock Technologies Inc | Method of secure server control of local media via a trigger through a network for instant local access of encrypted data on local media |
| US5758343A (en) | 1995-12-08 | 1998-05-26 | Ncr Corporation | Apparatus and method for integrating multiple delegate directory service agents |
| US5745574A (en) | 1995-12-15 | 1998-04-28 | Entegrity Solutions Corporation | Security infrastructure for electronic transactions |
| US5793954A (en) | 1995-12-20 | 1998-08-11 | Nb Networks | System and method for general purpose network analysis |
| US5781901A (en) | 1995-12-21 | 1998-07-14 | Intel Corporation | Transmitting electronic mail attachment over a network using a e-mail page |
| US5903723A (en) | 1995-12-21 | 1999-05-11 | Intel Corporation | Method and apparatus for transmitting electronic mail attachments with attachment references |
| JP2000503154A (en) | 1996-01-11 | 2000-03-14 | エムアールジェイ インコーポレイテッド | System for controlling access and distribution of digital ownership |
| US5801700A (en) | 1996-01-19 | 1998-09-01 | Silicon Graphics Incorporated | System and method for an iconic drag and drop interface for electronic file transfer |
| US5898830A (en) | 1996-10-17 | 1999-04-27 | Network Engineering Software | Firewall providing enhanced network security and user transparency |
| US5826014A (en) | 1996-02-06 | 1998-10-20 | Network Engineering Software | Firewall system for protecting network elements connected to a public network |
| JP3165366B2 (en) | 1996-02-08 | 2001-05-14 | 株式会社日立製作所 | Network security system |
| US6587949B1 (en) | 1998-06-26 | 2003-07-01 | Fotonation Holdings, Llc | Secure storage device for transfer of data via removable storage |
| US5855020A (en) | 1996-02-21 | 1998-12-29 | Infoseek Corporation | Web scan process |
| US5963915A (en) | 1996-02-21 | 1999-10-05 | Infoseek Corporation | Secure, convenient and efficient system and method of performing trans-internet purchase transactions |
| US5751956A (en) | 1996-02-21 | 1998-05-12 | Infoseek Corporation | Method and apparatus for redirection of server external hyper-link references |
| US5790664A (en) | 1996-02-26 | 1998-08-04 | Network Engineering Software, Inc. | Automated system for management of licensed software |
| US20010011253A1 (en) | 1998-08-04 | 2001-08-02 | Christopher D. Coley | Automated system for management of licensed software |
| US6075863A (en) | 1996-02-28 | 2000-06-13 | Encanto Networks | Intelligent communication device |
| US5768388A (en) | 1996-03-01 | 1998-06-16 | Goldwasser; Shafi | Time delayed key escrow |
| US5684951A (en) | 1996-03-20 | 1997-11-04 | Synopsys, Inc. | Method and system for user authorization over a multi-user computer system |
| US5673322A (en) | 1996-03-22 | 1997-09-30 | Bell Communications Research, Inc. | System and method for providing protocol translation and filtering to access the world wide web from wireless or low-bandwidth networks |
| US5850442A (en) | 1996-03-26 | 1998-12-15 | Entegrity Solutions Corporation | Secure world wide electronic commerce over an open network |
| US5826022A (en) | 1996-04-05 | 1998-10-20 | Sun Microsystems, Inc. | Method and apparatus for receiving electronic mail |
| US5815573A (en) | 1996-04-10 | 1998-09-29 | International Business Machines Corporation | Cryptographic key recovery system |
| US5727156A (en) | 1996-04-10 | 1998-03-10 | Hotoffice Technologies, Inc. | Internet-based automatic publishing system |
| US5845084A (en) | 1996-04-18 | 1998-12-01 | Microsoft Corporation | Automatic data display formatting with a networking application |
| US5778372A (en) | 1996-04-18 | 1998-07-07 | Microsoft Corporation | Remote retrieval and display management of electronic document with incorporated images |
| US5815657A (en) | 1996-04-26 | 1998-09-29 | Verifone, Inc. | System, method and article of manufacture for network electronic authorization utilizing an authorization instrument |
| US5842216A (en) | 1996-05-03 | 1998-11-24 | Mitsubishi Electric Information Technology Center America, Inc. | System for sending small positive data notification messages over a network to indicate that a recipient node should obtain a particular version of a particular data item |
| US5793972A (en) | 1996-05-03 | 1998-08-11 | Westminster International Computers Inc. | System and method providing an interactive response to direct mail by creating personalized web page based on URL provided on mail piece |
| US5742769A (en) | 1996-05-06 | 1998-04-21 | Banyan Systems, Inc. | Directory with options for access to and display of email addresses |
| US5903651A (en) | 1996-05-14 | 1999-05-11 | Valicert, Inc. | Apparatus and method for demonstrating and confirming the status of a digital certificates and other data |
| US5884033A (en) | 1996-05-15 | 1999-03-16 | Spyglass, Inc. | Internet filtering system for filtering data transferred over the internet utilizing immediate and deferred filtering actions |
| US6085320A (en) | 1996-05-15 | 2000-07-04 | Rsa Security Inc. | Client/server protocol for proving authenticity |
| US5768528A (en) | 1996-05-24 | 1998-06-16 | V-Cast, Inc. | Client-server system for delivery of online information |
| US6092067A (en) | 1996-05-30 | 2000-07-18 | Microsoft Corporation | Desktop information manager for recording and viewing important events data structure |
| US5918013A (en) | 1996-06-03 | 1999-06-29 | Webtv Networks, Inc. | Method of transcoding documents in a network environment using a proxy server |
| US5822526A (en) | 1996-06-03 | 1998-10-13 | Microsoft Corporation | System and method for maintaining and administering email address names in a network |
| US6151643A (en) | 1996-06-07 | 2000-11-21 | Networks Associates, Inc. | Automatic updating of diverse software products on multiple client computer systems by downloading scanning application to client computer and generating software list on client computer |
| CA2257309C (en) | 1996-06-07 | 2002-06-11 | At&T Corp. | Internet file system |
| US5812398A (en) | 1996-06-10 | 1998-09-22 | Sun Microsystems, Inc. | Method and system for escrowed backup of hotelled world wide web sites |
| US6108688A (en) | 1996-06-12 | 2000-08-22 | Sun Microsystems, Inc. | System for reminding a sender of an email if recipient of the email does not respond by a selected time set by the sender |
| US6373950B1 (en) | 1996-06-17 | 2002-04-16 | Hewlett-Packard Company | System, method and article of manufacture for transmitting messages within messages utilizing an extensible, flexible architecture |
| US5798706A (en) | 1996-06-18 | 1998-08-25 | Raptor Systems, Inc. | Detecting unauthorized network communication |
| US5901227A (en) | 1996-06-20 | 1999-05-04 | Novell, Inc. | Method and apparatus for implementing partial and complete optional key escrow |
| US5991807A (en) | 1996-06-24 | 1999-11-23 | Nortel Networks Corporation | System for controlling users access to a distributive network in accordance with constraints present in common access distributive network interface separate from a server |
| US5781857A (en) | 1996-06-28 | 1998-07-14 | Motorola, Inc. | Method of establishing an email monitor responsive to a wireless communications system user |
| JP3531367B2 (en) | 1996-07-04 | 2004-05-31 | 株式会社日立製作所 | Translator |
| US5796830A (en) | 1996-07-29 | 1998-08-18 | International Business Machines Corporation | Interoperable cryptographic key recovery system |
| US5828832A (en) | 1996-07-30 | 1998-10-27 | Itt Industries, Inc. | Mixed enclave operation in a computer network with multi-level network security |
| US5802178A (en) | 1996-07-30 | 1998-09-01 | Itt Industries, Inc. | Stand alone device for providing security within computer networks |
| US5790789A (en) | 1996-08-02 | 1998-08-04 | Suarez; Larry | Method and architecture for the creation, control and deployment of services within a distributed computer environment |
| US5711348A (en)* | 1996-08-14 | 1998-01-27 | Moog Inc. | Hot gas control valve |
| US5907620A (en) | 1996-08-23 | 1999-05-25 | Cheyenne Property Trust | Method and apparatus for enforcing the use of cryptography in an international cryptography framework |
| US5799083A (en) | 1996-08-26 | 1998-08-25 | Brothers; Harlan Jay | Event verification system |
| US5832208A (en) | 1996-09-05 | 1998-11-03 | Cheyenne Software International Sales Corp. | Anti-virus agent for use with databases and mail servers |
| US5892903A (en) | 1996-09-12 | 1999-04-06 | Internet Security Systems, Inc. | Method and apparatus for detecting and identifying security vulnerabilities in an open network computer communication system |
| US5950195A (en) | 1996-09-18 | 1999-09-07 | Secure Computing Corporation | Generalized security policy management system and method |
| US6072942A (en) | 1996-09-18 | 2000-06-06 | Secure Computing Corporation | System and method of electronic mail filtering using interconnected nodes |
| US5951698A (en) | 1996-10-02 | 1999-09-14 | Trend Micro, Incorporated | System, apparatus and method for the detection and removal of viruses in macros |
| US5937066A (en) | 1996-10-02 | 1999-08-10 | International Business Machines Corporation | Two-phase cryptographic key recovery system |
| JPH10111727A (en) | 1996-10-03 | 1998-04-28 | Toshiba Corp | Information equipment having telephone function and method for realizing security of the information equipment |
| US6119236A (en) | 1996-10-07 | 2000-09-12 | Shipley; Peter M. | Intelligent network security device and method |
| US5835090A (en) | 1996-10-16 | 1998-11-10 | Etma, Inc. | Desktop manager for graphical user interface based system with enhanced desktop |
| US5930479A (en) | 1996-10-21 | 1999-07-27 | At&T Corp | Communications addressing system |
| US6502191B1 (en) | 1997-02-14 | 2002-12-31 | Tumbleweed Communications Corp. | Method and system for binary data firewall delivery |
| US6385655B1 (en) | 1996-10-24 | 2002-05-07 | Tumbleweed Communications Corp. | Method and apparatus for delivering documents over an electronic network |
| US6119137A (en) | 1997-01-30 | 2000-09-12 | Tumbleweed Communications Corp. | Distributed dynamic document conversion server |
| US5790790A (en) | 1996-10-24 | 1998-08-04 | Tumbleweed Software Corporation | Electronic document delivery system in which notification of said electronic document is sent to a recipient thereof |
| AU5094398A (en) | 1996-10-30 | 1998-05-22 | Theodor Holm Nelson | Many-to-many payment system for network content materials |
| US5923885A (en) | 1996-10-31 | 1999-07-13 | Sun Microsystems, Inc. | Acquisition and operation of remotely loaded software using applet modification of browser software |
| US6453345B2 (en) | 1996-11-06 | 2002-09-17 | Datadirect Networks, Inc. | Network security and surveillance system |
| US5991881A (en) | 1996-11-08 | 1999-11-23 | Harris Corporation | Network surveillance system |
| US6167520A (en) | 1996-11-08 | 2000-12-26 | Finjan Software, Inc. | System and method for protecting a client during runtime from hostile downloadables |
| US6154844A (en) | 1996-11-08 | 2000-11-28 | Finjan Software, Ltd. | System and method for attaching a downloadable security profile to a downloadable |
| US5796948A (en) | 1996-11-12 | 1998-08-18 | Cohen; Elliot D. | Offensive message interceptor for computers |
| US5796942A (en) | 1996-11-21 | 1998-08-18 | Computer Associates International, Inc. | Method and apparatus for automated network-wide surveillance and security breach intervention |
| JPH10164124A (en) | 1996-12-04 | 1998-06-19 | Canon Inc | Communication device |
| US6367012B1 (en) | 1996-12-06 | 2002-04-02 | Microsoft Corporation | Embedding certifications in executable files for network transmission |
| US5892904A (en) | 1996-12-06 | 1999-04-06 | Microsoft Corporation | Code certification for network transmission |
| US5968119A (en) | 1996-12-09 | 1999-10-19 | Wall Data Incorporated | Method of accessing information of an SNA host computer from a client computer using a specific terminal emulation |
| US5959976A (en) | 1996-12-09 | 1999-09-28 | Kuo; Yung-Tien | Method and device for filtering transmission |
| US6285991B1 (en) | 1996-12-13 | 2001-09-04 | Visa International Service Association | Secure interactive electronic account statement delivery system |
| US6009274A (en) | 1996-12-13 | 1999-12-28 | 3Com Corporation | Method and apparatus for automatically updating software components on end systems over a network |
| US5903882A (en) | 1996-12-13 | 1999-05-11 | Certco, Llc | Reliance server for electronic transaction system |
| JP2000507791A (en) | 1996-12-16 | 2000-06-20 | サムスン エレクトロニクス カンパニー リミテッド | Method and apparatus for transmitting an e-mail message in a local network |
| US5911776A (en) | 1996-12-18 | 1999-06-15 | Unisys Corporation | Automatic format conversion system and publishing methodology for multi-user network |
| US6061722A (en) | 1996-12-23 | 2000-05-09 | T E Network, Inc. | Assessing network performance without interference with normal network operations |
| US5951644A (en) | 1996-12-24 | 1999-09-14 | Apple Computer, Inc. | System for predicting and managing network performance by managing and monitoring resourse utilization and connection of network |
| US5907618A (en) | 1997-01-03 | 1999-05-25 | International Business Machines Corporation | Method and apparatus for verifiably providing key recovery information in a cryptographic system |
| US5805801A (en) | 1997-01-09 | 1998-09-08 | International Business Machines Corporation | System and method for detecting and preventing security |
| US5905859A (en) | 1997-01-09 | 1999-05-18 | International Business Machines Corporation | Managed network device security method and apparatus |
| US5898836A (en) | 1997-01-14 | 1999-04-27 | Netmind Services, Inc. | Change-detection tool indicating degree and location of change of internet documents by comparison of cyclic-redundancy-check(CRC) signatures |
| US5933647A (en) | 1997-01-24 | 1999-08-03 | Cognet Corporation | System and method for software distribution and desktop management in a computer network environment |
| US5978799A (en) | 1997-01-30 | 1999-11-02 | Hirsch; G. Scott | Search engine including query database, user profile database, information templates and email facility |
| US5956481A (en) | 1997-02-06 | 1999-09-21 | Microsoft Corporation | Method and apparatus for protecting data files on a computer from virus infection |
| US5953502A (en) | 1997-02-13 | 1999-09-14 | Helbig, Sr.; Walter A | Method and apparatus for enhancing computer system security |
| JPH10232875A (en) | 1997-02-19 | 1998-09-02 | Hitachi Ltd | Database management method and parallel database management system |
| US5896499A (en) | 1997-02-21 | 1999-04-20 | International Business Machines Corporation | Embedded security processor |
| US5920630A (en) | 1997-02-25 | 1999-07-06 | United States Of America | Method of public key cryptography that includes key escrow |
| US5922074A (en) | 1997-02-28 | 1999-07-13 | Xcert Software, Inc. | Method of and apparatus for providing secure distributed directory services and public key infrastructure |
| US6408336B1 (en) | 1997-03-10 | 2002-06-18 | David S. Schneider | Distributed administration of access to information |
| GB2324892B (en) | 1997-03-14 | 1999-12-01 | Interactuality Limited | Process monitoring system |
| US5960170A (en) | 1997-03-18 | 1999-09-28 | Trend Micro, Inc. | Event triggered iterative virus detection |
| US5987606A (en) | 1997-03-19 | 1999-11-16 | Bascom Global Internet Services, Inc. | Method and system for content filtering information retrieved from an internet computer network |
| US5958010A (en) | 1997-03-20 | 1999-09-28 | Firstsense Software, Inc. | Systems and methods for monitoring distributed applications including an interface running in an operating system kernel |
| US5996011A (en) | 1997-03-25 | 1999-11-30 | Unified Research Laboratories, Inc. | System and method for filtering data received by a computer system |
| US6539430B1 (en) | 1997-03-25 | 2003-03-25 | Symantec Corporation | System and method for filtering data received by a computer system |
| US6304904B1 (en) | 1997-03-27 | 2001-10-16 | Intel Corporation | Method and apparatus for collecting page-level performance statistics from a network device |
| EP1021917A4 (en) | 1997-03-31 | 2002-05-15 | Broadband Associates | Method and system for providing a presentation on a network |
| US6061448A (en) | 1997-04-01 | 2000-05-09 | Tumbleweed Communications Corp. | Method and system for dynamic server document encryption |
| US6249585B1 (en) | 1998-04-08 | 2001-06-19 | Network Associates, Inc | Publicly verifiable key recovery |
| US5964889A (en) | 1997-04-16 | 1999-10-12 | Symantec Corporation | Method to analyze a program for presence of computer viruses by examining the opcode for faults before emulating instruction in emulator |
| US6243815B1 (en) | 1997-04-25 | 2001-06-05 | Anand K. Antur | Method and apparatus for reconfiguring and managing firewalls and security devices |
| US6108786A (en) | 1997-04-25 | 2000-08-22 | Intel Corporation | Monitor network bindings for computer security |
| US6123737A (en) | 1997-05-21 | 2000-09-26 | Symantec Corporation | Push deployment of software packages using notification transports |
| US6167438A (en) | 1997-05-22 | 2000-12-26 | Trustees Of Boston University | Method and system for distributed caching, prefetching and replication |
| US5948104A (en) | 1997-05-23 | 1999-09-07 | Neuromedical Systems, Inc. | System and method for automated anti-viral file update |
| US6314190B1 (en) | 1997-06-06 | 2001-11-06 | Networks Associates Technology, Inc. | Cryptographic system with methods for user-controlled message recovery |
| US6070243A (en) | 1997-06-13 | 2000-05-30 | Xylan Corporation | Deterministic user authentication service for communication network |
| US5996077A (en) | 1997-06-16 | 1999-11-30 | Cylink Corporation | Access control system and method using hierarchical arrangement of security devices |
| US6009462A (en) | 1997-06-16 | 1999-12-28 | Digital Equipment Corporation | Replacing large bit component of electronic mail (e-mail) message with hot-link in distributed computer system |
| US6449640B1 (en) | 1997-06-19 | 2002-09-10 | International Business Machines Corporation | Web server with unique identification of linked objects |
| US6226666B1 (en) | 1997-06-27 | 2001-05-01 | International Business Machines Corporation | Agent-based management system having an open layered architecture for synchronous and/or asynchronous messaging handling |
| US6144744A (en) | 1997-06-30 | 2000-11-07 | International Business Machines Corporation | Method and apparatus for the secure transfer of objects between cryptographic processors |
| US6453352B1 (en) | 1997-07-14 | 2002-09-17 | Electronic Data Systems Corporation | Integrated electronic commerce system and method |
| US6230194B1 (en) | 1997-07-14 | 2001-05-08 | Freegate Corporation | Upgrading a secure network interface |
| US5958005A (en) | 1997-07-17 | 1999-09-28 | Bell Atlantic Network Services, Inc. | Electronic mail security |
| US7127741B2 (en) | 1998-11-03 | 2006-10-24 | Tumbleweed Communications Corp. | Method and system for e-mail message transmission |
| US7117358B2 (en)* | 1997-07-24 | 2006-10-03 | Tumbleweed Communications Corp. | Method and system for filtering communication |
| DE69841210D1 (en) | 1997-07-24 | 2009-11-12 | Axway Inc | Email Firewall |
| US20050081059A1 (en)* | 1997-07-24 | 2005-04-14 | Bandini Jean-Christophe Denis | Method and system for e-mail filtering |
| US7162738B2 (en) | 1998-11-03 | 2007-01-09 | Tumbleweed Communications Corp. | E-mail firewall with stored key encryption/decryption |
| US5941998A (en) | 1997-07-25 | 1999-08-24 | Samsung Electronics Co., Ltd. | Disk drive incorporating read-verify after write method |
| US6073140A (en) | 1997-07-29 | 2000-06-06 | Acxiom Corporation | Method and system for the creation, enhancement and update of remote data using persistent keys |
| US5946679A (en) | 1997-07-31 | 1999-08-31 | Torrent Networking Technologies, Corp. | System and method for locating a route in a route table using hashing and compressed radix tree searching |
| US5919257A (en) | 1997-08-08 | 1999-07-06 | Novell, Inc. | Networked workstation intrusion detection system |
| US6006329A (en) | 1997-08-11 | 1999-12-21 | Symantec Corporation | Detection of computer viruses spanning multiple data streams |
| US5999967A (en)* | 1997-08-17 | 1999-12-07 | Sundsted; Todd | Electronic mail filtering by electronic stamp |
| US6199102B1 (en) | 1997-08-26 | 2001-03-06 | Christopher Alan Cobb | Method and system for filtering electronic messages |
