Note
Access to this page requires authorization. You can trysigning in orchanging directories.
Access to this page requires authorization. You can trychanging directories.
Store secrets in a key vault in Azure DevTest Labs
In this article
You might need to enter a complex secret when you use Azure DevTest Labs. Secrets include passwords for your Windows VMs, public SSH keys for your Linux VMs, or personal access token to clone your Git repo through an artifact. Secrets are often long and have random characters. Entering them can be tricky and inconvenient, especially if you use the same secret multiple times.
To solve this problem and keep your secrets in a safe place, DevTest Labs supports storing secrets in anAzure Key Vault. The first time a user saves a secret, DevTest Labs automatically creates a key vault in the same resource group as the lab, and stores the secret. DevTest Labs creates a separate key vault for each user.
Lab users need to create a lab virtual machine before they can create a secret in the key vault. This requirement is because DevTest Labs must associate lab users with valid user documents. DevTest Labs then allows users to create and store secrets in their key vaults.
Save a secret in Azure Key Vault
To save your secret in Azure Key Vault, do the following steps:
- SelectMy secrets on the left menu.
- Enter aname for the secret. You see this name in the drop-down list when creating a VM, formula, or an environment.
- Enter the secret as thevalue.

Use a secret from Azure Key Vault
When you enter a secret to create a VM, formula, or environment, you can enter the secret manually or select a saved secret from the key vault. To use a secret stored in your key vault, do the following actions:
- SelectUse a saved secret.
- Select your secret from the drop-down list forPick a secret.

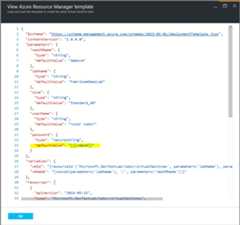
Use a secret in an Azure Resource Manager template
You can specify your secret name in an Azure Resource Manager template that's used to create a VM as shown in the following example:
Related content
Feedback
Was this page helpful?
Need help with this topic?
Want to try using Ask Learn to clarify or guide you through this topic?
Additional resources
- Last updated on
2025-09-26
In this article
Was this page helpful?
Want to try using Ask Learn to clarify or guide you through this topic?
[8]ページ先頭