Dependabot quickstart guide
Find and fix vulnerable dependencies you rely on with Dependabot.
Who can use this feature?
Dependabot alerts is available for the following repositories:
- Organization-owned and user-owned repositories
In this article
About Dependabot
This quickstart guide walks you through setting up and enabling Dependabot, viewing Dependabot alerts, and updating your repository to use a secure version of the dependency.
Dependabot consists of three different features that help you manage your dependencies:
- Dependabot alerts: Inform you about vulnerabilities in the dependencies that you use in your repository.
- Dependabot security updates: Automatically raise pull requests to update the dependencies you use that have known security vulnerabilities.
- Dependabot version updates: Automatically raise pull requests to keep your dependencies up-to-date.
Prerequisites
For the purpose of this guide, we're going to use a demo repository to illustrate how Dependabot finds vulnerabilities in dependencies, where you can see Dependabot alerts on GitHub, and how you can explore, fix, or dismiss these alerts.
You need to start by forking the demo repository.
- Navigate tohttps://github.com/dependabot/demo.
- At the top of the page, on the right, click Fork.
- Select an owner (you can select your GitHub personal account) and type a repository name. For more information about forking repositories, seeFork a repository.
- ClickCreate fork.
Enabling Dependabot for your repository
You need to follow the steps below on the repository you forked inPrerequisites.
On GitHub, navigate to the main page of the repository.
Under your repository name, click Settings. If you cannot see the "Settings" tab, select the dropdown menu, then clickSettings.

In the "Security" section of the sidebar, click Advanced Security.
Under "Dependabot", clickEnable for Dependabot alerts, Dependabot security updates, and Dependabot version updates.
If you clickedEnable for Dependabot version updates, you can edit the default
dependabot.ymlconfiguration file that GitHub creates for you in the/.githubdirectory of your repository.To enable Dependabot version updates for your repository, you typically configure this file to suit your needs by editing the default file, and committing your changes. You can refer to the snippet provided inConfiguring Dependabot version updates for an example.
Note
If the dependency graph is not already enabled for the repository, GitHub will enable it automatically when you enable Dependabot.
For more information about configuring each of these Dependabot features, seeConfiguring Dependabot alerts,Configuring Dependabot security updates, andConfiguring Dependabot version updates.
Viewing Dependabot alerts for your repository
If Dependabot alerts are enabled for a repository, you can view Dependabot alerts on the "Security" tab for the repository. You can use the forked repository that you enabled Dependabot alerts on in the previous section.
On GitHub, navigate to the main page of the repository.
Under the repository name, click Security. If you cannot see the "Security" tab, select the dropdown menu, and then clickSecurity.

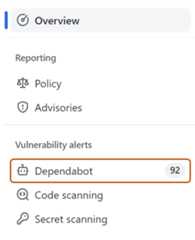
In the "Vulnerability alerts" sidebar of security overview, clickDependabot. If this option is missing, it means you don't have access to security alerts and need to be given access. For more information, seeManaging security and analysis settings for your repository.
Review the open alerts on the Dependabot alerts page. By default, the page displays theOpen tab, listing the open alerts. (You'll be able to view any closed alerts by clickingClosed.)

You can filter Dependabot alerts in the list, using a variety of filters or labels. For more information, seeViewing and updating Dependabot alerts. You can also use Dependabot auto-triage rules to filter out false positive alerts or alerts you're not interested in. For more information, seeAbout Dependabot auto-triage rules.
Click the "Command Injection in lodash" alert on the
javascript/package-lock.jsonfile. The details page for the alert will show the following information (note that some information may not apply to all alerts):- Whether Dependabot created a pull request that will fix the vulnerability. You can review the suggested security update by clickingReview security update.
- Package involved
- Affected versions
- Patched version
- Brief description of the vulnerability

Optionally, you can also explore the information on the right-side of the page. Some of the information shown in the screenshot may not apply to every alert.
- Severity
- CVSS metrics: We use CVSS levels to assign severity levels. For more information, seeAbout the GitHub Advisory database.
- Tags
- Weaknesses: List of CWEs related to the vulnerability, if applicable
- CVE ID: Unique CVE identifier for the vulnerability, if applicable
- GHSA ID: Unique identifier of the corresponding advisory on the GitHub Advisory Database. For more information, seeAbout the GitHub Advisory database.
- Option to navigate to the advisory on the GitHub Advisory Database
- Option to see all of your repositories that are affected by this vulnerability
- Option to suggest improvements for this advisory on the GitHub Advisory Database

For more information about viewing, prioritizing, and sorting Dependabot alerts, seeViewing and updating Dependabot alerts.
Fixing or dismissing a Dependabot alert
You can fix or dismiss Dependabot alerts on GitHub. Let's continue to use the forked repository as an example, and the "Command Injection in lodash" alert described in the previous section.
- Navigate to the Dependabot alerts tab for the repository. For more information, see theViewing Dependabot alerts for your repository section above.
- Click an alert.
- Click the "Command Injection in lodash" alert on the
javascript/package-lock.jsonfile. - Review the alert. You can:
Review the suggested security update by clickingReview security update. This will open the pull request generated by Dependabot with the security fix.

- On the pull request description, you can clickCommits to explore the commits included in the pull request.
- You can also clickDependabot commands and options to learn about the commands that you can use to interact with the pull request.
- When you're ready to update your dependency and resolve the vulnerability, merge the pull request.
If you decide that you want to dismiss the alert
Go back to the alert details page.
On the top-right corner, clickDismiss alert.
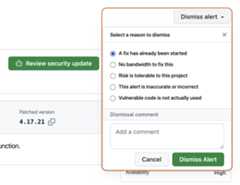
Select a reason for dismissing the alert.
Optionally, add a dismissal comment. The dismissal comment will be added to the alert timeline and can be used as justification during auditing and reporting.
ClickDismiss alert. The alert won't appear anymore in theOpen tab of the alert list, and you are able to view it in theClosed tab.
For more information about reviewing and updating Dependabot alerts, seeViewing and updating Dependabot alerts.
Troubleshooting
You may need to do some troubleshooting if:
- Dependabot is blocked from creating a pull request to fix an alert, or
- The information reported by Dependabot is not what you expect.
For more information, seeTroubleshooting Dependabot errors andTroubleshooting the detection of vulnerable dependencies, respectively.
Next steps
For more information about configuring Dependabot updates, seeConfiguring Dependabot security updates andConfiguring Dependabot version updates.
For more information about configuring Dependabot for an organization, seeConfiguring Dependabot alerts.
For more information about viewing pull requests opened by Dependabot, seeManaging pull requests for dependency updates.
For more information about the security advisories that contribute to Dependabot alerts, seeBrowsing security advisories in the GitHub Advisory Database.
For more information about configuring notifications about Dependabot alerts, seeConfiguring notifications for Dependabot alerts.