| US6442688B1 (en) | 1997-08-29 | 2002-08-27 | Entrust Technologies Limited | Method and apparatus for obtaining status of public key certificate updates |
| US6357008B1 (en) | 1997-09-23 | 2002-03-12 | Symantec Corporation | Dynamic heuristic method for detecting computer viruses using decryption exploration and evaluation phases |
| US6385644B1 (en) | 1997-09-26 | 2002-05-07 | Mci Worldcom, Inc. | Multi-threaded web based user inbox for report management |
| US6119230A (en) | 1997-10-01 | 2000-09-12 | Novell, Inc. | Distributed dynamic security capabilities |
| US6055519A (en) | 1997-10-11 | 2000-04-25 | I2 Technologies, Inc. | Framework for negotiation and tracking of sale of goods |
| US5991879A (en) | 1997-10-23 | 1999-11-23 | Bull Hn Information Systems Inc. | Method for gradual deployment of user-access security within a data processing system |
| US6393568B1 (en) | 1997-10-23 | 2002-05-21 | Entrust Technologies Limited | Encryption and decryption system and method with content analysis provision |
| US6496979B1 (en) | 1997-10-24 | 2002-12-17 | Microsoft Corporation | System and method for managing application installation for a mobile device |
| US6092102A (en) | 1997-10-24 | 2000-07-18 | University Of Pittsburgh Of The Commonwealth System Of Higher Education | System and method for notifying users about information or events of an enterprise |
| US6092201A (en) | 1997-10-24 | 2000-07-18 | Entrust Technologies | Method and apparatus for extending secure communication operations via a shared list |
| US6215763B1 (en) | 1997-10-29 | 2001-04-10 | Lucent Technologies Inc. | Multi-phase process for distributed precomputation of network signal paths |
| US6223172B1 (en) | 1997-10-31 | 2001-04-24 | Nortel Networks Limited | Address routing using address-sensitive mask decimation scheme |
| US6119231A (en) | 1997-10-31 | 2000-09-12 | Cisco Technologies, Inc. | Data scanning network security technique |
| US6275937B1 (en) | 1997-11-06 | 2001-08-14 | International Business Machines Corporation | Collaborative server processing of content and meta-information with application to virus checking in a server network |
| US6112181A (en) | 1997-11-06 | 2000-08-29 | Intertrust Technologies Corporation | Systems and methods for matching, selecting, narrowcasting, and/or classifying based on rights management and/or other information |
| US6362836B1 (en) | 1998-04-06 | 2002-03-26 | The Santa Cruz Operation, Inc. | Universal application server for providing applications on a variety of client devices in a client/server network |
| US6119165A (en) | 1997-11-17 | 2000-09-12 | Trend Micro, Inc. | Controlled distribution of application programs in a computer network |
| US6003027A (en) | 1997-11-21 | 1999-12-14 | International Business Machines Corporation | System and method for determining confidence levels for the results of a categorization system |
| US6094731A (en) | 1997-11-24 | 2000-07-25 | Symantec Corporation | Antivirus accelerator for computer networks |
| US6393465B2 (en)* | 1997-11-25 | 2002-05-21 | Nixmail Corporation | Junk electronic mail detector and eliminator |
| JPH11175329A (en) | 1997-12-08 | 1999-07-02 | Hitachi Ltd | Application cooperation method and device |
| US6202157B1 (en) | 1997-12-08 | 2001-03-13 | Entrust Technologies Limited | Computer network security system and method having unilateral enforceable security policy provision |
| US7055173B1 (en) | 1997-12-19 | 2006-05-30 | Avaya Technology Corp. | Firewall pooling in a network flowswitch |
| US6009103A (en) | 1997-12-23 | 1999-12-28 | Mediaone Group, Inc. | Method and system for automatic allocation of resources in a network |
| US6052709A (en)* | 1997-12-23 | 2000-04-18 | Bright Light Technologies, Inc. | Apparatus and method for controlling delivery of unsolicited electronic mail |
| US6694023B1 (en) | 1997-12-29 | 2004-02-17 | Samsung Electronics Co., Ltd. | Method and apparatus for protecting copyright of digital recording medium and copyright protected digital recording medium |
| US6088803A (en) | 1997-12-30 | 2000-07-11 | Intel Corporation | System for virus-checking network data during download to a client device |
| US6035423A (en) | 1997-12-31 | 2000-03-07 | Network Associates, Inc. | Method and system for providing automated updating and upgrading of antivirus applications using a computer network |
| US6279133B1 (en) | 1997-12-31 | 2001-08-21 | Kawasaki Steel Corporation | Method and apparatus for significantly improving the reliability of multilevel memory architecture |
| US6088804A (en) | 1998-01-12 | 2000-07-11 | Motorola, Inc. | Adaptive system and method for responding to computer network security attacks |
| US5999932A (en) | 1998-01-13 | 1999-12-07 | Bright Light Technologies, Inc. | System and method for filtering unsolicited electronic mail messages using data matching and heuristic processing |
| US6138254A (en) | 1998-01-22 | 2000-10-24 | Micron Technology, Inc. | Method and apparatus for redundant location addressing using data compression |
| CA2228687A1 (en) | 1998-02-04 | 1999-08-04 | Brett Howard | Secured virtual private networks |
| US6385596B1 (en) | 1998-02-06 | 2002-05-07 | Liquid Audio, Inc. | Secure online music distribution system |
| US5987610A (en) | 1998-02-12 | 1999-11-16 | Ameritech Corporation | Computer virus screening methods and systems |
| US6233577B1 (en) | 1998-02-17 | 2001-05-15 | Phone.Com, Inc. | Centralized certificate management system for two-way interactive communication devices in data networks |
| ATE484054T1 (en) | 1998-02-27 | 2010-10-15 | Doug Carson & Associates Inc | INDIVIDUAL SETTING OF PIT AND LAND CROSSING POINTS IN AN OPTICAL DRIVE MASTER PROCESS |
| US6279113B1 (en) | 1998-03-16 | 2001-08-21 | Internet Tools, Inc. | Dynamic signature inspection-based network intrusion detection |
| US6134550A (en) | 1998-03-18 | 2000-10-17 | Entrust Technologies Limited | Method and apparatus for use in determining validity of a certificate in a communication system employing trusted paths |
| US6738814B1 (en) | 1998-03-18 | 2004-05-18 | Cisco Technology, Inc. | Method for blocking denial of service and address spoofing attacks on a private network |
| US6453419B1 (en) | 1998-03-18 | 2002-09-17 | Secure Computing Corporation | System and method for implementing a security policy |
| US6052531A (en) | 1998-03-25 | 2000-04-18 | Symantec Corporation | Multi-tiered incremental software updating |
| US6154769A (en) | 1998-03-27 | 2000-11-28 | Hewlett-Packard Company | Scheduling server requests to decrease response time and increase server throughput |
| US6430184B1 (en) | 1998-04-10 | 2002-08-06 | Top Layer Networks, Inc. | System and process for GHIH-speed pattern matching for application-level switching of data packets |
| US6092114A (en) | 1998-04-17 | 2000-07-18 | Siemens Information And Communication Networks, Inc. | Method and system for determining the location for performing file-format conversions of electronics message attachments |
| US6145083A (en) | 1998-04-23 | 2000-11-07 | Siemens Information And Communication Networks, Inc. | Methods and system for providing data and telephony security |
| US6529498B1 (en) | 1998-04-28 | 2003-03-04 | Cisco Technology, Inc. | Routing support for point-to-multipoint connections |
| US6104500A (en) | 1998-04-29 | 2000-08-15 | Bcl, Computer Inc. | Networked fax routing via email |
| US6298445B1 (en) | 1998-04-30 | 2001-10-02 | Netect, Ltd. | Computer security |
| US6119157A (en) | 1998-05-14 | 2000-09-12 | Sun Microsystems, Inc. | Protocol for exchanging configuration data in a computer network |
| JP3017712B2 (en) | 1998-05-15 | 2000-03-13 | 松下電送システム株式会社 | Internet facsimile |
| US6275942B1 (en) | 1998-05-20 | 2001-08-14 | Network Associates, Inc. | System, method and computer program product for automatic response to computer system misuse using active response modules |
| US6058482A (en) | 1998-05-22 | 2000-05-02 | Sun Microsystems, Inc. | Apparatus, method and system for providing network security for executable code in computer and communications networks |
| US6330589B1 (en) | 1998-05-26 | 2001-12-11 | Microsoft Corporation | System and method for using a client database to manage conversation threads generated from email or news messages |
| GB2337903B (en) | 1998-05-28 | 2000-06-07 | 3Com Corp | Methods and apparatus for collecting storing processing and using network traffic data |
| CA2239060A1 (en) | 1998-05-28 | 1999-11-28 | Newbridge Networks Corporation | Rate monitoring of connections in a communications network using history buffer |
| US6397259B1 (en) | 1998-05-29 | 2002-05-28 | Palm, Inc. | Method, system and apparatus for packet minimized communications |
| US6289214B1 (en) | 1998-05-29 | 2001-09-11 | Ericsson Inc. | Systems and methods for deactivating a cellular radiotelephone system using an ANSI-41 short message service email |
| US6167407A (en) | 1998-06-03 | 2000-12-26 | Symantec Corporation | Backtracked incremental updating |
| US6347374B1 (en) | 1998-06-05 | 2002-02-12 | Intrusion.Com, Inc. | Event detection |
| US6240401B1 (en) | 1998-06-05 | 2001-05-29 | Digital Video Express, L.P. | System and method for movie transaction processing |
| US6216175B1 (en) | 1998-06-08 | 2001-04-10 | Microsoft Corporation | Method for upgrading copies of an original file with same update data after normalizing differences between copies created during respective original installations |
| US6317829B1 (en) | 1998-06-19 | 2001-11-13 | Entrust Technologies Limited | Public key cryptography based security system to facilitate secure roaming of users |
| US6161130A (en) | 1998-06-23 | 2000-12-12 | Microsoft Corporation | Technique which utilizes a probabilistic classifier to detect "junk" e-mail by automatically updating a training and re-training the classifier based on the updated training set |
| US6266337B1 (en) | 1998-06-23 | 2001-07-24 | Expand Network Ltd. | Packet retransmission eliminator |
| US6049789A (en) | 1998-06-24 | 2000-04-11 | Mentor Graphics Corporation | Software pay per use licensing system |
| US6446109B2 (en) | 1998-06-29 | 2002-09-03 | Sun Microsystems, Inc. | Application computing environment |
| US6141778A (en) | 1998-06-29 | 2000-10-31 | Mci Communications Corporation | Method and apparatus for automating security functions in a computer system |
| US6324656B1 (en) | 1998-06-30 | 2001-11-27 | Cisco Technology, Inc. | System and method for rules-driven multi-phase network vulnerability assessment |
| JP2000023116A (en) | 1998-07-01 | 2000-01-21 | Hitachi Ltd | Object identifier processing method and recording medium for implementing the method |
| US6442686B1 (en) | 1998-07-02 | 2002-08-27 | Networks Associates Technology, Inc. | System and methodology for messaging server-based management and enforcement of crypto policies |
| US6347375B1 (en) | 1998-07-08 | 2002-02-12 | Ontrack Data International, Inc | Apparatus and method for remote virus diagnosis and repair |
| US6292833B1 (en) | 1998-07-17 | 2001-09-18 | Openwave Systems Inc. | Method and apparatus for providing access control to local services of mobile devices |
| US6253337B1 (en) | 1998-07-21 | 2001-06-26 | Raytheon Company | Information security analysis system |
| US6269447B1 (en) | 1998-07-21 | 2001-07-31 | Raytheon Company | Information security analysis system |
| US6151675A (en) | 1998-07-23 | 2000-11-21 | Tumbleweed Software Corporation | Method and apparatus for effecting secure document format conversion |
| GB2340344A (en) | 1998-07-29 | 2000-02-16 | Nokia Mobile Phones Ltd | Bilateral Data Transfer Verification for Programming a Cellular Phone |
| US6223213B1 (en) | 1998-07-31 | 2001-04-24 | Webtv Networks, Inc. | Browser-based email system with user interface for audio/video capture |
| US6711127B1 (en) | 1998-07-31 | 2004-03-23 | General Dynamics Government Systems Corporation | System for intrusion detection and vulnerability analysis in a telecommunications signaling network |
| US6266668B1 (en) | 1998-08-04 | 2001-07-24 | Dryken Technologies, Inc. | System and method for dynamic data-mining and on-line communication of customized information |
| US6330551B1 (en) | 1998-08-06 | 2001-12-11 | Cybersettle.Com, Inc. | Computerized dispute resolution system and method |
| US6304973B1 (en) | 1998-08-06 | 2001-10-16 | Cryptek Secure Communications, Llc | Multi-level security network system |
| US6169969B1 (en)* | 1998-08-07 | 2001-01-02 | The United States Of America As Represented By The Director Of The National Security Agency | Device and method for full-text large-dictionary string matching using n-gram hashing |
| US6356935B1 (en)* | 1998-08-14 | 2002-03-12 | Xircom Wireless, Inc. | Apparatus and method for an authenticated electronic userid |
| US6442588B1 (en) | 1998-08-20 | 2002-08-27 | At&T Corp. | Method of administering a dynamic filtering firewall |
| US6223094B1 (en) | 1998-08-21 | 2001-04-24 | Sap Aktiengesellschaft | Multi-tiered structure for storing and displaying product and process variants |
| US6269380B1 (en) | 1998-08-31 | 2001-07-31 | Xerox Corporation | Property based mechanism for flexibility supporting front-end and back-end components having different communication protocols |
| US6438612B1 (en) | 1998-09-11 | 2002-08-20 | Ssh Communications Security, Ltd. | Method and arrangement for secure tunneling of data between virtual routers |
| US6401210B1 (en) | 1998-09-23 | 2002-06-04 | Intel Corporation | Method of managing computer virus infected files |
| US6324569B1 (en) | 1998-09-23 | 2001-11-27 | John W. L. Ogilvie | Self-removing email verified or designated as such by a message distributor for the convenience of a recipient |
| US6687732B1 (en) | 1998-09-28 | 2004-02-03 | Inktomi Corporation | Adaptive traffic bypassing in an intercepting network driver |
| US6577920B1 (en) | 1998-10-02 | 2003-06-10 | Data Fellows Oyj | Computer virus screening |
| US6256733B1 (en) | 1998-10-08 | 2001-07-03 | Entrust Technologies Limited | Access and storage of secure group communication cryptographic keys |
| US6230190B1 (en) | 1998-10-09 | 2001-05-08 | Openwave Systems Inc. | Shared-everything file storage for clustered system |
| US6219706B1 (en) | 1998-10-16 | 2001-04-17 | Cisco Technology, Inc. | Access control for networks |
| US6330670B1 (en) | 1998-10-26 | 2001-12-11 | Microsoft Corporation | Digital rights management operating system |
| US6327652B1 (en) | 1998-10-26 | 2001-12-04 | Microsoft Corporation | Loading and identifying a digital rights management operating system |
| US6460141B1 (en) | 1998-10-28 | 2002-10-01 | Rsa Security Inc. | Security and access management system for web-enabled and non-web-enabled applications and content on a computer network |
| US6260043B1 (en) | 1998-11-06 | 2001-07-10 | Microsoft Corporation | Automatic file format converter |
| US6321338B1 (en) | 1998-11-09 | 2001-11-20 | Sri International | Network surveillance |
| US6820202B1 (en) | 1998-11-09 | 2004-11-16 | First Data Corporation | Account authority digital signature (AADS) system |
| US6282565B1 (en) | 1998-11-17 | 2001-08-28 | Kana Communications, Inc. | Method and apparatus for performing enterprise email management |
| US6249807B1 (en) | 1998-11-17 | 2001-06-19 | Kana Communications, Inc. | Method and apparatus for performing enterprise email management |
| US6272532B1 (en) | 1998-12-02 | 2001-08-07 | Harold F. Feinleib | Electronic reminder system with universal email input |
| US6438549B1 (en) | 1998-12-03 | 2002-08-20 | International Business Machines Corporation | Method for storing sparse hierarchical data in a relational database |
| US6571245B2 (en) | 1998-12-07 | 2003-05-27 | Magically, Inc. | Virtual desktop in a computer network |
| US6266774B1 (en) | 1998-12-08 | 2001-07-24 | Mcafee.Com Corporation | Method and system for securing, managing or optimizing a personal computer |
| US6370648B1 (en) | 1998-12-08 | 2002-04-09 | Visa International Service Association | Computer network intrusion detection |
| US6546416B1 (en) | 1998-12-09 | 2003-04-08 | Infoseek Corporation | Method and system for selectively blocking delivery of bulk electronic mail |
| US6400804B1 (en) | 1998-12-10 | 2002-06-04 | At&T Corp. | On-hold activity selection apparatus and method |
| US6550012B1 (en) | 1998-12-11 | 2003-04-15 | Network Associates, Inc. | Active firewall system and methodology |
| US6249575B1 (en) | 1998-12-11 | 2001-06-19 | Securelogix Corporation | Telephony security system |
| US6367009B1 (en) | 1998-12-17 | 2002-04-02 | International Business Machines Corporation | Extending SSL to a multi-tier environment using delegation of authentication and authority |
| US6430688B1 (en) | 1998-12-22 | 2002-08-06 | International Business Machines Corporation | Architecture for web-based on-line-off-line digital certificate authority |
| US6664666B2 (en) | 1998-12-23 | 2003-12-16 | Engineering Matters, Inc. | Motor assembly allowing output in multiple degrees of freedom |
| US6434536B1 (en) | 1998-12-23 | 2002-08-13 | Timothy S. Geiger | Methods and systems for commerce |
| US6574737B1 (en) | 1998-12-23 | 2003-06-03 | Symantec Corporation | System for penetrating computer or computer network |
| US6615242B1 (en)* | 1998-12-28 | 2003-09-02 | At&T Corp. | Automatic uniform resource locator-based message filter |
| US6118856A (en) | 1998-12-28 | 2000-09-12 | Nortel Networks Corporation | Method and apparatus for automatically forwarding an email message or portion thereof to a remote device |
| US6301668B1 (en) | 1998-12-29 | 2001-10-09 | Cisco Technology, Inc. | Method and system for adaptive network security using network vulnerability assessment |
| US6499107B1 (en) | 1998-12-29 | 2002-12-24 | Cisco Technology, Inc. | Method and system for adaptive network security using intelligent packet analysis |
| US6654787B1 (en) | 1998-12-31 | 2003-11-25 | Brightmail, Incorporated | Method and apparatus for filtering e-mail |
| US6266692B1 (en) | 1999-01-04 | 2001-07-24 | International Business Machines Corporation | Method for blocking all unwanted e-mail (SPAM) using a header-based password |
| US6477651B1 (en) | 1999-01-08 | 2002-11-05 | Cisco Technology, Inc. | Intrusion detection system and method having dynamically loaded signatures |
| US6715082B1 (en) | 1999-01-14 | 2004-03-30 | Cisco Technology, Inc. | Security server token caching |
| US6487666B1 (en) | 1999-01-15 | 2002-11-26 | Cisco Technology, Inc. | Intrusion detection signature analysis using regular expressions and logical operators |
| US6578147B1 (en) | 1999-01-15 | 2003-06-10 | Cisco Technology, Inc. | Parallel intrusion detection sensors with load balancing for high speed networks |
| US6954775B1 (en) | 1999-01-15 | 2005-10-11 | Cisco Technology, Inc. | Parallel intrusion detection sensors with load balancing for high speed networks |
| US6327594B1 (en) | 1999-01-29 | 2001-12-04 | International Business Machines Corporation | Methods for shared data management in a pervasive computing environment |
| US7917744B2 (en) | 1999-02-03 | 2011-03-29 | Cybersoft, Inc. | Apparatus and methods for intercepting, examining and controlling code, data and files and their transfer in instant messaging and peer-to-peer applications |
| US6230266B1 (en) | 1999-02-03 | 2001-05-08 | Sun Microsystems, Inc. | Authentication system and process |
| US6424650B1 (en) | 1999-02-09 | 2002-07-23 | 3Com Corporation | Network address filter device |
| JP4779183B2 (en) | 1999-03-26 | 2011-09-28 | ソニー株式会社 | Playback apparatus and playback method |
| US6678270B1 (en) | 1999-03-12 | 2004-01-13 | Sandstorm Enterprises, Inc. | Packet interception system including arrangement facilitating authentication of intercepted packets |
| US6405318B1 (en) | 1999-03-12 | 2002-06-11 | Psionic Software, Inc. | Intrusion detection system |
| US6725377B1 (en) | 1999-03-12 | 2004-04-20 | Networks Associates Technology, Inc. | Method and system for updating anti-intrusion software |
| US6609205B1 (en) | 1999-03-18 | 2003-08-19 | Cisco Technology, Inc. | Network intrusion detection signature analysis using decision graphs |
| US6301699B1 (en) | 1999-03-18 | 2001-10-09 | Corekt Security Systems, Inc. | Method for detecting buffer overflow for computer security |
| US6438576B1 (en) | 1999-03-29 | 2002-08-20 | International Business Machines Corporation | Method and apparatus of a collaborative proxy system for distributed deployment of object rendering |
| US6711679B1 (en) | 1999-03-31 | 2004-03-23 | International Business Machines Corporation | Public key infrastructure delegation |
| US6732149B1 (en) | 1999-04-09 | 2004-05-04 | International Business Machines Corporation | System and method for hindering undesired transmission or receipt of electronic messages |
