For a security enthusiast, a rooted Android device is essential to perform dynamic assessments of Android applications. They either rely on a physical device or a virtual device. The disadvantage of going for a physical device is the cost it incurs, the malfunctioning you may cause when rooting the device if a step goes wrong, or worse, leaving your device non-functional / bricked. A bricked device essentially means that the device will not function at all, unless remediating measures are taken, i.e., flashing Android ROM (which in my experience is a very tedious process, that may or may not yield the desired results).
To avoid issues like these, it is recommended to have a virtual device. Unlike a physical device, you can create a device to your liking and desired test cases, varying RAM and storage, varying operating systems, and architectural styles of these Android devices.
While Genymotion is the most favored emulator the community prefers, Android Studio does not come with a pre-rooted Android Virtual Device (AVD). Seeing Genymotion-rooted AVD made me wonder if it was possible to root AVD in Android Studio in Ubuntu, and that was the motivation behind the creation of this blog.
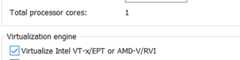
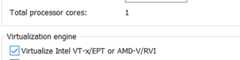
Disclaimer: For this post, I’m using Ubuntu OS ver. 18.04. You can run the same in a virtual machine, provided your virtual machine supports nested virtualization. To have that enabled, you need to make sure to enable Intel VT-x support in your virtualization application, otherwise, you cannot run Genymotion / Android Studio in a VM. It should look something like this in VMWare
The installation process of Android Studio remains identical across all flavors of Linux, except few minor differences. I’m skipping the explanation of the same since it is an easy process and there are plenty of other blogs that explain it.
Most of the resources that I used and the steps that I’ll be performing for Android AVD rooting have been taken from https://github.com/0xFireball/root_avd/. However, the persistence of the rooting procedure may / may not be there in subsequent restarts, and I’ll explain to have a persistent, rooted AVD at your disposal.
Prerequisite :-
a. Superuser — Application that allows privileged (su) access in Android. Download.
b. Drozer agent — Drozer should be installed in the host machine, i.e., Ubuntu in my case. Download.
c. Frida-server binary — The binary should be selected as per the architecture of AVD and version of Frida installed. At this point, I have 12.9.4 installed. Download.
d. Xposed Framework — Framework for modules that can change the behavior of system and applications without touching any APK. Download
e. Inspeckage — A tool developed to offer dynamic analysis of Android applications. By applying hooks to functions of the Android API, Inspeckage will help you understand what an Android application is doing at runtime. Download
f. Any root checker application. Download.
g. The main component — SU binary. Depending upon the architecture you are going to use for the AVD, you need to select the correct one from the GitHub repository.
AVD creation:
emulator -avd testAVD11. Here testAVD is the name of the device I assigned at the point of creationAVD Rooting :- Now that my AVD is working, we can start the process of rooting it. I’ll turn off my AVD and start it again with the following commandemulator -avd testAVD -writable-system -selinux disabled -qemu -enable-kvmemulator -avd testAVD -writable-system
The -writable-system switch ensures that whatever changes we are making in the /system folder of AVDs, it is persistent through reboots. This can also be seen as a warning message sent by emulatorMy suggestion is to create an alias of the command like this:

I’ve kept all my APKs along with Frida-server and su binary in the Downloads folder. Installing APKs is easy. Simply use the following command:
adb install <apk2>.apk
Using this, we’ll install some APKs
Before proceeding further, I must inform you that the image that I chose was an x86 Android image, hence I have downloaded the su binary from the following link:
https://github.com/0xFireball/root_avd/tree/master/SuperSU/x86
Kindly proceed with caution and download the correct su binary as per the architecture you have chosen to create your AVD.
Once you download the correct su binary, the following commands are to be executed on a new terminal window to enable root access and install su binary:
adb root && adb remount
adb push su /system/xbin/suadb shell chmod 06755 /system/xbin/su
adb shell su --install
adb shell su --daemon&
adb shell setenforce 0
Once you complete all these steps, go to your AVD and open the SuperUser application. It will prompt you to update the su binary. This shows that we were successfully able to root our AVD.
once you click on Continue, it will prompt you to update the binary either via the TWRP method or the Normal method. Select the Normal method.
Click on OK and proceed ahead. In case you get a prompt of update failure, click on continue and then check your root status with the root checker application. It should still show you that root access is working fine.
It may happen that once the su binary is updated, you will be tempted to reboot your device. But do not perform that action. All changes done for rooting may revert back and the device shall not boot up. Instead, create a snapshot of the working device from the Extended controls option
And that’s it. Whenever you want to have a clean AVD that has all your applications installed, along with working root, simply perform the following actions:
1. Launch the emulator: $HOME/Android/Sdk/emulator/emulator -avd testAVD -writable-system -selinux disabled -qemu -enable-kvm2. Restore the saved snapshot3. Run the following commands: a. adb root && adb remount b. adb shell su --daemon&
In the next blog, I’ll show how to configure applications such as Drozer, Frida, Inspeckage, etc.