| JP2000293587A (en)* | 1999-04-09 | 2000-10-20 | Sony Corp | Information processor, information processing method, management device and method, and providing medium |
| US6584488B1 (en) | 1999-04-12 | 2003-06-24 | International Business Machines Corporation | Controlling allocation of system resources with an enhanced priority calculation |
| US6804778B1 (en) | 1999-04-15 | 2004-10-12 | Gilian Technologies, Ltd. | Data quality assurance |
| US6981146B1 (en) | 1999-05-17 | 2005-12-27 | Invicta Networks, Inc. | Method of communications and communication network intrusion protection methods and intrusion attempt detection system |
| US6578025B1 (en) | 1999-06-11 | 2003-06-10 | Abuzz Technologies, Inc. | Method and apparatus for distributing information to users |
| US6901402B1 (en)* | 1999-06-18 | 2005-05-31 | Microsoft Corporation | System for improving the performance of information retrieval-type tasks by identifying the relations of constituents |
| US6731756B1 (en) | 1999-06-21 | 2004-05-04 | Elisar Software Corporation, Inc. | Method for securing video images |
| US6804237B1 (en) | 1999-06-23 | 2004-10-12 | Nortel Networks Limited | Method, devices and signals for multiplexing payload data for transport in a data network |
| US6484176B1 (en) | 1999-06-25 | 2002-11-19 | Baynet World, Inc. | System and process for providing remote interactive access to a real estate information database using a portable computing device |
| US6895436B1 (en) | 1999-07-01 | 2005-05-17 | International Business Machines Corporation | Method and system for evaluating network security |
| US6910135B1 (en) | 1999-07-07 | 2005-06-21 | Verizon Corporate Services Group Inc. | Method and apparatus for an intruder detection reporting and response system |
| US6560632B1 (en) | 1999-07-16 | 2003-05-06 | International Business Machines Corporation | System and method for managing files in a distributed system using prioritization |
| US6772346B1 (en) | 1999-07-16 | 2004-08-03 | International Business Machines Corporation | System and method for managing files in a distributed system using filtering |
| US6915426B1 (en) | 1999-07-23 | 2005-07-05 | Networks Associates Technology, Inc. | System and method for enabling authentication at different authentication strength-performance levels |
| US6976168B1 (en) | 1999-07-23 | 2005-12-13 | Mcafee, Inc. | System and method for adaptive cryptographically synchronized authentication |
| US7886008B2 (en) | 1999-07-28 | 2011-02-08 | Rpost International Limited | System and method for verifying delivery and integrity of electronic messages |
| US6647400B1 (en) | 1999-08-30 | 2003-11-11 | Symantec Corporation | System and method for analyzing filesystems to detect intrusions |
| US6742015B1 (en) | 1999-08-31 | 2004-05-25 | Accenture Llp | Base services patterns in a netcentric environment |
| US6324647B1 (en) | 1999-08-31 | 2001-11-27 | Michel K. Bowman-Amuah | System, method and article of manufacture for security management in a development architecture framework |
| US6332163B1 (en) | 1999-09-01 | 2001-12-18 | Accenture, Llp | Method for providing communication services over a computer network system |
| US7853989B2 (en) | 2000-02-08 | 2010-12-14 | Katsikas Peter L | System for eliminating unauthorized electronic mail |
| US6952776B1 (en) | 1999-09-22 | 2005-10-04 | International Business Machines Corporation | Method and apparatus for increasing virus detection speed using a database |
| US6389419B1 (en) | 1999-10-06 | 2002-05-14 | Cisco Technology, Inc. | Storing and retrieving connection information using bidirectional hashing of connection identifiers |
| US6304898B1 (en) | 1999-10-13 | 2001-10-16 | Datahouse, Inc. | Method and system for creating and sending graphical email |
| US6789202B1 (en) | 1999-10-15 | 2004-09-07 | Networks Associates Technology, Inc. | Method and apparatus for providing a policy-driven intrusion detection system |
| JP3843667B2 (en) | 1999-10-15 | 2006-11-08 | セイコーエプソン株式会社 | Data transfer control device and electronic device |
| US6662230B1 (en) | 1999-10-20 | 2003-12-09 | International Business Machines Corporation | System and method for dynamically limiting robot access to server data |
| US7181768B1 (en)* | 1999-10-28 | 2007-02-20 | Cigital | Computer intrusion detection system and method based on application monitoring |
| US6611869B1 (en) | 1999-10-28 | 2003-08-26 | Networks Associates, Inc. | System and method for providing trustworthy network security concern communication in an active security management environment |
| JP3463803B2 (en) | 1999-11-09 | 2003-11-05 | 松下電器産業株式会社 | Cluster server device |
| US6990591B1 (en) | 1999-11-18 | 2006-01-24 | Secureworks, Inc. | Method and system for remotely configuring and monitoring a communication device |
| US7363361B2 (en) | 2000-08-18 | 2008-04-22 | Akamai Technologies, Inc. | Secure content delivery system |
| US6321267B1 (en) | 1999-11-23 | 2001-11-20 | Escom Corporation | Method and apparatus for filtering junk email |
| US6363489B1 (en) | 1999-11-29 | 2002-03-26 | Forescout Technologies Inc. | Method for automatic intrusion detection and deflection in a network |
| US6851057B1 (en) | 1999-11-30 | 2005-02-01 | Symantec Corporation | Data driven detection of viruses |
| US6728886B1 (en) | 1999-12-01 | 2004-04-27 | Trend Micro Incorporated | Distributed virus scanning arrangements and methods therefor |
| FR2802667B1 (en) | 1999-12-21 | 2002-01-25 | Bull Sa | METHOD AND DEVICE FOR CONFIGURING FIREWALLS IN A COMPUTER SYSTEM |
| US6697950B1 (en) | 1999-12-22 | 2004-02-24 | Networks Associates Technology, Inc. | Method and apparatus for detecting a macro computer virus using static analysis |
| US6460050B1 (en)* | 1999-12-22 | 2002-10-01 | Mark Raymond Pace | Distributed content identification system |
| US6775657B1 (en) | 1999-12-22 | 2004-08-10 | Cisco Technology, Inc. | Multilayered intrusion detection system and method |
| US20010034839A1 (en) | 1999-12-24 | 2001-10-25 | Guenter Karjoth | Method and apparatus for secure transmission of data and applications |
| GB2353372B (en) | 1999-12-24 | 2001-08-22 | F Secure Oyj | Remote computer virus scanning |
| US6701440B1 (en) | 2000-01-06 | 2004-03-02 | Networks Associates Technology, Inc. | Method and system for protecting a computer using a remote e-mail scanning device |
| US6976271B1 (en) | 2000-01-06 | 2005-12-13 | International Business Machines Corporation | Method and system for retrieving an anti-virus signature from one or a plurality of virus-free certificate authorities |
| US6928550B1 (en) | 2000-01-06 | 2005-08-09 | International Business Machines Corporation | Method and system for generating and using a virus free file certificate |
| US6735700B1 (en) | 2000-01-11 | 2004-05-11 | Network Associates Technology, Inc. | Fast virus scanning using session stamping |
| US6785818B1 (en) | 2000-01-14 | 2004-08-31 | Symantec Corporation | Thwarting malicious registry mapping modifications and map-loaded module masquerade attacks |
| US6802002B1 (en) | 2000-01-14 | 2004-10-05 | Hewlett-Packard Development Company, L.P. | Method and apparatus for providing field confidentiality in digital certificates |
| IL134066A (en) | 2000-01-16 | 2004-07-25 | Eluv Holdings Ltd | Key encrypted e-mail system |
| JP2001209584A (en) | 2000-01-26 | 2001-08-03 | Nec Niigata Ltd | Data encryption device and its method |
| US6883101B1 (en) | 2000-02-08 | 2005-04-19 | Harris Corporation | System and method for assessing the security posture of a network using goal oriented fuzzy logic decision rules |
| US7117246B2 (en) | 2000-02-22 | 2006-10-03 | Sendmail, Inc. | Electronic mail system with methodology providing distributed message store |
| US6452613B1 (en) | 2000-03-01 | 2002-09-17 | First Usa Bank, N.A. | System and method for an automated scoring tool for assessing new technologies |
| US6691156B1 (en) | 2000-03-10 | 2004-02-10 | International Business Machines Corporation | Method for restricting delivery of unsolicited E-mail |
| US6971019B1 (en) | 2000-03-14 | 2005-11-29 | Symantec Corporation | Histogram-based virus detection |
| US6748531B1 (en) | 2000-03-28 | 2004-06-08 | Koninklijke Philips Electronics N.V | Method and apparatus for confirming and revoking trust in a multi-level content distribution system |
| US6892237B1 (en) | 2000-03-28 | 2005-05-10 | Cisco Technology, Inc. | Method and apparatus for high-speed parsing of network messages |
| US6519703B1 (en) | 2000-04-14 | 2003-02-11 | James B. Joyce | Methods and apparatus for heuristic firewall |
| US6584564B2 (en)* | 2000-04-25 | 2003-06-24 | Sigaba Corporation | Secure e-mail system |
| US7089428B2 (en) | 2000-04-28 | 2006-08-08 | Internet Security Systems, Inc. | Method and system for managing computer security information |
| US6735703B1 (en) | 2000-05-08 | 2004-05-11 | Networks Associates Technology, Inc. | Multi-platform sequence-based anomaly detection wrapper |
| US6742124B1 (en) | 2000-05-08 | 2004-05-25 | Networks Associates Technology, Inc. | Sequence-based anomaly detection using a distance matrix |
| US6968336B1 (en) | 2000-05-18 | 2005-11-22 | International Business Machines Corporation | Method for generating, organizing table codes either code is highest code level or code is linked to parent code in hierarchical structure |
| US6950933B1 (en) | 2000-05-19 | 2005-09-27 | Networks Associates Technology, Inc. | Method and system for management and notification of electronic certificate changes |
| US6922776B2 (en) | 2000-05-19 | 2005-07-26 | Networks Associates Technology, Inc. | Scalable system and method for management and notification of electronic certificate changes |
| US20030159070A1 (en) | 2001-05-28 | 2003-08-21 | Yaron Mayer | System and method for comprehensive general generic protection for computers against malicious programs that may steal information and/or cause damages |
| JP2002056176A (en) | 2000-06-01 | 2002-02-20 | Asgent Inc | Security policy construction method and apparatus, and method and apparatus for supporting security policy construction |
| US6895385B1 (en) | 2000-06-02 | 2005-05-17 | Open Ratings | Method and system for ascribing a reputation to an entity as a rater of other entities |
| US6892179B1 (en) | 2000-06-02 | 2005-05-10 | Open Ratings Inc. | System and method for ascribing a reputation to an entity |
| US6892178B1 (en) | 2000-06-02 | 2005-05-10 | Open Ratings Inc. | Method and system for ascribing a reputation to an entity from the perspective of another entity |
| US7007301B2 (en) | 2000-06-12 | 2006-02-28 | Hewlett-Packard Development Company, L.P. | Computer architecture for an intrusion detection system |
| US7134141B2 (en) | 2000-06-12 | 2006-11-07 | Hewlett-Packard Development Company, L.P. | System and method for host and network based intrusion detection and response |
| US6611925B1 (en) | 2000-06-13 | 2003-08-26 | Networks Associates Technology, Inc. | Single point of entry/origination item scanning within an enterprise or workgroup |
| US6732101B1 (en) | 2000-06-15 | 2004-05-04 | Zix Corporation | Secure message forwarding system detecting user's preferences including security preferences |
| US6721721B1 (en) | 2000-06-15 | 2004-04-13 | International Business Machines Corporation | Virus checking and reporting for computer database search results |
| US20030061506A1 (en) | 2001-04-05 | 2003-03-27 | Geoffrey Cooper | System and method for security policy |
| US6981158B1 (en) | 2000-06-19 | 2005-12-27 | Bbnt Solutions Llc | Method and apparatus for tracing packets |
| US7328349B2 (en) | 2001-12-14 | 2008-02-05 | Bbn Technologies Corp. | Hash-based systems and methods for detecting, preventing, and tracing network worms and viruses |
| US7058974B1 (en) | 2000-06-21 | 2006-06-06 | Netrake Corporation | Method and apparatus for preventing denial of service attacks |
| US20020046041A1 (en) | 2000-06-23 | 2002-04-18 | Ken Lang | Automated reputation/trust service |
| US7127743B1 (en) | 2000-06-23 | 2006-10-24 | Netforensics, Inc. | Comprehensive security structure platform for network managers |
| WO2002003653A2 (en) | 2000-06-30 | 2002-01-10 | British Telecommunications Public Limited Company | Packet data communications |
| US6870849B1 (en) | 2000-07-06 | 2005-03-22 | Ross W. Callon | Apparatus and method for efficient hashing in networks |
| US8661539B2 (en) | 2000-07-10 | 2014-02-25 | Oracle International Corporation | Intrusion threat detection |
| US6738462B1 (en) | 2000-07-19 | 2004-05-18 | Avaya Technology Corp. | Unified communications automated personal name addressing |
| US6757675B2 (en) | 2000-07-24 | 2004-06-29 | The Regents Of The University Of California | Method and apparatus for indexing document content and content comparison with World Wide Web search service |
| IL153955A0 (en) | 2000-07-25 | 2003-07-31 | Peribit Networks Inc | Network architecture and methods for transparent on-line cross-sessional encoding and transport of network communications data |
| US6687696B2 (en) | 2000-07-26 | 2004-02-03 | Recommind Inc. | System and method for personalized search, information filtering, and for generating recommendations utilizing statistical latent class models |
| US6687687B1 (en) | 2000-07-26 | 2004-02-03 | Zix Scm, Inc. | Dynamic indexing information retrieval or filtering system |
| US7085934B1 (en) | 2000-07-27 | 2006-08-01 | Mcafee, Inc. | Method and system for limiting processor utilization by a virus scanner |
| GB2365158A (en) | 2000-07-28 | 2002-02-13 | Content Technologies Ltd | File analysis using byte distributions |
| EP1312193A2 (en) | 2000-08-16 | 2003-05-21 | Filestream, Inc. | End-to-end secure file transfer method and system |
| US6799197B1 (en) | 2000-08-29 | 2004-09-28 | Networks Associates Technology, Inc. | Secure method and system for using a public network or email to administer to software on a plurality of client computers |
| US6910134B1 (en) | 2000-08-29 | 2005-06-21 | Netrake Corporation | Method and device for innoculating email infected with a virus |
| US6772334B1 (en) | 2000-08-31 | 2004-08-03 | Networks Associates, Inc. | System and method for preventing a spoofed denial of service attack in a networked computing environment |
| GB2368233B (en) | 2000-08-31 | 2002-10-16 | F Secure Oyj | Maintaining virus detection software |
| US7043759B2 (en) | 2000-09-07 | 2006-05-09 | Mazu Networks, Inc. | Architecture to thwart denial of service attacks |
| US7278159B2 (en) | 2000-09-07 | 2007-10-02 | Mazu Networks, Inc. | Coordinated thwarting of denial of service attacks |
| US20020032793A1 (en) | 2000-09-08 | 2002-03-14 | The Regents Of The University Of Michigan | Method and system for reconstructing a path taken by undesirable network traffic through a computer network from a source of the traffic |
| US20020032871A1 (en) | 2000-09-08 | 2002-03-14 | The Regents Of The University Of Michigan | Method and system for detecting, tracking and blocking denial of service attacks over a computer network |
| US20020038339A1 (en) | 2000-09-08 | 2002-03-28 | Wei Xu | Systems and methods for packet distribution |
| US6785732B1 (en) | 2000-09-11 | 2004-08-31 | International Business Machines Corporation | Web server apparatus and method for virus checking |
| US6826698B1 (en) | 2000-09-15 | 2004-11-30 | Networks Associates Technology, Inc. | System, method and computer program product for rule based network security policies |
| US6650890B1 (en) | 2000-09-29 | 2003-11-18 | Postini, Inc. | Value-added electronic messaging services and transparent implementation thereof using intermediate server |
| US6968461B1 (en) | 2000-10-03 | 2005-11-22 | Networks Associates Technology, Inc. | Providing break points in a malware scanning operation |
| US6757830B1 (en) | 2000-10-03 | 2004-06-29 | Networks Associates Technology, Inc. | Detecting unwanted properties in received email messages |
| US20020069263A1 (en) | 2000-10-13 | 2002-06-06 | Mark Sears | Wireless java technology |
| US20030097439A1 (en) | 2000-10-23 | 2003-05-22 | Strayer William Timothy | Systems and methods for identifying anomalies in network data streams |
| US20020129002A1 (en) | 2000-10-27 | 2002-09-12 | Alberts Douglas Wesley | eMediaCarts |
| US7082536B2 (en) | 2000-11-13 | 2006-07-25 | Globalcerts, Lc | System and method for computerized global messaging encryption |
| US20040181462A1 (en)* | 2000-11-17 | 2004-09-16 | Bauer Robert D. | Electronic communication service |
| US6934857B1 (en) | 2000-11-27 | 2005-08-23 | Networks Associates Technology, Inc. | Security system and method for handheld computers |
| US6782503B1 (en) | 2000-11-28 | 2004-08-24 | Nortel Networks Limited | Generating a signature to add to a test packet to achieve a target check value |
| US20020078382A1 (en) | 2000-11-29 | 2002-06-20 | Ali Sheikh | Scalable system for monitoring network system and components and methodology therefore |
| DE60124295T8 (en) | 2000-11-30 | 2007-12-06 | Lancope, Inc. | RIVER-BASED DETECTION OF AN INSERT INTO A NETWORK |
| CA2327211A1 (en) | 2000-12-01 | 2002-06-01 | Nortel Networks Limited | Management of log archival and reporting for data network security systems |
| US7844666B2 (en) | 2000-12-12 | 2010-11-30 | Microsoft Corporation | Controls and displays for acquiring preferences, inspecting behavior, and guiding the learning and decision policies of an adaptive communications prioritization and routing system |
| US6622150B1 (en) | 2000-12-18 | 2003-09-16 | Networks Associates Technology, Inc. | System and method for efficiently managing computer virus definitions using a structured virus database |
| US20020083342A1 (en) | 2000-12-21 | 2002-06-27 | Webb Brian T. | Systems, methods and computer program products for accessing devices on private networks via clients on a public network |
| US6738932B1 (en) | 2000-12-22 | 2004-05-18 | Sun Microsystems, Inc. | Method and system for identifying software revisions from memory images |
| US6725223B2 (en)* | 2000-12-22 | 2004-04-20 | International Business Machines Corporation | Storage format for encoded vector indexes |
| US20030084020A1 (en) | 2000-12-22 | 2003-05-01 | Li Shu | Distributed fault tolerant and secure storage |
| US6775704B1 (en) | 2000-12-28 | 2004-08-10 | Networks Associates Technology, Inc. | System and method for preventing a spoofed remote procedure call denial of service attack in a networked computing environment |
| US6779033B1 (en) | 2000-12-28 | 2004-08-17 | Networks Associates Technology, Inc. | System and method for transacting a validated application session in a networked computing environment |
| MXPA03006024A (en) | 2001-01-02 | 2005-02-14 | Trusecure Corp | Object-oriented method, system and medium for risk management by creating inter-dependency between objects, criteria and metrics. |
| US6965939B2 (en) | 2001-01-05 | 2005-11-15 | International Business Machines Corporation | Method and apparatus for processing requests in a network data processing system based on a trust association between servers |
| GB2371125A (en) | 2001-01-13 | 2002-07-17 | Secr Defence | Computer protection system |
| US20020133586A1 (en) | 2001-01-16 | 2002-09-19 | Carter Shanklin | Method and device for monitoring data traffic and preventing unauthorized access to a network |
| US20030051026A1 (en) | 2001-01-19 | 2003-03-13 | Carter Ernst B. | Network surveillance and security system |
| US7168093B2 (en) | 2001-01-25 | 2007-01-23 | Solutionary, Inc. | Method and apparatus for verifying the integrity and security of computer networks and implementation of counter measures |
| US6983380B2 (en) | 2001-02-06 | 2006-01-03 | Networks Associates Technology, Inc. | Automatically generating valid behavior specifications for intrusion detection |
| US7281267B2 (en) | 2001-02-20 | 2007-10-09 | Mcafee, Inc. | Software audit system |
| US8219620B2 (en) | 2001-02-20 | 2012-07-10 | Mcafee, Inc. | Unwanted e-mail filtering system including voting feedback |
| US7415504B2 (en)* | 2001-02-26 | 2008-08-19 | Symantec Corporation | System and method for controlling distribution of network communications |
| US20020120853A1 (en) | 2001-02-27 | 2002-08-29 | Networks Associates Technology, Inc. | Scripted distributed denial-of-service (DDoS) attack discrimination using turing tests |
| US7363657B2 (en) | 2001-03-12 | 2008-04-22 | Emc Corporation | Using a virus checker in one file server to check for viruses in another file server |
| US20020143963A1 (en) | 2001-03-15 | 2002-10-03 | International Business Machines Corporation | Web server intrusion detection method and apparatus |
| US20020133365A1 (en) | 2001-03-19 | 2002-09-19 | William Grey | System and method for aggregating reputational information |
| US7287280B2 (en) | 2002-02-12 | 2007-10-23 | Goldman Sachs & Co. | Automated security management |
| US20040193482A1 (en) | 2001-03-23 | 2004-09-30 | Restaurant Services, Inc. | System, method and computer program product for user-specific advertising in a supply chain management framework |
| US20020138759A1 (en) | 2001-03-26 | 2002-09-26 | International Business Machines Corporation | System and method for secure delivery of a parcel or document |
| US7010696B1 (en) | 2001-03-30 | 2006-03-07 | Mcafee, Inc. | Method and apparatus for predicting the incidence of a virus |
| US7080000B1 (en) | 2001-03-30 | 2006-07-18 | Mcafee, Inc. | Method and system for bi-directional updating of antivirus database |
| US7007169B2 (en) | 2001-04-04 | 2006-02-28 | International Business Machines Corporation | Method and apparatus for protecting a web server against vandals attacks without restricting legitimate access |
| WO2002093334A2 (en) | 2001-04-06 | 2002-11-21 | Symantec Corporation | Temporal access control for computer virus outbreaks |
| US20020147734A1 (en) | 2001-04-06 | 2002-10-10 | Shoup Randall Scott | Archiving method and system |
| US20020147780A1 (en) | 2001-04-09 | 2002-10-10 | Liu James Y. | Method and system for scanning electronic mail to detect and eliminate computer viruses using a group of email-scanning servers and a recipient's email gateway |
| US7089589B2 (en) | 2001-04-10 | 2006-08-08 | Lenovo (Singapore) Pte. Ltd. | Method and apparatus for the detection, notification, and elimination of certain computer viruses on a network using a promiscuous system as bait |
| US20020194161A1 (en) | 2001-04-12 | 2002-12-19 | Mcnamee J. Paul | Directed web crawler with machine learning |
| US6941478B2 (en) | 2001-04-13 | 2005-09-06 | Nokia, Inc. | System and method for providing exploit protection with message tracking |
| CN1509438A (en)* | 2001-04-13 | 2004-06-30 | ��˹��ŵ�� | System and method for providing utilization protection for a network |
| US6947936B1 (en) | 2001-04-30 | 2005-09-20 | Hewlett-Packard Development Company, L.P. | Method for a topic hierarchy classification system |
| US7603709B2 (en) | 2001-05-03 | 2009-10-13 | Computer Associates Think, Inc. | Method and apparatus for predicting and preventing attacks in communications networks |
| US7769845B2 (en) | 2001-05-04 | 2010-08-03 | Whale Communications Ltd | Method and system for terminating an authentication session upon user sign-off |
| US20030055931A1 (en) | 2001-09-18 | 2003-03-20 | Cravo De Almeida Marcio | Managing a remote device |
| US7228565B2 (en) | 2001-05-15 | 2007-06-05 | Mcafee, Inc. | Event reporting between a reporting computer and a receiving computer |
| US6768991B2 (en) | 2001-05-15 | 2004-07-27 | Networks Associates Technology, Inc. | Searching for sequences of character data |
| CA2386491A1 (en) | 2001-05-16 | 2002-11-16 | Kasten Chase Applied Research Limited | System for secure electronic information transmission |
| US20030028803A1 (en) | 2001-05-18 | 2003-02-06 | Bunker Nelson Waldo | Network vulnerability assessment system and method |
| US20020178227A1 (en) | 2001-05-25 | 2002-11-28 | International Business Machines Corporation | Routing instant messages using configurable, pluggable delivery managers |
| US20030009698A1 (en)* | 2001-05-30 | 2003-01-09 | Cascadezone, Inc. | Spam avenger |
| US7380126B2 (en) | 2001-06-01 | 2008-05-27 | Logan James D | Methods and apparatus for controlling the transmission and receipt of email messages |
| US7458094B2 (en) | 2001-06-06 | 2008-11-25 | Science Applications International Corporation | Intrusion prevention system |
| US20040103315A1 (en) | 2001-06-07 | 2004-05-27 | Geoffrey Cooper | Assessment tool |
| US7350234B2 (en) | 2001-06-11 | 2008-03-25 | Research Triangle Institute | Intrusion tolerant communication networks and associated methods |
| US20020186698A1 (en) | 2001-06-12 | 2002-12-12 | Glen Ceniza | System to map remote lan hosts to local IP addresses |
| DE60135449D1 (en) | 2001-06-14 | 2008-10-02 | Ibm | Intrusion detection in data processing systems |
| US20020194490A1 (en) | 2001-06-18 | 2002-12-19 | Avner Halperin | System and method of virus containment in computer networks |
| US6769016B2 (en) | 2001-07-26 | 2004-07-27 | Networks Associates Technology, Inc. | Intelligent SPAM detection system using an updateable neural analysis engine |
| US7181015B2 (en) | 2001-07-31 | 2007-02-20 | Mcafee, Inc. | Method and apparatus for cryptographic key establishment using an identity based symmetric keying technique |
| US7117533B1 (en) | 2001-08-03 | 2006-10-03 | Mcafee, Inc. | System and method for providing dynamic screening of transient messages in a distributed computing environment |
| US6745192B1 (en) | 2001-08-03 | 2004-06-01 | Networks Associates Technology Inc. | System and method for providing a multi-tiered hierarchical transient message store accessed using multiply hashed unique filenames |
| US7243374B2 (en) | 2001-08-08 | 2007-07-10 | Microsoft Corporation | Rapid application security threat analysis |
| US20030033463A1 (en) | 2001-08-10 | 2003-02-13 | Garnett Paul J. | Computer system storage |
| US20030037141A1 (en) | 2001-08-16 | 2003-02-20 | Gary Milo | Heuristic profiler software features |
| US7278160B2 (en) | 2001-08-16 | 2007-10-02 | International Business Machines Corporation | Presentation of correlated events as situation classes |
| US7120252B1 (en) | 2001-08-16 | 2006-10-10 | Mcafee, Inc. | System and method for automatically protecting private video content using cryptographic security for legacy systems |
| US7657935B2 (en)* | 2001-08-16 | 2010-02-02 | The Trustees Of Columbia University In The City Of New York | System and methods for detecting malicious email transmission |
| US6928556B2 (en) | 2001-08-30 | 2005-08-09 | International Business Machines Corporation | Method and apparatus in a data processing system for managing situations from correlated events |
| US6978223B2 (en) | 2001-09-06 | 2005-12-20 | Bbnt Solutions Llc | Systems and methods for network performance measurement using packet signature collection |
| US20030051163A1 (en) | 2001-09-13 | 2003-03-13 | Olivier Bidaud | Distributed network architecture security system |
| US7107618B1 (en) | 2001-09-25 | 2006-09-12 | Mcafee, Inc. | System and method for certifying that data received over a computer network has been checked for viruses |
| US7266844B2 (en) | 2001-09-27 | 2007-09-04 | Mcafee, Inc. | Heuristic detection of polymorphic computer viruses based on redundancy in viral code |
| US20030065943A1 (en) | 2001-09-28 | 2003-04-03 | Christoph Geis | Method and apparatus for recognizing and reacting to denial of service attacks on a computerized network |
| US7010608B2 (en) | 2001-09-28 | 2006-03-07 | Intel Corporation | System and method for remotely accessing a home server while preserving end-to-end security |
| US6892241B2 (en) | 2001-09-28 | 2005-05-10 | Networks Associates Technology, Inc. | Anti-virus policy enforcement system and method |
| US6907430B2 (en) | 2001-10-04 | 2005-06-14 | Booz-Allen Hamilton, Inc. | Method and system for assessing attacks on computer networks using Bayesian networks |
| US7310818B1 (en) | 2001-10-25 | 2007-12-18 | Mcafee, Inc. | System and method for tracking computer viruses |
| US8261059B2 (en) | 2001-10-25 | 2012-09-04 | Verizon Business Global Llc | Secure file transfer and secure file transfer protocol |
| US20030084323A1 (en) | 2001-10-31 | 2003-05-01 | Gales George S. | Network intrusion detection system and method |
| US7444679B2 (en) | 2001-10-31 | 2008-10-28 | Hewlett-Packard Development Company, L.P. | Network, method and computer readable medium for distributing security updates to select nodes on a network |
| US20030135749A1 (en) | 2001-10-31 | 2003-07-17 | Gales George S. | System and method of defining the security vulnerabilities of a computer system |
| JP2003150748A (en) | 2001-11-09 | 2003-05-23 | Asgent Inc | Risk assessment method |
| US7315944B2 (en) | 2001-11-13 | 2008-01-01 | Ericsson Inc. | Secure handling of stored-value data objects |
| US20030093695A1 (en) | 2001-11-13 | 2003-05-15 | Santanu Dutta | Secure handling of stored-value data objects |
| US7487262B2 (en) | 2001-11-16 | 2009-02-03 | At & T Mobility Ii, Llc | Methods and systems for routing messages through a communications network based on message content |
| US20030095555A1 (en) | 2001-11-16 | 2003-05-22 | Mcnamara Justin | System for the validation and routing of messages |
| US20030101381A1 (en) | 2001-11-29 | 2003-05-29 | Nikolay Mateev | System and method for virus checking software |
| AU2002357029A1 (en) | 2001-11-30 | 2003-06-17 | A New Voice, Inc. | Method and system for contextual prioritization of unified messages |
| US6546493B1 (en) | 2001-11-30 | 2003-04-08 | Networks Associates Technology, Inc. | System, method and computer program product for risk assessment scanning based on detected anomalous events |
| US20030126464A1 (en) | 2001-12-04 | 2003-07-03 | Mcdaniel Patrick D. | Method and system for determining and enforcing security policy in a communication session |
| US7150042B2 (en) | 2001-12-06 | 2006-12-12 | Mcafee, Inc. | Techniques for performing malware scanning of files stored within a file storage device of a computer network |
| US7093002B2 (en) | 2001-12-06 | 2006-08-15 | Mcafee, Inc. | Handling of malware scanning of files stored within a file storage device of a computer network |
| US20030110392A1 (en) | 2001-12-06 | 2003-06-12 | Aucsmith David W. | Detecting intrusions |
| US7150043B2 (en) | 2001-12-12 | 2006-12-12 | International Business Machines Corporation | Intrusion detection method and signature table |
| KR100427449B1 (en) | 2001-12-14 | 2004-04-14 | 한국전자통신연구원 | Intrusion detection method using adaptive rule estimation in nids |
| US7096500B2 (en) | 2001-12-21 | 2006-08-22 | Mcafee, Inc. | Predictive malware scanning of internet data |
| US6754705B2 (en) | 2001-12-21 | 2004-06-22 | Networks Associates Technology, Inc. | Enterprise network analyzer architecture framework |
| US7400729B2 (en) | 2001-12-28 | 2008-07-15 | Intel Corporation | Secure delivery of encrypted digital content |
| CA2472268A1 (en) | 2001-12-31 | 2003-07-17 | Citadel Security Software Inc. | Automated computer vulnerability resolution system |
| JP4152108B2 (en) | 2002-01-18 | 2008-09-17 | 株式会社コムスクエア | Vulnerability monitoring method and system |
| US7076803B2 (en) | 2002-01-28 | 2006-07-11 | International Business Machines Corporation | Integrated intrusion detection services |
| US7222366B2 (en) | 2002-01-28 | 2007-05-22 | International Business Machines Corporation | Intrusion event filtering |
| US7743415B2 (en) | 2002-01-31 | 2010-06-22 | Riverbed Technology, Inc. | Denial of service attacks characterization |
| US7268899B2 (en) | 2002-01-31 | 2007-09-11 | Hewlett-Packard Development Company, L.P. | Secure system for delivery of a fax to a remote user |
| US7174566B2 (en) | 2002-02-01 | 2007-02-06 | Intel Corporation | Integrated network intrusion detection |
| US20030149887A1 (en) | 2002-02-01 | 2003-08-07 | Satyendra Yadav | Application-specific network intrusion detection |
| US6760845B1 (en) | 2002-02-08 | 2004-07-06 | Networks Associates Technology, Inc. | Capture file format system and method for a network analyzer |
| US8370936B2 (en) | 2002-02-08 | 2013-02-05 | Juniper Networks, Inc. | Multi-method gateway-based network security systems and methods |
| US7073074B2 (en) | 2002-02-13 | 2006-07-04 | Microsoft Corporation | System and method for storing events to enhance intrusion detection |
| KR100468232B1 (en) | 2002-02-19 | 2005-01-26 | 한국전자통신연구원 | Network-based Attack Tracing System and Method Using Distributed Agent and Manager Systems |
| WO2003071390A2 (en) | 2002-02-19 | 2003-08-28 | Postini Corporation | E-mail management services |
| US7458098B2 (en) | 2002-03-08 | 2008-11-25 | Secure Computing Corporation | Systems and methods for enhancing electronic communication security |
| US6941467B2 (en) | 2002-03-08 | 2005-09-06 | Ciphertrust, Inc. | Systems and methods for adaptive message interrogation through multiple queues |
| US7096498B2 (en) | 2002-03-08 | 2006-08-22 | Cipher Trust, Inc. | Systems and methods for message threat management |
| US7694128B2 (en) | 2002-03-08 | 2010-04-06 | Mcafee, Inc. | Systems and methods for secure communication delivery |
| US7124438B2 (en) | 2002-03-08 | 2006-10-17 | Ciphertrust, Inc. | Systems and methods for anomaly detection in patterns of monitored communications |
| US20030233328A1 (en) | 2002-04-23 | 2003-12-18 | Scott David A. | Method and system for securely communicating data in a communications network |
| AUPS193202A0 (en) | 2002-04-23 | 2002-05-30 | Pickup, Robert Barkley Mr | A method and system for authorising electronic mail |
| US6741595B2 (en) | 2002-06-11 | 2004-05-25 | Netrake Corporation | Device for enabling trap and trace of internet protocol communications |
| EP1376420A1 (en) | 2002-06-19 | 2004-01-02 | Pitsos Errikos | Method and system for classifying electronic documents |
| US20040203589A1 (en) | 2002-07-11 | 2004-10-14 | Wang Jiwei R. | Method and system for controlling messages in a communication network |
| US7222157B1 (en)* | 2002-07-15 | 2007-05-22 | Aol Llc | Identification and filtration of digital communications |
| US7017186B2 (en) | 2002-07-30 | 2006-03-21 | Steelcloud, Inc. | Intrusion detection system using self-organizing clusters |
| US6742128B1 (en) | 2002-08-28 | 2004-05-25 | Networks Associates Technology | Threat assessment orchestrator system and method |
| JP3831696B2 (en) | 2002-09-20 | 2006-10-11 | 株式会社日立製作所 | Network management apparatus and network management method |
| US20040111531A1 (en) | 2002-12-06 | 2004-06-10 | Stuart Staniford | Method and system for reducing the rate of infection of a communications network by a software worm |
| US6732157B1 (en) | 2002-12-13 | 2004-05-04 | Networks Associates Technology, Inc. | Comprehensive anti-spam system, method, and computer program product for filtering unwanted e-mail messages |
| US6859793B1 (en) | 2002-12-19 | 2005-02-22 | Networks Associates Technology, Inc. | Software license reporting and control system and method |
| US7171450B2 (en) | 2003-01-09 | 2007-01-30 | Microsoft Corporation | Framework to enable integration of anti-spam technologies |
| US8266215B2 (en) | 2003-02-20 | 2012-09-11 | Sonicwall, Inc. | Using distinguishing properties to classify messages |
| US20040177120A1 (en) | 2003-03-07 | 2004-09-09 | Kirsch Steven T. | Method for filtering e-mail messages |
| US20060168006A1 (en)* | 2003-03-24 | 2006-07-27 | Mr. Marvin Shannon | System and method for the classification of electronic communication |
| JP2004284241A (en) | 2003-03-24 | 2004-10-14 | Tdk Corp | Optical recording medium and sputtering target for optical recording medium |
| US7676546B2 (en) | 2003-03-25 | 2010-03-09 | Verisign, Inc. | Control and management of electronic messaging |
| GB0307913D0 (en) | 2003-04-05 | 2003-05-14 | Hewlett Packard Development Co | Management of peer-to-peer network using reputation services |
| US7483947B2 (en)* | 2003-05-02 | 2009-01-27 | Microsoft Corporation | Message rendering for identification of content features |
| US7051077B2 (en) | 2003-06-30 | 2006-05-23 | Mx Logic, Inc. | Fuzzy logic voting method and system for classifying e-mail using inputs from multiple spam classifiers |
| US7769594B2 (en) | 2003-09-05 | 2010-08-03 | France Telecom | Evaluation of reputation of an entity by a primary evaluation centre |
| US7415018B2 (en) | 2003-09-17 | 2008-08-19 | Alcatel Lucent | IP Time to Live (TTL) field used as a covert channel |
| US20050086526A1 (en) | 2003-10-17 | 2005-04-21 | Panda Software S.L. (Sociedad Unipersonal) | Computer implemented method providing software virus infection information in real time |
| US20050102366A1 (en) | 2003-11-07 | 2005-05-12 | Kirsch Steven T. | E-mail filter employing adaptive ruleset |
| US7624274B1 (en)* | 2004-02-11 | 2009-11-24 | AOL LLC, a Delaware Limited Company | Decreasing the fragility of duplicate document detecting algorithms |
| US7644127B2 (en) | 2004-03-09 | 2010-01-05 | Gozoom.Com, Inc. | Email analysis using fuzzy matching of text |
| US20050204159A1 (en)* | 2004-03-09 | 2005-09-15 | International Business Machines Corporation | System, method and computer program to block spam |
| US8918466B2 (en) | 2004-03-09 | 2014-12-23 | Tonny Yu | System for email processing and analysis |
| US7366764B1 (en)* | 2004-06-23 | 2008-04-29 | Chelonia Llc | Method for the identification and management of mass unsolicited e-mail |
| US7693945B1 (en)* | 2004-06-30 | 2010-04-06 | Google Inc. | System for reclassification of electronic messages in a spam filtering system |
| US7660865B2 (en)* | 2004-08-12 | 2010-02-09 | Microsoft Corporation | Spam filtering with probabilistic secure hashes |
| US7933985B2 (en) | 2004-08-13 | 2011-04-26 | Sipera Systems, Inc. | System and method for detecting and preventing denial of service attacks in a communications system |
| US20060047794A1 (en) | 2004-09-02 | 2006-03-02 | Microsoft Corporation | Application of genetic algorithms to computer system tuning |
| US8010460B2 (en) | 2004-09-02 | 2011-08-30 | Linkedin Corporation | Method and system for reputation evaluation of online users in a social networking scheme |
| US20060095404A1 (en) | 2004-10-29 | 2006-05-04 | The Go Daddy Group, Inc | Presenting search engine results based on domain name related reputation |
| US20060095966A1 (en)* | 2004-11-03 | 2006-05-04 | Shawn Park | Method of detecting, comparing, blocking, and eliminating spam emails |
| US7574409B2 (en)* | 2004-11-04 | 2009-08-11 | Vericept Corporation | Method, apparatus, and system for clustering and classification |
| US20060168017A1 (en)* | 2004-11-30 | 2006-07-27 | Microsoft Corporation | Dynamic spam trap accounts |
| US20060123083A1 (en) | 2004-12-03 | 2006-06-08 | Xerox Corporation | Adaptive spam message detector |
| US20060149820A1 (en)* | 2005-01-04 | 2006-07-06 | International Business Machines Corporation | Detecting spam e-mail using similarity calculations |
| US20060230039A1 (en) | 2005-01-25 | 2006-10-12 | Markmonitor, Inc. | Online identity tracking |
| CA2600344A1 (en) | 2005-03-02 | 2006-09-08 | Markmonitor Inc. | Distribution of trust data |
| US7822620B2 (en) | 2005-05-03 | 2010-10-26 | Mcafee, Inc. | Determining website reputations using automatic testing |
| US20060259551A1 (en)* | 2005-05-12 | 2006-11-16 | Idalis Software | Detection of unsolicited electronic messages |
| WO2009003059A1 (en)* | 2007-06-25 | 2008-12-31 | Google Inc. | Zero-hour quarantine of suspect electronic messages |
| US20090083413A1 (en)* | 2007-09-24 | 2009-03-26 | Levow Zachary S | Distributed frequency data collection via DNS |
| US8364766B2 (en)* | 2008-12-04 | 2013-01-29 | Yahoo! Inc. | Spam filtering based on statistics and token frequency modeling |
- 2003
- 2003-09-04USUS10/654,771patent/US20040073617A1/ennot_activeAbandoned
- 2008
- 2008-10-01USUS12/243,785patent/US20090031129A1/ennot_activeAbandoned
- 2008-10-01USUS12/243,778patent/US20090031136A1/ennot_activeAbandoned
- 2008-10-09USUS12/248,790patent/US8204945B2/ennot_activeExpired - Fee Related
- 2008-10-10USUS12/249,823patent/US20090158046A1/ennot_activeAbandoned
- 2008-10-10USUS12/249,804patent/US20090313339A1/ennot_activeAbandoned
- 2008-10-10USUS12/249,832patent/US20090182867A1/ennot_activeAbandoned
- 2008-10-10USUS12/249,803patent/US20090158435A1/ennot_activeAbandoned
- 2010
- 2010-04-18USUS12/762,365patent/US20100205672A1/ennot_activeAbandoned
- 2010-04-18USUS12/762,366patent/US20100205670A1/ennot_activeAbandoned
- 2010-04-18USUS12/762,367patent/US8272060B2/ennot_activeExpired - Fee Related
- 2010-04-19USUS12/762,368patent/US20100205265A1/ennot_activeAbandoned
- 2012
- 2012-09-14USUS13/620,692patent/US20130014261A1/ennot_activeAbandoned
Patent Citations (100)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US4641274A (en)* | 1982-12-03 | 1987-02-03 | International Business Machines Corporation | Method for communicating changes made to text form a text processor to a remote host |
| US4996711A (en)* | 1989-06-21 | 1991-02-26 | Chaum David L | Selected-exponent signature systems |
| US5495610A (en)* | 1989-11-30 | 1996-02-27 | Seer Technologies, Inc. | Software distribution system to build and distribute a software release |
| US5386470A (en)* | 1989-12-06 | 1995-01-31 | 3Com Ireland | Repeaters for secure local area networks |
| US5388189A (en)* | 1989-12-06 | 1995-02-07 | Racal-Datacom, Inc. | Alarm filter in an expert system for communications network |
| US5276736A (en)* | 1990-01-29 | 1994-01-04 | David Chaum | Optionally moderated transaction systems |
| US5276869A (en)* | 1990-09-10 | 1994-01-04 | International Business Machines Corporation | System for selecting document recipients as determined by technical content of document and for electronically corroborating receipt of document |
| US5379374A (en)* | 1990-11-21 | 1995-01-03 | Hitachi, Ltd. | Collaborative information processing system and workstation |
| US5283887A (en)* | 1990-12-19 | 1994-02-01 | Bull Hn Information Systems Inc. | Automatic document format conversion in an electronic mail system based upon user preference |
| US5379340A (en)* | 1991-08-02 | 1995-01-03 | Betterprize Limited | Text communication system |
| US5276901A (en)* | 1991-12-16 | 1994-01-04 | International Business Machines Corporation | System for controlling group access to objects using group access control folder and group identification as individual user |
| US5280527A (en)* | 1992-04-14 | 1994-01-18 | Kamahira Safe Co., Inc. | Biometric token for authorizing access to a host system |
| US5276735A (en)* | 1992-04-17 | 1994-01-04 | Secure Computing Corporation | Data enclave and trusted path system |
| US5276737A (en)* | 1992-04-20 | 1994-01-04 | Silvio Micali | Fair cryptosystems and methods of use |
| US5276737B1 (en)* | 1992-04-20 | 1995-09-12 | Silvio Micali | Fair cryptosystems and methods of use |
| US5485409A (en)* | 1992-04-30 | 1996-01-16 | International Business Machines Corporation | Automated penetration analysis system and method |
| US5278901A (en)* | 1992-04-30 | 1994-01-11 | International Business Machines Corporation | Pattern-oriented intrusion-detection system and method |
| US5483466A (en)* | 1992-11-13 | 1996-01-09 | Hitachi, Ltd. | Client/server system and mail reception/display control method |
| US6014651A (en)* | 1993-11-04 | 2000-01-11 | Crawford; Christopher M. | Commercial online software distribution systems and methods using encryption for security |
| US5606668A (en)* | 1993-12-15 | 1997-02-25 | Checkpoint Software Technologies Ltd. | System for securing inbound and outbound data packet flow in a computer network |
| US5491750A (en)* | 1993-12-30 | 1996-02-13 | International Business Machines Corporation | Method and apparatus for three-party entity authentication and key distribution using message authentication codes |
| US5857022A (en)* | 1994-01-13 | 1999-01-05 | Certco Llc | Enhanced cryptographic system and method with key escrow feature |
| US5872849A (en)* | 1994-01-13 | 1999-02-16 | Certco Llc | Enhanced cryptographic system and method with key escrow feature |
| US5481613A (en)* | 1994-04-15 | 1996-01-02 | Northern Telecom Limited | Computer network cryptographic key distribution system |
| US5485460A (en)* | 1994-08-19 | 1996-01-16 | Microsoft Corporation | System and method for running multiple incompatible network protocol stacks |
| US5604490A (en)* | 1994-09-09 | 1997-02-18 | International Business Machines Corporation | Method and system for providing a user access to multiple secured subsystems |
| US5481312A (en)* | 1994-09-12 | 1996-01-02 | At&T Corp. | Method of and apparatus for the transmission of high and low priority segments of a video bitstream over packet networks |
| US5864683A (en)* | 1994-10-12 | 1999-01-26 | Secure Computing Corporartion | System for providing secure internetwork by connecting type enforcing secure computers to external network for limiting access to data based on user and process access rights |
| US5710883A (en)* | 1995-03-10 | 1998-01-20 | Stanford University | Hypertext document transport mechanism for firewall-compatible distributed world-wide web publishing |
| US5864667A (en)* | 1995-04-05 | 1999-01-26 | Diversinet Corp. | Method for safe communications |
| US5708826A (en)* | 1995-05-16 | 1998-01-13 | Fujitsu Limited | Apparatus and method for converting presentation data |
| US5708780A (en)* | 1995-06-07 | 1998-01-13 | Open Market, Inc. | Internet server access control and monitoring systems |
| US5706507A (en)* | 1995-07-05 | 1998-01-06 | International Business Machines Corporation | System and method for controlling access to data located on a content server |
| US5859966A (en)* | 1995-10-10 | 1999-01-12 | Data General Corporation | Security system for computer systems |
| US5717758A (en)* | 1995-11-02 | 1998-02-10 | Micall; Silvio | Witness-based certificate revocation system |
| US5706442A (en)* | 1995-12-20 | 1998-01-06 | Block Financial Corporation | System for on-line financial services using distributed objects |
| US5602918A (en)* | 1995-12-22 | 1997-02-11 | Virtual Open Network Environment Corp. | Application level security system and method |
| US5862325A (en)* | 1996-02-29 | 1999-01-19 | Intermind Corporation | Computer-based communication system and method using metadata defining a control structure |
| US5864852A (en)* | 1996-04-26 | 1999-01-26 | Netscape Communications Corporation | Proxy server caching mechanism that provides a file directory structure and a mapping mechanism within the file directory structure |
| US6178509B1 (en)* | 1996-06-13 | 2001-01-23 | Intel Corporation | Tamper resistant methods and apparatus |
| US5872931A (en)* | 1996-08-13 | 1999-02-16 | Veritas Software, Corp. | Management agent automatically executes corrective scripts in accordance with occurrences of specified events regardless of conditions of management interface and management engine |
| US5717757A (en)* | 1996-08-29 | 1998-02-10 | Micali; Silvio | Certificate issue lists |
| US6012144A (en)* | 1996-10-08 | 2000-01-04 | Pickett; Thomas E. | Transaction security method and apparatus |
| US6192407B1 (en)* | 1996-10-24 | 2001-02-20 | Tumbleweed Communications Corp. | Private, trackable URLs for directed document delivery |
| US5872844A (en)* | 1996-11-18 | 1999-02-16 | Microsoft Corporation | System and method for detecting fraudulent expenditure of transferable electronic assets |
| US6178242B1 (en)* | 1997-02-07 | 2001-01-23 | Nds Limited | Digital recording protection system |
| US6185682B1 (en)* | 1997-06-03 | 2001-02-06 | U.S. Philips Corporation | Authentication system |
| US6185678B1 (en)* | 1997-10-02 | 2001-02-06 | Trustees Of The University Of Pennsylvania | Secure and reliable bootstrap architecture |
| US6021510A (en)* | 1997-11-24 | 2000-02-01 | Symantec Corporation | Antivirus accelerator |
| US5860068A (en)* | 1997-12-04 | 1999-01-12 | Petabyte Corporation | Method and system for custom manufacture and delivery of a data product |
| US6023723A (en)* | 1997-12-22 | 2000-02-08 | Accepted Marketing, Inc. | Method and system for filtering unwanted junk e-mail utilizing a plurality of filtering mechanisms |
| US6029256A (en)* | 1997-12-31 | 2000-02-22 | Network Associates, Inc. | Method and system for allowing computer programs easy access to features of a virus scanning engine |
| US20020016826A1 (en)* | 1998-02-07 | 2002-02-07 | Olof Johansson | Firewall apparatus and method of controlling network data packet traffic between internal and external networks |
| US6026414A (en)* | 1998-03-05 | 2000-02-15 | International Business Machines Corporation | System including a proxy client to backup files in a distributed computing environment |
| US6182226B1 (en)* | 1998-03-18 | 2001-01-30 | Secure Computing Corporation | System and method for controlling interactions between networks |
| US20020026591A1 (en)* | 1998-06-15 | 2002-02-28 | Hartley Bruce V. | Method and apparatus for assessing the security of a computer system |
| US6192360B1 (en)* | 1998-06-23 | 2001-02-20 | Microsoft Corporation | Methods and apparatus for classifying text and for building a text classifier |
| US6185689B1 (en)* | 1998-06-24 | 2001-02-06 | Richard S. Carson & Assoc., Inc. | Method for network self security assessment |
| US6182142B1 (en)* | 1998-07-10 | 2001-01-30 | Encommerce, Inc. | Distributed access management of information resources |
| US6338141B1 (en)* | 1998-09-30 | 2002-01-08 | Cybersoft, Inc. | Method and apparatus for computer virus detection, analysis, and removal in real time |
| US6507851B1 (en)* | 1998-12-03 | 2003-01-14 | Sony Corporation | Customer information retrieving method, a customer information retrieving apparatus, a data preparation method, and a database |
| US6341369B1 (en)* | 1998-12-03 | 2002-01-22 | International Business Machines Corporation | Method and data processing system for specifying and applying rules to classification-based decision points in an application system |
| US6510466B1 (en)* | 1998-12-14 | 2003-01-21 | International Business Machines Corporation | Methods, systems and computer program products for centralized management of application programs on a network |
| US20030023695A1 (en)* | 1999-02-26 | 2003-01-30 | Atabok Japan, Inc. | Modifying an electronic mail system to produce a secure delivery system |
| US6681331B1 (en)* | 1999-05-11 | 2004-01-20 | Cylant, Inc. | Dynamic software system intrusion detection |
| US6510431B1 (en)* | 1999-06-28 | 2003-01-21 | International Business Machines Corporation | Method and system for the routing of requests using an automated classification and profile matching in a networked environment |
| US6675153B1 (en)* | 1999-07-06 | 2004-01-06 | Zix Corporation | Transaction authorization system |
| US6675209B1 (en)* | 1999-07-19 | 2004-01-06 | Hewlett-Packard Development Company, L.P. | Method and system for assigning priority among network segments |
| US6845449B1 (en)* | 1999-07-23 | 2005-01-18 | Networks Associates Technology, Inc. | System and method for fast nested message authentication codes and error correction codes |
| US6842860B1 (en)* | 1999-07-23 | 2005-01-11 | Networks Associates Technology, Inc. | System and method for selectively authenticating data |
| US6684335B1 (en)* | 1999-08-19 | 2004-01-27 | Epstein, Iii Edwin A. | Resistance cell architecture |
| US6510464B1 (en)* | 1999-12-14 | 2003-01-21 | Verizon Corporate Services Group Inc. | Secure gateway having routing feature |
| US20020016910A1 (en)* | 2000-02-11 | 2002-02-07 | Wright Robert P. | Method for secure distribution of documents over electronic networks |
| US7159237B2 (en)* | 2000-03-16 | 2007-01-02 | Counterpane Internet Security, Inc. | Method and system for dynamic network intrusion monitoring, detection and response |
| US6842861B1 (en)* | 2000-03-24 | 2005-01-11 | Networks Associates Technology, Inc. | Method and system for detecting viruses on handheld computers |
| US20020001384A1 (en)* | 2000-04-13 | 2002-01-03 | Broadcom Corporation | Authentication engine architecture and method |
| US20020019945A1 (en)* | 2000-04-28 | 2002-02-14 | Internet Security System, Inc. | System and method for managing security events on a network |
| US20020023140A1 (en)* | 2000-06-08 | 2002-02-21 | Hile John K. | Electronic document delivery system |
| US6985923B1 (en)* | 2000-06-13 | 2006-01-10 | International Business Machines Corporation | Method, article of manufacture and apparatus for processing redundant electronic mail messages |
| US20020004902A1 (en)* | 2000-07-07 | 2002-01-10 | Eng-Whatt Toh | Secure and reliable document delivery |
| US20030023873A1 (en)* | 2001-03-16 | 2003-01-30 | Yuval Ben-Itzhak | Application-layer security method and system |
| US20030009696A1 (en)* | 2001-05-18 | 2003-01-09 | Bunker V. Nelson Waldo | Network security testing |
| US20030004689A1 (en)* | 2001-06-13 | 2003-01-02 | Gupta Ramesh M. | Hierarchy-based method and apparatus for detecting attacks on a computer system |
| US20030014662A1 (en)* | 2001-06-13 | 2003-01-16 | Gupta Ramesh M. | Protocol-parsing state machine and method of using same |
| US20030004688A1 (en)* | 2001-06-13 | 2003-01-02 | Gupta Ramesh M. | Virtual intrusion detection system and method of using same |
| US20030009699A1 (en)* | 2001-06-13 | 2003-01-09 | Gupta Ramesh M. | Method and apparatus for detecting intrusions on a computer system |
| US20030005326A1 (en)* | 2001-06-29 | 2003-01-02 | Todd Flemming | Method and system for implementing a security application services provider |
| US20030014664A1 (en)* | 2001-06-29 | 2003-01-16 | Daavid Hentunen | Intrusion detection method and system |
| US20030009554A1 (en)* | 2001-07-09 | 2003-01-09 | Burch Hal Joseph | Method and apparatus for tracing packets in a communications network |
| US20030009693A1 (en)* | 2001-07-09 | 2003-01-09 | International Business Machines Corporation | Dynamic intrusion detection for computer systems |
| US20030023874A1 (en)* | 2001-07-16 | 2003-01-30 | Rudy Prokupets | System for integrating security and access for facilities and information systems |
| US20030023875A1 (en)* | 2001-07-26 | 2003-01-30 | Hursey Neil John | Detecting e-mail propagated malware |
| US20030021280A1 (en)* | 2001-07-26 | 2003-01-30 | Makinson Graham Arthur | Malware scanning using a network bridge |
| US20030023692A1 (en)* | 2001-07-27 | 2003-01-30 | Fujitsu Limited | Electronic message delivery system, electronic message delivery managment server, and recording medium in which electronic message delivery management program is recorded |
| US6993660B1 (en)* | 2001-08-03 | 2006-01-31 | Mcafee, Inc. | System and method for performing efficient computer virus scanning of transient messages using checksums in a distributed computing environment |
| US20040015554A1 (en)* | 2002-07-16 | 2004-01-22 | Brian Wilson | Active e-mail filter with challenge-response |
| US6847888B2 (en)* | 2002-08-07 | 2005-01-25 | Hrl Laboratories, Llc | Method and apparatus for geographic shape preservation for identification |
| US20050021738A1 (en)* | 2002-11-12 | 2005-01-27 | Kenneth Goeller | Network geo-location system |
| US20050021736A1 (en)* | 2003-01-07 | 2005-01-27 | International Business Machines Corporation | Method and system for monitoring performance of distributed applications |
| US20050014749A1 (en)* | 2003-06-20 | 2005-01-20 | Amgen Inc. | Piperazine derivatives and methods of use |
Cited By (468)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US7302698B1 (en) | 1999-09-17 | 2007-11-27 | Hewlett-Packard Development Company, L.P. | Operation of trusted state in computing platform |
| US7788329B2 (en) | 2000-05-16 | 2010-08-31 | Aol Inc. | Throttling electronic communications from one or more senders |
| US7877799B2 (en) | 2000-08-18 | 2011-01-25 | Hewlett-Packard Development Company, L.P. | Performance of a service on a computing platform |
| US9633206B2 (en) | 2000-11-28 | 2017-04-25 | Hewlett-Packard Development Company, L.P. | Demonstrating integrity of a compartment of a compartmented operating system |
| US20020194493A1 (en)* | 2000-11-28 | 2002-12-19 | Hewlett-Packard Company | Demonstrating integrity of a compartment of a compartmented operating system |
| US20030149895A1 (en)* | 2001-01-31 | 2003-08-07 | Choo Tse Huong | Trusted gateway system |
| US20020122543A1 (en)* | 2001-02-12 | 2002-09-05 | Rowen Chris E. | System and method of indexing unique electronic mail messages and uses for the same |
| US20020124052A1 (en)* | 2001-02-17 | 2002-09-05 | Richard Brown | Secure e-mail handling using a compartmented operating system |
| US20020120575A1 (en)* | 2001-02-23 | 2002-08-29 | Hewlett-Packard Company | Method of and apparatus for ascertaining the status of a data processing environment |
| US8218765B2 (en) | 2001-02-23 | 2012-07-10 | Hewlett-Packard Development Company, L.P. | Information system |
| US8219496B2 (en) | 2001-02-23 | 2012-07-10 | Hewlett-Packard Development Company, L.P. | Method of and apparatus for ascertaining the status of a data processing environment |
| US20020194241A1 (en)* | 2001-06-19 | 2002-12-19 | Jonathan Griffin | Performing secure and insecure computing operations in a compartmented operating system |
| US7159210B2 (en) | 2001-06-19 | 2007-01-02 | Hewlett-Packard Development Company, L.P. | Performing secure and insecure computing operations in a compartmented operating system |
| US7076655B2 (en) | 2001-06-19 | 2006-07-11 | Hewlett-Packard Development Company, L.P. | Multiple trusted computing environments with verifiable environment identities |
| US8056131B2 (en)* | 2001-06-21 | 2011-11-08 | Cybersoft, Inc. | Apparatus, methods and articles of manufacture for intercepting, examining and controlling code, data and files and their transfer |
| US20040199773A1 (en)* | 2001-06-21 | 2004-10-07 | Radatti Peter V. | Apparatus, methods and articles of manufacture for intercepting, examining and controlling code, data and files and their transfer |
| US20030023875A1 (en)* | 2001-07-26 | 2003-01-30 | Hursey Neil John | Detecting e-mail propagated malware |
| US7673342B2 (en)* | 2001-07-26 | 2010-03-02 | Mcafee, Inc. | Detecting e-mail propagated malware |
| US7979907B2 (en)* | 2001-07-30 | 2011-07-12 | The Trustees Of Columbia University In The City Of New York | Systems and methods for detection of new malicious executables |
| US20090254992A1 (en)* | 2001-07-30 | 2009-10-08 | Schultz Matthew G | Systems and methods for detection of new malicious executables |
| US20030079140A1 (en)* | 2001-10-24 | 2003-04-24 | Yosuke Ura | Multiple protecting system to protect personal computer data from burglary utilized flash memory drive |
| US20030084323A1 (en)* | 2001-10-31 | 2003-05-01 | Gales George S. | Network intrusion detection system and method |
| US20050022014A1 (en)* | 2001-11-21 | 2005-01-27 | Shipman Robert A | Computer security system |
| US7774845B2 (en)* | 2001-11-21 | 2010-08-10 | British Telecommunications Public Limited Company | Computer security system |
| US20050223221A1 (en)* | 2001-11-22 | 2005-10-06 | Proudler Graeme J | Apparatus and method for creating a trusted environment |
| US7467370B2 (en) | 2001-11-22 | 2008-12-16 | Hewlett-Packard Development Company, L.P. | Apparatus and method for creating a trusted environment |
| US20070083606A1 (en)* | 2001-12-05 | 2007-04-12 | Bellsouth Intellectual Property Corporation | Foreign Network Spam Blocker |
| US8090778B2 (en) | 2001-12-05 | 2012-01-03 | At&T Intellectual Property I, L.P. | Foreign network SPAM blocker |
| US20040003283A1 (en)* | 2002-06-26 | 2004-01-01 | Goodman Joshua Theodore | Spam detector with challenges |
| US8046832B2 (en) | 2002-06-26 | 2011-10-25 | Microsoft Corporation | Spam detector with challenges |
| US8732245B2 (en)* | 2002-12-03 | 2014-05-20 | Blackberry Limited | Method, system and computer software product for pre-selecting a folder for a message |
| US20060026236A1 (en)* | 2002-12-03 | 2006-02-02 | Research In Motion Limited | Method, system and computer software product for pre-selecting a folder for a message |
| US20040111531A1 (en)* | 2002-12-06 | 2004-06-10 | Stuart Staniford | Method and system for reducing the rate of infection of a communications network by a software worm |
| US7219131B2 (en) | 2003-01-16 | 2007-05-15 | Ironport Systems, Inc. | Electronic message delivery using an alternate source approach |
| US20040199595A1 (en)* | 2003-01-16 | 2004-10-07 | Scott Banister | Electronic message delivery using a virtual gateway approach |
| US8904490B2 (en) | 2003-01-23 | 2014-12-02 | Unspam, Llc | Method and apparatus for a non-revealing do-not-contact list system |
| US7461263B2 (en)* | 2003-01-23 | 2008-12-02 | Unspam, Llc. | Method and apparatus for a non-revealing do-not-contact list system |
| US20040148506A1 (en)* | 2003-01-23 | 2004-07-29 | Prince Matthew B. | Method and apparatus for a non-revealing do-not-contact list system |
| US9699125B2 (en) | 2003-01-23 | 2017-07-04 | Unspam, Llc | Method and apparatus for a non-revealing do-not-contact list system |
| US20090055895A1 (en)* | 2003-01-23 | 2009-02-26 | Prince Matthew B | Method and Apparatus for a Non-Revealing Do-Not-Contact List System |
| US7941842B2 (en) | 2003-01-23 | 2011-05-10 | Unspam, Llc. | Method and apparatus for a non-revealing do-not-contact list system |
| US20040167964A1 (en)* | 2003-02-25 | 2004-08-26 | Rounthwaite Robert L. | Adaptive junk message filtering system |
| US7249162B2 (en) | 2003-02-25 | 2007-07-24 | Microsoft Corporation | Adaptive junk message filtering system |
| US20040177110A1 (en)* | 2003-03-03 | 2004-09-09 | Rounthwaite Robert L. | Feedback loop for spam prevention |
| US20040215977A1 (en)* | 2003-03-03 | 2004-10-28 | Goodman Joshua T. | Intelligent quarantining for spam prevention |
| US7558832B2 (en) | 2003-03-03 | 2009-07-07 | Microsoft Corporation | Feedback loop for spam prevention |
| US7543053B2 (en) | 2003-03-03 | 2009-06-02 | Microsoft Corporation | Intelligent quarantining for spam prevention |
| JP2006521622A (en)* | 2003-03-25 | 2006-09-21 | ベリサイン・インコーポレイテッド | Control and management of electronic messages |
| US10462084B2 (en) | 2003-03-25 | 2019-10-29 | Verisign, Inc. | Control and management of electronic messaging via authentication and evaluation of credentials |
| WO2004088455A3 (en)* | 2003-03-25 | 2005-12-15 | Verisign Inc | Control and management of electronic messaging |
| US20100306836A1 (en)* | 2003-03-25 | 2010-12-02 | Verisign, Inc. | Control and Management of Electronic Messaging |
| US20040205135A1 (en)* | 2003-03-25 | 2004-10-14 | Hallam-Baker Phillip Martin | Control and management of electronic messaging |
| US8745146B2 (en) | 2003-03-25 | 2014-06-03 | Verisign, Inc. | Control and management of electronic messaging |
| US9083695B2 (en) | 2003-03-25 | 2015-07-14 | Verisign, Inc. | Control and management of electronic messaging |
| US8103732B2 (en)* | 2003-03-25 | 2012-01-24 | Verisign, Inc. | Methods for control and management of electronic messaging based on sender information |
| US7676546B2 (en)* | 2003-03-25 | 2010-03-09 | Verisign, Inc. | Control and management of electronic messaging |
| US20060168059A1 (en)* | 2003-03-31 | 2006-07-27 | Affini, Inc. | System and method for providing filtering email messages |
| US8606860B2 (en)* | 2003-03-31 | 2013-12-10 | Affini, Inc. | System and method for providing filtering email messages |
| US7680886B1 (en) | 2003-04-09 | 2010-03-16 | Symantec Corporation | Suppressing spam using a machine learning based spam filter |
| US7650382B1 (en) | 2003-04-24 | 2010-01-19 | Symantec Corporation | Detecting spam e-mail with backup e-mail server traps |
| US7739494B1 (en) | 2003-04-25 | 2010-06-15 | Symantec Corporation | SSL validation and stripping using trustworthiness factors |
| US7366919B1 (en) | 2003-04-25 | 2008-04-29 | Symantec Corporation | Use of geo-location data for spam detection |
| US20100088380A1 (en)* | 2003-05-02 | 2010-04-08 | Microsoft Corporation | Message rendering for identification of content features |
| US7483947B2 (en)* | 2003-05-02 | 2009-01-27 | Microsoft Corporation | Message rendering for identification of content features |
| US8250159B2 (en) | 2003-05-02 | 2012-08-21 | Microsoft Corporation | Message rendering for identification of content features |
| US20040221062A1 (en)* | 2003-05-02 | 2004-11-04 | Starbuck Bryan T. | Message rendering for identification of content features |
| US20110055343A1 (en)* | 2003-05-15 | 2011-03-03 | Symantec Corporation | Method and apparatus for filtering email spam using email noise reduction |
| US20050108339A1 (en)* | 2003-05-15 | 2005-05-19 | Matt Gleeson | Method and apparatus for filtering email spam using email noise reduction |
| US8402102B2 (en) | 2003-05-15 | 2013-03-19 | Symantec Corporation | Method and apparatus for filtering email spam using email noise reduction |
| US7831667B2 (en)* | 2003-05-15 | 2010-11-09 | Symantec Corporation | Method and apparatus for filtering email spam using email noise reduction |
| US7293063B1 (en) | 2003-06-04 | 2007-11-06 | Symantec Corporation | System utilizing updated spam signatures for performing secondary signature-based analysis of a held e-mail to improve spam email detection |
| US7272853B2 (en) | 2003-06-04 | 2007-09-18 | Microsoft Corporation | Origination/destination features and lists for spam prevention |
| US7464264B2 (en) | 2003-06-04 | 2008-12-09 | Microsoft Corporation | Training filters for detecting spasm based on IP addresses and text-related features |
| US7665131B2 (en) | 2003-06-04 | 2010-02-16 | Microsoft Corporation | Origination/destination features and lists for spam prevention |
| US20040260922A1 (en)* | 2003-06-04 | 2004-12-23 | Goodman Joshua T. | Training filters for IP address and URL learning |
| US7409708B2 (en) | 2003-06-04 | 2008-08-05 | Microsoft Corporation | Advanced URL and IP features |
| US20070118904A1 (en)* | 2003-06-04 | 2007-05-24 | Microsoft Corporation | Origination/destination features and lists for spam prevention |
| US20050022008A1 (en)* | 2003-06-04 | 2005-01-27 | Goodman Joshua T. | Origination/destination features and lists for spam prevention |
| US7287060B1 (en)* | 2003-06-12 | 2007-10-23 | Storage Technology Corporation | System and method for rating unsolicited e-mail |
| US8145710B2 (en) | 2003-06-18 | 2012-03-27 | Symantec Corporation | System and method for filtering spam messages utilizing URL filtering module |
| US7519668B2 (en) | 2003-06-20 | 2009-04-14 | Microsoft Corporation | Obfuscation of spam filter |
| US20050021649A1 (en)* | 2003-06-20 | 2005-01-27 | Goodman Joshua T. | Prevention of outgoing spam |
| US20050015454A1 (en)* | 2003-06-20 | 2005-01-20 | Goodman Joshua T. | Obfuscation of spam filter |
| US7711779B2 (en) | 2003-06-20 | 2010-05-04 | Microsoft Corporation | Prevention of outgoing spam |
| US20040260776A1 (en)* | 2003-06-23 | 2004-12-23 | Starbuck Bryan T. | Advanced spam detection techniques |
| US8533270B2 (en) | 2003-06-23 | 2013-09-10 | Microsoft Corporation | Advanced spam detection techniques |
| US9305079B2 (en) | 2003-06-23 | 2016-04-05 | Microsoft Technology Licensing, Llc | Advanced spam detection techniques |
| US20070198642A1 (en)* | 2003-06-30 | 2007-08-23 | Bellsouth Intellectual Property Corporation | Filtering Email Messages Corresponding to Undesirable Domains |
| US7506031B2 (en) | 2003-06-30 | 2009-03-17 | At&T Intellectual Property I, L.P. | Filtering email messages corresponding to undesirable domains |
| US7844678B2 (en) | 2003-06-30 | 2010-11-30 | At&T Intellectual Property I, L.P. | Filtering email messages corresponding to undesirable domains |
| US8892673B1 (en)* | 2003-08-08 | 2014-11-18 | Radix Holdings, Llc | Hybrid challenge-response |
| US20090158429A1 (en)* | 2003-09-19 | 2009-06-18 | Marshall Van Alstyne | Methods and systems for enabling analysis of communication content while preserving confidentiality |
| US7203964B1 (en)* | 2003-10-07 | 2007-04-10 | Elmer V. Pass | Method of stopping internet viruses |
| US7949718B2 (en) | 2003-10-14 | 2011-05-24 | At&T Intellectual Property I, L.P. | Phonetic filtering of undesired email messages |
| US7664812B2 (en)* | 2003-10-14 | 2010-02-16 | At&T Intellectual Property I, L.P. | Phonetic filtering of undesired email messages |
| US20050080860A1 (en)* | 2003-10-14 | 2005-04-14 | Daniell W. Todd | Phonetic filtering of undesired email messages |
| US20050080889A1 (en)* | 2003-10-14 | 2005-04-14 | Malik Dale W. | Child protection from harmful email |
| US20050080642A1 (en)* | 2003-10-14 | 2005-04-14 | Daniell W. Todd | Consolidated email filtering user interface |
| US7930351B2 (en)* | 2003-10-14 | 2011-04-19 | At&T Intellectual Property I, L.P. | Identifying undesired email messages having attachments |
| US20050091321A1 (en)* | 2003-10-14 | 2005-04-28 | Daniell W. T. | Identifying undesired email messages having attachments |
| US20050097174A1 (en)* | 2003-10-14 | 2005-05-05 | Daniell W. T. | Filtered email differentiation |
| US20100077051A1 (en)* | 2003-10-14 | 2010-03-25 | At&T Intellectual Property I, L.P. | Phonetic Filtering of Undesired Email Messages |
| US7921159B1 (en) | 2003-10-14 | 2011-04-05 | Symantec Corporation | Countering spam that uses disguised characters |
| US7451184B2 (en) | 2003-10-14 | 2008-11-11 | At&T Intellectual Property I, L.P. | Child protection from harmful email |
| US7610341B2 (en) | 2003-10-14 | 2009-10-27 | At&T Intellectual Property I, L.P. | Filtered email differentiation |
| US7548956B1 (en)* | 2003-12-30 | 2009-06-16 | Aol Llc | Spam control based on sender account characteristics |
| US20050154601A1 (en)* | 2004-01-09 | 2005-07-14 | Halpern Joshua I. | Information security threat identification, analysis, and management |
| US20050188032A1 (en)* | 2004-01-14 | 2005-08-25 | Katsuyuki Yamazaki | Mass mail detection system and mail server |
| US7853654B2 (en)* | 2004-01-14 | 2010-12-14 | Kddi Corporation | Mass mail detection system and mail server |
| US8301702B2 (en)* | 2004-01-20 | 2012-10-30 | Cloudmark, Inc. | Method and an apparatus to screen electronic communications |
| US20050198289A1 (en)* | 2004-01-20 | 2005-09-08 | Prakash Vipul V. | Method and an apparatus to screen electronic communications |
| US20110238770A1 (en)* | 2004-01-20 | 2011-09-29 | Cloudmark, Inc. | Method and apparatus to screen electronic communications |
| US20060123476A1 (en)* | 2004-02-12 | 2006-06-08 | Karim Yaghmour | System and method for warranting electronic mail using a hybrid public key encryption scheme |
| US7653695B2 (en) | 2004-02-17 | 2010-01-26 | Ironport Systems, Inc. | Collecting, aggregating, and managing information relating to electronic messages |
| US20050193073A1 (en)* | 2004-03-01 | 2005-09-01 | Mehr John D. | (More) advanced spam detection features |
| US8214438B2 (en) | 2004-03-01 | 2012-07-03 | Microsoft Corporation | (More) advanced spam detection features |
| US20100106677A1 (en)* | 2004-03-09 | 2010-04-29 | Gozoom.Com, Inc. | Email analysis using fuzzy matching of text |
| US8515894B2 (en)* | 2004-03-09 | 2013-08-20 | Gozoom.Com, Inc. | Email analysis using fuzzy matching of text |
| US20050204005A1 (en)* | 2004-03-12 | 2005-09-15 | Purcell Sean E. | Selective treatment of messages based on junk rating |
| US20050204006A1 (en)* | 2004-03-12 | 2005-09-15 | Purcell Sean E. | Message junk rating interface |
| US7966658B2 (en) | 2004-04-08 | 2011-06-21 | The Regents Of The University Of California | Detecting public network attacks using signatures and fast content analysis |
| US20050229254A1 (en)* | 2004-04-08 | 2005-10-13 | Sumeet Singh | Detecting public network attacks using signatures and fast content analysis |
| US20080307524A1 (en)* | 2004-04-08 | 2008-12-11 | The Regents Of The University Of California | Detecting Public Network Attacks Using Signatures and Fast Content Analysis |
| US8296842B2 (en) | 2004-04-08 | 2012-10-23 | The Regents Of The University Of California | Detecting public network attacks using signatures and fast content analysis |
| WO2005103899A1 (en)* | 2004-04-08 | 2005-11-03 | The Regents Of The University Of California | Detecting public network attacks using signatures and fast content analysis |
| US8171549B2 (en)* | 2004-04-26 | 2012-05-01 | Cybersoft, Inc. | Apparatus, methods and articles of manufacture for intercepting, examining and controlling code, data, files and their transfer |
| US20050240910A1 (en)* | 2004-04-26 | 2005-10-27 | Radatti Peter V | Apparatus, methods and articles of manufacture for intercepting, examining and controlling code, data, files and their transfer |
| US7941490B1 (en)* | 2004-05-11 | 2011-05-10 | Symantec Corporation | Method and apparatus for detecting spam in email messages and email attachments |
| US20060031314A1 (en)* | 2004-05-28 | 2006-02-09 | Robert Brahms | Techniques for determining the reputation of a message sender |
| US7756930B2 (en) | 2004-05-28 | 2010-07-13 | Ironport Systems, Inc. | Techniques for determining the reputation of a message sender |
| US20060101680A1 (en)* | 2004-05-28 | 2006-05-18 | Smith Michael J | Container contents identifier |
| WO2005119485A1 (en)* | 2004-05-29 | 2005-12-15 | Ironport Systems, Inc. | Method and apparatus for mail flow monitoring |
| US20060059238A1 (en)* | 2004-05-29 | 2006-03-16 | Slater Charles S | Monitoring the flow of messages received at a server |
| US20060010215A1 (en)* | 2004-05-29 | 2006-01-12 | Clegg Paul J | Managing connections and messages at a server by associating different actions for both different senders and different recipients |
| US8166310B2 (en) | 2004-05-29 | 2012-04-24 | Ironport Systems, Inc. | Method and apparatus for providing temporary access to a network device |
| US20050265319A1 (en)* | 2004-05-29 | 2005-12-01 | Clegg Paul J | Method and apparatus for destination domain-based bounce profiles |
| US20060031359A1 (en)* | 2004-05-29 | 2006-02-09 | Clegg Paul J | Managing connections, messages, and directory harvest attacks at a server |
| US7917588B2 (en) | 2004-05-29 | 2011-03-29 | Ironport Systems, Inc. | Managing delivery of electronic messages using bounce profiles |
| US7849142B2 (en) | 2004-05-29 | 2010-12-07 | Ironport Systems, Inc. | Managing connections, messages, and directory harvest attacks at a server |
| US7873695B2 (en) | 2004-05-29 | 2011-01-18 | Ironport Systems, Inc. | Managing connections and messages at a server by associating different actions for both different senders and different recipients |
| WO2005119482A1 (en)* | 2004-05-29 | 2005-12-15 | Ironport Systems, Inc. | Method and apparatus for destination domain-based bounce profiles |
| US7870200B2 (en) | 2004-05-29 | 2011-01-11 | Ironport Systems, Inc. | Monitoring the flow of messages received at a server |
| US20110178962A1 (en)* | 2004-06-04 | 2011-07-21 | Messagemind, Inc. | System and method for dynamic adaptive user-based prioritization and display of electronic messages |
| US20060010217A1 (en)* | 2004-06-04 | 2006-01-12 | Business Instruments Corp. | System and method for dynamic adaptive user-based prioritization and display of electronic messages |
| US7941491B2 (en) | 2004-06-04 | 2011-05-10 | Messagemind, Inc. | System and method for dynamic adaptive user-based prioritization and display of electronic messages |
| US20050283837A1 (en)* | 2004-06-16 | 2005-12-22 | Michael Olivier | Method and apparatus for managing computer virus outbreaks |
| US7748038B2 (en) | 2004-06-16 | 2010-06-29 | Ironport Systems, Inc. | Method and apparatus for managing computer virus outbreaks |
| US7664819B2 (en) | 2004-06-29 | 2010-02-16 | Microsoft Corporation | Incremental anti-spam lookup and update service |
| GB2415854B (en)* | 2004-07-01 | 2006-12-27 | Ericsson Telefon Ab L M | Email spam reduction method |
| GB2415854A (en)* | 2004-07-01 | 2006-01-04 | Ericsson Telefon Ab L M | Email Spam reduction |
| US9516047B2 (en) | 2004-07-13 | 2016-12-06 | Dell Software Inc. | Time zero classification of messages |
| US8122508B2 (en)* | 2004-07-13 | 2012-02-21 | Sonicwall, Inc. | Analyzing traffic patterns to detect infectious messages |
| US10069851B2 (en) | 2004-07-13 | 2018-09-04 | Sonicwall Inc. | Managing infectious forwarded messages |
| US9325724B2 (en) | 2004-07-13 | 2016-04-26 | Dell Software Inc. | Time zero classification of messages |
| US10084801B2 (en) | 2004-07-13 | 2018-09-25 | Sonicwall Inc. | Time zero classification of messages |
| US9237163B2 (en) | 2004-07-13 | 2016-01-12 | Dell Software Inc. | Managing infectious forwarded messages |
| US8955136B2 (en) | 2004-07-13 | 2015-02-10 | Sonicwall, Inc. | Analyzing traffic patterns to detect infectious messages |
| US8955106B2 (en) | 2004-07-13 | 2015-02-10 | Sonicwall, Inc. | Managing infectious forwarded messages |
| US20080134336A1 (en)* | 2004-07-13 | 2008-06-05 | Mailfrontier, Inc. | Analyzing traffic patterns to detect infectious messages |
| US9154511B1 (en) | 2004-07-13 | 2015-10-06 | Dell Software Inc. | Time zero detection of infectious messages |
| US8850566B2 (en) | 2004-07-13 | 2014-09-30 | Sonicwall, Inc. | Time zero detection of infectious messages |
| US7904517B2 (en) | 2004-08-09 | 2011-03-08 | Microsoft Corporation | Challenge response systems |
| US20060031338A1 (en)* | 2004-08-09 | 2006-02-09 | Microsoft Corporation | Challenge response systems |
| US20060036695A1 (en)* | 2004-08-12 | 2006-02-16 | Rolnik Robert C | Timed delivery of alert notifications based on user set criteria |
| US7660865B2 (en)* | 2004-08-12 | 2010-02-09 | Microsoft Corporation | Spam filtering with probabilistic secure hashes |
| US20060036693A1 (en)* | 2004-08-12 | 2006-02-16 | Microsoft Corporation | Spam filtering with probabilistic secure hashes |
| US7490244B1 (en) | 2004-09-14 | 2009-02-10 | Symantec Corporation | Blocking e-mail propagation of suspected malicious computer code |
| US7555524B1 (en) | 2004-09-16 | 2009-06-30 | Symantec Corporation | Bulk electronic message detection by header similarity analysis |
| US8528084B1 (en) | 2004-09-30 | 2013-09-03 | Google Inc. | Systems and methods for detecting potential communications fraud |
| US8615802B1 (en) | 2004-09-30 | 2013-12-24 | Google Inc. | Systems and methods for detecting potential communications fraud |
| US8056128B1 (en)* | 2004-09-30 | 2011-11-08 | Google Inc. | Systems and methods for detecting potential communications fraud |
| US8495144B1 (en)* | 2004-10-06 | 2013-07-23 | Trend Micro Incorporated | Techniques for identifying spam e-mail |
| US7546349B1 (en) | 2004-11-01 | 2009-06-09 | Symantec Corporation | Automatic generation of disposable e-mail addresses |
| US7197539B1 (en) | 2004-11-01 | 2007-03-27 | Symantec Corporation | Automated disablement of disposable e-mail addresses based on user actions |
| WO2006048529A1 (en)* | 2004-11-02 | 2006-05-11 | Bruno Decarpigny | System and method for transmitting messages in an electronic messaging communication network, using a transmission filter |
| FR2877528A1 (en)* | 2004-11-02 | 2006-05-05 | Bruno Decarpigny | SYSTEM AND METHOD FOR SENDING MESSAGES IN AN ELECTRONIC MESSAGING COMMUNICATION NETWORK, BASED ON THE USE OF A SENDING FILTER |
| US20060095523A1 (en)* | 2004-11-02 | 2006-05-04 | Bruno Decarpigny | System and method for sending messages into a communications network by electronic mail, based on the use of a send filter |
| US20060161986A1 (en)* | 2004-11-09 | 2006-07-20 | Sumeet Singh | Method and apparatus for content classification |
| US7936682B2 (en) | 2004-11-09 | 2011-05-03 | Cisco Technology, Inc. | Detecting malicious attacks using network behavior and header analysis |
| US8010685B2 (en) | 2004-11-09 | 2011-08-30 | Cisco Technology, Inc. | Method and apparatus for content classification |
| US20060098585A1 (en)* | 2004-11-09 | 2006-05-11 | Cisco Technology, Inc. | Detecting malicious attacks using network behavior and header analysis |
| US20060161989A1 (en)* | 2004-12-13 | 2006-07-20 | Eran Reshef | System and method for deterring rogue users from attacking protected legitimate users |
| US20060168202A1 (en)* | 2004-12-13 | 2006-07-27 | Eran Reshef | System and method for deterring rogue users from attacking protected legitimate users |
| US7756933B2 (en) | 2004-12-13 | 2010-07-13 | Collactive Ltd. | System and method for deterring rogue users from attacking protected legitimate users |
| US7640590B1 (en) | 2004-12-21 | 2009-12-29 | Symantec Corporation | Presentation of network source and executable characteristics |
| US20060212523A1 (en)* | 2005-03-21 | 2006-09-21 | International Business Machines Corporation | Policy based control of multiple message forwards |
| US8539587B2 (en) | 2005-03-22 | 2013-09-17 | Hewlett-Packard Development Company, L.P. | Methods, devices and data structures for trusted data |
| US7975010B1 (en) | 2005-03-23 | 2011-07-05 | Symantec Corporation | Countering spam through address comparison |
| US20170041293A1 (en)* | 2005-04-22 | 2017-02-09 | Blue Coat Systems, Inc. | Methods and apparatus for blocking unwanted software downloads |
| US8001193B2 (en)* | 2005-05-17 | 2011-08-16 | Ntt Docomo, Inc. | Data communications system and data communications method for detecting unsolicited communications |
| US20060262867A1 (en)* | 2005-05-17 | 2006-11-23 | Ntt Docomo, Inc. | Data communications system and data communications method |
| US7757288B1 (en) | 2005-05-23 | 2010-07-13 | Symantec Corporation | Malicious e-mail attack inversion filter |
| US20080126951A1 (en)* | 2005-06-03 | 2008-05-29 | C-Mail Corp. | System and method of dynamically prioritized electronic mail graphical user interface, and measuring email productivity and collaboration trends |
| US8161122B2 (en) | 2005-06-03 | 2012-04-17 | Messagemind, Inc. | System and method of dynamically prioritized electronic mail graphical user interface, and measuring email productivity and collaboration trends |
| US20070038705A1 (en)* | 2005-07-29 | 2007-02-15 | Microsoft Corporation | Trees of classifiers for detecting email spam |
| US7930353B2 (en)* | 2005-07-29 | 2011-04-19 | Microsoft Corporation | Trees of classifiers for detecting email spam |
| US7856090B1 (en) | 2005-08-08 | 2010-12-21 | Symantec Corporation | Automatic spim detection |
| US8201254B1 (en) | 2005-08-30 | 2012-06-12 | Symantec Corporation | Detection of e-mail threat acceleration |
| US7617285B1 (en) | 2005-09-29 | 2009-11-10 | Symantec Corporation | Adaptive threshold based spam classification |
| US7912907B1 (en) | 2005-10-07 | 2011-03-22 | Symantec Corporation | Spam email detection based on n-grams with feature selection |
| US20070118759A1 (en)* | 2005-10-07 | 2007-05-24 | Sheppard Scott K | Undesirable email determination |
| US8065370B2 (en) | 2005-11-03 | 2011-11-22 | Microsoft Corporation | Proofs to filter spam |
| US20070118874A1 (en)* | 2005-11-18 | 2007-05-24 | Research In Motion Limited | System and method for handling electronic messages |
| US8191105B2 (en)* | 2005-11-18 | 2012-05-29 | Research In Motion Limited | System and method for handling electronic messages |
| US20070143848A1 (en)* | 2005-12-16 | 2007-06-21 | Kraemer Jeffrey A | Methods and apparatus providing computer and network security for polymorphic attacks |
| US9286469B2 (en) | 2005-12-16 | 2016-03-15 | Cisco Technology, Inc. | Methods and apparatus providing computer and network security utilizing probabilistic signature generation |
| US20070256127A1 (en)* | 2005-12-16 | 2007-11-01 | Kraemer Jeffrey A | Methods and apparatus providing computer and network security utilizing probabilistic signature generation |
| US20070143847A1 (en)* | 2005-12-16 | 2007-06-21 | Kraemer Jeffrey A | Methods and apparatus providing automatic signature generation and enforcement |
| US20100242111A1 (en)* | 2005-12-16 | 2010-09-23 | Kraemer Jeffrey A | Methods and apparatus providing computer and network security utilizing probabilistic policy reposturing |
| US8255995B2 (en) | 2005-12-16 | 2012-08-28 | Cisco Technology, Inc. | Methods and apparatus providing computer and network security utilizing probabilistic policy reposturing |
| US8413245B2 (en)* | 2005-12-16 | 2013-04-02 | Cisco Technology, Inc. | Methods and apparatus providing computer and network security for polymorphic attacks |
| US8495743B2 (en) | 2005-12-16 | 2013-07-23 | Cisco Technology, Inc. | Methods and apparatus providing automatic signature generation and enforcement |
| US7810160B2 (en) | 2005-12-28 | 2010-10-05 | Microsoft Corporation | Combining communication policies into common rules store |
| US20070150933A1 (en)* | 2005-12-28 | 2007-06-28 | Microsoft Corporation | Combining communication policies into common rules store |
| US8495037B1 (en)* | 2006-02-21 | 2013-07-23 | Symantec Operating Corporation | Efficient isolation of backup versions of data objects affected by malicious software |
| US20100077052A1 (en)* | 2006-03-09 | 2010-03-25 | Watchguard Technologies, Inc. | Method and system for recognizing desired email |
| US20070214220A1 (en)* | 2006-03-09 | 2007-09-13 | John Alsop | Method and system for recognizing desired email |
| US8572190B2 (en)* | 2006-03-09 | 2013-10-29 | Watchguard Technologies, Inc. | Method and system for recognizing desired email |
| US9576131B2 (en)* | 2006-04-06 | 2017-02-21 | Juniper Networks, Inc. | Malware detection system and method for mobile platforms |
| US20150347753A1 (en)* | 2006-04-06 | 2015-12-03 | Juniper Networks, Inc. | Malware detection system and method for mobile platforms |
| US20070282953A1 (en)* | 2006-05-31 | 2007-12-06 | Microsoft Corporation | Perimeter message filtering with extracted user-specific preferences |
| US8028026B2 (en)* | 2006-05-31 | 2011-09-27 | Microsoft Corporation | Perimeter message filtering with extracted user-specific preferences |
| US8332947B1 (en) | 2006-06-27 | 2012-12-11 | Symantec Corporation | Security threat reporting in light of local security tools |
| US20080033905A1 (en)* | 2006-08-05 | 2008-02-07 | Terry Lee Stokes | System and Method for the Capture and Archival of Electronic Communications |
| US20080059588A1 (en)* | 2006-09-01 | 2008-03-06 | Ratliff Emily J | Method and System for Providing Notification of Nefarious Remote Control of a Data Processing System |
| US20080059590A1 (en)* | 2006-09-05 | 2008-03-06 | Ecole Polytechnique Federale De Lausanne (Epfl) | Method to filter electronic messages in a message processing system |
| US7788576B1 (en)* | 2006-10-04 | 2010-08-31 | Trend Micro Incorporated | Grouping of documents that contain markup language code |
| US20080109448A1 (en)* | 2006-11-06 | 2008-05-08 | Messageone, Inc. | System and Method for Managing Data Across Multiple Environments |
| US10783498B2 (en)* | 2006-11-06 | 2020-09-22 | Messageone, Llc | System and method for managing data across multiple environments |
| US8677490B2 (en)* | 2006-11-13 | 2014-03-18 | Samsung Sds Co., Ltd. | Method for inferring maliciousness of email and detecting a virus pattern |
| US20100077480A1 (en)* | 2006-11-13 | 2010-03-25 | Samsung Sds Co., Ltd. | Method for Inferring Maliciousness of Email and Detecting a Virus Pattern |
| US8224905B2 (en) | 2006-12-06 | 2012-07-17 | Microsoft Corporation | Spam filtration utilizing sender activity data |
| US20080147861A1 (en)* | 2006-12-13 | 2008-06-19 | Takumi Oishi | Data distribution network and an apparatus of index holding |
| US20080162135A1 (en)* | 2006-12-30 | 2008-07-03 | Emc Corporation | Analyzing network traffic |
| US9152706B1 (en) | 2006-12-30 | 2015-10-06 | Emc Corporation | Anonymous identification tokens |
| US8577680B2 (en) | 2006-12-30 | 2013-11-05 | Emc Corporation | Monitoring and logging voice traffic on data network |
| US20130246378A1 (en)* | 2007-04-30 | 2013-09-19 | Stephen Owen Hearnden | Partial hash system, method, and computer program product |
| US20080275957A1 (en)* | 2007-05-03 | 2008-11-06 | Microsoft Corporation | Identifying and correlating electronic mail messages |
| US8423616B2 (en)* | 2007-05-03 | 2013-04-16 | Microsoft Corporation | Identifying and correlating electronic mail messages |
| US20080313708A1 (en)* | 2007-06-12 | 2008-12-18 | Alcatel Lucent | Data content matching |
| US20090077182A1 (en)* | 2007-09-17 | 2009-03-19 | Iconix, Inc | System and method for identifying email campaigns |
| US8775604B2 (en)* | 2007-09-24 | 2014-07-08 | Barracuda Networks, Inc. | Distributed frequency data collection via indicator embedded with DNS request |
| US20100049848A1 (en)* | 2007-09-24 | 2010-02-25 | Barracuda Networks, Inc | Distributed frequency data collection via indicator embedded with dns request |
| US7769485B2 (en)* | 2007-09-29 | 2010-08-03 | Pitney Bowes Inc. | Systems and methods for segregating undesired mail |
| US20090084713A1 (en)* | 2007-09-29 | 2009-04-02 | Miller John P | Systems and Methods for Segregating Undesired Mail |
| US20090100079A1 (en)* | 2007-10-12 | 2009-04-16 | Fujitsu Limited | E-mail information management apparatus, and e-mail information management method |
| US8832202B2 (en)* | 2007-10-12 | 2014-09-09 | Fujitsu Limited | E-mail information management apparatus, and E-mail information management method |
| US20090164506A1 (en)* | 2007-12-19 | 2009-06-25 | Casdex, Inc. | System and Method for Content-Based Email Authentication |
| US20090183257A1 (en)* | 2008-01-15 | 2009-07-16 | Microsoft Corporation | Preventing secure data from leaving the network perimeter |
| CN101911591A (en)* | 2008-01-15 | 2010-12-08 | 微软公司 | Preventing secure data from leaving a network perimeter |
| US8316442B2 (en)* | 2008-01-15 | 2012-11-20 | Microsoft Corporation | Preventing secure data from leaving the network perimeter |
| US8392511B2 (en)* | 2008-01-17 | 2013-03-05 | International Business Machines Corporation | Embedding a unique serial number into the content of an email for tracking information dispersion |
| US20090187629A1 (en)* | 2008-01-17 | 2009-07-23 | International Business Machines Corporation | Embedding a unque serial number into the content of an email for tracking information dispersion |
| US10104041B2 (en) | 2008-05-16 | 2018-10-16 | Cisco Technology, Inc. | Controlling the spread of interests and content in a content centric network |
| US9497205B1 (en)* | 2008-05-19 | 2016-11-15 | Emc Corporation | Global commonality and network logging |
| US20090300761A1 (en)* | 2008-05-28 | 2009-12-03 | John Park | Intelligent Hashes for Centralized Malware Detection |
| US8732825B2 (en)* | 2008-05-28 | 2014-05-20 | Symantec Corporation | Intelligent hashes for centralized malware detection |
| WO2009146536A1 (en) | 2008-06-02 | 2009-12-10 | Corporation De L'ecole Polytechnique De Montreal | File presence detection and monitoring |
| US20110145267A1 (en)* | 2008-06-02 | 2011-06-16 | Jean-Pierre David | File presence detection and monitoring |
| JP2011523130A (en)* | 2008-06-02 | 2011-08-04 | コーポレーション ド レコール ポリテクニーク ド モントリオール | File presence detection and monitoring |
| US9264434B2 (en)* | 2008-06-02 | 2016-02-16 | Polyvalor, Limited Partnership | File presence detection and monitoring |
| US9894039B2 (en)* | 2008-06-22 | 2018-02-13 | Microsoft Technology Licensing, Llc | Signed ephemeral email addresses |
| US20140331310A1 (en)* | 2008-06-22 | 2014-11-06 | Microsoft Corporation | Signed ephemeral email addresses |
| US7530106B1 (en)* | 2008-07-02 | 2009-05-05 | Kaspersky Lab, Zao | System and method for security rating of computer processes |
| US8180838B2 (en)* | 2008-08-29 | 2012-05-15 | Microsoft Corporation | Efficiently managing modular data storage systems |
| US20100058023A1 (en)* | 2008-08-29 | 2010-03-04 | Microsoft Corporation | Efficiently managing modular data storage systems |
| US20110202620A1 (en)* | 2008-12-02 | 2011-08-18 | Tencent Technology (Shenzhen) Company Limited | Method and device for intercepting junk mail |
| US9461930B2 (en) | 2009-04-27 | 2016-10-04 | Intel Corporation | Modifying data streams without reordering in a multi-thread, multi-flow network processor |
| US9208475B2 (en)* | 2009-06-11 | 2015-12-08 | Hewlett-Packard Development Company, L.P. | Apparatus and method for email storage |
| US20100318612A1 (en)* | 2009-06-11 | 2010-12-16 | Vivek Agarwal | Apparatus and Method for Email Storage |
| US20190012338A1 (en)* | 2009-06-19 | 2019-01-10 | International Business Machines Corporation | Hierarchical diff files |
| US10997145B2 (en)* | 2009-06-19 | 2021-05-04 | International Business Machines Corporation | Hierarchical diff files |
| US9686194B2 (en) | 2009-10-21 | 2017-06-20 | Cisco Technology, Inc. | Adaptive multi-interface use for content networking |
| US20110099291A1 (en)* | 2009-10-23 | 2011-04-28 | Comcast Cable Communications, Llc | Address Couplet Communication Filtering |
| US20130246550A1 (en)* | 2009-10-23 | 2013-09-19 | Camcast Cable Communications, LLC | Address Couplet Communication Filtering |
| EP2315407A3 (en)* | 2009-10-23 | 2013-06-19 | Comcast Cable Communications, LLC | Address couplet communication filtering |
| US8463938B2 (en)* | 2009-10-23 | 2013-06-11 | Comcast Cable Communications, Llc | Address couplet communication filtering |
| US10284504B2 (en)* | 2009-10-23 | 2019-05-07 | Comcast Cable Communications, Llc | Address couplet communication filtering |
| US20120158729A1 (en)* | 2010-05-18 | 2012-06-21 | Lsi Corporation | Concurrent linked-list traversal for real-time hash processing in multi-core, multi-thread network processors |
| US8515965B2 (en)* | 2010-05-18 | 2013-08-20 | Lsi Corporation | Concurrent linked-list traversal for real-time hash processing in multi-core, multi-thread network processors |
| US9154442B2 (en) | 2010-05-18 | 2015-10-06 | Intel Corporation | Concurrent linked-list traversal for real-time hash processing in multi-core, multi-thread network processors |
| WO2012007202A1 (en)* | 2010-07-13 | 2012-01-19 | F-Secure Corporation | Identifying polymorphic malware |
| US9336380B2 (en) | 2010-12-15 | 2016-05-10 | Microsoft Technology Licensing Llc | Applying activity actions to frequent activities |
| WO2012162676A2 (en) | 2011-05-25 | 2012-11-29 | Microsoft Corporation | Dynamic rule reordering for message classification |
| US9116879B2 (en) | 2011-05-25 | 2015-08-25 | Microsoft Technology Licensing, Llc | Dynamic rule reordering for message classification |
| EP2715565A4 (en)* | 2011-05-25 | 2015-07-15 | Microsoft Technology Licensing Llc | Dynamic rule reordering for message classification |
| US9224000B1 (en)* | 2011-06-14 | 2015-12-29 | Ionic Security, Inc. | Systems and methods for providing information security using context-based keys |
| US9621343B1 (en) | 2011-06-14 | 2017-04-11 | Ionic Security Inc. | Systems and methods for providing information security using context-based keys |
| US10095874B1 (en)* | 2011-06-14 | 2018-10-09 | Ionic Security Inc. | Systems and methods for providing information security using context-based keys |
| US9619659B1 (en) | 2011-06-14 | 2017-04-11 | Ionic Security Inc. | Systems and methods for providing information security using context-based keys |
| US9811664B1 (en) | 2011-08-15 | 2017-11-07 | Trend Micro Incorporated | Methods and systems for detecting unwanted web contents |
| US8700913B1 (en) | 2011-09-23 | 2014-04-15 | Trend Micro Incorporated | Detection of fake antivirus in computers |
| US20150381539A1 (en)* | 2012-01-25 | 2015-12-31 | Bitdefender IPR Management Ltd. | Systems and Methods for Spam Detection Using Frequency Spectra of Character Strings |
| US10212114B2 (en)* | 2012-01-25 | 2019-02-19 | Bitdefender IPR Management Ltd. | Systems and methods for spam detection using frequency spectra of character strings |
| US8719356B2 (en) | 2012-04-17 | 2014-05-06 | Return Path, Inc | Methods, systems, and computer readable media for monitoring deliverability of electronic mail based on subscriber and seed deliverability data |
| EP2811699A1 (en)* | 2013-06-06 | 2014-12-10 | Kaspersky Lab, ZAO | System and method for spam filtering using shingles |
| US8996638B2 (en) | 2013-06-06 | 2015-03-31 | Kaspersky Lab Zao | System and method for spam filtering using shingles |
| US9391936B2 (en) | 2013-06-06 | 2016-07-12 | AO Kaspersky Lab | System and method for spam filtering using insignificant shingles |
| US11425076B1 (en)* | 2013-10-30 | 2022-08-23 | Mesh Labs Inc. | Method and system for filtering electronic communications |
| US10805251B2 (en)* | 2013-10-30 | 2020-10-13 | Mesh Labs Inc. | Method and system for filtering electronic communications |
| US11005989B1 (en) | 2013-11-07 | 2021-05-11 | Rightquestion, Llc | Validating automatic number identification data |
| US12238243B2 (en) | 2013-11-07 | 2025-02-25 | Rightquestion, Llc | Validating automatic number identification data |
| US11856132B2 (en) | 2013-11-07 | 2023-12-26 | Rightquestion, Llc | Validating automatic number identification data |
| US10098051B2 (en) | 2014-01-22 | 2018-10-09 | Cisco Technology, Inc. | Gateways and routing in software-defined manets |
| US9223971B1 (en)* | 2014-01-28 | 2015-12-29 | Exelis Inc. | User reporting and automatic threat processing of suspicious email |
| US10469510B2 (en)* | 2014-01-31 | 2019-11-05 | Juniper Networks, Inc. | Intermediate responses for non-html downloads |
| US20150222650A1 (en)* | 2014-01-31 | 2015-08-06 | Juniper Networks, Inc. | Intermediate responses for non-html downloads |
| US9954678B2 (en) | 2014-02-06 | 2018-04-24 | Cisco Technology, Inc. | Content-based transport security |
| US9264418B1 (en)* | 2014-02-20 | 2016-02-16 | Amazon Technologies, Inc. | Client-side spam detection and prevention |
| US10445380B2 (en) | 2014-03-04 | 2019-10-15 | Cisco Technology, Inc. | System and method for direct storage access in a content-centric network |
| US9836540B2 (en) | 2014-03-04 | 2017-12-05 | Cisco Technology, Inc. | System and method for direct storage access in a content-centric network |
| US9473405B2 (en)* | 2014-03-10 | 2016-10-18 | Palo Alto Research Center Incorporated | Concurrent hashes and sub-hashes on data streams |
| US9626413B2 (en) | 2014-03-10 | 2017-04-18 | Cisco Systems, Inc. | System and method for ranking content popularity in a content-centric network |
| US20150256461A1 (en)* | 2014-03-10 | 2015-09-10 | Palo Alto Research Center Incorporated | Concurrent hashes and sub-hashes on data streams |
| US9716622B2 (en) | 2014-04-01 | 2017-07-25 | Cisco Technology, Inc. | System and method for dynamic name configuration in content-centric networks |
| US9473576B2 (en) | 2014-04-07 | 2016-10-18 | Palo Alto Research Center Incorporated | Service discovery using collection synchronization with exact names |
| US20150295869A1 (en)* | 2014-04-14 | 2015-10-15 | Microsoft Corporation | Filtering Electronic Messages |
| US20210344632A1 (en)* | 2014-04-29 | 2021-11-04 | At&T Intellectual Property I, L.P. | Detection of spam messages |
| US11095586B2 (en)* | 2014-04-29 | 2021-08-17 | At&T Intellectual Property I, L.P. | Detection of spam messages |
| US9992281B2 (en) | 2014-05-01 | 2018-06-05 | Cisco Technology, Inc. | Accountable content stores for information centric networks |
| US9928465B2 (en)* | 2014-05-20 | 2018-03-27 | Oath Inc. | Machine learning and validation of account names, addresses, and/or identifiers |
| US10789537B2 (en) | 2014-05-20 | 2020-09-29 | Oath Inc. | Machine learning and validation of account names, addresses, and/or identifiers |
| US11704583B2 (en) | 2014-05-20 | 2023-07-18 | Yahoo Assets Llc | Machine learning and validation of account names, addresses, and/or identifiers |
| US10158656B2 (en) | 2014-05-22 | 2018-12-18 | Cisco Technology, Inc. | Method and apparatus for preventing insertion of malicious content at a named data network router |
| US9609014B2 (en) | 2014-05-22 | 2017-03-28 | Cisco Systems, Inc. | Method and apparatus for preventing insertion of malicious content at a named data network router |
| US9699198B2 (en) | 2014-07-07 | 2017-07-04 | Cisco Technology, Inc. | System and method for parallel secure content bootstrapping in content-centric networks |
| US9621354B2 (en) | 2014-07-17 | 2017-04-11 | Cisco Systems, Inc. | Reconstructable content objects |
| US10237075B2 (en) | 2014-07-17 | 2019-03-19 | Cisco Technology, Inc. | Reconstructable content objects |
| US9590887B2 (en) | 2014-07-18 | 2017-03-07 | Cisco Systems, Inc. | Method and system for keeping interest alive in a content centric network |
| US9729616B2 (en) | 2014-07-18 | 2017-08-08 | Cisco Technology, Inc. | Reputation-based strategy for forwarding and responding to interests over a content centric network |
| US9929935B2 (en) | 2014-07-18 | 2018-03-27 | Cisco Technology, Inc. | Method and system for keeping interest alive in a content centric network |
| US10305968B2 (en) | 2014-07-18 | 2019-05-28 | Cisco Technology, Inc. | Reputation-based strategy for forwarding and responding to interests over a content centric network |
| US9882964B2 (en) | 2014-08-08 | 2018-01-30 | Cisco Technology, Inc. | Explicit strategy feedback in name-based forwarding |
| US9729662B2 (en) | 2014-08-11 | 2017-08-08 | Cisco Technology, Inc. | Probabilistic lazy-forwarding technique without validation in a content centric network |
| US9800637B2 (en) | 2014-08-19 | 2017-10-24 | Cisco Technology, Inc. | System and method for all-in-one content stream in content-centric networks |
| US10367871B2 (en) | 2014-08-19 | 2019-07-30 | Cisco Technology, Inc. | System and method for all-in-one content stream in content-centric networks |
| US10715634B2 (en) | 2014-10-23 | 2020-07-14 | Cisco Technology, Inc. | System and method for creating virtual interfaces based on network characteristics |
| US10069933B2 (en) | 2014-10-23 | 2018-09-04 | Cisco Technology, Inc. | System and method for creating virtual interfaces based on network characteristics |
| US9590948B2 (en) | 2014-12-15 | 2017-03-07 | Cisco Systems, Inc. | CCN routing using hardware-assisted hash tables |
| US10237189B2 (en) | 2014-12-16 | 2019-03-19 | Cisco Technology, Inc. | System and method for distance-based interest forwarding |
| US10003520B2 (en) | 2014-12-22 | 2018-06-19 | Cisco Technology, Inc. | System and method for efficient name-based content routing using link-state information in information-centric networks |
| US10091012B2 (en) | 2014-12-24 | 2018-10-02 | Cisco Technology, Inc. | System and method for multi-source multicasting in content-centric networks |
| US9660825B2 (en) | 2014-12-24 | 2017-05-23 | Cisco Technology, Inc. | System and method for multi-source multicasting in content-centric networks |
| US9954795B2 (en) | 2015-01-12 | 2018-04-24 | Cisco Technology, Inc. | Resource allocation using CCN manifests |
| US9946743B2 (en) | 2015-01-12 | 2018-04-17 | Cisco Technology, Inc. | Order encoded manifests in a content centric network |
| US9832291B2 (en) | 2015-01-12 | 2017-11-28 | Cisco Technology, Inc. | Auto-configurable transport stack |
| US9916457B2 (en) | 2015-01-12 | 2018-03-13 | Cisco Technology, Inc. | Decoupled name security binding for CCN objects |
| US10440161B2 (en) | 2015-01-12 | 2019-10-08 | Cisco Technology, Inc. | Auto-configurable transport stack |
| US10020936B1 (en) | 2015-02-05 | 2018-07-10 | Ionic Security Inc. | Systems and methods for encryption and provision of information security using platform services |
| US11973860B1 (en) | 2015-02-05 | 2024-04-30 | lonic Security Inc. | Systems and methods for encryption and provision of information security using platform services |
| US9608810B1 (en) | 2015-02-05 | 2017-03-28 | Ionic Security Inc. | Systems and methods for encryption and provision of information security using platform services |
| US9608809B1 (en) | 2015-02-05 | 2017-03-28 | Ionic Security Inc. | Systems and methods for encryption and provision of information security using platform services |
| US10270592B1 (en) | 2015-02-05 | 2019-04-23 | Ionic Security Inc. | Systems and methods for encryption and provision of information security using platform services |
| US10020935B1 (en) | 2015-02-05 | 2018-07-10 | Ionic Security Inc. | Systems and methods for encryption and provision of information security using platform services |
| US9614670B1 (en) | 2015-02-05 | 2017-04-04 | Ionic Security Inc. | Systems and methods for encryption and provision of information security using platform services |
| US10333840B2 (en) | 2015-02-06 | 2019-06-25 | Cisco Technology, Inc. | System and method for on-demand content exchange with adaptive naming in information-centric networks |
| US10075401B2 (en) | 2015-03-18 | 2018-09-11 | Cisco Technology, Inc. | Pending interest table behavior |
| US10075402B2 (en) | 2015-06-24 | 2018-09-11 | Cisco Technology, Inc. | Flexible command and control in content centric networks |
| US10701038B2 (en) | 2015-07-27 | 2020-06-30 | Cisco Technology, Inc. | Content negotiation in a content centric network |
| US9986034B2 (en) | 2015-08-03 | 2018-05-29 | Cisco Technology, Inc. | Transferring state in content centric network stacks |
| US10419345B2 (en) | 2015-09-11 | 2019-09-17 | Cisco Technology, Inc. | Network named fragments in a content centric network |
| US9832123B2 (en) | 2015-09-11 | 2017-11-28 | Cisco Technology, Inc. | Network named fragments in a content centric network |
| US10355999B2 (en) | 2015-09-23 | 2019-07-16 | Cisco Technology, Inc. | Flow control with network named fragments |
| US10313227B2 (en) | 2015-09-24 | 2019-06-04 | Cisco Technology, Inc. | System and method for eliminating undetected interest looping in information-centric networks |
| US9977809B2 (en) | 2015-09-24 | 2018-05-22 | Cisco Technology, Inc. | Information and data framework in a content centric network |
| US10454820B2 (en) | 2015-09-29 | 2019-10-22 | Cisco Technology, Inc. | System and method for stateless information-centric networking |
| US10263965B2 (en) | 2015-10-16 | 2019-04-16 | Cisco Technology, Inc. | Encrypted CCNx |
| US9912776B2 (en) | 2015-12-02 | 2018-03-06 | Cisco Technology, Inc. | Explicit content deletion commands in a content centric network |
| US10097346B2 (en) | 2015-12-09 | 2018-10-09 | Cisco Technology, Inc. | Key catalogs in a content centric network |
| US11709948B1 (en) | 2015-12-28 | 2023-07-25 | Ionic Security Inc. | Systems and methods for generation of secure indexes for cryptographically-secure queries |
| US11232216B1 (en) | 2015-12-28 | 2022-01-25 | Ionic Security Inc. | Systems and methods for generation of secure indexes for cryptographically-secure queries |
| US10503730B1 (en) | 2015-12-28 | 2019-12-10 | Ionic Security Inc. | Systems and methods for cryptographically-secure queries using filters generated by multiple parties |
| US10257271B2 (en) | 2016-01-11 | 2019-04-09 | Cisco Technology, Inc. | Chandra-Toueg consensus in a content centric network |
| US10581967B2 (en) | 2016-01-11 | 2020-03-03 | Cisco Technology, Inc. | Chandra-Toueg consensus in a content centric network |
| US10305864B2 (en) | 2016-01-25 | 2019-05-28 | Cisco Technology, Inc. | Method and system for interest encryption in a content centric network |
| US10043016B2 (en) | 2016-02-29 | 2018-08-07 | Cisco Technology, Inc. | Method and system for name encryption agreement in a content centric network |
| US10051071B2 (en) | 2016-03-04 | 2018-08-14 | Cisco Technology, Inc. | Method and system for collecting historical network information in a content centric network |
| US10742596B2 (en) | 2016-03-04 | 2020-08-11 | Cisco Technology, Inc. | Method and system for reducing a collision probability of hash-based names using a publisher identifier |
| US10003507B2 (en) | 2016-03-04 | 2018-06-19 | Cisco Technology, Inc. | Transport session state protocol |
| US10469378B2 (en) | 2016-03-04 | 2019-11-05 | Cisco Technology, Inc. | Protocol to query for historical network information in a content centric network |
| US10038633B2 (en) | 2016-03-04 | 2018-07-31 | Cisco Technology, Inc. | Protocol to query for historical network information in a content centric network |
| US10129368B2 (en) | 2016-03-14 | 2018-11-13 | Cisco Technology, Inc. | Adjusting entries in a forwarding information base in a content centric network |
| US9832116B2 (en) | 2016-03-14 | 2017-11-28 | Cisco Technology, Inc. | Adjusting entries in a forwarding information base in a content centric network |
| US10212196B2 (en) | 2016-03-16 | 2019-02-19 | Cisco Technology, Inc. | Interface discovery and authentication in a name-based network |
| US10067948B2 (en) | 2016-03-18 | 2018-09-04 | Cisco Technology, Inc. | Data deduping in content centric networking manifests |
| US11436656B2 (en) | 2016-03-18 | 2022-09-06 | Palo Alto Research Center Incorporated | System and method for a real-time egocentric collaborative filter on large datasets |
| US10091330B2 (en) | 2016-03-23 | 2018-10-02 | Cisco Technology, Inc. | Interest scheduling by an information and data framework in a content centric network |
| US10033639B2 (en) | 2016-03-25 | 2018-07-24 | Cisco Technology, Inc. | System and method for routing packets in a content centric network using anonymous datagrams |
| CN107294834A (en)* | 2016-03-31 | 2017-10-24 | 阿里巴巴集团控股有限公司 | A kind of method and apparatus for recognizing spam |
| US20170289082A1 (en)* | 2016-03-31 | 2017-10-05 | Alibaba Group Holding Limited | Method and device for identifying spam mail |
| US10320760B2 (en) | 2016-04-01 | 2019-06-11 | Cisco Technology, Inc. | Method and system for mutating and caching content in a content centric network |
| US10348865B2 (en) | 2016-04-04 | 2019-07-09 | Cisco Technology, Inc. | System and method for compressing content centric networking messages |
| US9930146B2 (en) | 2016-04-04 | 2018-03-27 | Cisco Technology, Inc. | System and method for compressing content centric networking messages |
| US10425503B2 (en) | 2016-04-07 | 2019-09-24 | Cisco Technology, Inc. | Shared pending interest table in a content centric network |
| US10027578B2 (en) | 2016-04-11 | 2018-07-17 | Cisco Technology, Inc. | Method and system for routable prefix queries in a content centric network |
| US10841212B2 (en) | 2016-04-11 | 2020-11-17 | Cisco Technology, Inc. | Method and system for routable prefix queries in a content centric network |
| US10404450B2 (en) | 2016-05-02 | 2019-09-03 | Cisco Technology, Inc. | Schematized access control in a content centric network |
| US10565183B1 (en)* | 2016-05-02 | 2020-02-18 | Pure Storage, Inc. | Efficient deduplication signature utilization |
| US10320675B2 (en) | 2016-05-04 | 2019-06-11 | Cisco Technology, Inc. | System and method for routing packets in a stateless content centric network |
| US10547589B2 (en) | 2016-05-09 | 2020-01-28 | Cisco Technology, Inc. | System for implementing a small computer systems interface protocol over a content centric network |
| US10084764B2 (en) | 2016-05-13 | 2018-09-25 | Cisco Technology, Inc. | System for a secure encryption proxy in a content centric network |
| US10693852B2 (en) | 2016-05-13 | 2020-06-23 | Cisco Technology, Inc. | System for a secure encryption proxy in a content centric network |
| US10404537B2 (en) | 2016-05-13 | 2019-09-03 | Cisco Technology, Inc. | Updating a transport stack in a content centric network |
| US10063414B2 (en) | 2016-05-13 | 2018-08-28 | Cisco Technology, Inc. | Updating a transport stack in a content centric network |
| US10103989B2 (en) | 2016-06-13 | 2018-10-16 | Cisco Technology, Inc. | Content object return messages in a content centric network |
| US10305865B2 (en) | 2016-06-21 | 2019-05-28 | Cisco Technology, Inc. | Permutation-based content encryption with manifests in a content centric network |
| US10581741B2 (en) | 2016-06-27 | 2020-03-03 | Cisco Technology, Inc. | Method and system for interest groups in a content centric network |
| US10148572B2 (en) | 2016-06-27 | 2018-12-04 | Cisco Technology, Inc. | Method and system for interest groups in a content centric network |
| US10009266B2 (en) | 2016-07-05 | 2018-06-26 | Cisco Technology, Inc. | Method and system for reference counted pending interest tables in a content centric network |
| US9992097B2 (en) | 2016-07-11 | 2018-06-05 | Cisco Technology, Inc. | System and method for piggybacking routing information in interests in a content centric network |
| US10122624B2 (en) | 2016-07-25 | 2018-11-06 | Cisco Technology, Inc. | System and method for ephemeral entries in a forwarding information base in a content centric network |
| US10069729B2 (en) | 2016-08-08 | 2018-09-04 | Cisco Technology, Inc. | System and method for throttling traffic based on a forwarding information base in a content centric network |
| US10956412B2 (en) | 2016-08-09 | 2021-03-23 | Cisco Technology, Inc. | Method and system for conjunctive normal form attribute matching in a content centric network |
| US10033642B2 (en) | 2016-09-19 | 2018-07-24 | Cisco Technology, Inc. | System and method for making optimal routing decisions based on device-specific parameters in a content centric network |
| US10805270B2 (en) | 2016-09-26 | 2020-10-13 | Agari Data, Inc. | Mitigating communication risk by verifying a sender of a message |
| US10880322B1 (en) | 2016-09-26 | 2020-12-29 | Agari Data, Inc. | Automated tracking of interaction with a resource of a message |
| US12074850B2 (en) | 2016-09-26 | 2024-08-27 | Agari Data, Inc. | Mitigating communication risk by verifying a sender of a message |
| US11936604B2 (en) | 2016-09-26 | 2024-03-19 | Agari Data, Inc. | Multi-level security analysis and intermediate delivery of an electronic message |
| US11595354B2 (en) | 2016-09-26 | 2023-02-28 | Agari Data, Inc. | Mitigating communication risk by detecting similarity to a trusted message contact |
| US12316591B2 (en) | 2016-09-26 | 2025-05-27 | Agari Data, Inc. | Multi-level security analysis and intermediate delivery of an electronic message |
| US10992645B2 (en) | 2016-09-26 | 2021-04-27 | Agari Data, Inc. | Mitigating communication risk by detecting similarity to a trusted message contact |
| US10212248B2 (en) | 2016-10-03 | 2019-02-19 | Cisco Technology, Inc. | Cache management on high availability routers in a content centric network |
| US10897518B2 (en) | 2016-10-03 | 2021-01-19 | Cisco Technology, Inc. | Cache management on high availability routers in a content centric network |
| US10447805B2 (en) | 2016-10-10 | 2019-10-15 | Cisco Technology, Inc. | Distributed consensus in a content centric network |
| US10511563B2 (en)* | 2016-10-28 | 2019-12-17 | Micro Focus Llc | Hashes of email text |
| US20180124007A1 (en)* | 2016-10-28 | 2018-05-03 | Hewlett Packard Enterprise Development Lp | Hashes of email text |
| US10135948B2 (en) | 2016-10-31 | 2018-11-20 | Cisco Technology, Inc. | System and method for process migration in a content centric network |
| US12143413B2 (en)* | 2016-10-31 | 2024-11-12 | KnowBe4, Inc. | Systems and methods for an artificial intelligence driven agent |
| US12212596B2 (en) | 2016-10-31 | 2025-01-28 | KnowBe4, Inc. | Systems and methods for an artificial intelligence driven smart template |
| US10721332B2 (en) | 2016-10-31 | 2020-07-21 | Cisco Technology, Inc. | System and method for process migration in a content centric network |
| US20220417278A1 (en)* | 2016-10-31 | 2022-12-29 | KnowBe4, Inc. | Systems and methods for an artificial intelligence driven agent |
| US10243851B2 (en) | 2016-11-21 | 2019-03-26 | Cisco Technology, Inc. | System and method for forwarder connection information in a content centric network |
| US11722513B2 (en) | 2016-11-30 | 2023-08-08 | Agari Data, Inc. | Using a measure of influence of sender in determining a security risk associated with an electronic message |
| US11044267B2 (en) | 2016-11-30 | 2021-06-22 | Agari Data, Inc. | Using a measure of influence of sender in determining a security risk associated with an electronic message |
| US11210412B1 (en) | 2017-02-01 | 2021-12-28 | Ionic Security Inc. | Systems and methods for requiring cryptographic data protection as a precondition of system access |
| US11841959B1 (en) | 2017-02-01 | 2023-12-12 | Ionic Security Inc. | Systems and methods for requiring cryptographic data protection as a precondition of system access |
| US10757053B2 (en)* | 2017-03-02 | 2020-08-25 | Microsoft Technology Licensing, Llc | High confidence digital content treatment |
| US20180255010A1 (en)* | 2017-03-02 | 2018-09-06 | Linkedin Corporation | High confidence digital content treatment |
| US20180268474A1 (en)* | 2017-03-16 | 2018-09-20 | Amobee, Inc. | Sketch-based bid fraud detection |
| US12184662B2 (en) | 2017-04-26 | 2024-12-31 | Agari Data, Inc. | Message security assessment using sender identity profiles |
| US11019076B1 (en) | 2017-04-26 | 2021-05-25 | Agari Data, Inc. | Message security assessment using sender identity profiles |
| US11722497B2 (en) | 2017-04-26 | 2023-08-08 | Agari Data, Inc. | Message security assessment using sender identity profiles |
| US10805314B2 (en) | 2017-05-19 | 2020-10-13 | Agari Data, Inc. | Using message context to evaluate security of requested data |
| US20240089285A1 (en)* | 2017-06-07 | 2024-03-14 | Agari Data, Inc. | Automated responsive message to determine a security risk of a message sender |
| US11757914B1 (en)* | 2017-06-07 | 2023-09-12 | Agari Data, Inc. | Automated responsive message to determine a security risk of a message sender |
| US11102244B1 (en)* | 2017-06-07 | 2021-08-24 | Agari Data, Inc. | Automated intelligence gathering |
| US11516248B2 (en)* | 2017-08-25 | 2022-11-29 | Ecrime Management Strategies, Inc. | Security system for detection and mitigation of malicious communications |
| US10891419B2 (en)* | 2017-10-27 | 2021-01-12 | International Business Machines Corporation | Displaying electronic text-based messages according to their typographic features |
| US20190129924A1 (en)* | 2017-10-27 | 2019-05-02 | International Business Machines Corporation | Displaying electronic text-based messages according to their typographic features |
| US11151087B2 (en) | 2017-12-12 | 2021-10-19 | Interset Software Inc. | Tracking file movement in a network environment |
| US11132335B2 (en)* | 2017-12-12 | 2021-09-28 | Interset Software, Inc. | Systems and methods for file fingerprinting |
| WO2020061051A1 (en)* | 2018-09-17 | 2020-03-26 | Valimail Inc. | Entity-separated email domain authentication for known and open sign-up domains |
| US11258759B2 (en) | 2018-09-17 | 2022-02-22 | Valimail Inc. | Entity-separated email domain authentication for known and open sign-up domains |
| US20210067515A1 (en)* | 2018-11-21 | 2021-03-04 | Capital One Services, Llc | Method and System for Electronic Mail Attachment Management |
| US11658973B2 (en)* | 2018-11-21 | 2023-05-23 | Capital One Services, Llc | Method and system for electronic mail attachment management |
| US11641331B2 (en)* | 2019-06-04 | 2023-05-02 | Microsoft Technology Licensing, Llc | System and method for blocking distribution of non-acceptable attachments |
| US20230188499A1 (en)* | 2020-02-10 | 2023-06-15 | Proofpoint, Inc. | Electronic message processing systems and methods |
| US12058107B2 (en)* | 2020-02-10 | 2024-08-06 | Proofpoint, Inc. | Electronic message processing systems and methods |
| US11582190B2 (en)* | 2020-02-10 | 2023-02-14 | Proofpoint, Inc. | Electronic message processing systems and methods |
| US20210314748A1 (en)* | 2020-04-01 | 2021-10-07 | Lg Electronics Inc. | Verification of messages using hash chaining |
| US11811943B2 (en)* | 2020-04-01 | 2023-11-07 | Lg Electronics Inc. | Verification of messages using hash chaining |
| US20230370436A1 (en)* | 2020-05-27 | 2023-11-16 | Step Software Inc. | Systems and methods for data communications |
| US12184623B2 (en)* | 2020-05-27 | 2024-12-31 | Step Software Inc. | Systems and methods for data communications |
| US11956196B2 (en) | 2020-10-29 | 2024-04-09 | Proofpoint, Inc. | Bulk messaging detection and enforcement |
| US11652771B2 (en) | 2020-10-29 | 2023-05-16 | Proofpoint, Inc. | Bulk messaging detection and enforcement |
| US12199933B2 (en) | 2020-10-29 | 2025-01-14 | Proofpoint, Inc. | Bulk messaging detection and enforcement |
| US11411905B2 (en)* | 2020-10-29 | 2022-08-09 | Proofpoint, Inc. | Bulk messaging detection and enforcement |
| US20220141165A1 (en)* | 2020-10-29 | 2022-05-05 | Proofpoint, Inc. | Bulk Messaging Detection and Enforcement |
Also Published As
| Publication number | Publication date |
|---|---|
| US8204945B2 (en) | 2012-06-19 |
| US20100205670A1 (en) | 2010-08-12 |
| US8272060B2 (en) | 2012-09-18 |
| US20100205265A1 (en) | 2010-08-12 |
| US20090031129A1 (en) | 2009-01-29 |
| US20100205671A1 (en) | 2010-08-12 |
| US20090031136A1 (en) | 2009-01-29 |
| US20130014261A1 (en) | 2013-01-10 |
| US20090182867A1 (en) | 2009-07-16 |
| US20090132669A1 (en) | 2009-05-21 |
| US20090313339A1 (en) | 2009-12-17 |
| US20090158046A1 (en) | 2009-06-18 |
| US20090158435A1 (en) | 2009-06-18 |
| US20100205672A1 (en) | 2010-08-12 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| US8204945B2 (en) | Hash-based systems and methods for detecting and preventing transmission of unwanted e-mail | |
| US10084801B2 (en) | Time zero classification of messages | |
| US8955106B2 (en) | Managing infectious forwarded messages | |
| US9419927B2 (en) | Method and system for handling unwanted email messages | |
| CA2607005C (en) | Identifying threats in electronic messages | |
| EP1997281B1 (en) | Method and sytem for recognizing desired email | |
| US7801960B2 (en) | Monitoring electronic mail message digests | |
| US9338026B2 (en) | Delay technique in e-mail filtering system | |
| US10193898B2 (en) | Reputation-based method and system for determining a likelihood that a message is undesired | |
| US9648038B2 (en) | Propagation of viruses through an information technology network | |
| US20060149820A1 (en) | Detecting spam e-mail using similarity calculations | |
| EP1635524A1 (en) | A method and system for identifying and blocking spam email messages at an inspecting point | |
| CN111147489B (en) | Link camouflage-oriented fishfork attack mail discovery method and device | |
| US20060075099A1 (en) | Automatic elimination of viruses and spam | |
| US8612523B1 (en) | Methods and apparatus for detecting botnet attacks | |
| US20200097655A1 (en) | Time zero classification of messages | |
| Srikanthan | An Overview of Spam Handling Techniques |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| AS | Assignment | Owner name:BBNT SOLUTIONS LLC, MASSACHUSETTS Free format text:ASSIGNMENT OF ASSIGNORS INTEREST;ASSIGNORS:MILLIKEN, WALTER CLARK;STRAYER, WILLIAM TIMOTHY;MILLIGAN, STEPHEN DOUGLAS;REEL/FRAME:014474/0767 Effective date:20030902 | |
| AS | Assignment | Owner name:FLEET NATIONAL BANK, AS AGENT, MASSACHUSETTS Free format text:PATENT & TRADEMARK SECURITY AGREEMENT;ASSIGNOR:BBNT SOLUTIONS LLC;REEL/FRAME:014624/0196 Effective date:20040326 Owner name:FLEET NATIONAL BANK, AS AGENT,MASSACHUSETTS Free format text:PATENT & TRADEMARK SECURITY AGREEMENT;ASSIGNOR:BBNT SOLUTIONS LLC;REEL/FRAME:014624/0196 Effective date:20040326 | |
| AS | Assignment | Owner name:BBN TECHNOLOGIES CORP.,MASSACHUSETTS Free format text:MERGER;ASSIGNOR:BBNT SOLUTIONS LLC;REEL/FRAME:017274/0318 Effective date:20060103 Owner name:BBN TECHNOLOGIES CORP., MASSACHUSETTS Free format text:MERGER;ASSIGNOR:BBNT SOLUTIONS LLC;REEL/FRAME:017274/0318 Effective date:20060103 | |
| AS | Assignment | Owner name:STRAGENT, LLC, TEXAS Free format text:ASSIGNMENT OF ASSIGNORS INTEREST;ASSIGNOR:BBN TECHNOLOGIES CORP.;REEL/FRAME:021567/0572 Effective date:20080915 | |
| AS | Assignment | Owner name:BBN TECHNOLOGIES CORP. (AS SUCCESSOR BY MERGER TO Free format text:RELEASE OF SECURITY INTEREST;ASSIGNOR:BANK OF AMERICA, N.A. (SUCCESSOR BY MERGER TO FLEET NATIONAL BANK);REEL/FRAME:023427/0436 Effective date:20091026 | |
| AS | Assignment | Owner name:STRAGENT, LLC,TEXAS Free format text:ASSIGNMENT OF ASSIGNORS INTEREST;ASSIGNOR:AZURE NETWORKS, LLC;REEL/FRAME:023905/0349 Effective date:20090820 Owner name:AZURE NETWORKS, LLC,TEXAS Free format text:ASSIGNMENT OF ASSIGNORS INTEREST;ASSIGNOR:STRAGENT, LLC;REEL/FRAME:023909/0810 Effective date:20081010 | |
| STCB | Information on status: application discontinuation | Free format text:ABANDONED -- FAILURE TO RESPOND TO AN OFFICE ACTION |